mm_streaming - College of Engineering | Oregon State University
... my_addr.sin_port = htons(MYPORT); // short, network byte order my_addr.sin_addr.s_addr = INADDR_ANY; // automatically fill with my IP memset(&(my_addr.sin_zero), '\0', 8); // zero the rest of the struct ...
... my_addr.sin_port = htons(MYPORT); // short, network byte order my_addr.sin_addr.s_addr = INADDR_ANY; // automatically fill with my IP memset(&(my_addr.sin_zero), '\0', 8); // zero the rest of the struct ...
Presentation - Arca Technologies
... Semi-permanent connection Semi-permanent/nailed-up connection on BRI/PRI B channels ...
... Semi-permanent connection Semi-permanent/nailed-up connection on BRI/PRI B channels ...
Demystifying Layer 2 and Layer 3 VPNs
... 4.2.10 Customer Control of Layer 3 Routing and IP Addressing ................................................................................................................................................. 32 4.2.11 National VLANs..................................................................... ...
... 4.2.10 Customer Control of Layer 3 Routing and IP Addressing ................................................................................................................................................. 32 4.2.11 National VLANs..................................................................... ...
chapter 5 - BWN-Lab
... Provides a structured & reliable means to transport signaling traffic between two ATM end users. As part of the C_PLANE (Control Plane), it serves as the interface between higher layer control & signaling functions such as UNI 3.1/Q.2931 and the ATM layer. SSCF: responsible for mapping the higher la ...
... Provides a structured & reliable means to transport signaling traffic between two ATM end users. As part of the C_PLANE (Control Plane), it serves as the interface between higher layer control & signaling functions such as UNI 3.1/Q.2931 and the ATM layer. SSCF: responsible for mapping the higher la ...
Trickle: A Userland Bandwidth Shaper for Unix-like Systems
... propagate. More detail regarding the interaction between this scheme and TCP is provided in section 4. While this scheme is practical, two issues would hinder widespread employment. Firstly, the scheme outlined is deceptively simple. As we will see in section 4, there are many details which make sha ...
... propagate. More detail regarding the interaction between this scheme and TCP is provided in section 4. While this scheme is practical, two issues would hinder widespread employment. Firstly, the scheme outlined is deceptively simple. As we will see in section 4, there are many details which make sha ...
Why Latency Lags Bandwidth, and What it Means to Computing
... multiple replicas of data at remote sites Caching (obviously) to reducing latency Replication: multiple requests to multiple copies and just use the quickest reply Prefetching to reduce latency Large block sizes for disk and memory Protocol: few very large messages – vs. chatty protocol with lots sm ...
... multiple replicas of data at remote sites Caching (obviously) to reducing latency Replication: multiple requests to multiple copies and just use the quickest reply Prefetching to reduce latency Large block sizes for disk and memory Protocol: few very large messages – vs. chatty protocol with lots sm ...
Presentation
... multiple replicas of data at remote sites Caching (obviously) to reducing latency Replication: multiple requests to multiple copies and just use the quickest reply Prefetching to reduce latency Large block sizes for disk and memory Protocol: few very large messages – vs. chatty protocol with lots sm ...
... multiple replicas of data at remote sites Caching (obviously) to reducing latency Replication: multiple requests to multiple copies and just use the quickest reply Prefetching to reduce latency Large block sizes for disk and memory Protocol: few very large messages – vs. chatty protocol with lots sm ...
TCAM - Renesas e-Learning
... address, and receives the data stored at the supplied address With a CAM, the operating system supplies the data, and the CAM returns a list of addresses where the data is stored, if it finds any A CAM searches the entire memory in one operation, so it is considerably faster than RAM Any switc ...
... address, and receives the data stored at the supplied address With a CAM, the operating system supplies the data, and the CAM returns a list of addresses where the data is stored, if it finds any A CAM searches the entire memory in one operation, so it is considerably faster than RAM Any switc ...
Cisco IP SLA`s
... IP SLA for Voice over IP • VoIP may be difficult to deploy when the network behavior is not well understood Cisco IOS IP SLAs will verify network readiness and QoS Measure critical performance for VoIP deployment Real time warning of network performance degradation IP SLA is universally available a ...
