Linked list
... APIs are usually feature rich. Study purposes of classes and interfaces. Study hierarchical class and interface structures. Study methods available. ...
... APIs are usually feature rich. Study purposes of classes and interfaces. Study hierarchical class and interface structures. Study methods available. ...
Korat: Automated Testing Based on Java Predicates
... reachable from root, keeping track of the visited nodes to detect cycles. (The method add from java.util.Set returns false if the argument already exists in the set.) ...
... reachable from root, keeping track of the visited nodes to detect cycles. (The method add from java.util.Set returns false if the argument already exists in the set.) ...
Korat: Automated Testing Based on Java Predicates (ISSTA 2002)
... reachable from root, keeping track of the visited nodes to detect cycles. (The method add from java.util.Set returns false if the argument already exists in the set.) ...
... reachable from root, keeping track of the visited nodes to detect cycles. (The method add from java.util.Set returns false if the argument already exists in the set.) ...
OpenVMS Distributed Lock Manager Performance
... which you may have been trying to off-load work. In some cases, node may thus be saturated and unable to initiate lock remastering Programs running locally on existing lock master can generate so many requests that tree won’t move because you can’t generate nearly as many lock requests remotely ...
... which you may have been trying to off-load work. In some cases, node may thus be saturated and unable to initiate lock remastering Programs running locally on existing lock master can generate so many requests that tree won’t move because you can’t generate nearly as many lock requests remotely ...
Linked List - MHS Comp Sci
... The actual implementation of which is left to the specific data structure As for the Iterator and ListIterator Interfaces, we will discuss these shortly The List Interface requires you implement a Size and an Add Behavior ...
... The actual implementation of which is left to the specific data structure As for the Iterator and ListIterator Interfaces, we will discuss these shortly The List Interface requires you implement a Size and an Add Behavior ...
Logarithmic data structures for multicores
... architectures so to scale to large datasets, however it does not avoid hotspots and its performance degrades under contention. We tried to understand this phenomenon by comparing the performance of Crain’s and Fraser’s skip lists on the publicly available Synchrobench benchmark suite. For the sake o ...
... architectures so to scale to large datasets, however it does not avoid hotspots and its performance degrades under contention. We tried to understand this phenomenon by comparing the performance of Crain’s and Fraser’s skip lists on the publicly available Synchrobench benchmark suite. For the sake o ...
Software Engineering with Reusable Components
... The J2EE Architectural Solution The EJB Architectural Solution EJB Programming ...
... The J2EE Architectural Solution The EJB Architectural Solution EJB Programming ...
Scalable Address Spaces Using RCU Balanced Trees - PDOS-MIT
... RCU for kernel data structures to improve scalability [16], but applying RCU is often not straightforward: RCU requires that mutating operations update only one pointer and that readers read each pointer at most once. This makes the update appear atomic: a reader will appear to execute either entire ...
... RCU for kernel data structures to improve scalability [16], but applying RCU is often not straightforward: RCU requires that mutating operations update only one pointer and that readers read each pointer at most once. This makes the update appear atomic: a reader will appear to execute either entire ...
Scalable Address Spaces Using RCU Balanced Trees
... RCU for kernel data structures to improve scalability [16], but applying RCU is often not straightforward: RCU requires that mutating operations update only one pointer and that readers read each pointer at most once. This makes the update appear atomic: a reader will appear to execute either entire ...
... RCU for kernel data structures to improve scalability [16], but applying RCU is often not straightforward: RCU requires that mutating operations update only one pointer and that readers read each pointer at most once. This makes the update appear atomic: a reader will appear to execute either entire ...
Hashing
... compute the number of collisions. If there are more than n collisions, repeat. For each cell i,if ni>1, choose a random hash function hi from H(p,ni2). If there are any collisions, repeat. Expected construction time – O(n) Worst case search time – O(1) ...
... compute the number of collisions. If there are more than n collisions, repeat. For each cell i,if ni>1, choose a random hash function hi from H(p,ni2). If there are any collisions, repeat. Expected construction time – O(n) Worst case search time – O(1) ...
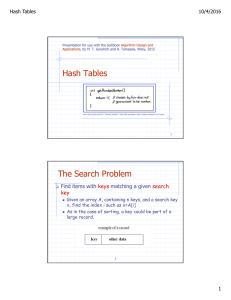
Hash Tables The Search Problem
... There is a class of hash functions we can use, which involve simple table lookups, known as tabulation-based hashing. We can initialize d tables, T1, T2, . . . , Td, of size M each, so that each Ti[j] is a uniformly chosen independent random number in the range [0,N − 1]. We then can compute the has ...
... There is a class of hash functions we can use, which involve simple table lookups, known as tabulation-based hashing. We can initialize d tables, T1, T2, . . . , Td, of size M each, so that each Ti[j] is a uniformly chosen independent random number in the range [0,N − 1]. We then can compute the has ...
Data Structures So Far
... /** Replaces the element at index I with e, returning the previous element at i. */ ...
... /** Replaces the element at index I with e, returning the previous element at i. */ ...
Dictionaries and Hash Tables
... insertions and removals on a hash table take O(n) time The worst case occurs when all the keys inserted into the dictionary collide The load factor a = n/N affects the performance of a hash table Assuming that the hash values are like random numbers, it can be shown that the expected number of probe ...
