P2P-NAT - Universität Freiburg
... does. Applications must therefore authen- points (10.1.1.3:4321, 155.99.25.11:62000) on B’s priChristian Schindelhauer ticate all messages in some way to filter out such stray vate network, and by the endpoints (138.76.29.7:31000, traffic robustly. The messages might include application- 155.99.25.1 ...
... does. Applications must therefore authen- points (10.1.1.3:4321, 155.99.25.11:62000) on B’s priChristian Schindelhauer ticate all messages in some way to filter out such stray vate network, and by the endpoints (138.76.29.7:31000, traffic robustly. The messages might include application- 155.99.25.1 ...
Availability and Popularity Measurements of Peer
... at separate geographic locations for one hour and analyzed the effects of caching search queries. Due to the high temporal locality of queries observed, a simple query caching scheme was shown to reduce query traffic by as much as a factor of two. This traffic does not include the traffic caused by ...
... at separate geographic locations for one hour and analyzed the effects of caching search queries. Due to the high temporal locality of queries observed, a simple query caching scheme was shown to reduce query traffic by as much as a factor of two. This traffic does not include the traffic caused by ...
GI3112131218
... *(Research Scholar, Department of Electronics Engineering, YMCA UST, Faridabad, India) ** ( Professor, Department of Electronics Engineering, YMCA UST, Faridabad, India) ***(Astt. Professor, Department of Electronics & Comm. Engineering, JMI, New Delhi, India) ...
... *(Research Scholar, Department of Electronics Engineering, YMCA UST, Faridabad, India) ** ( Professor, Department of Electronics Engineering, YMCA UST, Faridabad, India) ***(Astt. Professor, Department of Electronics & Comm. Engineering, JMI, New Delhi, India) ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... guarantees are required when network capacity is insufficient, especially for real-time streaming multimedia applications, as these require fixed bit rate and are delay sensitive and in network with limited resource [6] capacity. MANET routing protocols like AODV, DSR, and TORA, were designed withou ...
... guarantees are required when network capacity is insufficient, especially for real-time streaming multimedia applications, as these require fixed bit rate and are delay sensitive and in network with limited resource [6] capacity. MANET routing protocols like AODV, DSR, and TORA, were designed withou ...
A Network Application Programming Interface for Data
... In addition to the most basic form of unicast addressing for identifying the recipient of a message, the proposed API must also support a multicast group addressing mode as well as addressing modes based on physical regions, either centered around the sending node or around an arbitrary point in spa ...
... In addition to the most basic form of unicast addressing for identifying the recipient of a message, the proposed API must also support a multicast group addressing mode as well as addressing modes based on physical regions, either centered around the sending node or around an arbitrary point in spa ...
MANET Routing Protocols and Wormhole Attack against AODV
... 2. Destination-Sequenced Distance Vector Destination-Sequenced Distance Vector (DSDV) is a traditional table-driven protocol for MANET. To solve the routing loop problem, it was invented by C. Perkins and P. Bhagwat in 1994. Routes are established based on constant control traffic and they are avail ...
... 2. Destination-Sequenced Distance Vector Destination-Sequenced Distance Vector (DSDV) is a traditional table-driven protocol for MANET. To solve the routing loop problem, it was invented by C. Perkins and P. Bhagwat in 1994. Routes are established based on constant control traffic and they are avail ...
I/O Router Placement and Fine-Grained Routing
... FGR introduced a new LNET routing configuration. This new configuration assigned varying weights to LNET routes based on client I/O server pairings. Tests showed that with FGR, aggregate performance was boosted by 30%. Other solutions have since adopted the FGR techniques, including Cray’s Sonexion ...
... FGR introduced a new LNET routing configuration. This new configuration assigned varying weights to LNET routes based on client I/O server pairings. Tests showed that with FGR, aggregate performance was boosted by 30%. Other solutions have since adopted the FGR techniques, including Cray’s Sonexion ...
Safely Harnessing Wide Area Surrogate Computing -or-
... around the internet by downloading and installing grid middleware on available surrogates. Bob and Mary are playing a network game. Rather than using a public game server, which are often overrun by hormone-drenched teenagers, or running a private game server on one of their home PCs, which might gi ...