... IP SLA for Voice over IP • VoIP may be difficult to deploy when the network behavior is not well understood Cisco IOS IP SLAs will verify network readiness and QoS Measure critical performance for VoIP deployment Real time warning of network performance degradation IP SLA is universally available a ...
Msc Jian Li 2013 - Department of Electrical and Computer
... The success of the smart grid greatly depends on the advanced communication architectures. An advanced smart grid network should satisfy the future demands of the electric systems in terms of reliability and latency. The latest 4th-generation (4G) wireless technology, Long Term Evolution (LTE), is a ...
... The success of the smart grid greatly depends on the advanced communication architectures. An advanced smart grid network should satisfy the future demands of the electric systems in terms of reliability and latency. The latest 4th-generation (4G) wireless technology, Long Term Evolution (LTE), is a ...
International Electrical Engineering Journal (IEEJ) Vol. 6 (2015) No.2, pp. 1765-1770
... Abstract— The paper proposes a new concept of protection philosophy for Distribution Grids with high penetration of renewable energy. Conventional protection concepts are normally based on protection schemes that consist of definite or inverse time overcurrent relays. In future power systems, these ...
... Abstract— The paper proposes a new concept of protection philosophy for Distribution Grids with high penetration of renewable energy. Conventional protection concepts are normally based on protection schemes that consist of definite or inverse time overcurrent relays. In future power systems, these ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... join and leave a network easily. But this flexibility of mobile nodes results in a dynamic topology that makes it very difficult in developing secure ad-hoc routing protocols. Wireless communication is always unreliable. The use of wireless links renders a mobile ad-hoc network to be vulnerable to a ...
... join and leave a network easily. But this flexibility of mobile nodes results in a dynamic topology that makes it very difficult in developing secure ad-hoc routing protocols. Wireless communication is always unreliable. The use of wireless links renders a mobile ad-hoc network to be vulnerable to a ...
Example towards RFI - The Alliance for Telecommunications
... devices have their own telemetry capabilities to send digital data to the supervisory system like RTUs, whereas some have separate communications equipment located adjacent to the sensor/control device since they do not provide their own telemetry (e.g., PLCs). Unique requirements include reliabilit ...
... devices have their own telemetry capabilities to send digital data to the supervisory system like RTUs, whereas some have separate communications equipment located adjacent to the sensor/control device since they do not provide their own telemetry (e.g., PLCs). Unique requirements include reliabilit ...
IP-MPLS - E-Photon One +
... A sub-problem is solved after the branching operation has been performed on it A sub-problem is completed if it is solved and either it is a leaf or both its children are completed Every process maintains a list of new locally completed problems and a table of the completed problems it knows about T ...
... A sub-problem is solved after the branching operation has been performed on it A sub-problem is completed if it is solved and either it is a leaf or both its children are completed Every process maintains a list of new locally completed problems and a table of the completed problems it knows about T ...
Physical Layer Pt1 - Faculty of Computer Science and Information
... •Throughput is the actual transfer rate of data over the medium in a period of time. •Throughput, like bandwidth, is measured in bits per second. •Many factors influence throughput, including the following: • The amount of traffic • The type of traffic • The number of network devices encountered on ...
... •Throughput is the actual transfer rate of data over the medium in a period of time. •Throughput, like bandwidth, is measured in bits per second. •Many factors influence throughput, including the following: • The amount of traffic • The type of traffic • The number of network devices encountered on ...
ITE PC v4.0 Chapter 1 - Система е
... Different applications have different transport reliability requirements TCP/IP provides two transport layer protocols, TCP and UDP Transmission Control Protocol (TCP) Provides reliable delivery ensuring that all of the data arrives at the destination. Uses acknowledged delivery and other proces ...
... Different applications have different transport reliability requirements TCP/IP provides two transport layer protocols, TCP and UDP Transmission Control Protocol (TCP) Provides reliable delivery ensuring that all of the data arrives at the destination. Uses acknowledged delivery and other proces ...
ITE PC v4.0 Chapter 1
... Different applications have different transport reliability requirements TCP/IP provides two transport layer protocols, TCP and UDP Transmission Control Protocol (TCP) Provides reliable delivery ensuring that all of the data arrives at the destination. Uses acknowledged delivery and other proces ...
