Abstracts Logic and Random Graphs
... In some natural cases of finite graphs/structures a logical limit law, but not zero-one law, arises. This happens, for example, if one considers regular graphs, graphs with a fixed bound on the maximum degree, or graphs in which a certain fixed graph may not appear as a subgraph. In proving these re ...
... In some natural cases of finite graphs/structures a logical limit law, but not zero-one law, arises. This happens, for example, if one considers regular graphs, graphs with a fixed bound on the maximum degree, or graphs in which a certain fixed graph may not appear as a subgraph. In proving these re ...
Lecture 4 1 Balls and bins games - IC
... The problems discussed before have been extensively studied in mathematics for many decades, while the problem of analyzing the maximum load has been extensively studied only very recently, because of its many applications in computer science. Indeed, the problem of finding maximum load has many app ...
... The problems discussed before have been extensively studied in mathematics for many decades, while the problem of analyzing the maximum load has been extensively studied only very recently, because of its many applications in computer science. Indeed, the problem of finding maximum load has many app ...
IntroReview powerpoint
... 5. What is stylistically wrong with the following statement? double circumference = 3.14 * diameter; ...
... 5. What is stylistically wrong with the following statement? double circumference = 3.14 * diameter; ...
Chapter 3 Gambling, random walks and the Central Limit Theorem
... 1 − ǫ. What about the large value of the expected sum in the end of the game? It IS growing exponentially! The resolution is that with probability less than ǫ a HUGE sum is won, making up for losses which happen most of the time. Is there any way to exploit the large expected value and win this game ...
... 1 − ǫ. What about the large value of the expected sum in the end of the game? It IS growing exponentially! The resolution is that with probability less than ǫ a HUGE sum is won, making up for losses which happen most of the time. Is there any way to exploit the large expected value and win this game ...
Why Dembski`s Design Inference Doesn`t Work
... Suppose someone did not know about the chaos game. Since the area of the original triangle is zero, if a point in it were picked at random, it would have zero probability of being in the Sierpinski triangle. Similarly, any random sequence of points in the original triangle would seem to have zero ch ...
... Suppose someone did not know about the chaos game. Since the area of the original triangle is zero, if a point in it were picked at random, it would have zero probability of being in the Sierpinski triangle. Similarly, any random sequence of points in the original triangle would seem to have zero ch ...
Characteristic functions and the central limit theorem
... Our goal at the end of the day is to determine the distribution of Snn as n approaches infinity. So we need a better way to deal with sequences of random variables. It is natural to ask, “if we have a sequence of random variables X1 , X2 , . . . such that their characteristic function converge, then ...
... Our goal at the end of the day is to determine the distribution of Snn as n approaches infinity. So we need a better way to deal with sequences of random variables. It is natural to ask, “if we have a sequence of random variables X1 , X2 , . . . such that their characteristic function converge, then ...
Week 3 Notes.
... i ∈ I, ωi ∈ Ωi ). Ω is equipped with projections, Xi : Ω → Ωi , Xi (ω) = ωi . [picture of square, Ω1 on one side, Ω2 on other, point ω in middle, maps under projection to each side] Definition 7.3.2 A product σ-field on Ω is that generated by the projections: F = σ ((Xi ∈ Fi ) | Fi ∈ Fi ). F1 × F2 = ...
... i ∈ I, ωi ∈ Ωi ). Ω is equipped with projections, Xi : Ω → Ωi , Xi (ω) = ωi . [picture of square, Ω1 on one side, Ω2 on other, point ω in middle, maps under projection to each side] Definition 7.3.2 A product σ-field on Ω is that generated by the projections: F = σ ((Xi ∈ Fi ) | Fi ∈ Fi ). F1 × F2 = ...
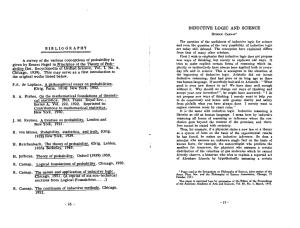
Probability, Analysis and Number Theory. Papers in Honour of N. H.
... fine probabilist and author; he was a difficult man, but was always very nice to me. He spoke at Westfield c. 1971, on the state of play in Markov processes. He began: “We’ve been going — too fast too fast; we’ve been proving — too many theorems too many theorems; now it’s time for a period of — re ...
... fine probabilist and author; he was a difficult man, but was always very nice to me. He spoke at Westfield c. 1971, on the state of play in Markov processes. He began: “We’ve been going — too fast too fast; we’ve been proving — too many theorems too many theorems; now it’s time for a period of — re ...
The ancestral process of long
... Comparing this to our previous construction of the ancestral process, we realise that PNµ can be considered as being the restriction of P̂Nµ to situations regarding the ancestry of a sample, and hence, with slight abuse of notation, we will identify the two measures, dropping the notation P̂Nµ . A t ...
