Dynamic problem structure analysis as a basis for constraint
... Many powerful propagation techniques have been developed for constraint-directed scheduling in recent years, for instance, variations of edge-finding [20,22,50,58] and shaving [21]. It has long been known that search can be drastically reduced by enforcing various degrees of consistency [36]. The ef ...
... Many powerful propagation techniques have been developed for constraint-directed scheduling in recent years, for instance, variations of edge-finding [20,22,50,58] and shaving [21]. It has long been known that search can be drastically reduced by enforcing various degrees of consistency [36]. The ef ...
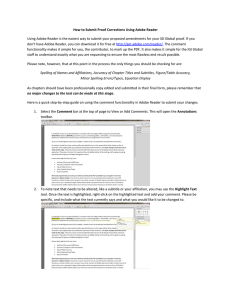
How to Submit Proof Corrections Using Adobe Reader
... As last, a roulette wheel method is used to calculate the possibility of selecting the locations: p (x i ) = ...
... As last, a roulette wheel method is used to calculate the possibility of selecting the locations: p (x i ) = ...
Part I: Heuristics
... Defined in either way, a stochastic shortest-path problem is a special case of a fully-observable infinite-horizon Markov decision process (MDP). There are several ...
... Defined in either way, a stochastic shortest-path problem is a special case of a fully-observable infinite-horizon Markov decision process (MDP). There are several ...
Non-Deterministic Planning with Temporally Extended Goals
... that are temporally extended, require adherence to safety constraints and directives, necessitate the optimization of preferences or other quality measures, and/or require or may benefit from following a prescribed high-level script that specifies how the task is to be realized. In this paper we foc ...
... that are temporally extended, require adherence to safety constraints and directives, necessitate the optimization of preferences or other quality measures, and/or require or may benefit from following a prescribed high-level script that specifies how the task is to be realized. In this paper we foc ...
A Quotient Construction on Markov Chains with
... the time, they arise as discrete-time, finite-state, stationary Markov processes (i.e., Markov chains), which are fully determined by a transition matrix and an initial distribution. For example, in an earlier paper [14], we analyzed the dynamics of Young’s adaptive learning model in repeated games ...
... the time, they arise as discrete-time, finite-state, stationary Markov processes (i.e., Markov chains), which are fully determined by a transition matrix and an initial distribution. For example, in an earlier paper [14], we analyzed the dynamics of Young’s adaptive learning model in repeated games ...
The Exploration of Greedy Hill-climbing Search in Markov
... space (GS algorithm) takes an initial graph, defines a neighborhood, computes a score for every graph in this neighborhood, and chooses the one which maximizes the score for the next iteration, until the scoring function between two consecutive iterations does not improve. And the neighborhood is de ...
... space (GS algorithm) takes an initial graph, defines a neighborhood, computes a score for every graph in this neighborhood, and chooses the one which maximizes the score for the next iteration, until the scoring function between two consecutive iterations does not improve. And the neighborhood is de ...
A preliminary analysis of the Soar architecture as a basis for general
... The lowest level of the Soar architecture is the level at which these memory phenomena occur. All of Soar's long-term knowledge is stored in a single production memory. Whether a piece of knowledge represents procedural, declarative, or episodic knowledge, it is stored in one or more productions. Ea ...
... The lowest level of the Soar architecture is the level at which these memory phenomena occur. All of Soar's long-term knowledge is stored in a single production memory. Whether a piece of knowledge represents procedural, declarative, or episodic knowledge, it is stored in one or more productions. Ea ...
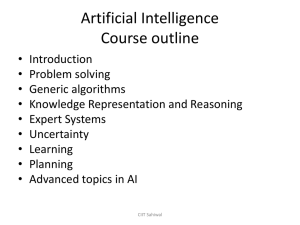
Artificial Intelligence Problem Solving and Search
... • Operator: description of an action • State space: all states reachable from the initial state by any sequence action • Path: sequence of actions leading from one state to another • Goal test: which the agent can apply to a single state description to determine if it is a goal state • Path cost fun ...
... • Operator: description of an action • State space: all states reachable from the initial state by any sequence action • Path: sequence of actions leading from one state to another • Goal test: which the agent can apply to a single state description to determine if it is a goal state • Path cost fun ...
An efficient approach for finding the MPE in belief networks
... tions for the MPE is simply given right instantiation of all variables. This means that finding the MPE can be a search problem. We can use search with back tracking techniques to find the MPE, but it may not be an efficient way because the search complexity is exponential with respect to the number ...
... tions for the MPE is simply given right instantiation of all variables. This means that finding the MPE can be a search problem. We can use search with back tracking techniques to find the MPE, but it may not be an efficient way because the search complexity is exponential with respect to the number ...
