Streams and File I/O
... ISBN 0136091113 © 2009 Pearson Education, Inc., Upper Saddle River, NJ. All Rights Reserved ...
... ISBN 0136091113 © 2009 Pearson Education, Inc., Upper Saddle River, NJ. All Rights Reserved ...
TCP/UDP Sockets
... • Write routines to print out sockaddrs • Use trace, strace, ptrace, truss, etc ...
... • Write routines to print out sockaddrs • Use trace, strace, ptrace, truss, etc ...
Intro to Web Programming, PhP, and Flash
... - This is where you include the debreifing for your experiments (it can be blank…but has to exist). 6. PhP: .php parser - This is a program I wrote that converts Flash data into a .csv data file - You never have to touch this file…just make sure it’s there. Flash Workshop - Intro to Web Programming, ...
... - This is where you include the debreifing for your experiments (it can be blank…but has to exist). 6. PhP: .php parser - This is a program I wrote that converts Flash data into a .csv data file - You never have to touch this file…just make sure it’s there. Flash Workshop - Intro to Web Programming, ...
PS14
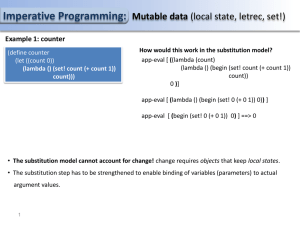
... (define make-player (lambda (total) (letrec ((steps 0) (get-steps (lambda () steps)) (set-steps (lambda () (set! steps (+ steps 1)))) (get-total (lambda () total)) (set-total (lambda (piece) (let ((piece-value (cond ( (eq? piece 'queen) 9) ((eq? piece 'rook) 5) ((eq? piece 'bishop) 3) ((eq? piece 'k ...
... (define make-player (lambda (total) (letrec ((steps 0) (get-steps (lambda () steps)) (set-steps (lambda () (set! steps (+ steps 1)))) (get-total (lambda () total)) (set-total (lambda (piece) (let ((piece-value (cond ( (eq? piece 'queen) 9) ((eq? piece 'rook) 5) ((eq? piece 'bishop) 3) ((eq? piece 'k ...
Recursion and Implementation of Functions
... – A last-in, first-out data structure provided by the operating system for each running program – For temporary storage of automatic variables, arguments, function results, and other stuff ...
... – A last-in, first-out data structure provided by the operating system for each running program – For temporary storage of automatic variables, arguments, function results, and other stuff ...
TCP/UDP Sockets
... • no need to call bind first, the O.S. will take care of assigning the local endpoint address – TCP port number, IP address CPE 401/601 Lecture 11 : TCP Socket Programming ...
... • no need to call bind first, the O.S. will take care of assigning the local endpoint address – TCP port number, IP address CPE 401/601 Lecture 11 : TCP Socket Programming ...
What is the use of java? - Entrance
... debugging, and documenting your applications. The main tools used are the Javac compiler, the java launcher, and the javadoc documentation tool. Application Programming Interface (API): The API provides the core functionality of the Java programming language. It gives a wide collection of useful cla ...
... debugging, and documenting your applications. The main tools used are the Javac compiler, the java launcher, and the javadoc documentation tool. Application Programming Interface (API): The API provides the core functionality of the Java programming language. It gives a wide collection of useful cla ...
Object-Oriented Programming - Department Of Computer Science
... the virtual function table Java: an object pointer consists of a pointer to the object and a pointer to the dispatch table ...
... the virtual function table Java: an object pointer consists of a pointer to the object and a pointer to the dispatch table ...
Proof-Outline Logic. - Faculty of Engineering and Applied Science
... Here are some small examples of Hoare triples. In each case the variables should be understood to be integers {x + 1 = y} x := x + 1 {x = y} Is this triple correct? (Answer for yourself before reading on...) If initially y is x + 1 and we change x to x + 1, then finally both x and y will equal the o ...
... Here are some small examples of Hoare triples. In each case the variables should be understood to be integers {x + 1 = y} x := x + 1 {x = y} Is this triple correct? (Answer for yourself before reading on...) If initially y is x + 1 and we change x to x + 1, then finally both x and y will equal the o ...
Java Prerequisites
... In the first part, we can select our projects, files and libraries. For beginners, it is better not to change anything in this part. Second part is of much better use. Here we can check variables, their values, attributes of classes etc. Now, you cannot understand it, but it will change soon. The th ...
... In the first part, we can select our projects, files and libraries. For beginners, it is better not to change anything in this part. Second part is of much better use. Here we can check variables, their values, attributes of classes etc. Now, you cannot understand it, but it will change soon. The th ...
Examples - Department of Computer and Information Science
... Top-Down Programming, also called functional decomposition, uses functions to hide details of an algorithm inside the function. In the prior example, main called calculate_triangular_number without regards to how the function is implemented. You can write a call to calculate_triangular_number withou ...
... Top-Down Programming, also called functional decomposition, uses functions to hide details of an algorithm inside the function. In the prior example, main called calculate_triangular_number without regards to how the function is implemented. You can write a call to calculate_triangular_number withou ...
CSE244 Compiler (a.k.a. Programming Language Translation)
... – First Pass: all identifiers are assigned to memory addresses (0offset) – e.g. substitute 0 for a, and 4 for b – Second Pass: produce relocatable machine code: ...
