Module 1: Overview of Microsoft ISA Server
... improve the speed at which users on your internal network can access Internet resources. You can also deploy ISA Server as a reverse caching server to improve the speed at which external users can access selected Web resources that you make available to the Internet. In addition, you can distribute ...
... improve the speed at which users on your internal network can access Internet resources. You can also deploy ISA Server as a reverse caching server to improve the speed at which external users can access selected Web resources that you make available to the Internet. In addition, you can distribute ...
Guide to Firewalls and Network Security with Intrusion Detection and
... packet (application proxies examine data in the packet) ...
... packet (application proxies examine data in the packet) ...
long talk - Cs.princeton.edu
... BGP tables: mostly match, as our algorithm assumes Refined mapping: change 2.9% of original mapping – Robust to reducing # of probes and introducing noise ...
... BGP tables: mostly match, as our algorithm assumes Refined mapping: change 2.9% of original mapping – Robust to reducing # of probes and introducing noise ...
Toolbox - PlanetOne Communications
... SIP Trunking Adds Value by … • Supporting Business Continuity. SIP can be programmed to auto forward to mobile phones or alternative DIDs, ensuring that customer calls are not dropped or unanswered. • Enabling Unified Communications. SIP is the standard protocol for VoIP, but it was designed for al ...
... SIP Trunking Adds Value by … • Supporting Business Continuity. SIP can be programmed to auto forward to mobile phones or alternative DIDs, ensuring that customer calls are not dropped or unanswered. • Enabling Unified Communications. SIP is the standard protocol for VoIP, but it was designed for al ...
ppt
... Corporate Backbone... More Secure than the Commodity Internet Can move a lot of data rapidly (if you pay for proper CIR and burst rate) Is marginal for moving time sensitive traffic Generally Cheaper for data than Leased Lines Fewer access lines required Backbone has higher Carrying Capacity ...
... Corporate Backbone... More Secure than the Commodity Internet Can move a lot of data rapidly (if you pay for proper CIR and burst rate) Is marginal for moving time sensitive traffic Generally Cheaper for data than Leased Lines Fewer access lines required Backbone has higher Carrying Capacity ...
PPT - Protocol Engineering and Technology Unit
... service requirements. This requires mapping of user defined QoS requirement to resouce allocations for providing the service. ...
... service requirements. This requires mapping of user defined QoS requirement to resouce allocations for providing the service. ...
4. Virtual Private Networks ( VPN )
... Intranet-based - This type of Site-to-site VPN is used to extend a company's existing LAN to other buildings and sites, so that these remote employees can utilize the same Extranet-based- With an Extranet-based VPN two or more companies can establish a network services. secure network connection in ...
... Intranet-based - This type of Site-to-site VPN is used to extend a company's existing LAN to other buildings and sites, so that these remote employees can utilize the same Extranet-based- With an Extranet-based VPN two or more companies can establish a network services. secure network connection in ...
Diapositiva 1
... with different configurations, but always with two new equipment and reusing the previous switch/router. We chose the more advantageous: separated L2 and L3 equipment in one node, same equipment in the other node. ...
... with different configurations, but always with two new equipment and reusing the previous switch/router. We chose the more advantageous: separated L2 and L3 equipment in one node, same equipment in the other node. ...
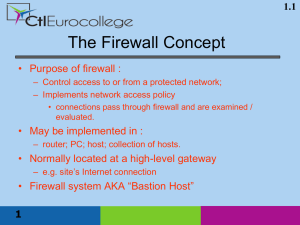
Firewall - theodoros christophides site
... – cost of introducing firewall may exceed cost of vulnerabilities – alternative solutions may be appropriate ...
... – cost of introducing firewall may exceed cost of vulnerabilities – alternative solutions may be appropriate ...
Firewalls and Virtual Private Networks
... secure connection is generally associated with private networks. (A private network is a network that is owned, or at least controlled via leased lines, by an organization.) Using the techniques discussed later in this chapter, a VPN can transform the characteristics of a public non-secure network i ...
... secure connection is generally associated with private networks. (A private network is a network that is owned, or at least controlled via leased lines, by an organization.) Using the techniques discussed later in this chapter, a VPN can transform the characteristics of a public non-secure network i ...
IPv6 Microsegmentation - Interop Conference Presentations
... first-hop router • A /64 subnet is allocated to each dial-up interface (usually from a local pool) • Aggregate IPv6 prefix is advertised to the network core to minimize number of prefixes advertised in the core ...