Applications of Artificial Intelligence
... Gödel could show during the 20ties of the last century: PK1 (predicate logic of the first level) is not computable ! We have problems which are not computable ! ...
... Gödel could show during the 20ties of the last century: PK1 (predicate logic of the first level) is not computable ! We have problems which are not computable ! ...
RIGID E-UNIFICATION
... solvable by computing these equivalence classes. Shostak proved that for computing the equivalence classes of all terms in ThE s t i , no terms that are not in ThE s t i have to be considered: If s can be derived from t using the equalities in E, then this can be done without using an intermediate t ...
... solvable by computing these equivalence classes. Shostak proved that for computing the equivalence classes of all terms in ThE s t i , no terms that are not in ThE s t i have to be considered: If s can be derived from t using the equalities in E, then this can be done without using an intermediate t ...
Artificial Intelligence UNIT I Page 1 of 116 CSE– Dhaanish Ahmed
... Fig : The Tom Evan’s ANALOGY program could solve geometric analogy problems as shown. A dose of reality (1966-1973) From the beginning, AI researchers were not shy about making predictions of their coming successes. The following statement by Herbert Simon in 1957 is often quoted: “It is not my aim ...
... Fig : The Tom Evan’s ANALOGY program could solve geometric analogy problems as shown. A dose of reality (1966-1973) From the beginning, AI researchers were not shy about making predictions of their coming successes. The following statement by Herbert Simon in 1957 is often quoted: “It is not my aim ...
- PPT Topics
... * GPS did not use specific info about problem at hand in selection of state transition * GPS examined all states leading to exponential time complexity * breakthrough in AI towards more specialised problem-solving system, i.e., Knowledge-based systems www.ppttopics.com ...
... * GPS did not use specific info about problem at hand in selection of state transition * GPS examined all states leading to exponential time complexity * breakthrough in AI towards more specialised problem-solving system, i.e., Knowledge-based systems www.ppttopics.com ...
comparative study of case based reasoning software
... Case-based Reasoning is an emerging field in Artificial intelligence. It is mostly used in problem solving in the artificial intelligence applications. Case-based reasoning is an approach which utilizes the experience gained from solving past problems [1]. This approach maintains all information of ...
... Case-based Reasoning is an emerging field in Artificial intelligence. It is mostly used in problem solving in the artificial intelligence applications. Case-based reasoning is an approach which utilizes the experience gained from solving past problems [1]. This approach maintains all information of ...
SetA*: An Efficient BDD-Based Heuristic Search Algorithm
... has to be found. However since 0K 0L is a single state this is trivial. Similar to the regular A* algorithm, SetA* continues popping the top node of the queue until the queue is either empty or the states of the top node overlaps with the goal. The top node is expanded by finding the image of it for ...
... has to be found. However since 0K 0L is a single state this is trivial. Similar to the regular A* algorithm, SetA* continues popping the top node of the queue until the queue is either empty or the states of the top node overlaps with the goal. The top node is expanded by finding the image of it for ...
Multiple-Query Optimization
... Rule 3: retrieve (EMP.all) where EMP.salary > 30 and EMP.experience 5 3 Then, given a query that asks Is Mike well paid? the system will have to evaluate all three rules in order to come up with the answer. Because of the similarities that Prolog [6] clauses have with the above type of rules, our di ...
... Rule 3: retrieve (EMP.all) where EMP.salary > 30 and EMP.experience 5 3 Then, given a query that asks Is Mike well paid? the system will have to evaluate all three rules in order to come up with the answer. Because of the similarities that Prolog [6] clauses have with the above type of rules, our di ...
Discrete coding of stimulus value, reward expectation, and reward
... consisting of a fixed 4 s plus an exponentially distributed interval with a mean of 5 s. The exception ...
... consisting of a fixed 4 s plus an exponentially distributed interval with a mean of 5 s. The exception ...
Bayesian Reasoning - Bayesian Intelligence
... Artificial intelligence (AI), should it ever exist, will be an intelligence developed by humans, implemented as an artifact. The level of intelligence demanded by Alan Turing’s famous test (1950) — the ability to fool ordinary (unfoolish) humans about whether the other end of a dialogue is being car ...
... Artificial intelligence (AI), should it ever exist, will be an intelligence developed by humans, implemented as an artifact. The level of intelligence demanded by Alan Turing’s famous test (1950) — the ability to fool ordinary (unfoolish) humans about whether the other end of a dialogue is being car ...
A sufficiently fast algorithm for finding close to optimal clique trees
... Kloks in his book Treewidth [14], which is devoted to finding clique trees in various graphs, gives a polynomial algorithm that finds a clique tree of a given graph G such that its largest clique size is at most a factor 12∆ log n off optimal where ∆ is a large unspecified constant (see also, [6]). ...