... around the internet by downloading and installing grid middleware on available surrogates. Bob and Mary are playing a network game. Rather than using a public game server, which are often overrun by hormone-drenched teenagers, or running a private game server on one of their home PCs, which might gi ...
Safely Harnessing Wide Area Surrogate Computing -or-
... around the internet by downloading and installing grid middleware on available surrogates. Bob and Mary are playing a network game. Rather than using a public game server, which are often overrun by hormone-drenched teenagers, or running a private game server on one of their home PCs, which might gi ...
... around the internet by downloading and installing grid middleware on available surrogates. Bob and Mary are playing a network game. Rather than using a public game server, which are often overrun by hormone-drenched teenagers, or running a private game server on one of their home PCs, which might gi ...
SOCC 2011
... destination. A node may use a well-established protocol, such as OSPF [29], to discover the shortest path to all destinations. Precomputing shortest paths will minimize the path stretch that is possible with a given topology, reduce congestion, and thus increase bandwidth. There are a few potential ...
... destination. A node may use a well-established protocol, such as OSPF [29], to discover the shortest path to all destinations. Precomputing shortest paths will minimize the path stretch that is possible with a given topology, reduce congestion, and thus increase bandwidth. There are a few potential ...
Brief Announcement: Atomic Consistency and Partition
... – Development cycle: build, test, debug, deploy ...
... – Development cycle: build, test, debug, deploy ...
ppt - Computer Science Division - University of California, Berkeley
... – suppose N hosts issue packet every M cycles with ave dist » each msg occupies h channels for l = n/w cycles each » C/N channels available per node » link utilization for store-and-forward: r = (hl/M channel cycles/node)/(C/N) = Nhl/MC < 1! » link utilization for wormhole routing? ...
... – suppose N hosts issue packet every M cycles with ave dist » each msg occupies h channels for l = n/w cycles each » C/N channels available per node » link utilization for store-and-forward: r = (hl/M channel cycles/node)/(C/N) = Nhl/MC < 1! » link utilization for wormhole routing? ...
CPU Performance
... Traffic pattern is a very important factor for the performance of a network In uniform random traffic each source is equally likely to send to each destination Uniform random traffic is the most commonly used traffic pattern for network evaluation. However it implies balancing of the load, which oft ...
... Traffic pattern is a very important factor for the performance of a network In uniform random traffic each source is equally likely to send to each destination Uniform random traffic is the most commonly used traffic pattern for network evaluation. However it implies balancing of the load, which oft ...
CPU Performance
... Traffic pattern is a very important factor for the performance of a network In uniform random traffic each source is equally likely to send to each destination Uniform random traffic is the most commonly used traffic pattern for network evaluation. However it implies balancing of the load, which oft ...
... Traffic pattern is a very important factor for the performance of a network In uniform random traffic each source is equally likely to send to each destination Uniform random traffic is the most commonly used traffic pattern for network evaluation. However it implies balancing of the load, which oft ...
How to Lease the Internet in Your Spare Time
... two distinct entities: infrastructure providers and service providers. An infrastructure provider owns and maintains the network equipment (e.g., routers and links) that forms an infrastructure network. A service provider establishes agreements with one or more infrastructure providers for access to ...
... two distinct entities: infrastructure providers and service providers. An infrastructure provider owns and maintains the network equipment (e.g., routers and links) that forms an infrastructure network. A service provider establishes agreements with one or more infrastructure providers for access to ...
Improved GAF in Wireless Sensor Network E-ISSN: 2321-9637 Jagpreet Singh
... Wireless sensor network is a network consisting of sensor nodes. To transmit information from one node to another routing protocols are used. Routing protocols select the best route in the network for transmitting data. The designing of routing protocol depends upon the application where it has to b ...
... Wireless sensor network is a network consisting of sensor nodes. To transmit information from one node to another routing protocols are used. Routing protocols select the best route in the network for transmitting data. The designing of routing protocol depends upon the application where it has to b ...
