Java Concurrency and IO
... Java Overview Part II Based on Notes by J. Johns (based on Java in a Nutshell, Learning Java) Also Java Tutorial, Concurrent Programming in Java ...
... Java Overview Part II Based on Notes by J. Johns (based on Java in a Nutshell, Learning Java) Also Java Tutorial, Concurrent Programming in Java ...
Java Reflection Explained Simply
... But it becomes much easier once you “get it” Reflection seems natural to people who have written compilers (a parse tree is conceptually similar to metadata in reflection) ...
... But it becomes much easier once you “get it” Reflection seems natural to people who have written compilers (a parse tree is conceptually similar to metadata in reflection) ...
PPT - UBC Department of Computer Science
... Programming languages have well-defined semantics, no ambiguity Different than natural languages like English. Consider statement: Mary counted on her computer. How could we interpret this? ...
... Programming languages have well-defined semantics, no ambiguity Different than natural languages like English. Consider statement: Mary counted on her computer. How could we interpret this? ...
Introduction
... Machine language • the language that can be directly used and understood by the computer • operations are very low-level, specific to the architecture (not portable) • made up of binary-coded instructions (strings of 0s and 1s) ...
... Machine language • the language that can be directly used and understood by the computer • operations are very low-level, specific to the architecture (not portable) • made up of binary-coded instructions (strings of 0s and 1s) ...
CIS 175 Java Programming
... Java was developed by James Gosling at Sun Microsystems and was originally called Oak. It was designed for use in embedded consumer electronic applications in 1991. It was redesigned for developing Internet applications and renamed Java in 1995. Java is partially modeled after C++ but has been simpl ...
... Java was developed by James Gosling at Sun Microsystems and was originally called Oak. It was designed for use in embedded consumer electronic applications in 1991. It was redesigned for developing Internet applications and renamed Java in 1995. Java is partially modeled after C++ but has been simpl ...
unit 1
... • An identifier can be made up of letters, digits, the underscore character ‘_’, and the dollar sign ‘$’ • An identifier must begin with a letter, ‘_’ or ‘$’ • Java is case sensitive, therefore Total and total are different identifiers ...
... • An identifier can be made up of letters, digits, the underscore character ‘_’, and the dollar sign ‘$’ • An identifier must begin with a letter, ‘_’ or ‘$’ • Java is case sensitive, therefore Total and total are different identifiers ...
UNIT-1
... Explain any four methods of the StringBuffer class. 21. Write a program to illustrate the usage of the following methods of StringBuffer Class .Explain the output in each case. Delete (),setCharAt(),Append(),CharAt(),getchar(). 22. Write a java program to convert the given decimal numbers into binay ...
... Explain any four methods of the StringBuffer class. 21. Write a program to illustrate the usage of the following methods of StringBuffer Class .Explain the output in each case. Delete (),setCharAt(),Append(),CharAt(),getchar(). 22. Write a java program to convert the given decimal numbers into binay ...
document
... Synchronization is done within methods and blocks • Limited to block-structured locking • Cannot acquire a lock in one method and release it in another ...
... Synchronization is done within methods and blocks • Limited to block-structured locking • Cannot acquire a lock in one method and release it in another ...
Kapitel8[1]
... • RMI provides an activation schema for remote object servers • There is only one “server” running (the rmideamon), who will “wake up” the server when a client requests a service • It is necessary then to write and run a set-up program, which will register the “sleeping” server with the rmid • For t ...
... • RMI provides an activation schema for remote object servers • There is only one “server” running (the rmideamon), who will “wake up” the server when a client requests a service • It is necessary then to write and run a set-up program, which will register the “sleeping” server with the rmid • For t ...
COMP 110 Spring 2009 28
... Classes declare the attributes of objects of its type and the actions they will perform Class: all cars have an attribute “make” and action “drive” Objects: several instance of a class • each has a specific model: “Scion xB” , “Toyota Matrix” • but performs the same action: “drive” ...
... Classes declare the attributes of objects of its type and the actions they will perform Class: all cars have an attribute “make” and action “drive” Objects: several instance of a class • each has a specific model: “Scion xB” , “Toyota Matrix” • but performs the same action: “drive” ...
An Overview of MiniJava - Stanford Computer Science
... significant changes to the language itself, along with a completely redesigned event model and a wide variety of additional packages and classes. Such changes have a profound effect on education. The rapid changes make it difficult to develop reusable materials or to write effective textbooks; many ...
... significant changes to the language itself, along with a completely redesigned event model and a wide variety of additional packages and classes. Such changes have a profound effect on education. The rapid changes make it difficult to develop reusable materials or to write effective textbooks; many ...
Java - ASE
... “Singleton is used to control the amount of created objects.” In same category beside Singleton, there is Objects Pool. Java Factory Method: Where to use & benefits Connect parallel class hierarchies. A class wants its subclasses to specify the object. A class cannot anticipate its subclas ...
... “Singleton is used to control the amount of created objects.” In same category beside Singleton, there is Objects Pool. Java Factory Method: Where to use & benefits Connect parallel class hierarchies. A class wants its subclasses to specify the object. A class cannot anticipate its subclas ...