... Different applications have different transport reliability requirements TCP/IP provides two transport layer protocols, TCP and UDP Transmission Control Protocol (TCP) Provides reliable delivery ensuring that all of the data arrives at the destination. Uses acknowledged delivery and other proces ...
Voice
... • Voice payload calculation 20 msec voice sample * 8 Kbps (for G.729)/8 bits/byte = 20 bytes Note: to derive the payload for G.711, substitute 64 Kbps = ...
... • Voice payload calculation 20 msec voice sample * 8 Kbps (for G.729)/8 bits/byte = 20 bytes Note: to derive the payload for G.711, substitute 64 Kbps = ...
Xilinx Wireless Backhaul Solutions
... reliability, timing, and cost constraints are paramount. The Xilinx solution supports legacy interfaces such as multiple E1/T1 and SDH as well as Gigabit Ethernet. Data rates are scalable up to 1Gbps in a single polarization and 2Gbps in dual-polarized mode. Enhanced phase noise tolerance enables BO ...
... reliability, timing, and cost constraints are paramount. The Xilinx solution supports legacy interfaces such as multiple E1/T1 and SDH as well as Gigabit Ethernet. Data rates are scalable up to 1Gbps in a single polarization and 2Gbps in dual-polarized mode. Enhanced phase noise tolerance enables BO ...
Fax over IP recommendations
... any changes to the devices they are responsible for or to their firmware or software statuses. Practical use shows that, even with successfully tested constellations, following adjustment of a single component (e.g. new ATA box, new software release, re-configuration of the fax on the opposite end), ...
... any changes to the devices they are responsible for or to their firmware or software statuses. Practical use shows that, even with successfully tested constellations, following adjustment of a single component (e.g. new ATA box, new software release, re-configuration of the fax on the opposite end), ...
chapter 1 - Test Banks | Solution Manuals
... Work processes that are customer-focused and with results built on quality measurement 5. Communication and knowledge sharing for improvement One key difference appears to be that the new approaches were not just “handed down” by management, but required a new commitment and involvement of managemen ...
... Work processes that are customer-focused and with results built on quality measurement 5. Communication and knowledge sharing for improvement One key difference appears to be that the new approaches were not just “handed down” by management, but required a new commitment and involvement of managemen ...
Wireless Sensor Networks for Habitat Monitoring
... an idiosyncratic instance. Second, they provide a context in which some problems have simple, concrete solutions while others remain open research areas. Third, an application-driven approach separates actual problems from potential ones, and relevant issues from irrelevant ones. Finally, collaborat ...
... an idiosyncratic instance. Second, they provide a context in which some problems have simple, concrete solutions while others remain open research areas. Third, an application-driven approach separates actual problems from potential ones, and relevant issues from irrelevant ones. Finally, collaborat ...
Presentation
... Ensure proper segmentation of voice and data packets on the same physical network as well as prevent data network security threats from affecting voice services Shift from the traditional, reactive mindset of monitoring PBX-based voice to a proactive mindset where problems are identified before ...
... Ensure proper segmentation of voice and data packets on the same physical network as well as prevent data network security threats from affecting voice services Shift from the traditional, reactive mindset of monitoring PBX-based voice to a proactive mindset where problems are identified before ...
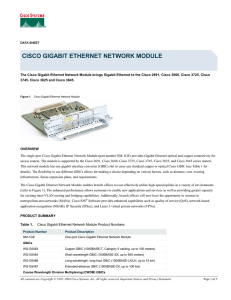
CISCO GIGABIT ETHERNET NETWORK MODULE
... The single-port Cisco Gigabit Ethernet Network Module (part number NM-1GE) provides Gigabit Ethernet optical and copper connectivity for access routers. The module is supported by the Cisco 2691, Cisco 3660, Cisco 3725, Cisco 3745, Cisco 3825, and Cisco 3845 series routers. This network module has o ...
... The single-port Cisco Gigabit Ethernet Network Module (part number NM-1GE) provides Gigabit Ethernet optical and copper connectivity for access routers. The module is supported by the Cisco 2691, Cisco 3660, Cisco 3725, Cisco 3745, Cisco 3825, and Cisco 3845 series routers. This network module has o ...