The UNIX/Linux Operating System Networking/Internet
... ONet Networking is the non-profit ISP (Internet Service Provider) mostly made out of Ontario educational and research institutions. It was the first public Ontario-based regional network (1988). Prior to 2003, NRC’s WAN was connected to ONet. For direct access to CA*net 2 and CA*net 4, ONet has a Gi ...
... ONet Networking is the non-profit ISP (Internet Service Provider) mostly made out of Ontario educational and research institutions. It was the first public Ontario-based regional network (1988). Prior to 2003, NRC’s WAN was connected to ONet. For direct access to CA*net 2 and CA*net 4, ONet has a Gi ...
pptx - Department of Computer Science
... Single network called may later become one) FastTrack used by other Publish: client sends list of clients as well files to its super-node Eventually the protocol Search: send query to superchanged so other clients node, and the super-nodes could no longer talk to it flood queries among thems ...
... Single network called may later become one) FastTrack used by other Publish: client sends list of clients as well files to its super-node Eventually the protocol Search: send query to superchanged so other clients node, and the super-nodes could no longer talk to it flood queries among thems ...
CNF_MultiNet, Connecting to Multiple IEEE 802.11 Networks Using
... The above protocol also ensures transparent switching: applications using a switching card do not have to know its state. Packets sent to the switching card are all received, though with some extra delay, as long as everybody is honest about their switching period. 4) Buffering on IEEE 802.11 Access ...
... The above protocol also ensures transparent switching: applications using a switching card do not have to know its state. Packets sent to the switching card are all received, though with some extra delay, as long as everybody is honest about their switching period. 4) Buffering on IEEE 802.11 Access ...
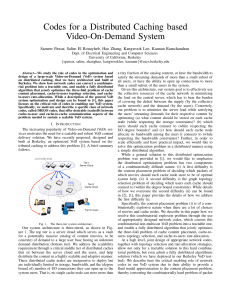
Codes for a Distributed Caching based Video-On
... the system experiences a “flash crowd” requesting a the total content stored on each cache and the sum upload rate video that is becoming viral. of each cache are within its storage and bandwidth capacity it may be more beneficial for the system, that a cache down3 Of course, since we are interested ...
... the system experiences a “flash crowd” requesting a the total content stored on each cache and the sum upload rate video that is becoming viral. of each cache are within its storage and bandwidth capacity it may be more beneficial for the system, that a cache down3 Of course, since we are interested ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... Protocol (VoIP) is a technology that enables one to make and receive calls through the Internet instead of using the traditional analog PSTN (Public Switched Telephone Network) lines. VOIP technology converts the analog telephone communication signals into digital communication signals and transfers ...
... Protocol (VoIP) is a technology that enables one to make and receive calls through the Internet instead of using the traditional analog PSTN (Public Switched Telephone Network) lines. VOIP technology converts the analog telephone communication signals into digital communication signals and transfers ...
View PDF - CiteSeerX
... Geographical ad hoc routing protocols are heavily dependent on the existence of scalable location management services, which are able to provide the location of any host at any time throughout the entire network. The most common way to enable nodes of knowing their location is by equipping them with ...
... Geographical ad hoc routing protocols are heavily dependent on the existence of scalable location management services, which are able to provide the location of any host at any time throughout the entire network. The most common way to enable nodes of knowing their location is by equipping them with ...
Peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or work loads between peers. Peers are equally privileged, equipotent participants in the application. They are said to form a peer-to-peer network of nodes.Peers make a portion of their resources, such as processing power, disk storage or network bandwidth, directly available to other network participants, without the need for central coordination by servers or stable hosts. Peers are both suppliers and consumers of resources, in contrast to the traditional client-server model in which the consumption and supply of resources is divided. Emerging collaborative P2P systems are going beyond the era of peers doing similar things while sharing resources, and are looking for diverse peers that can bring in unique resources and capabilities to a virtual community thereby empowering it to engage in greater tasks beyond those that can be accomplished by individual peers, yet that are beneficial to all the peers.While P2P systems had previously been used in many application domains, the architecture was popularized by the file sharing system Napster, originally released in 1999. The concept has inspired new structures and philosophies in many areas of human interaction. In such social contexts, peer-to-peer as a meme refers to the egalitarian social networking that has emerged throughout society, enabled by Internet technologies in general.