ppt - NOISE
... broadcast storms – E.g., if the network contains a cycle of switches – Either accidentally, or by design for higher reliability ...
... broadcast storms – E.g., if the network contains a cycle of switches – Either accidentally, or by design for higher reliability ...
Ch_08 - UCF EECS
... through 4-kHz voice channels. We assume that each link uses FDM to connect a maximum of two voice channels. The bandwidth of each link is then 8 kHz. Figure 8.4 shows the situation. Telephone 1 is connected to telephone 7; 2 to 5; 3 to 8; and 4 to 6. Of course the situation may change when new conne ...
... through 4-kHz voice channels. We assume that each link uses FDM to connect a maximum of two voice channels. The bandwidth of each link is then 8 kHz. Figure 8.4 shows the situation. Telephone 1 is connected to telephone 7; 2 to 5; 3 to 8; and 4 to 6. Of course the situation may change when new conne ...
Glossary Of Telephony Terms
... Pulse Code Modulation. The most common method of encoding an analog voice signal into a digital bit stream. Prefix The leading digits of a telephone number. PRI See Primary Rate Interface below. Primary Rate Interface (PRI) One of two levels of ISDN service. In North America, the PRI typically provi ...
... Pulse Code Modulation. The most common method of encoding an analog voice signal into a digital bit stream. Prefix The leading digits of a telephone number. PRI See Primary Rate Interface below. Primary Rate Interface (PRI) One of two levels of ISDN service. In North America, the PRI typically provi ...
Overview of Switches
... Switches are widely being used today by most of the business networks to connect multiple devices such as computers, printers and servers that are present within a particular boundary like a campus or building. The switch is responsible for enabling communication between the networking devices on a ...
... Switches are widely being used today by most of the business networks to connect multiple devices such as computers, printers and servers that are present within a particular boundary like a campus or building. The switch is responsible for enabling communication between the networking devices on a ...
NFPA 72 FAQs
... alarm system at a protected premise to a supervising station. The most widely used means is a digital alarm communicator system. These systems use a digital alarm communicator transmitter (DACT) connected through two transmission channels. The Code requires the primary channel to be a telephon ...
... alarm system at a protected premise to a supervising station. The most widely used means is a digital alarm communicator system. These systems use a digital alarm communicator transmitter (DACT) connected through two transmission channels. The Code requires the primary channel to be a telephon ...
packet switching exchange (PSE)
... • Wide area networks connect multiple local area networks together. • If an organization wishes to have a wide area connection to another office, it needs to decide on a networking service and the speed at which it wishes to connect. ...
... • Wide area networks connect multiple local area networks together. • If an organization wishes to have a wide area connection to another office, it needs to decide on a networking service and the speed at which it wishes to connect. ...
presentation source
... • I wouldn’t waste fiber on anything less than 100Mbps. • Currently Gigabit Ethernet is only available using fiber. SX-short wave, LX-long wave ...
... • I wouldn’t waste fiber on anything less than 100Mbps. • Currently Gigabit Ethernet is only available using fiber. SX-short wave, LX-long wave ...
LAN Switching - Academic Server
... If two devices transmit simultaneously, a collision occurs. The NIC senses this because it is transmitting and receiving at the same time The first device to detect the collision will generate a jam signal (colliding devices continue to transmit so that all devices will hear the collision) All devic ...
... If two devices transmit simultaneously, a collision occurs. The NIC senses this because it is transmitting and receiving at the same time The first device to detect the collision will generate a jam signal (colliding devices continue to transmit so that all devices will hear the collision) All devic ...
Datacenter Network Topologies
... – Hash packet header to choose a path – All packets of the same flow go on the same path ...
... – Hash packet header to choose a path – All packets of the same flow go on the same path ...
Ch. 8 Circuit Switching - The Coming
... • Signaling Functions (cont.) – A signal to make the phone ring. – Transmission of information for billing. – Transmission of information giving status of equipment or lines. – Transmission of information used in diagnosing and ...
... • Signaling Functions (cont.) – A signal to make the phone ring. – Transmission of information for billing. – Transmission of information giving status of equipment or lines. – Transmission of information used in diagnosing and ...
