Document
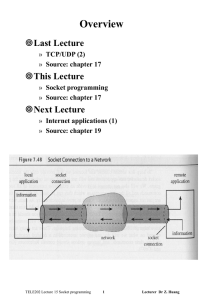
... – SOCK_RAW, a raw type that allows privileged programs to access low-level protocols or network interfaces » protocol is used to select a specific protocol in the protocol family if there are multiple protocols to support the same service type ...
... – SOCK_RAW, a raw type that allows privileged programs to access low-level protocols or network interfaces » protocol is used to select a specific protocol in the protocol family if there are multiple protocols to support the same service type ...
PowerPoint
... • Compiling miniTAJS takes 35 seconds – 4500 lines of code – 113 classes + 40 objects = 580 .class files ...
... • Compiling miniTAJS takes 35 seconds – 4500 lines of code – 113 classes + 40 objects = 580 .class files ...
Jan 7
... Learn about different types of computers Explore the hardware and software components of a computer system Learn about the language of a computer Learn about the evolution of programming languages Examine high-level programming languages © Janice Regan 2003 ...
... Learn about different types of computers Explore the hardware and software components of a computer system Learn about the language of a computer Learn about the evolution of programming languages Examine high-level programming languages © Janice Regan 2003 ...
NORTH MAHARASHTRA UNIVERSITY, JALGAON (M.S.) Teacher and Examiner’s Manual
... programming techniques. Limitations of procedural programming. Need of objectoriented programming. Object-Oriented Programming concepts and the basics of C++. 1. Introduction to Object Oriented Programming a Introduction: Introduction to procedural, modular and object-oriented programming techniques ...
... programming techniques. Limitations of procedural programming. Need of objectoriented programming. Object-Oriented Programming concepts and the basics of C++. 1. Introduction to Object Oriented Programming a Introduction: Introduction to procedural, modular and object-oriented programming techniques ...
Sams Teach Yourself Beginning Programming in
... Warning and Disclaimer Every effort has been made to make this book as complete and as accurate as possible, but no warranty or fitness is implied. The information provided is on an “as is” basis. The authors and the publisher shall have neither liability nor responsibility to any person or entity w ...
... Warning and Disclaimer Every effort has been made to make this book as complete and as accurate as possible, but no warranty or fitness is implied. The information provided is on an “as is” basis. The authors and the publisher shall have neither liability nor responsibility to any person or entity w ...
ch01_old1
... The OO paradigm is based on the idea that all aspects of software – its design, implementation, internal structure, as well as the supporting tools and language – should be based on the real-world objects the software is associated with. Example - An OO software system for air traffic control wo ...
... The OO paradigm is based on the idea that all aspects of software – its design, implementation, internal structure, as well as the supporting tools and language – should be based on the real-world objects the software is associated with. Example - An OO software system for air traffic control wo ...
UNIT-1 Introduction to System Programming
... lang. is m/c dependent. Assemblers with different syntax for a particular CPU or instruction set architecture. Example:- An instruction to add memory data to a register x86-family processor: add eax,[ebx], whereas this would be written addl (%ebx),%eax in the AT&T syntax used by the GNU Assemble ...
... lang. is m/c dependent. Assemblers with different syntax for a particular CPU or instruction set architecture. Example:- An instruction to add memory data to a register x86-family processor: add eax,[ebx], whereas this would be written addl (%ebx),%eax in the AT&T syntax used by the GNU Assemble ...
Uniform Proofs as a Foundation for Logic Programming
... Most logic programming languages can be thought of as implementations of the classical, first-order theory of Horn clauses. The language Prolog [29], for instance, is generally described using these formulas and its interpreter is based on SLD-resolution [1, 31]. Although the use of first-order Horn ...
... Most logic programming languages can be thought of as implementations of the classical, first-order theory of Horn clauses. The language Prolog [29], for instance, is generally described using these formulas and its interpreter is based on SLD-resolution [1, 31]. Although the use of first-order Horn ...
Relief for the Forlorn Programmer
... Intel x86 family of microprocessors (8086/8088 through Pentium and beyond). It offers the programmer complete control over the processor (formerly only available to assembly language programmers) without the tedium and bookkeeping chores formerly associated with this type of programming. This is ach ...
... Intel x86 family of microprocessors (8086/8088 through Pentium and beyond). It offers the programmer complete control over the processor (formerly only available to assembly language programmers) without the tedium and bookkeeping chores formerly associated with this type of programming. This is ach ...
ppt - Zoo - Yale University
... These features can be very useful and save time. • Example features are GUI compile, GUI execution, code completion, and syntax highlighting. ...
... These features can be very useful and save time. • Example features are GUI compile, GUI execution, code completion, and syntax highlighting. ...
Ebook Programming tools developers
... This is a wxWidgets user graphical interface written in Python, but that can generate source code for other programming languages such as C++, Lisp or Perl. wxGlade is not an integrated development environment with all the tools to develop in Python, it is just a designer that lets you view the widg ...
... This is a wxWidgets user graphical interface written in Python, but that can generate source code for other programming languages such as C++, Lisp or Perl. wxGlade is not an integrated development environment with all the tools to develop in Python, it is just a designer that lets you view the widg ...
Computing Science - Thompson Rivers University
... function; they come into existence when the function is entered, and disappear when it is left. External variables, on the other hand, are permanent, so they can retain values from one function invocation to the next. Thus if two functions must share some data, yet neither calls the other, it is oft ...
... function; they come into existence when the function is entered, and disappear when it is left. External variables, on the other hand, are permanent, so they can retain values from one function invocation to the next. Thus if two functions must share some data, yet neither calls the other, it is oft ...
