
PDF - Complete Book (2.43 MB)
... installed in accordance with Cisco’s installation instructions, it may cause interference with radio and television reception. This equipment has been tested and found to comply with the limits for a Class B digital device in accordance with the specifications in part 15 of the FCC rules. These spec ...
... installed in accordance with Cisco’s installation instructions, it may cause interference with radio and television reception. This equipment has been tested and found to comply with the limits for a Class B digital device in accordance with the specifications in part 15 of the FCC rules. These spec ...
cable modem - Simple Help
... These pads (or "feet") can be attached to keep the modem from sliding around on your desktop. You have 2 options for placing the pads: Option 1: Attach the pads to the four slight indentations on the back of the modem. Option 2: Attach the pads to the “rudders” on the bottom of the cable modem. Be s ...
... These pads (or "feet") can be attached to keep the modem from sliding around on your desktop. You have 2 options for placing the pads: Option 1: Attach the pads to the four slight indentations on the back of the modem. Option 2: Attach the pads to the “rudders” on the bottom of the cable modem. Be s ...
Content Analysis 1.3 Administration Guide
... Manual File Blacklist and Whitelist - As your organization identifies files that are known good or bad, you can add them to a list of manually defined file hashes to either allow or deny those files without further processing. Sandbox integration with Blue Coat's Malware Analysis, Lastline or FireEy ...
... Manual File Blacklist and Whitelist - As your organization identifies files that are known good or bad, you can add them to a list of manually defined file hashes to either allow or deny those files without further processing. Sandbox integration with Blue Coat's Malware Analysis, Lastline or FireEy ...
WiMax – Overview
... broadband access standard could supply the missing link for the “last mile” connection in wireless metropolitan area networks. Wireless broadband access is set up like cellular systems, using base stations that service a radius of several miles/kilometers. Base stations do not necessarily have to re ...
... broadband access standard could supply the missing link for the “last mile” connection in wireless metropolitan area networks. Wireless broadband access is set up like cellular systems, using base stations that service a radius of several miles/kilometers. Base stations do not necessarily have to re ...
0110/0111/0115 Access Point
... About the Intermec 0110/0111/0115 Access Points The Intermec access points are long-range, high-performance local area network (LAN) products that bridge Intermec’s 2.4 GHz radio frequency (RF) network and your wired (Ethernet or token ring) network. The access points operate at the Data Link level ...
... About the Intermec 0110/0111/0115 Access Points The Intermec access points are long-range, high-performance local area network (LAN) products that bridge Intermec’s 2.4 GHz radio frequency (RF) network and your wired (Ethernet or token ring) network. The access points operate at the Data Link level ...
TTAS tandard - TTA표준화 위원회
... it may be beneficial to still keep some traffic(e.g. VoIP flow) in the cellular access. With this IP flow mobility solution the operator can lower it data access costs while the subscriber just experiences maximized bandwidth without any service disruption or interruption. It is therefore of interes ...
... it may be beneficial to still keep some traffic(e.g. VoIP flow) in the cellular access. With this IP flow mobility solution the operator can lower it data access costs while the subscriber just experiences maximized bandwidth without any service disruption or interruption. It is therefore of interes ...
What Is a Virtual Private Network?
... What Is a Virtual Private Network? A virtual private network (VPN) allows the provisioning of private network services for an organization or organizations over a public or shared infrastructure such as the Internet or service provider backbone network. The shared service provider backbone network i ...
... What Is a Virtual Private Network? A virtual private network (VPN) allows the provisioning of private network services for an organization or organizations over a public or shared infrastructure such as the Internet or service provider backbone network. The shared service provider backbone network i ...
IMTC H.323 Forum Launch
... o Fibre To The Home (FTTH) is the next step for many operators o The major change is driven by the explosive growth of the Internet usage o Public and private networks evolve from multiple overlay networks to a unified network platform able to carry multiple applications ITU-T SG15 ...
... o Fibre To The Home (FTTH) is the next step for many operators o The major change is driven by the explosive growth of the Internet usage o Public and private networks evolve from multiple overlay networks to a unified network platform able to carry multiple applications ITU-T SG15 ...
ATIS IPTV Standards Development via ATIS IPTV
... • Continue with SDO and ITU-T coordination and collaboration. • Established important relationships with all of the leading organizations working in the IPTV realm to share our end-to-end view of the standards being developed. ...
... • Continue with SDO and ITU-T coordination and collaboration. • Established important relationships with all of the leading organizations working in the IPTV realm to share our end-to-end view of the standards being developed. ...
CIS Cisco IOS 15 Benchmark
... warranties, or covenants of any kind whatsoever (including the absence of any warranty regarding: (a) the effect or lack of effect of any SB Product on the operation or the security of any network, system, software, hardware, or any component of any of them, and (b) the accuracy, utility, reliabilit ...
... warranties, or covenants of any kind whatsoever (including the absence of any warranty regarding: (a) the effect or lack of effect of any SB Product on the operation or the security of any network, system, software, hardware, or any component of any of them, and (b) the accuracy, utility, reliabilit ...
CCNA Security - IIS Windows Server
... • Extends access security by combining authentication, user access, and administrator access with policy control • Allows greater flexibility and mobility, increased security, and user-productivity gains • Enforces a uniform security policy for all users • Reduces the administrative and management e ...
... • Extends access security by combining authentication, user access, and administrator access with policy control • Allows greater flexibility and mobility, increased security, and user-productivity gains • Enforces a uniform security policy for all users • Reduces the administrative and management e ...