... Comparing this to our previous construction of the ancestral process, we realise that PNµ can be considered as being the restriction of P̂Nµ to situations regarding the ancestry of a sample, and hence, with slight abuse of notation, we will identify the two measures, dropping the notation P̂Nµ . A t ...
Notes on Zero Knowledge 1 Interactive Proofs
... by HVPZK. A view of VL is described by the random input of VL and the sequence of messages exchanged between VL and PL . The definition captures the intuition that, if a protocol is HVPZK, then the verifier VL gains no useful information from the interaction with PL . In fact, anything that VL might ...
... by HVPZK. A view of VL is described by the random input of VL and the sequence of messages exchanged between VL and PL . The definition captures the intuition that, if a protocol is HVPZK, then the verifier VL gains no useful information from the interaction with PL . In fact, anything that VL might ...
PROBABILITY THEORY - PART 2 INDEPENDENT RANDOM
... is called Chebyshev’s inequality. Higher the moments that exist, better the asymptotic tail bounds that we get. For example, if E[eλX ] < ∞ for some λ > 0, we get exponential tail bounds by P(X > t) = P(eλX > eλt ) ≤ e−λt E[eλX ]. Note that X is not assumed to be non-negative in these examples as Ma ...
... is called Chebyshev’s inequality. Higher the moments that exist, better the asymptotic tail bounds that we get. For example, if E[eλX ] < ∞ for some λ > 0, we get exponential tail bounds by P(X > t) = P(eλX > eλt ) ≤ e−λt E[eλX ]. Note that X is not assumed to be non-negative in these examples as Ma ...
Class Notes Day 31: Intro to Series
... Series: Infinite Sums Series are a way to make sense of certain types of infinitely long sums. We will need to be able to do this if we are to attain our goal of approximating transcendental functions by using ‘infinite degree’ polynomials. But before we try to add together an infinite number of pol ...
... Series: Infinite Sums Series are a way to make sense of certain types of infinitely long sums. We will need to be able to do this if we are to attain our goal of approximating transcendental functions by using ‘infinite degree’ polynomials. But before we try to add together an infinite number of pol ...
Efficient Sketches for Earth-Mover Distance, with Applications
... elements from [n] such that, with “good probability”, we subsample exactly one element from Sj , say i ∈ Sj , and no element from Sj 0 for j 0 < j. We refer to this event as E. In a sense, we “isolate” (at most) one element i ∈ Sj , while the rest of the remaining elements are from “lighter” levels ...
... elements from [n] such that, with “good probability”, we subsample exactly one element from Sj , say i ∈ Sj , and no element from Sj 0 for j 0 < j. We refer to this event as E. In a sense, we “isolate” (at most) one element i ∈ Sj , while the rest of the remaining elements are from “lighter” levels ...
Section 4 - Probability Distributions
... 1. A binomial probability distribution always has a fixed number of trials. (in our example, this was 14 – we checked the probability of 0-14 girls among 14 newborns) 2. The trials must be independent. The outcome of any individual trial doesn’t affect the probabilities in the other trials. (in our ...
... 1. A binomial probability distribution always has a fixed number of trials. (in our example, this was 14 – we checked the probability of 0-14 girls among 14 newborns) 2. The trials must be independent. The outcome of any individual trial doesn’t affect the probabilities in the other trials. (in our ...
Infinite monkey theorem

The infinite monkey theorem states that a monkey hitting keys at random on a typewriter keyboard for an infinite amount of time will almost surely type a given text, such as the complete works of William Shakespeare.In this context, ""almost surely"" is a mathematical term with a precise meaning, and the ""monkey"" is not an actual monkey, but a metaphor for an abstract device that produces an endless random sequence of letters and symbols. One of the earliest instances of the use of the ""monkey metaphor"" is that of French mathematician Émile Borel in 1913, but the first instance may be even earlier. The relevance of the theorem is questionable—the probability of a universe full of monkeys typing a complete work such as Shakespeare's Hamlet is so tiny that the chance of it occurring during a period of time hundreds of thousands of orders of magnitude longer than the age of the universe is extremely low (but technically not zero). It should also be noted that real monkeys don't produce uniformly random output, which means that an actual monkey hitting keys for an infinite amount of time has no statistical certainty of ever producing any given text.Variants of the theorem include multiple and even infinitely many typists, and the target text varies between an entire library and a single sentence. The history of these statements can be traced back to Aristotle's On Generation and Corruption and Cicero's De natura deorum (On the Nature of the Gods), through Blaise Pascal and Jonathan Swift, and finally to modern statements with their iconic simians and typewriters. In the early 20th century, Émile Borel and Arthur Eddington used the theorem to illustrate the timescales implicit in the foundations of statistical mechanics.