IMUSIC - Interdisciplinary Centre for Computer Music Research
... as its tone-based input is designed to help such programmers access and learn scriptbased approaches to programming. IMUSIC evolved from MUSIC. The original proposal for MUSIC can be found here [1]. During its implementation Interactive MUSIC involved in which the program structure is continuously ...
... as its tone-based input is designed to help such programmers access and learn scriptbased approaches to programming. IMUSIC evolved from MUSIC. The original proposal for MUSIC can be found here [1]. During its implementation Interactive MUSIC involved in which the program structure is continuously ...
Programming Strategically for PK/PD Data
... It is critical to have this discussion with the pharmacometrician before start working on programming. Certain rules on data specification may be based on assumptions, which may not be appropriate based on the real data cases. Pay extreme attention on missing values in the data and missing value imp ...
... It is critical to have this discussion with the pharmacometrician before start working on programming. Certain rules on data specification may be based on assumptions, which may not be appropriate based on the real data cases. Pay extreme attention on missing values in the data and missing value imp ...
Software review The Bioà toolkits – a brief overview
... either Perl or Java for a novice to learn, encourages a cleaner programming style, and certainly makes it easier to follow others’ code. Python also has a large and growing base of additional software modules, including some that fall into the ‘Killer app’ category such as Zope,13 a combination web- ...
... either Perl or Java for a novice to learn, encourages a cleaner programming style, and certainly makes it easier to follow others’ code. Python also has a large and growing base of additional software modules, including some that fall into the ‘Killer app’ category such as Zope,13 a combination web- ...
01365p_chapter_05
... • By default, a session has a single DML queue and a transaction control statement would affect all DML in the queue regardless of which program unit initiated the statement • DML statements of a program unit can be treated separately or as an autonomous ...
... • By default, a session has a single DML queue and a transaction control statement would affect all DML in the queue regardless of which program unit initiated the statement • DML statements of a program unit can be treated separately or as an autonomous ...
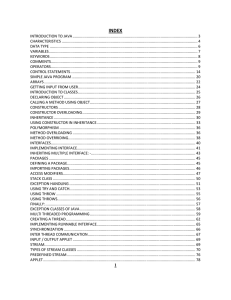
JAVA - Sunrise Academy, Ajmer
... easily as they can do in a local system this enables multiple programmers at multiple remote locations to collaborate and work together on a single project. 9. Dynamic: - Java is a more dynamic language than C and C++. This is an important feature in those situations in which code needs to be added ...
... easily as they can do in a local system this enables multiple programmers at multiple remote locations to collaborate and work together on a single project. 9. Dynamic: - Java is a more dynamic language than C and C++. This is an important feature in those situations in which code needs to be added ...
... • To write compilers and interpreters for various programming languages and domain-specific languages Examples: Java, JavaScript, C, C++, C#, Modula-3, Scheme, ML, Tcl/Tk, Database Query Lang., Mathematica, Matlab, Shell-Command-Languages, Awk, Perl, your .mailrc file, HTML, TeX, PostScript, Kermit ...
Chapter 1: Introduction to Computers and Java
... • These statements are known as source code. • A text editor is used to edit and save a Java source code file. • Source code files have a .java file extension. • A compiler is a program that translates source code into an executable form. ©2013 Pearson Education, Inc. Upper Saddle River, NJ. All Rig ...
... • These statements are known as source code. • A text editor is used to edit and save a Java source code file. • Source code files have a .java file extension. • A compiler is a program that translates source code into an executable form. ©2013 Pearson Education, Inc. Upper Saddle River, NJ. All Rig ...
Chapter 1
... • These statements are known as source code. • A text editor is used to edit and save a Java source code file. • Source code files have a .java file extension. • A compiler is a program that translates source code into an executable form. ©2013 Pearson Education, Inc. Upper Saddle River, NJ. All Rig ...
... • These statements are known as source code. • A text editor is used to edit and save a Java source code file. • Source code files have a .java file extension. • A compiler is a program that translates source code into an executable form. ©2013 Pearson Education, Inc. Upper Saddle River, NJ. All Rig ...
Object Oriented Programming
... A quick diversion from OOP here! At this point you might think it doesn't matter whether you use C++ or Java, they both implement object oriented technology. Well, C++ can be used to design programs without implementing any objects; C++ can be used as an extended C. In Java, you must implement any n ...
... A quick diversion from OOP here! At this point you might think it doesn't matter whether you use C++ or Java, they both implement object oriented technology. Well, C++ can be used to design programs without implementing any objects; C++ can be used as an extended C. In Java, you must implement any n ...
Chapter 9: Object-Oriented Software Development
... data from direct access by clients. You can use get methods and set methods to provide users with access to the private data, but only to private data you want the user to see or to modify. A class should also hide methods not intended for client use. The gcd method in the Rational class in Example ...
... data from direct access by clients. You can use get methods and set methods to provide users with access to the private data, but only to private data you want the user to see or to modify. A class should also hide methods not intended for client use. The gcd method in the Rational class in Example ...
Chapter 10 slides
... data from direct access by clients. You can use get methods and set methods to provide users with access to the private data, but only to private data you want the user to see or to modify. A class should also hide methods not intended for client use. The gcd method in the Rational class in Example ...
... data from direct access by clients. You can use get methods and set methods to provide users with access to the private data, but only to private data you want the user to see or to modify. A class should also hide methods not intended for client use. The gcd method in the Rational class in Example ...
call
... • Represent program code and data as lists • Every list returns a value, which will be used as an input of its upper level list. – The return value of the top level will be output ...
... • Represent program code and data as lists • Every list returns a value, which will be used as an input of its upper level list. – The return value of the top level will be output ...