Cisco IP SLA`s
... • Enterprise will verify SP SLAs by using access router edge to edge measurements Enterprise may provide restricted Simple Network Management Protocol (SNMP) (RTT, Latency, QoS) visibility into Access router for Service Provider Service Provider with restricted access can report SLA as a service bac ...
... • Enterprise will verify SP SLAs by using access router edge to edge measurements Enterprise may provide restricted Simple Network Management Protocol (SNMP) (RTT, Latency, QoS) visibility into Access router for Service Provider Service Provider with restricted access can report SLA as a service bac ...
FTT-10A Free Topology Twisted Pair Transceiver
... LPT-10 Link Power Transceiver, and these transceivers can communicate with each other on a single twisted pair cable. This capability provides an inexpensive means of interfacing to nodes whose current or voltage requirements would otherwise exceed the capacity of the link power segment. When equipp ...
... LPT-10 Link Power Transceiver, and these transceivers can communicate with each other on a single twisted pair cable. This capability provides an inexpensive means of interfacing to nodes whose current or voltage requirements would otherwise exceed the capacity of the link power segment. When equipp ...
6 Multi-layer Recovery Strategy in Resilient Packet
... Thus, the introduction of RPR-based metropolitan networks is gaining importance and it represents a very promising networking solution to transport data traffic in a short/medium term. In fact, the IEEE 802.17 RPR standard has been approved in June 2004 and thus, network equipments standard-complian ...
... Thus, the introduction of RPR-based metropolitan networks is gaining importance and it represents a very promising networking solution to transport data traffic in a short/medium term. In fact, the IEEE 802.17 RPR standard has been approved in June 2004 and thus, network equipments standard-complian ...
Guidelines for Reliable Long Line 1-Wire Networks
... conditions during searches are much different from normal communications with a single selected slave. If any of many slaves misses an edge or fails to discriminate a pulse, then it will become unsynchronized with the search algorithm and will cause errors in subsequent bits of the search. This mean ...
... conditions during searches are much different from normal communications with a single selected slave. If any of many slaves misses an edge or fails to discriminate a pulse, then it will become unsynchronized with the search algorithm and will cause errors in subsequent bits of the search. This mean ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... power unsettling influences and blackouts and frequently bring about long administration interferences. Electric framework mechanization, which is the production of a dependable, self-recuperating electric framework that quickly reacts to constant occasions with proper activities, plans to keep up c ...
... power unsettling influences and blackouts and frequently bring about long administration interferences. Electric framework mechanization, which is the production of a dependable, self-recuperating electric framework that quickly reacts to constant occasions with proper activities, plans to keep up c ...
BayStack LAN Switching
... These have been shown with a ? in the individual product codes. The ? should be replaced by the relevant country code below to make up a valid product code that Nortel Networks will recognise ...
... These have been shown with a ? in the individual product codes. The ? should be replaced by the relevant country code below to make up a valid product code that Nortel Networks will recognise ...
FTT-10A Free Topology Twisted Pair Tranceiver Datasheet
... The FTT-10A transceiver consists of an isolation transformer that is integrated with a 78kbps differential Manchester coded communication transceiver. Pins are provided for connection to the Neuron Chip Communications Port (CP) and clock lines, +5V power, and the twisted pair network. The pins are k ...
... The FTT-10A transceiver consists of an isolation transformer that is integrated with a 78kbps differential Manchester coded communication transceiver. Pins are provided for connection to the Neuron Chip Communications Port (CP) and clock lines, +5V power, and the twisted pair network. The pins are k ...
ITE PC v4.0 Chapter 1
... communication session between two applications and delivering data between them. TCP/IP uses two protocols to achieve this: Transmission Control Protocol (TCP) User Datagram Protocol (UDP) Primary Responsibilities of Transport Layer Protocols Tracking the individual communication between appli ...
... communication session between two applications and delivering data between them. TCP/IP uses two protocols to achieve this: Transmission Control Protocol (TCP) User Datagram Protocol (UDP) Primary Responsibilities of Transport Layer Protocols Tracking the individual communication between appli ...
