hybrid expert system agents - Universitatea"Petru Maior"
... diagnosis system is proposed for difficult problems solving, like the diagnoses of combinations of illnesses (patients that suffer from combinations of illnesses). In the papers [5, 6] are analyzed different aspects related with a novel hybrid diagnosis system. The novelty consists in the diagnosis ...
... diagnosis system is proposed for difficult problems solving, like the diagnoses of combinations of illnesses (patients that suffer from combinations of illnesses). In the papers [5, 6] are analyzed different aspects related with a novel hybrid diagnosis system. The novelty consists in the diagnosis ...
Expected Value, Reward Outcome, and
... pence with a probability of 0.9. On the right, in different trial sets, the probability of the large reward was 0.9 (making the EV defined as probability 3 RM = 27 pence); the probability was 0.33 making the EV 10 pence; or the probability was 0.16 making the EV 5 pence (see Fig. 1a). (On the trials ...
... pence with a probability of 0.9. On the right, in different trial sets, the probability of the large reward was 0.9 (making the EV defined as probability 3 RM = 27 pence); the probability was 0.33 making the EV 10 pence; or the probability was 0.16 making the EV 5 pence (see Fig. 1a). (On the trials ...
LAO*: A heuristic search algorithm that finds solutions with loops
... represents a failed reduction to primitive subproblems. However, there is an important class of problems for which it does make sense for a solution to contain loops. These problems can be formalized as Markov decision processes, a framework that is widely used in artificial intelligence for problem ...
... represents a failed reduction to primitive subproblems. However, there is an important class of problems for which it does make sense for a solution to contain loops. These problems can be formalized as Markov decision processes, a framework that is widely used in artificial intelligence for problem ...
as a PDF - Idiap Publications
... where a St −1St represents the transition probability and is supposed to be identical for the speaker and the world parameters and, bclient , St () and bworld , St () are the client’s and respectively the world’s output distributions relative to the state St. By replacing Eq. (3) into Eq.(1), it app ...
... where a St −1St represents the transition probability and is supposed to be identical for the speaker and the world parameters and, bclient , St () and bworld , St () are the client’s and respectively the world’s output distributions relative to the state St. By replacing Eq. (3) into Eq.(1), it app ...
Intrusion detection using clustering
... S. Otherwise the cluster which gives minimum distance between the data point and the cluster is found, next the distance is compared the result with the cluster radius threshold, if it is less than the defined threshold then the data point is added to the cluster otherwise new cluster is created wit ...
... S. Otherwise the cluster which gives minimum distance between the data point and the cluster is found, next the distance is compared the result with the cluster radius threshold, if it is less than the defined threshold then the data point is added to the cluster otherwise new cluster is created wit ...
A Low-Cost Approximate Minimal Hitting Set Algorithm
... with higher cardinality. The brute-force approach, as well as the above heuristic approach are examples of approaches that find minimal hitting sets with lower cardinality first. In many situations, however, obtaining MHS solutions in order of just cardinality does not suffice. An example is model-b ...
... with higher cardinality. The brute-force approach, as well as the above heuristic approach are examples of approaches that find minimal hitting sets with lower cardinality first. In many situations, however, obtaining MHS solutions in order of just cardinality does not suffice. An example is model-b ...
powerpoint slides
... This mimics the evolutionary process that small changes occur more often than larger ones An algorithm (in C++) that produces Gaussian random numbers is supplied in the handout ...
... This mimics the evolutionary process that small changes occur more often than larger ones An algorithm (in C++) that produces Gaussian random numbers is supplied in the handout ...
Combining Clustering with Classification for Spam Detection in
... a great success in many areas, their training time is at least O(N 2 ) for training data of size N , which makes them non favourable for large data sets. The same problem applies to other classifiers as well. In this vein, clustering is used as a down-sampling pre-process to classification, in order ...
... a great success in many areas, their training time is at least O(N 2 ) for training data of size N , which makes them non favourable for large data sets. The same problem applies to other classifiers as well. In this vein, clustering is used as a down-sampling pre-process to classification, in order ...
Population Based Algorithms - School of Computer Science
... Genetic Algorithm Example III Many applications of genetic algorithms. Best suited to problems where the efficient solutions are not already known. Strength of GA's: ability to heuristically search for solutions when all else fails. If you can represent the solutions to the problem in a suitable fo ...
... Genetic Algorithm Example III Many applications of genetic algorithms. Best suited to problems where the efficient solutions are not already known. Strength of GA's: ability to heuristically search for solutions when all else fails. If you can represent the solutions to the problem in a suitable fo ...
Mechanism Design for Computationally Limited Agents
... • Good estimates of other agents’ valuations can allow an agent to tailor its strategy to achieve higher utility • Strong strategic computing: Agent uses some of its deliberation resources to compute on others’ problems • Weak strategic computing: Agent uses information from others’ performance prof ...