... Kloks in his book Treewidth [14], which is devoted to finding clique trees in various graphs, gives a polynomial algorithm that finds a clique tree of a given graph G such that its largest clique size is at most a factor 12∆ log n off optimal where ∆ is a large unspecified constant (see also, [6]). ...
Heuristic Classification
... heuristic classification can be derived from some simple assumptions about how data and solutions are typically related (Section 4). Another detailed discussion then considers “what gets selected,” possible kinds of solutions (e.g., diagnoses). A taxonomy of problem types is proposed that characteri ...
... heuristic classification can be derived from some simple assumptions about how data and solutions are typically related (Section 4). Another detailed discussion then considers “what gets selected,” possible kinds of solutions (e.g., diagnoses). A taxonomy of problem types is proposed that characteri ...
Reward loss and addiction: Opportunities for cross
... 1996). In these tasks, behavior (whether consummatory or instrumental) is rewarded with a large reward for a number of preshift sessions and then the magnitude or quality of the reward is downshifted. This unexpected reward downshift causes either consummatory suppression or instrumental avoidance o ...
... 1996). In these tasks, behavior (whether consummatory or instrumental) is rewarded with a large reward for a number of preshift sessions and then the magnitude or quality of the reward is downshifted. This unexpected reward downshift causes either consummatory suppression or instrumental avoidance o ...
45 Online Planning for Large Markov Decision Processes
... space before the agent is actually interacting with the environment. In practice, offline algorithms often suffer from the problem of scalability due to the well-known “curse of dimensionality”—that is, the size of state space grows exponentially with the number of state variables [Littman et al. 19 ...
... space before the agent is actually interacting with the environment. In practice, offline algorithms often suffer from the problem of scalability due to the well-known “curse of dimensionality”—that is, the size of state space grows exponentially with the number of state variables [Littman et al. 19 ...
Numeric Planning via Search Space Abstraction - CEUR
... to distinguish when actions are or are not applicable and when the goal has been reached. To achieve this we simply add a propositional fluent for each unique action precondition and goal condition in the problem. In this way, we produce a goal preserving and affordance preserving abstraction for th ...
... to distinguish when actions are or are not applicable and when the goal has been reached. To achieve this we simply add a propositional fluent for each unique action precondition and goal condition in the problem. In this way, we produce a goal preserving and affordance preserving abstraction for th ...
Improving Adjustable Autonomy Strategies for Time
... avoid a potentially poor input from the human. The aim of this paper is to develop an overarching framework that will work with any inconsistency resolution method that is chosen, given its estimated action duration. Secondly, RIAACT creates adjustable autonomy policies with precisely timed transfer ...
... avoid a potentially poor input from the human. The aim of this paper is to develop an overarching framework that will work with any inconsistency resolution method that is chosen, given its estimated action duration. Secondly, RIAACT creates adjustable autonomy policies with precisely timed transfer ...
Combining Linear Programming and Satisfiability Solving for
... assignment” and “inconsistent partial assignment”. As described in the previous section, each of these concepts in an LCNF problem refers to the active constraint set; however, in a boolean satisfiability problem, the solver considers only the CNF formula when checking for satisfiability. We now des ...
... assignment” and “inconsistent partial assignment”. As described in the previous section, each of these concepts in an LCNF problem refers to the active constraint set; however, in a boolean satisfiability problem, the solver considers only the CNF formula when checking for satisfiability. We now des ...
Multi-armed bandit

In probability theory, the multi-armed bandit problem (sometimes called the K- or N-armed bandit problem) is a problem in which a gambler at a row of slot machines (sometimes known as ""one-armed bandits"") has to decide which machines to play, how many times to play each machine and in which order to play them. When played, each machine provides a random reward from a distribution specific to that machine. The objective of the gambler is to maximize the sum of rewards earned through a sequence of lever pulls.Robbins in 1952, realizing the importance of the problem, constructed convergent population selection strategies in ""some aspects of the sequential design of experiments"".A theorem, the Gittins index published first by John C. Gittins gives an optimal policy in the Markov setting for maximizing the expected discounted reward.In practice, multi-armed bandits have been used to model the problem of managing research projects in a large organization, like a science foundation or a pharmaceutical company. Given a fixed budget, the problem is to allocate resources among the competing projects, whose properties are only partially known at the time of allocation, but which may become better understood as time passes.In early versions of the multi-armed bandit problem, the gambler has no initial knowledge about the machines. The crucial tradeoff the gambler faces at each trial is between ""exploitation"" of the machine that has the highest expected payoff and ""exploration"" to get more information about the expected payoffs of the other machines. The trade-off between exploration and exploitation is also faced in reinforcement learning.