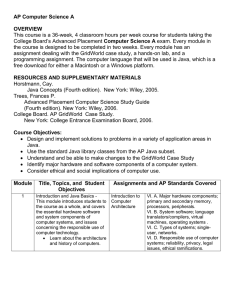
Kennesaw State University: AP Computer Science A
... III. A. 3. Testing: perform integration testing. III. C. Understand and modify existing code. II. B. 2. Programming constructs; Declaration, constants, variables, and classes. II. C. Java library classes. III. H. 1. Numerical representations and limits; representation of numbers in different bases. ...
... III. A. 3. Testing: perform integration testing. III. C. Understand and modify existing code. II. B. 2. Programming constructs; Declaration, constants, variables, and classes. II. C. Java library classes. III. H. 1. Numerical representations and limits; representation of numbers in different bases. ...
pptx
... // create Scanner to obtain input from command window Scanner input = new Scanner( System.in ); // read the first integer System.out.print("Enter first integer:"); number1 = input.nextInt(); // read the second integer System.out.print("Enter second integer:"); number2 = input.nextInt(); ...
... // create Scanner to obtain input from command window Scanner input = new Scanner( System.in ); // read the first integer System.out.print("Enter first integer:"); number1 = input.nextInt(); // read the second integer System.out.print("Enter second integer:"); number2 = input.nextInt(); ...
Java set 1
... – Now used to create web pages with interactive content, enhance web servers, applications for consumer devices (pagers, cell phones)... ...
... – Now used to create web pages with interactive content, enhance web servers, applications for consumer devices (pagers, cell phones)... ...
Evaluation of C# Language
... wrapping it up in a little box, which can then be treated like an object. Unboxing simply reverses this process. This concept is important to the earlier point that “every non-pointer type in C# is convertible to an object” (Lippert). As mentioned earlier, value types also include struct and enum ty ...
... wrapping it up in a little box, which can then be treated like an object. Unboxing simply reverses this process. This concept is important to the earlier point that “every non-pointer type in C# is convertible to an object” (Lippert). As mentioned earlier, value types also include struct and enum ty ...
1-16 - AD Book Enterprises
... • A OOP program has objects that can perform actions on other objects. • EX: – newspaper • editor, researcher, writer, layout designer ...
... • A OOP program has objects that can perform actions on other objects. • EX: – newspaper • editor, researcher, writer, layout designer ...
Chapter 12
... All of the basic properties of JButton and JMenuItem are inherited from AbstractButton. JButton and JMenuItem are similar because they are derived from the same abstract class. Since AbstractButton is an abstract class, no objects of that class can be made. The purpose of the AbstractButton class is ...
... All of the basic properties of JButton and JMenuItem are inherited from AbstractButton. JButton and JMenuItem are similar because they are derived from the same abstract class. Since AbstractButton is an abstract class, no objects of that class can be made. The purpose of the AbstractButton class is ...
Java_01
... Reserved Words Reserved words or keywords are words that have a specific meaning to the compiler and cannot be used for other purposes in the program. For example, when the compiler sees the word class, it understands that the word after class is the name for the class. Other reserved words in Exam ...
... Reserved Words Reserved words or keywords are words that have a specific meaning to the compiler and cannot be used for other purposes in the program. For example, when the compiler sees the word class, it understands that the word after class is the name for the class. Other reserved words in Exam ...
ppt
... Class class = this.getClass(); URL url = class.getResource("beep.au"); AudioClip audioClip = Applet.newAudioClip(url); Liang, Introduction to Java Programming, Sixth Edition, (c) 2007 Pearson Education, Inc. All ...
... Class class = this.getClass(); URL url = class.getResource("beep.au"); AudioClip audioClip = Applet.newAudioClip(url); Liang, Introduction to Java Programming, Sixth Edition, (c) 2007 Pearson Education, Inc. All ...
What is a Computer?
... – Now used to create web pages with interactive content, enhance web servers, applications for consumer devices (pagers, cell phones)... ...
... – Now used to create web pages with interactive content, enhance web servers, applications for consumer devices (pagers, cell phones)... ...
Introduction to JAVA
... A file having a name same as the class name should be used to save the program. The extension of this file is ”.java”. “MyFirstprogram.java”. Compiling a Java program : Call the Java compiler javac The Java compiler generates a file called ” MyFirstprogram.class” (the bytecode). ...
... A file having a name same as the class name should be used to save the program. The extension of this file is ”.java”. “MyFirstprogram.java”. Compiling a Java program : Call the Java compiler javac The Java compiler generates a file called ” MyFirstprogram.class” (the bytecode). ...
Dr Java has a definitions pane
... Java Programming Environment .java files compiled into a .class files, called bytecode. This is run on a JVM (Java Virtual Machine) such as Sun’s Hotspot. The bytecode is a standardized portable binary format. Multiple .class files can be packaged together into a .jar (Java archive). The JVM runtim ...
... Java Programming Environment .java files compiled into a .class files, called bytecode. This is run on a JVM (Java Virtual Machine) such as Sun’s Hotspot. The bytecode is a standardized portable binary format. Multiple .class files can be packaged together into a .jar (Java archive). The JVM runtim ...



![Kapitel8[1]](http://s1.studyres.com/store/data/008583971_1-aafd1fbca205779dfcc4f84523255c4a-300x300.png)