... – First Pass: all identifiers are assigned to memory addresses (0offset) – e.g. substitute 0 for a, and 4 for b – Second Pass: produce relocatable machine code: ...
Sexy types in action - Indiana University Computer Science
... gives rise to a parametricity law, an equation satisfied by any value expressible as a λ-term and any value in a parametric model (Reynolds 1983; Wadler 1989, 2004). As we will see below, useful parametricity laws tend to arise from higher-rank polymorphism. ...
... gives rise to a parametricity law, an equation satisfied by any value expressible as a λ-term and any value in a parametric model (Reynolds 1983; Wadler 1989, 2004). As we will see below, useful parametricity laws tend to arise from higher-rank polymorphism. ...
“while” loop
... Repetition - Cont. • The number of repetitions is controlled by changing the limit value for the loop counter - “i” in the example on the previous slide. • That example had i increasing by one each time. The loop counter was being incremented by one. • It could have been incremented by some other v ...
... Repetition - Cont. • The number of repetitions is controlled by changing the limit value for the loop counter - “i” in the example on the previous slide. • That example had i increasing by one each time. The loop counter was being incremented by one. • It could have been incremented by some other v ...
ASP - User pages
... A script is a series of commands or instructions. Script command instructs the web server to perform an action. VBScript is similar to Visual Basic and Visual Basic for Application (VBA). Server Side Programming ASP ...
... A script is a series of commands or instructions. Script command instructs the web server to perform an action. VBScript is similar to Visual Basic and Visual Basic for Application (VBA). Server Side Programming ASP ...
Lecture10
... Makes the subnet structure of a network invisible outside the organization’s private network. External Internet does not need to know internal subnet structure. To reach any host, external routers only need to know the path to the “gateway” router for the entire subnetwork. Subnetting reduces the si ...
... Makes the subnet structure of a network invisible outside the organization’s private network. External Internet does not need to know internal subnet structure. To reach any host, external routers only need to know the path to the “gateway” router for the entire subnetwork. Subnetting reduces the si ...
Chapter 1
... • In the distant past, programmers wrote programs in machine language. • Programmers developed higher level programming languages to make things easier. • The first of these was assembler. • Assembler made things easier but was also processor dependent. ...
... • In the distant past, programmers wrote programs in machine language. • Programmers developed higher level programming languages to make things easier. • The first of these was assembler. • Assembler made things easier but was also processor dependent. ...
Functional Programming
... inferencing process is used to produce results. • Logic programs are declarative rather than procedural. • Programs in logic programming languages are collections of facts and rules. • Programming that uses a form of symbolic logic as a programming languages is often called logic programming. • Exam ...
... inferencing process is used to produce results. • Logic programs are declarative rather than procedural. • Programs in logic programming languages are collections of facts and rules. • Programming that uses a form of symbolic logic as a programming languages is often called logic programming. • Exam ...
Chapter 17
... binary file consists of a sequence of bits. For example, the decimal integer 199 is stored as the sequence of three characters: '1', '9', '9' in a text file and the same integer is stored as a byte-type value C7 in a binary file, because decimal 199 equals to hex C7. Liang, Introduction to Java Prog ...
... binary file consists of a sequence of bits. For example, the decimal integer 199 is stored as the sequence of three characters: '1', '9', '9' in a text file and the same integer is stored as a byte-type value C7 in a binary file, because decimal 199 equals to hex C7. Liang, Introduction to Java Prog ...
17slide
... binary file consists of a sequence of bits. For example, the decimal integer 199 is stored as the sequence of three characters: '1', '9', '9' in a text file and the same integer is stored as a byte-type value C7 in a binary file, because decimal 199 equals to hex C7. Liang, Introduction to Java Prog ...
... binary file consists of a sequence of bits. For example, the decimal integer 199 is stored as the sequence of three characters: '1', '9', '9' in a text file and the same integer is stored as a byte-type value C7 in a binary file, because decimal 199 equals to hex C7. Liang, Introduction to Java Prog ...
PowerPoint
... • Compiling miniTAJS takes 35 seconds – 4500 lines of code – 113 classes + 40 objects = 580 .class files ...
... • Compiling miniTAJS takes 35 seconds – 4500 lines of code – 113 classes + 40 objects = 580 .class files ...
12~Chapter 12_Concur.. - Programming Assignment 0
... locations are atomic (note that this is not trivial; memory and/or busses must be designed to arbitrate and serialize concurrent accesses) • In early machines, reads and writes of individual memory locations were all that was atomic ...
... locations are atomic (note that this is not trivial; memory and/or busses must be designed to arbitrate and serialize concurrent accesses) • In early machines, reads and writes of individual memory locations were all that was atomic ...
Structured programming

Structured programming is a programming paradigm aimed at improving the clarity, quality, and development time of a computer program by making extensive use of subroutines, block structures and for and while loops—in contrast to using simple tests and jumps such as the goto statement which could lead to ""spaghetti code"" which is difficult both to follow and to maintain.It emerged in the 1960s—particularly from a famous letter, Go To Statement Considered Harmful.—and was bolstered theoretically by the structured program theorem, and practically by the emergence of languages such as ALGOL with suitably rich control structures.