... • Good estimates of other agents’ valuations can allow an agent to tailor its strategy to achieve higher utility • Strong strategic computing: Agent uses some of its deliberation resources to compute on others’ problems • Weak strategic computing: Agent uses information from others’ performance prof ...
The Problem of Logical-Form Equivalence
... deterministic. In fact, both of the published claims of solution to the logical-form equivalence problem are of this variety. The first such claim that has come to my attention is due to Calder, Reape, and Zeevat (1989). They state that We must generate all sentences whose semantic representations a ...
... deterministic. In fact, both of the published claims of solution to the logical-form equivalence problem are of this variety. The first such claim that has come to my attention is due to Calder, Reape, and Zeevat (1989). They state that We must generate all sentences whose semantic representations a ...
Online Full Text
... cluster identified, this is clearly giving us a high level explanation of the fuzzy clustering working mechanism. the selection process was performed by selecting the C. Testing Phase initial population from the sorted array which is sorted according to the error rate in ascending order, our The Tes ...
... cluster identified, this is clearly giving us a high level explanation of the fuzzy clustering working mechanism. the selection process was performed by selecting the C. Testing Phase initial population from the sorted array which is sorted according to the error rate in ascending order, our The Tes ...
Role of Expert Systems in Construction Roboticsl
... The principal distinction between expert systems and algorithmic programs lies in the use of knowledge. A traditional algorithmic application is organized into data and program. An expert system separates the program into an explicit knowledge base describing the problem solving strategy and a contr ...
... The principal distinction between expert systems and algorithmic programs lies in the use of knowledge. A traditional algorithmic application is organized into data and program. An expert system separates the program into an explicit knowledge base describing the problem solving strategy and a contr ...
SAT-based planning in complex domains: Concurrency, constraints
... • nondeterminism in the initial state and/or in the effects of actions. Because of nondeterminism, C-SAT employs a generate and test approach. The generate and test steps correspond to satisfiability and validity checks respectively, and both are performed using a procedure built on top of a SAT sol ...
... • nondeterminism in the initial state and/or in the effects of actions. Because of nondeterminism, C-SAT employs a generate and test approach. The generate and test steps correspond to satisfiability and validity checks respectively, and both are performed using a procedure built on top of a SAT sol ...
Planning Algorithms for Interactive Storytelling
... the early, noninteractive story-generating systems like UNIVERSE [Lebowitz 1985]. More recently, this correspondence has made the planning-based approach the most common one among IS researchers [Cavazza and Charles 2005]. Although planning systems have been used as an important part of several publ ...
... the early, noninteractive story-generating systems like UNIVERSE [Lebowitz 1985]. More recently, this correspondence has made the planning-based approach the most common one among IS researchers [Cavazza and Charles 2005]. Although planning systems have been used as an important part of several publ ...
On the connections between backdoors, restarts, and heavy
... set S of variables for which all other variables may be thought of as defined in terms of S. For example, a maximal subset of independent variables in a SAT encoding of a hardware verification problem is a backdoor for unit propagation, as the other variables’ values may be directly determined after ...
... set S of variables for which all other variables may be thought of as defined in terms of S. For example, a maximal subset of independent variables in a SAT encoding of a hardware verification problem is a backdoor for unit propagation, as the other variables’ values may be directly determined after ...
Automatically Building Special Purpose Search Engines with
... Astro Teller is the CEO and co-founder of BodyMedia. Astro holds a Ph.D. in Artificial Intelligence from Carnegie Mellon University, where he was inducted as a national Hertz fellow. His M.S. in symbolic and heuristic computation and B.S. in computer science are from Stanford University. His work in ...
... Astro Teller is the CEO and co-founder of BodyMedia. Astro holds a Ph.D. in Artificial Intelligence from Carnegie Mellon University, where he was inducted as a national Hertz fellow. His M.S. in symbolic and heuristic computation and B.S. in computer science are from Stanford University. His work in ...
IT7005B-Artificial Intelligence UNIT WISE Important Questions
... 3. Define backtracking search. 4. Define constraint propagation 5. List the different types of constraints. 6. What is a constraint satisfaction problem? 7. Differentiate greedy search with A* search. 8. Write short notes on monotonicity and optimality of A* search. 9. Give example for effective bra ...
... 3. Define backtracking search. 4. Define constraint propagation 5. List the different types of constraints. 6. What is a constraint satisfaction problem? 7. Differentiate greedy search with A* search. 8. Write short notes on monotonicity and optimality of A* search. 9. Give example for effective bra ...
On the Implementation of MIPS
... BDD Refinements (Version 1.1) Several approaches have been proposed to improve the efficiency in calculating the image of a set of states according to a transition function. The daunting problem is that even it the input and the output representations are small the representation during the computat ...
... BDD Refinements (Version 1.1) Several approaches have been proposed to improve the efficiency in calculating the image of a set of states according to a transition function. The daunting problem is that even it the input and the output representations are small the representation during the computat ...