... insertions and removals on a hash table take O(n) time The worst case occurs when all the keys inserted into the dictionary collide The load factor a = n/N affects the performance of a hash table Assuming that the hash values are like random numbers, it can be shown that the expected number of probe ...
Programming the Web Server Robert M. Dondero, Ph.D. Princeton University 1
... Use key to populate $_SESSION with saved "name=value" state pairs Allow PHP code to use/modify $_SESSION Pass "PHPSESSID=key" cookie to browser ...
... Use key to populate $_SESSION with saved "name=value" state pairs Allow PHP code to use/modify $_SESSION Pass "PHPSESSID=key" cookie to browser ...
Introduction to JSON (JavaScript Object Notation)
... • JSON objects are typed while XML data is typeless > JSON types: string, number, array, boolean, > XML data are all string ...
... • JSON objects are typed while XML data is typeless > JSON types: string, number, array, boolean, > XML data are all string ...
public boolean - University of Pittsburgh
... • Instance data and instance methods Access restrictions (i.e. data hiding through private declarations) allow the implementation details of the data type to be hidden from a user • public, protected and private allow various levels of accessibility ...
... • Instance data and instance methods Access restrictions (i.e. data hiding through private declarations) allow the implementation details of the data type to be hidden from a user • public, protected and private allow various levels of accessibility ...
GroveX10Overview - The X10 Programming Language
... Commodity cluster != MPP system but the programming model problem is highly similar © 2009 IBM Corporation ...
... Commodity cluster != MPP system but the programming model problem is highly similar © 2009 IBM Corporation ...
List - Hkbu.edu.hk
... Maximum(p): return the item with the highest priority in priority queue p ExtractMax(p): return and remove the item with the highest priority in p ...
... Maximum(p): return the item with the highest priority in priority queue p ExtractMax(p): return and remove the item with the highest priority in p ...
public boolean - Pitt Computer Science
... • Default methods are allowed • Static methods are allowed • No instance data is allowed • Regular instance methods have no bodies • Interface itself cannot be instantiated Any Java class (no matter what its inheritance) can implement an interface by implementing the methods defined in it A given ...
... • Default methods are allowed • Static methods are allowed • No instance data is allowed • Regular instance methods have no bodies • Interface itself cannot be instantiated Any Java class (no matter what its inheritance) can implement an interface by implementing the methods defined in it A given ...
CS 180 Problem Solving and OO Programming Fall 2010
... Iteration suffices for most problems that arise in practice. However, in some cases recursion allows compact and quick solution. An example follows. ...
... Iteration suffices for most problems that arise in practice. However, in some cases recursion allows compact and quick solution. An example follows. ...
JavaHTP6e_17
... To form linked data structures using references, selfreferential classes and recursion. The type-wrapper classes that enable programs to process primitive data values as objects. To use autoboxing to convert a primitive value to an object of the corresponding type-wrapper class. To use auto- ...
... To form linked data structures using references, selfreferential classes and recursion. The type-wrapper classes that enable programs to process primitive data values as objects. To use autoboxing to convert a primitive value to an object of the corresponding type-wrapper class. To use auto- ...
CBPQ: High Performance Lock-Free Priority Queue
... The CBPQ data structure is composed of a list of chunks. Each chunk has a range of keys associated with it, and all CBPQ entries with keys in this range are located in this chunk. The ranges do not intersect and the chunks are sorted by the ranges’ values. To improve the search of a specific range, ...
... The CBPQ data structure is composed of a list of chunks. Each chunk has a range of keys associated with it, and all CBPQ entries with keys in this range are located in this chunk. The ranges do not intersect and the chunks are sorted by the ranges’ values. To improve the search of a specific range, ...
This comprehensive guide shows you how to master the most... changes to Java since it was first released. Generics and...
... appropriate. The Java Collections Framework provides reusable interfaces and implementations for a number of common collection types, including lists, sets, queues, and maps. There is also a framework for comparing values, which is useful in sorting or building ordered trees. (Of course, not all pro ...
... appropriate. The Java Collections Framework provides reusable interfaces and implementations for a number of common collection types, including lists, sets, queues, and maps. There is also a framework for comparing values, which is useful in sorting or building ordered trees. (Of course, not all pro ...
Datastructures1:Lists, Sets and Hashing
... • If there is no collision, contains() operates in O(1) • If the set contains elements having the same hashcode, there is a collision. Being dupmax the maximum value of elements having the same hash code, contains() operates in O(dupmax) • If dupmax is near n, there is no increase in speed, since co ...
... • If there is no collision, contains() operates in O(1) • If the set contains elements having the same hashcode, there is a collision. Being dupmax the maximum value of elements having the same hash code, contains() operates in O(dupmax) • If dupmax is near n, there is no increase in speed, since co ...
Chapter 14
... because the second catch clause can never be used. The code contained in the (optional) finally clause is executed whether an exception is thrown in the try construct or not. This is useful for “cleanup” code (closing files, other freeing of resources, ...) that must always be executed. Binding of e ...
... because the second catch clause can never be used. The code contained in the (optional) finally clause is executed whether an exception is thrown in the try construct or not. This is useful for “cleanup” code (closing files, other freeing of resources, ...) that must always be executed. Binding of e ...