... first-hop router • A /64 subnet is allocated to each dial-up interface (usually from a local pool) • Aggregate IPv6 prefix is advertised to the network core to minimize number of prefixes advertised in the core ...
IPv4
... – Sometimes, tremendous traffic will be generated. – Some people may make damage on the network system with a malicious intent. ...
... – Sometimes, tremendous traffic will be generated. – Some people may make damage on the network system with a malicious intent. ...
Infrastructure Attack Vectors and Mitigation
... • What makes the network of networks eventually the Internet – IP (v4/v6): protocol to exchange data between endpoints – DNS: resolving human readable names to IP addresses – routing: inter-domain routing between networks, making IP addresses globally reachable ...
... • What makes the network of networks eventually the Internet – IP (v4/v6): protocol to exchange data between endpoints – DNS: resolving human readable names to IP addresses – routing: inter-domain routing between networks, making IP addresses globally reachable ...
Presentation at CPA 2003, Powerpoint
... • KRoC.net has a relatively low impact on processes running in the background • Even slightly better that DoP, a predecessor from 2001, which is most likely due to the dynamic setup of KRoC.net: – KRoC.net’s component processes are created ‘on the fly’ when they are needed – No copying of data invol ...
... • KRoC.net has a relatively low impact on processes running in the background • Even slightly better that DoP, a predecessor from 2001, which is most likely due to the dynamic setup of KRoC.net: – KRoC.net’s component processes are created ‘on the fly’ when they are needed – No copying of data invol ...
Broadband Reference Guide
... diverse constituent base through a physical network connection and also as an issue of important public policy. As a nation and state it is imperative that we pave the way for broadband. The National Broadband Plan is a roadmap to America’s future that recommends that the Federal Communications Comm ...
... diverse constituent base through a physical network connection and also as an issue of important public policy. As a nation and state it is imperative that we pave the way for broadband. The National Broadband Plan is a roadmap to America’s future that recommends that the Federal Communications Comm ...
22-InternetCloudTech.. - Systems and Computer Engineering
... Paul Baron “On Distributed Communications Networks” RAND Corp. ...
... Paul Baron “On Distributed Communications Networks” RAND Corp. ...
Cabernet: Connectivity Architecture for Better Network Services Yaping Zhu Rui Zhang-Shen
... are associated with the physical interfaces on node P , which are directly connected to the neighboring physical interfaces X1, Y 1, and Z1, on nodes not shown in Figure 2. Note that the virtual links in the service VN may not map directly to the virtual links in the connectivity VN. For example, th ...
... are associated with the physical interfaces on node P , which are directly connected to the neighboring physical interfaces X1, Y 1, and Z1, on nodes not shown in Figure 2. Note that the virtual links in the service VN may not map directly to the virtual links in the connectivity VN. For example, th ...
The Dawn of a Maturing Industry
... even if you delete the entry. This is also true for Facebook, MySpace, Twitter and other social networking sites © 2007 Prentice-Hall, Inc ...
... even if you delete the entry. This is also true for Facebook, MySpace, Twitter and other social networking sites © 2007 Prentice-Hall, Inc ...
L20 - MIT
... Total rate of EF traffic must be less than link rate Give EF traffic strict priority over other traffic Alternatively, use WFQ with high weight for EF traffic ...
... Total rate of EF traffic must be less than link rate Give EF traffic strict priority over other traffic Alternatively, use WFQ with high weight for EF traffic ...
Part 4 - CSE Labs User Home Pages
... are connected only as parents and children and not as peers ...
... are connected only as parents and children and not as peers ...
Lesson 9 - EdTechnology, educational technology
... architects, it is still based on the TCP/IP protocol suite. The design of TCP/IP is ideal for the decentralized and robust network that is the Internet. Many protocols used today were designed using the four-layer TCP/IP model. It is useful to know both the TCP/IP and OSI networking models. Each mod ...
... architects, it is still based on the TCP/IP protocol suite. The design of TCP/IP is ideal for the decentralized and robust network that is the Internet. Many protocols used today were designed using the four-layer TCP/IP model. It is useful to know both the TCP/IP and OSI networking models. Each mod ...
PPT
... A network is a set of devices connected by communication links. The Internet today is made up of many wide and local area networks joined by connecting devices and switching stations. Most end users who want Internet connection use the services of Internet service providers (ISPs). There are backb ...
... A network is a set of devices connected by communication links. The Internet today is made up of many wide and local area networks joined by connecting devices and switching stations. Most end users who want Internet connection use the services of Internet service providers (ISPs). There are backb ...