Efficient Sampling for k-Determinantal Point Processes
... models that capture diversity by assigning subset probabilities proportional to (sub)determinants of a kernel matrix. D PPs enjoy rising interest in machine learning [4, 23, 28, 30, 32, 34, 38]; a part of their appeal can be attributed to computational tractability of basic tasks such as computing p ...
... models that capture diversity by assigning subset probabilities proportional to (sub)determinants of a kernel matrix. D PPs enjoy rising interest in machine learning [4, 23, 28, 30, 32, 34, 38]; a part of their appeal can be attributed to computational tractability of basic tasks such as computing p ...
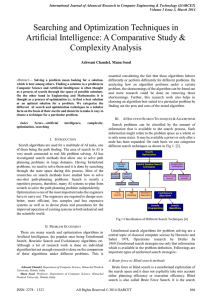
Searching and Optimization Techniques in Artificial
... Nilsson and Betram Rapahel. It is combination of Dijkstra’s algorithm and best first search. It can be used to solve many kinds of problems. A* search finds the shortest path through a search space to goal state using heuristic function. This technique finds minimal cost solutions and is also direct ...
... Nilsson and Betram Rapahel. It is combination of Dijkstra’s algorithm and best first search. It can be used to solve many kinds of problems. A* search finds the shortest path through a search space to goal state using heuristic function. This technique finds minimal cost solutions and is also direct ...
An Efficient Hybrid Strategy for Temporal Planning
... established AI and OR techniques. Our contribution is twofold. First, we propose an efficient STRIPS planning algorithm that is based on the planning-as-satisfiability (SATPlan) paradigm [25, 17] but improves SATPlan by incorporating an objective function to accommodate an effective goal-oriented va ...
... established AI and OR techniques. Our contribution is twofold. First, we propose an efficient STRIPS planning algorithm that is based on the planning-as-satisfiability (SATPlan) paradigm [25, 17] but improves SATPlan by incorporating an objective function to accommodate an effective goal-oriented va ...
Multi-Objective POMDPs with Lexicographic Reward Preferences
... model [Wray et al., 2015]. Slack increases the space of possible actions for subsequent value functions to utilize, as long as the deviation caused by sub-optimal action selection is within the allotted slack. For example, the highest-priority objective may be to minimize execution time, but within ...
... model [Wray et al., 2015]. Slack increases the space of possible actions for subsequent value functions to utilize, as long as the deviation caused by sub-optimal action selection is within the allotted slack. For example, the highest-priority objective may be to minimize execution time, but within ...
Engineering Note
... outcomes annotated by a probability of occurrence. In addition, the planning problem is conformant, i.e., the planner has to construct the best plan possible without assuming that the results of the actions performed can be observed. As an example of a conformant probabilistic planning problem, cons ...
... outcomes annotated by a probability of occurrence. In addition, the planning problem is conformant, i.e., the planner has to construct the best plan possible without assuming that the results of the actions performed can be observed. As an example of a conformant probabilistic planning problem, cons ...
What is Approximate Reasoning? - CORE Scholar
... inputs will be difficult to obtain in practice (since, e.g., in general there can be infinitely many different inputs). So rules of thumb, like giving short queries a higher probability than long ones, or using some kind of established benchmarks, will have to be used until more systematic data is a ...
... inputs will be difficult to obtain in practice (since, e.g., in general there can be infinitely many different inputs). So rules of thumb, like giving short queries a higher probability than long ones, or using some kind of established benchmarks, will have to be used until more systematic data is a ...
Multi-armed bandit

In probability theory, the multi-armed bandit problem (sometimes called the K- or N-armed bandit problem) is a problem in which a gambler at a row of slot machines (sometimes known as ""one-armed bandits"") has to decide which machines to play, how many times to play each machine and in which order to play them. When played, each machine provides a random reward from a distribution specific to that machine. The objective of the gambler is to maximize the sum of rewards earned through a sequence of lever pulls.Robbins in 1952, realizing the importance of the problem, constructed convergent population selection strategies in ""some aspects of the sequential design of experiments"".A theorem, the Gittins index published first by John C. Gittins gives an optimal policy in the Markov setting for maximizing the expected discounted reward.In practice, multi-armed bandits have been used to model the problem of managing research projects in a large organization, like a science foundation or a pharmaceutical company. Given a fixed budget, the problem is to allocate resources among the competing projects, whose properties are only partially known at the time of allocation, but which may become better understood as time passes.In early versions of the multi-armed bandit problem, the gambler has no initial knowledge about the machines. The crucial tradeoff the gambler faces at each trial is between ""exploitation"" of the machine that has the highest expected payoff and ""exploration"" to get more information about the expected payoffs of the other machines. The trade-off between exploration and exploitation is also faced in reinforcement learning.