FinalRevision File - Dr. Manal Helal Moodle Site
... D) Overloading a method is to provide more than one method with the same name but with different signatures to distinguish them. E) It is a compilation error if two methods differ only in return type in the same class. ...
... D) Overloading a method is to provide more than one method with the same name but with different signatures to distinguish them. E) It is a compilation error if two methods differ only in return type in the same class. ...
Kapitel8[1]
... Changing the way of designing distributed applications • Communication oriented design: FIRST design the communication protocol for the distributed system and then the program is developed accordingly • Application oriented design: Develop the application as if everything were locally and then divid ...
... Changing the way of designing distributed applications • Communication oriented design: FIRST design the communication protocol for the distributed system and then the program is developed accordingly • Application oriented design: Develop the application as if everything were locally and then divid ...
Java Programming
... Problems with Multiline Comments • Forgetting to terminate a multiline comment may cause the compiler to ignore part of a program: System.out.print("My "); /* forgot to close this comment... System.out.print("cat "); System.out.print("has "); /* so it ends here */ System.out.println("fleas"); ...
... Problems with Multiline Comments • Forgetting to terminate a multiline comment may cause the compiler to ignore part of a program: System.out.print("My "); /* forgot to close this comment... System.out.print("cat "); System.out.print("has "); /* so it ends here */ System.out.println("fleas"); ...
11slide_Exception_Handling
... java –ea AssertionDemo Assertions can be selectively enabled or disabled at class level or package level. The disable switch is – disableassertions or –da for short. For example, the following command enables assertions in package package1 and disables assertions in class Class1. java –ea:package1 – ...
... java –ea AssertionDemo Assertions can be selectively enabled or disabled at class level or package level. The disable switch is – disableassertions or –da for short. For example, the following command enables assertions in package package1 and disables assertions in class Class1. java –ea:package1 – ...
JAVA Database Connectivity (JDBC)
... JAVA Database Connectivity (JDBC) JDBC lets Java programmers connect to a database, query it or update it using SQL. Java and JDBC have an essential advantage over other database programming environments since the programs developed with this technology are platform-independent and vendorindepen ...
... JAVA Database Connectivity (JDBC) JDBC lets Java programmers connect to a database, query it or update it using SQL. Java and JDBC have an essential advantage over other database programming environments since the programs developed with this technology are platform-independent and vendorindepen ...
PowerPoint Presentation - Service Oriented Architecture
... Prerequisites to OOP Text Vs. Binary Why is the binary numbering system used? For much the same reason that we all use base 10 for arithmetic. The algorithms are easy to learn. Try doing long division with Roman numerals. It’s simple to build machines to add and multiply and so on if the numbering ...
... Prerequisites to OOP Text Vs. Binary Why is the binary numbering system used? For much the same reason that we all use base 10 for arithmetic. The algorithms are easy to learn. Try doing long division with Roman numerals. It’s simple to build machines to add and multiply and so on if the numbering ...
slides16prime
... We can't actually write one bit-at-a-time. We can't really write one char at a time either. Output and input are buffered,minimize memory accesses and disk accesses Why do we care about this when we talk about data structures and algorithms? • Where does data come from? ...
... We can't actually write one bit-at-a-time. We can't really write one char at a time either. Output and input are buffered,minimize memory accesses and disk accesses Why do we care about this when we talk about data structures and algorithms? • Where does data come from? ...
week03topics
... Example: JUnit test method. Upon doing Run Tests a green checkmark indicates successful test, a red X indicates that test failed. ...
... Example: JUnit test method. Upon doing Run Tests a green checkmark indicates successful test, a red X indicates that test failed. ...
Week 3 presentation
... • The classes and methods of the Java library are listed in the API documentation (application programming interface) • The API documentation can be found on the web at http://java.sun.com • The API for each class starts out with a purpose section, then summary tables for the constructors and method ...
... • The classes and methods of the Java library are listed in the API documentation (application programming interface) • The API documentation can be found on the web at http://java.sun.com • The API for each class starts out with a purpose section, then summary tables for the constructors and method ...
The scope of local v..
... • The second definition of the variable with the same name r takes places inside the inner scope • From what we have learned above, the first variable r is also accessible inside the inner scope • Therefore, there are 2 different variables with the same name (r) inside the inner scope • Houston, we ...
... • The second definition of the variable with the same name r takes places inside the inner scope • From what we have learned above, the first variable r is also accessible inside the inner scope • Therefore, there are 2 different variables with the same name (r) inside the inner scope • Houston, we ...
Exceptions
... Errors are system errors, such as memory exhaustion. Programmers should not attempt to handle these. Runtime exceptions are programming errors, such as a bad cast, an out-ofbounds array access, or a null pointer access. I/O exceptions occur when bad things happen to an otherwise good program, such a ...
... Errors are system errors, such as memory exhaustion. Programmers should not attempt to handle these. Runtime exceptions are programming errors, such as a bad cast, an out-ofbounds array access, or a null pointer access. I/O exceptions occur when bad things happen to an otherwise good program, such a ...
No Slide Title
... • If the compiler doesn’t find any errors in the program, it creates a class file containing bytecode instructions. This file will have the same name as the program but with .class as the extension. • To run a program, use the java command, which executes the Java interpreter. • java requires that t ...
... • If the compiler doesn’t find any errors in the program, it creates a class file containing bytecode instructions. This file will have the same name as the program but with .class as the extension. • To run a program, use the java command, which executes the Java interpreter. • java requires that t ...
list of zoo animals
... • Most students are helpless without the design recipe • The templates provide the basic structure of solutions • The final programs are < 20 lines of ...