VCL-EC_E1_VQE_&_Echo Canceller
... echo-tail displacement feature which may be programmed by the user, between 0ms. to 512ms. on the return path to cancel echo-tails, both at the near-end and the far-end, in the most demanding network conditions. This solution is also an ideal echo cancellation solution for long distance telephony, G ...
... echo-tail displacement feature which may be programmed by the user, between 0ms. to 512ms. on the return path to cancel echo-tails, both at the near-end and the far-end, in the most demanding network conditions. This solution is also an ideal echo cancellation solution for long distance telephony, G ...
DYNAMIC MANAGEMENT AND RESTORATION OF VIRTUAL PATHS IN BROADBAND NETWORKS
... Network management is a wide field including topics as diverse as fault restoration, network utilisation accounting, network elements configuration, security, performance monitoring, etc. This thesis focuses on resource management of broadband networks that have the mechanisms for performing resourc ...
... Network management is a wide field including topics as diverse as fault restoration, network utilisation accounting, network elements configuration, security, performance monitoring, etc. This thesis focuses on resource management of broadband networks that have the mechanisms for performing resourc ...
VCL-EC_T1_VQE_&_Echo Canceller
... echo-tail displacement feature which may be programmed by the user, between 0ms. to 512 ms. on the return path to cancel echo-tails, both at the near-end and the far-end, in the most demanding network conditions. This solution is also an ideal echo cancellation solution for long distance telephony, ...
... echo-tail displacement feature which may be programmed by the user, between 0ms. to 512 ms. on the return path to cancel echo-tails, both at the near-end and the far-end, in the most demanding network conditions. This solution is also an ideal echo cancellation solution for long distance telephony, ...
Introduction - School of Engineering
... What are the uncompressed bit rates for the following multimedia sources : a) Telephone voice signal with a bandwidth between 200 and 3400 Hz, sampled with 8000 samples/s and 12 bit/sample. b) Wideband speech signal with a bandwidth between 50 and 7000 Hz, sampled with 16000 samples/s and 14 bit/sam ...
... What are the uncompressed bit rates for the following multimedia sources : a) Telephone voice signal with a bandwidth between 200 and 3400 Hz, sampled with 8000 samples/s and 12 bit/sample. b) Wideband speech signal with a bandwidth between 50 and 7000 Hz, sampled with 16000 samples/s and 14 bit/sam ...
Ethernet - Computer Science Technology
... Ethernet, CSMA/CD must also be used • When using a switched topology, a computer can send and receive data simultaneously (full-duplex communication) – The collision detection circuitry is turned off because collisions aren’t possible – Results in a considerable performance advantage ...
... Ethernet, CSMA/CD must also be used • When using a switched topology, a computer can send and receive data simultaneously (full-duplex communication) – The collision detection circuitry is turned off because collisions aren’t possible – Results in a considerable performance advantage ...
TCP Fairness Issues
... – ECN must be supported by both TCP senders and receivers. – ECN-compliant TCP senders initiate their congestion avoidance algorithm after receiving marked ACK packets from the TCP receiver – A RED extension that marks packets to signal congestion ...
... – ECN must be supported by both TCP senders and receivers. – ECN-compliant TCP senders initiate their congestion avoidance algorithm after receiving marked ACK packets from the TCP receiver – A RED extension that marks packets to signal congestion ...
Annex B – Routing Area Reorganization in IETF (as of Nov
... services. Line services are point-to-point in nature and include services like Ethernet private and virtual lines. LAN services are multi-point-to-multi-point (such as virtual LAN services). Access services are of hub-and-spoke nature and enable single ISP/ASP to serve multiple, distinct, customers. ...
... services. Line services are point-to-point in nature and include services like Ethernet private and virtual lines. LAN services are multi-point-to-multi-point (such as virtual LAN services). Access services are of hub-and-spoke nature and enable single ISP/ASP to serve multiple, distinct, customers. ...
RAD Katalog 2016
... •• Open NFV/SDN architecture facilitates integration with network-wide orchestrators and ...
... •• Open NFV/SDN architecture facilitates integration with network-wide orchestrators and ...
Cisco 7200 Series Routers
... Layer 2 and Layer 3 protocols—Address Resolution Protocol (ARP), IPCP, IP forwarding, IP host, IP Multicast, PPPover-ATM, TCP, Telnet, Trivial File Transfer Protocol (TFTP), User Datagram Protocol (UDP), transparent bridging, virtual LAN (VLAN), MPLS, and IPv6 ...