Optical Burst Switching Obs.doc
... • Signaling Functions (cont.) – A signal to make the phone ring. – Transmission of information for billing. – Transmission of information giving status of equipment or lines. – Transmission of information used in diagnosing and ...
... • Signaling Functions (cont.) – A signal to make the phone ring. – Transmission of information for billing. – Transmission of information giving status of equipment or lines. – Transmission of information used in diagnosing and ...
Semester 3 Chapter 2 - IIS Windows Server
... The NIC senses this because it is transmitting and receiving at the same time The first device to detect the collision will generate a jam signal (colliding devices continue to transmit so that all devices will hear the collision) All devices calculate a backoff algorithm which will delay transmissi ...
... The NIC senses this because it is transmitting and receiving at the same time The first device to detect the collision will generate a jam signal (colliding devices continue to transmit so that all devices will hear the collision) All devices calculate a backoff algorithm which will delay transmissi ...
02_tcom5272_lan
... Bridges switch use software; switches typically switch using hardware (called the “switch fabric”) Bridges use store-and-forward, Switches can use cut-through switching which switches the packet as soon as the destination MAC is read M. Dahshan - TCOM5272 ...
... Bridges switch use software; switches typically switch using hardware (called the “switch fabric”) Bridges use store-and-forward, Switches can use cut-through switching which switches the packet as soon as the destination MAC is read M. Dahshan - TCOM5272 ...
Nodal Switch by Northrop Grumman
... the system is based on the use of industry-standard communications protocols and hardware. This standards-based approach allows the Nodal Switch to use standard commercial Ethernet switching equipment rather than proprietary hardware. This standardsbased approach allows direct connectivity to wide a ...
... the system is based on the use of industry-standard communications protocols and hardware. This standards-based approach allows the Nodal Switch to use standard commercial Ethernet switching equipment rather than proprietary hardware. This standardsbased approach allows direct connectivity to wide a ...
CCNA3 Chap1 practice testquestions
... Which is a desirable characteristic of an access layer switch allocated to a department where there are a large number of computer users? ...
... Which is a desirable characteristic of an access layer switch allocated to a department where there are a large number of computer users? ...
What are the Advantages and Disadvantages of a Policy
... employees, administrative support employees, meeting room and customer service were administered. The access switches were then configured using terminal to connect to the core as trunk ports. On the router device, the next step was to configure the ISP for the entire network by configuring the loop ...
... employees, administrative support employees, meeting room and customer service were administered. The access switches were then configured using terminal to connect to the core as trunk ports. On the router device, the next step was to configure the ISP for the entire network by configuring the loop ...
William Stallings Data and Computer Communications
... up to 100MHz Commonly pre-installed in new office buildings Twist length 0.6 cm to 0.85 cm ...
... up to 100MHz Commonly pre-installed in new office buildings Twist length 0.6 cm to 0.85 cm ...
Chapter_4_Transmission Media
... up to 100MHz Commonly pre-installed in new office buildings Twist length 0.6 cm to 0.85 cm ...
... up to 100MHz Commonly pre-installed in new office buildings Twist length 0.6 cm to 0.85 cm ...
06/07 Semester B - City University of Hong Kong
... (a) Given that n = (N/2)1/2 and that the number of links between stages is equal to the number of the incoming trunks, design a three-stage network for connecting 120 incoming trunks to 120 outgoing trunks. If there are more than one solution, determine which one is better. Draw the end result. [7 m ...
... (a) Given that n = (N/2)1/2 and that the number of links between stages is equal to the number of the incoming trunks, design a three-stage network for connecting 120 incoming trunks to 120 outgoing trunks. If there are more than one solution, determine which one is better. Draw the end result. [7 m ...
William Stallings Data and Computer Communications
... • up to 100MHz • Commonly pre-installed in new office buildings • Twist length 0.6 cm to 0.85 cm ...
... • up to 100MHz • Commonly pre-installed in new office buildings • Twist length 0.6 cm to 0.85 cm ...