2 Motivation for HSDPA
... the mobile operators are looking for new opportunities to increase the revenue. The situation is similar with the fixed line operators and internet service providers. They are also looking for new opportunities to increase the revenue. Mobile operators are trying to increase their revenue by providi ...
... the mobile operators are looking for new opportunities to increase the revenue. The situation is similar with the fixed line operators and internet service providers. They are also looking for new opportunities to increase the revenue. Mobile operators are trying to increase their revenue by providi ...
Nortel Secure Network Access 2.0 802.1X
... integrated way of detecting the state of a network client that is attempting to connect to a network and restricting the access of the network client until the policy requirements for connecting to the network have been met. The NSNA/NAP interoperability architecture allows customers to deploy both ...
... integrated way of detecting the state of a network client that is attempting to connect to a network and restricting the access of the network client until the policy requirements for connecting to the network have been met. The NSNA/NAP interoperability architecture allows customers to deploy both ...
2 Huawei LTE PTT Broadband Trunking Solution
... TruStar TruStar (Trunking Star) is the new-generation digital trunking solution that is developed by Huawei based on the third-generation mobile communications technology CDMA2000. In addition to the CS domain and PS domain inherited from the CDMA2000 network, the TruStar system has a trunking domai ...
... TruStar TruStar (Trunking Star) is the new-generation digital trunking solution that is developed by Huawei based on the third-generation mobile communications technology CDMA2000. In addition to the CS domain and PS domain inherited from the CDMA2000 network, the TruStar system has a trunking domai ...
1 Goals of the meeting
... FG IPTV-ID-31: It proposes architectural and functional requirements for IMS-based IPTV service including service control functions, which is in relationship with the IMS-based NGN requirements, new requirements including navigation, content distribution, content locating, etc. It is generally agree ...
... FG IPTV-ID-31: It proposes architectural and functional requirements for IMS-based IPTV service including service control functions, which is in relationship with the IMS-based NGN requirements, new requirements including navigation, content distribution, content locating, etc. It is generally agree ...
Toward an IPv6 world in mobile networks – mechanisms
... domain name system records, the DNS64 returns this record unchanged and the UE uses IPv6 to connect to the server directly. Otherwise, the DNS64 returns a synthesized address, and packets using that address are automatically routed to the NAT64. The NAT64 will perform address translation and forward ...
... domain name system records, the DNS64 returns this record unchanged and the UE uses IPv6 to connect to the server directly. Otherwise, the DNS64 returns a synthesized address, and packets using that address are automatically routed to the NAT64. The NAT64 will perform address translation and forward ...
RAD Katalog 2016
... RAD is a global Telecom Access solutions and products vendor. Our customers are top-tier service providers, power utilities, mass transportation systems, and government agencies. We are at the forefront of pioneering technologies, such as: • Distributed NFV for flexible virtual CPE deployments • H ...
... RAD is a global Telecom Access solutions and products vendor. Our customers are top-tier service providers, power utilities, mass transportation systems, and government agencies. We are at the forefront of pioneering technologies, such as: • Distributed NFV for flexible virtual CPE deployments • H ...
List of Figures
... There are three categories of market failure that we look for: (i) market power; (ii) externalities, and (iii) existing regulations. (i) and (ii) are dealt with in detail in the report. (iii) makes up a smaller section of the study as Internet backbones are not regulated directly. Nevertheless, regu ...
... There are three categories of market failure that we look for: (i) market power; (ii) externalities, and (iii) existing regulations. (i) and (ii) are dealt with in detail in the report. (iii) makes up a smaller section of the study as Internet backbones are not regulated directly. Nevertheless, regu ...
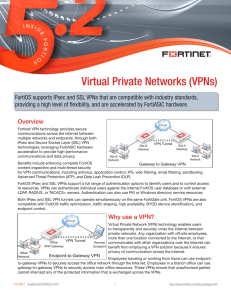
Virtual Private Networks (VPNs)
... FortiOS also supports policy-based and route-based IPsec VPNs. A route-based VPN creates a virtual IPsec network interface that applies encryption or decryption as needed to any traffic that interface carries. Route-based VPNs are also known as interface-based VPNs. A policy-based VPN is implemented ...
... FortiOS also supports policy-based and route-based IPsec VPNs. A route-based VPN creates a virtual IPsec network interface that applies encryption or decryption as needed to any traffic that interface carries. Route-based VPNs are also known as interface-based VPNs. A policy-based VPN is implemented ...
Linksys NR041 Manual
... FCC STATEMENT The Cable/DSL 4-Port Router has been tested and complies with the specifications for a Class B digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment gen ...
... FCC STATEMENT The Cable/DSL 4-Port Router has been tested and complies with the specifications for a Class B digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment gen ...
A Next Generation 911 Cost Study
... for handling calls, such as the switch, is housed in the PSAP. Under the hosted solution, a PSAP contracts with third party service providers for all network services and associated equipment, which are hosted offsite and are accessible by multiple PSAPs and other public safety entities. Costs are b ...
... for handling calls, such as the switch, is housed in the PSAP. Under the hosted solution, a PSAP contracts with third party service providers for all network services and associated equipment, which are hosted offsite and are accessible by multiple PSAPs and other public safety entities. Costs are b ...





![here - Campaign[x]](http://s1.studyres.com/store/data/008744944_1-0f4fd57a8eb108cf9826822f0ba0b000-300x300.png)