... • Most students are helpless without the design recipe • The templates provide the basic structure of solutions • The final programs are < 20 lines of ...
list of zoo animals
... • Most students are helpless without the design recipe • The templates provide the basic structure of solutions • The final programs are < 20 lines of ...
... • Most students are helpless without the design recipe • The templates provide the basic structure of solutions • The final programs are < 20 lines of ...
What`s in store in CS1101?
... System.out.print("What is your name? "); String name = scanner.next(); System.out.println("Hi " + name + "."); System.out.println("Welcome to CS1101!\n"); ...
... System.out.print("What is your name? "); String name = scanner.next(); System.out.println("Hi " + name + "."); System.out.println("Welcome to CS1101!\n"); ...
ppt - kaist
... out.write(data); is the same class as the } catch (FileNotFoundException e1) { thrown object or an System.err.println(“Can’t open a file.”); ancestor of it } catch (IOException e2) { System.err.println(“Can’t read or write.”); Specify code that is to be ...
... out.write(data); is the same class as the } catch (FileNotFoundException e1) { thrown object or an System.err.println(“Can’t open a file.”); ancestor of it } catch (IOException e2) { System.err.println(“Can’t read or write.”); Specify code that is to be ...
COS 333: Advanced Programming Techniques Robert M. Dondero, Ph.D.
... Advanced Programming Techniques: The practice of programming. Emphasis is on the development of real programs, writing code but also assessing tradeoffs, choosing among design alternatives, debugging and testing, and improving performance. Issues include compatibility, robustness, and reliability, w ...
... Advanced Programming Techniques: The practice of programming. Emphasis is on the development of real programs, writing code but also assessing tradeoffs, choosing among design alternatives, debugging and testing, and improving performance. Issues include compatibility, robustness, and reliability, w ...
Aug16_2010 - Computer Science
... This course is intended to provide a sound understanding of the concepts, models and practice involved in designing concurrent software. The emphasis on principles and concepts provides a thorough understanding of both the problems and the ...
... This course is intended to provide a sound understanding of the concepts, models and practice involved in designing concurrent software. The emphasis on principles and concepts provides a thorough understanding of both the problems and the ...
Presentation3
... The client and server can then send bytes to each other over the pipe, and all bytes sent arrive at the other side in order. With connectionSocket established, the server can continue to listen for other requests from other clients for the application using welcomeSocket. (This version of the progra ...
... The client and server can then send bytes to each other over the pipe, and all bytes sent arrive at the other side in order. With connectionSocket established, the server can continue to listen for other requests from other clients for the application using welcomeSocket. (This version of the progra ...
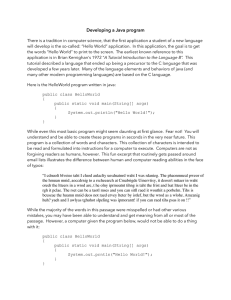
Developing a Java program
... Similarly, you can have the compiler translate your source code to run on a Pentium processor, but a Cray processor will not be able to make sense of the Pentium translation. You can run a second translation, and translate your source code to the Cray machine code if you want, but if all you’ve don ...
... Similarly, you can have the compiler translate your source code to run on a Pentium processor, but a Cray processor will not be able to make sense of the Pentium translation. You can run a second translation, and translate your source code to the Cray machine code if you want, but if all you’ve don ...
Multithreading
... resources usually won’t cause any problem, such as the programming exercise in workshop 4. When threads share access to a common object, they can conflict with each other. Consider several threads trying to access the same bank account, some trying to deposit and other to withdraw: these activities ...
... resources usually won’t cause any problem, such as the programming exercise in workshop 4. When threads share access to a common object, they can conflict with each other. Consider several threads trying to access the same bank account, some trying to deposit and other to withdraw: these activities ...
Java Programming Workshop - Allan Callaghan
... else { //we are off the track //if we are going to fast make our max speed very slow if (player1_xspeed> 0.05) {player1_xspeed=0.05;} if (player1_yspeed> 0.05) {player1_yspeed=0.05;} if (player1_xspeed<-0.05) {player1_xspeed=-0.05;} if (player1_yspeed<-0.05) {player1_yspeed=-0.05;} ...
... else { //we are off the track //if we are going to fast make our max speed very slow if (player1_xspeed> 0.05) {player1_xspeed=0.05;} if (player1_yspeed> 0.05) {player1_yspeed=0.05;} if (player1_xspeed<-0.05) {player1_xspeed=-0.05;} if (player1_yspeed<-0.05) {player1_yspeed=-0.05;} ...
Book Chapter 1
... single thread of control. A concurrent program has multiple threads of control allowing it perform multiple computations in parallel and to control multiple external activities which occur at the same time. Concurrency: introduction ...
... single thread of control. A concurrent program has multiple threads of control allowing it perform multiple computations in parallel and to control multiple external activities which occur at the same time. Concurrency: introduction ...
Chapter 22
... In Java 2, Vector is the same as ArrayList, except that Vector contains the synchronized methods for accessing and modifying the vector. None of the new collection data structures introduced so far are synchronized. If synchronization is required, you can use the synchronized versions of the collect ...
... In Java 2, Vector is the same as ArrayList, except that Vector contains the synchronized methods for accessing and modifying the vector. None of the new collection data structures introduced so far are synchronized. If synchronization is required, you can use the synchronized versions of the collect ...
Binary Search Trees
... Useful for ordering items according to priority Guarantees logarithmic insertions and removals Useful for implementing priority queues ...
... Useful for ordering items according to priority Guarantees logarithmic insertions and removals Useful for implementing priority queues ...
![Kapitel8[1]](http://s1.studyres.com/store/data/008583971_1-aafd1fbca205779dfcc4f84523255c4a-300x300.png)