Introduction - Eastern Illinois University
... - Class notes titled “Telecommunications Systems, Part 1”) - Class notes titled “Telecommunication Systems, Part 2” ...
... - Class notes titled “Telecommunications Systems, Part 1”) - Class notes titled “Telecommunication Systems, Part 2” ...
S3C2 – LAN Switching
... • Both bridges and switches connect LAN segments, use a table of MAC addresses to determine the segment on which a datagram needs to be transmitted, and reduce traffic. • Switches are more functional in today’s networks than bridges because they operate at much higher speeds than bridges and can sup ...
... • Both bridges and switches connect LAN segments, use a table of MAC addresses to determine the segment on which a datagram needs to be transmitted, and reduce traffic. • Switches are more functional in today’s networks than bridges because they operate at much higher speeds than bridges and can sup ...
ORCA BTX-8 and BTX-21 - Nuera Communications Inc
... of scalability and reliability for cable VoIP. This scalability and reliability enables cable network operators to efficiently build-out and maintain their networks. ...
... of scalability and reliability for cable VoIP. This scalability and reliability enables cable network operators to efficiently build-out and maintain their networks. ...
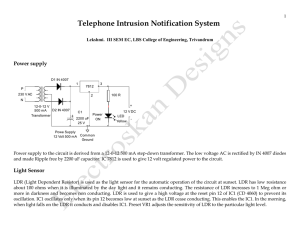
telephone-intrusion-notification-system
... IC1 as indicated by the blinking of LED 1(Green LED) connected to its output pin 7(Q3).The timeout period of the timer can be calculated using the formula t = 2 n / f osc = in seconds. ‘n’ is the selected Q output f osc = 1 / 2.5 (R1.C1) R1 is the resistor in ohms connected to the pin 10 and C1 is t ...
... IC1 as indicated by the blinking of LED 1(Green LED) connected to its output pin 7(Q3).The timeout period of the timer can be calculated using the formula t = 2 n / f osc = in seconds. ‘n’ is the selected Q output f osc = 1 / 2.5 (R1.C1) R1 is the resistor in ohms connected to the pin 10 and C1 is t ...
pptx - Cornell Computer Science
... Each pod consists of 12 racks with 48 machines each, and 48 individual 48-port GigE switches Place the 48 switches in a centralized rack Cables moves in sets of 12 from pod to pod and in sets of 48 from racks to pod switches opens additional opportunities for packing to reduce wiring ...
... Each pod consists of 12 racks with 48 machines each, and 48 individual 48-port GigE switches Place the 48 switches in a centralized rack Cables moves in sets of 12 from pod to pod and in sets of 48 from racks to pod switches opens additional opportunities for packing to reduce wiring ...
Telephone exchange

A telephone exchange is a telecommunications system used in the public switched telephone network or in large enterprises. An exchange consists of electronic components and in older systems also human operators that interconnect (switch) telephone subscriber lines or virtual circuits of digital systems to establish telephone calls between subscribers.In the public telecommunication networks a telephone exchange is located in a central office (CO), typically a building used to house the inside plant equipment of potentially several telephone exchanges, each serving a certain geographical exchange area. Central office locations are often identified in North America as wire centers, designating a facility from which a telephone obtains dial tone. For business and billing purposes, telephony carriers also define rate centers, which in larger cities may be clusters of central offices, to define specified geographical locations for determining distance measurements.In the United States and Canada, the Bell System established in the 1940s a uniform system of identifying each telephone exchange with a three-digit exchange code, or central office code, that was used as a prefix to subscriber telephone numbers. All exchanges within a larger region, typically aggregated by state, were assigned a common area code. With the development of international and transoceanic telephone trunks, especially driven by direct customer dialing, similar efforts of systematic organization of the telephone networks occurred in many countries in the mid-20th century.For corporate or enterprise use, a private telephone exchange is often referred to as a private branch exchange (PBX), when it has connections to the public switched telephone network. A PBX is installed in enterprise facilities, typically collocated with large office spaces or within an organizational campus to serve the local private telephone system and any private leased line circuits. Smaller installations might deploy a PBX or key telephone system in the office of a receptionist.