On the construction of operating systems for the - UvA-DARE
... of sitting in the back of our car with a pile of big boxes. I am convinced that this was a turning point in my life, as without this machine, I would not have ended up where I am today; completing my PhD thesis on a topic in Computer Science. The machine sparked my enthusiasm and fascination for com ...
... of sitting in the back of our car with a pile of big boxes. I am convinced that this was a turning point in my life, as without this machine, I would not have ended up where I am today; completing my PhD thesis on a topic in Computer Science. The machine sparked my enthusiasm and fascination for com ...
9 th Edition
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
Module 7: Process Synchronization
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
Virtualization: State of the Art
... Alliance. The material contained herein is provided on an “AS IS” basis and to the maximum extent permitted by applicable law, this material is provided AS IS AND WITH ALL FAULTS, and the authors and developers of this material and SCOPE Alliance and its members hereby disclaim all warranties and co ...
... Alliance. The material contained herein is provided on an “AS IS” basis and to the maximum extent permitted by applicable law, this material is provided AS IS AND WITH ALL FAULTS, and the authors and developers of this material and SCOPE Alliance and its members hereby disclaim all warranties and co ...
ch4
... Makes it easier to support multithreaded applications Different from multiprocessing, multiprogramming, multitasking Concurrency (multithreading) is useful for: improving program structure Improving responsiveness handling concurrent events (e.g., web requests) building parallel programs ...
... Makes it easier to support multithreaded applications Different from multiprocessing, multiprogramming, multitasking Concurrency (multithreading) is useful for: improving program structure Improving responsiveness handling concurrent events (e.g., web requests) building parallel programs ...
FreeBSD for the Linux user
... • It is possible to maintain a local mirror of the complete CVS tree • You can 'tag' a local copy of the tree as buildable, and then selectively include changes from FreeBSD ...
... • It is possible to maintain a local mirror of the complete CVS tree • You can 'tag' a local copy of the tree as buildable, and then selectively include changes from FreeBSD ...
The APIC Approach to High Performance Network Interface Design
... status registers, the software reset register, etc. There is one set of per-connection registers for each connection supported by the APIC; these hold state that varies from connection to connection, such as the connection identifier (VPI/VCI), the pacing bandwidth, etc. Protected I/O is designed to ...
... status registers, the software reset register, etc. There is one set of per-connection registers for each connection supported by the APIC; these hold state that varies from connection to connection, such as the connection identifier (VPI/VCI), the pacing bandwidth, etc. Protected I/O is designed to ...
Module 7: Process Synchronization
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
... 1. Mutual Exclusion - If process Pi is executing in its critical section, then no other processes can be executing in their critical sections 2. Progress - If no process is executing in its critical section and there exist some processes that wish to enter their critical section, then the selection ...
Section B MCA 404-AOS
... Upon activation of an interrupt , the microcontroller finishes the instruction it is executing and saves the address of the next instruction (Program Counter (PC)) on the stack. It also saves the current status of all the interrupts internally (ie not on the stack). It jumps to a fixed location in m ...
... Upon activation of an interrupt , the microcontroller finishes the instruction it is executing and saves the address of the next instruction (Program Counter (PC)) on the stack. It also saves the current status of all the interrupts internally (ie not on the stack). It jumps to a fixed location in m ...
Module 7: Process Synchronization
... the selection of the processes that will enter the critical-section next. The selection can not postponed indefinitely. 3. Bounded Waiting - A bound must exist on the number of times that other processes are allowed to enter their critical-sections after a process has made a request to enter its cri ...
... the selection of the processes that will enter the critical-section next. The selection can not postponed indefinitely. 3. Bounded Waiting - A bound must exist on the number of times that other processes are allowed to enter their critical-sections after a process has made a request to enter its cri ...
$doc.title
... It should be noted that this study is based on Linux kernel version 2.4 from an “out of the box” Linux distribution (section 8), which will be the most attractive option for many projects which do not have the knowledge or budget to modify Linux at the source code level. Special modifications of Lin ...
... It should be noted that this study is based on Linux kernel version 2.4 from an “out of the box” Linux distribution (section 8), which will be the most attractive option for many projects which do not have the knowledge or budget to modify Linux at the source code level. Special modifications of Lin ...
ch4
... kernel to inform the thread library when a user thread is about to block, and when it again becomes ready for execution When such event occurs, the kernel makes an upcall to the thread ...
... kernel to inform the thread library when a user thread is about to block, and when it again becomes ready for execution When such event occurs, the kernel makes an upcall to the thread ...
Android - Sukianti Binusian
... particular programming language and turns them into machine language or “code” that a computer’s processor uses. Programmer writes language statements in a language using an editor. File that is created contains what we called source statements. Programmer runs the appropriate language compiler, spe ...
... particular programming language and turns them into machine language or “code” that a computer’s processor uses. Programmer writes language statements in a language using an editor. File that is created contains what we called source statements. Programmer runs the appropriate language compiler, spe ...
MULTITHREADING A multithreaded program contains two or more
... Because multithreading introduces an asynchronous behavior to your programs, there must be a way for you to enforce synchronicity when you need it. For example, if you want two threads to communicate and share a complicated data structure, such as a linked list, you need some way to ensure that th ...
... Because multithreading introduces an asynchronous behavior to your programs, there must be a way for you to enforce synchronicity when you need it. For example, if you want two threads to communicate and share a complicated data structure, such as a linked list, you need some way to ensure that th ...
Operating Systems Principles and Programming More Contact
... The kernel implements a mapping of physical pages to virtual ones, different for every process ...
... The kernel implements a mapping of physical pages to virtual ones, different for every process ...
Empirical Performance Assessment Using Soft-Core Processors on Reconfigurable Hardware
... modeled and the fidelity of the underlying model itself. As a result, existing simulation models must make choices as to where they position themselves in this space. For example, very high fidelity models that approach (or achieve) cycle-accurate fidelity are constrained as to the scope of the mode ...
... modeled and the fidelity of the underlying model itself. As a result, existing simulation models must make choices as to where they position themselves in this space. For example, very high fidelity models that approach (or achieve) cycle-accurate fidelity are constrained as to the scope of the mode ...
Chapter 4: Threads
... Makes existing functions thread-safe . May be slightly less efficient than being reentrant Allows each thread to have its own copy of data Provides per-thread storage for a function Useful when you do not have control over the thread creation process (i.e., when using a thread pool) ...
... Makes existing functions thread-safe . May be slightly less efficient than being reentrant Allows each thread to have its own copy of data Provides per-thread storage for a function Useful when you do not have control over the thread creation process (i.e., when using a thread pool) ...
Kluge_Habilitation - OPUS Augsburg
... Technological advancements enable to integrate more and more processing cores on single chips. After several years of multicore processors, in the last years the first manycore processors with 64 and more cores have reached the markets. Concurrently, designers of safetycritical systems strive to int ...
... Technological advancements enable to integrate more and more processing cores on single chips. After several years of multicore processors, in the last years the first manycore processors with 64 and more cores have reached the markets. Concurrently, designers of safetycritical systems strive to int ...
Proceedings of the General Track: 2003 USENIX Annual Technical Conference
... call, counting the number of parallel requests to a component). Such probes can be implemented once, avoiding code replication across components. Application-specific optimizations: Application specializations are a well-known way of improving a particular application’s performance based on knowledg ...
... call, counting the number of parallel requests to a component). Such probes can be implemented once, avoiding code replication across components. Application-specific optimizations: Application specializations are a well-known way of improving a particular application’s performance based on knowledg ...
Transaction Processing Facility
... TPF also had its programs allocated as 381, 1055 and 4K bytes in size and each program consisted of a single record (aka segment). Therefore a comprehensive application needed many segments. With the advent of C-support, application programs were no longer limited to 4K sizes, much larger C programs ...
... TPF also had its programs allocated as 381, 1055 and 4K bytes in size and each program consisted of a single record (aka segment). Therefore a comprehensive application needed many segments. With the advent of C-support, application programs were no longer limited to 4K sizes, much larger C programs ...
The following paper was originally published in the
... In order to exploit concurrency and parallelism, operating systems like NT and Solaris further develop the notion of a process. These operating systems break the classical process into smaller sub-objects. These sub-objects are the basic entity to which the OS allocates processor time. Here we will ...
... In order to exploit concurrency and parallelism, operating systems like NT and Solaris further develop the notion of a process. These operating systems break the classical process into smaller sub-objects. These sub-objects are the basic entity to which the OS allocates processor time. Here we will ...
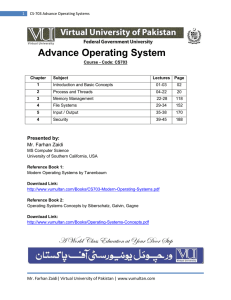
CS-703 Advance Operating Systems
... reporting etc. Transaction processing systems handle large number of small requests e.g. check processing in banks, air line reservations etc. Time-sharing systems allow multiple remote users to run jobs at the same time e.g. querying a database. OS Optimized for these tasks. Example is OS/390 • S ...
... reporting etc. Transaction processing systems handle large number of small requests e.g. check processing in banks, air line reservations etc. Time-sharing systems allow multiple remote users to run jobs at the same time e.g. querying a database. OS Optimized for these tasks. Example is OS/390 • S ...
Friendly Virtual Machines Leveraging a Feedback-Control Model for Application Adaptation
... Traditionally, efficiency is achieved by instrumenting the underlying system to avoid being overloaded (by over-stressing resources and hence operating in inefficient regions) through admission control, for example, whereas fairness is achieved through the use of potentially complex policies for schedul ...
... Traditionally, efficiency is achieved by instrumenting the underlying system to avoid being overloaded (by over-stressing resources and hence operating in inefficient regions) through admission control, for example, whereas fairness is achieved through the use of potentially complex policies for schedul ...
Design and Benchmarking of Real-Time Multiprocessor Operating
... Multiprocessor architectures, operating systems and real-time technologies are all interesting and highly advanced topics. Real-time demands inject an additional correctness criterion into computer systems. It is not just the result that is important, timing issues also have to be considered. A mult ...
... Multiprocessor architectures, operating systems and real-time technologies are all interesting and highly advanced topics. Real-time demands inject an additional correctness criterion into computer systems. It is not just the result that is important, timing issues also have to be considered. A mult ...