... Layer 2 and Layer 3 protocols—Address Resolution Protocol (ARP), IPCP, IP forwarding, IP host, IP Multicast, PPPover-ATM, TCP, Telnet, Trivial File Transfer Protocol (TFTP), User Datagram Protocol (UDP), transparent bridging, virtual LAN (VLAN), MPLS, and IPv6 ...
P1547-6-Minutes-20060804 - IEEE Standards working groups
... Low voltgage alternating current networks were first developed in the 1920’s to provide highly reliable electric service to concentrated load centers mainly in the downtown areas of major cities. There are two types of low voltage networks, the secondary network (also referred to as an area network, ...
... Low voltgage alternating current networks were first developed in the 1920’s to provide highly reliable electric service to concentrated load centers mainly in the downtown areas of major cities. There are two types of low voltage networks, the secondary network (also referred to as an area network, ...
Business Ready Branch Solutions for Enterprise and Small
... surveillance cameras, cash registers, kiosks, and inventory scanners all require the connection to the corporate network over the LAN. This assortment of devices requires simplified connectivity tailored to the demands of each device. For example, devices such as IP telephones or cameras may be powe ...
... surveillance cameras, cash registers, kiosks, and inventory scanners all require the connection to the corporate network over the LAN. This assortment of devices requires simplified connectivity tailored to the demands of each device. For example, devices such as IP telephones or cameras may be powe ...
5. Network Connection - National Electricity Code Administrator
... reasonable requirements of the Connection Applicant, including without limitation, the location of the proposed connection point and the level and standard of power transfer capability that the network will provide. ...
... reasonable requirements of the Connection Applicant, including without limitation, the location of the proposed connection point and the level and standard of power transfer capability that the network will provide. ...
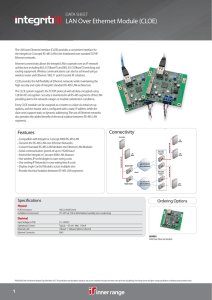
LAN Over Ethernet Module (CLOE)
... the Integriti (or Concept) RS-485 LAN to be distributed over standard TCP/IP Ethernet networks. Ethernet connectivity allows the Integriti LAN to operate over an IP network architecture including 802.3i (10baseT) and 802.3U (100baseT) switching and routing equipment. Wireless communications can also ...
... the Integriti (or Concept) RS-485 LAN to be distributed over standard TCP/IP Ethernet networks. Ethernet connectivity allows the Integriti LAN to operate over an IP network architecture including 802.3i (10baseT) and 802.3U (100baseT) switching and routing equipment. Wireless communications can also ...
Aalborg Universitet Adaptive Capacity Management in Bluetooth Networks Son, L.T.
... in short radio range, highly dynamic network environment, low power, and scarce resources, many new research challenges occur, such as limited wireless bandwidth operation, routing, scheduling, network control, etc. Currently Bluetooth specification particularly does not describe in details about ho ...
... in short radio range, highly dynamic network environment, low power, and scarce resources, many new research challenges occur, such as limited wireless bandwidth operation, routing, scheduling, network control, etc. Currently Bluetooth specification particularly does not describe in details about ho ...
WiMAX Protocol - London South Bank University
... diffused in broad-casting 360 degrees This limits its range and ultimately signal strength ...
... diffused in broad-casting 360 degrees This limits its range and ultimately signal strength ...
Achieving WAN Operational Efficiency with the Cisco ASR 1000 Series
... multiservice routers with the highest performance, availability, and density for concurrent data, security, voice, and application-acceleration services with maximum headroom for growth. Cisco ASR 1000 Series Aggregation Services Routers feature embedded security, performance, and memory enhancement ...
... multiservice routers with the highest performance, availability, and density for concurrent data, security, voice, and application-acceleration services with maximum headroom for growth. Cisco ASR 1000 Series Aggregation Services Routers feature embedded security, performance, and memory enhancement ...
No Slide Title
... Companies using RS-485 claim an advantage of higher bit rates (19.2K or faster) compared to INCOM (9.6K). One consultant tested the distance constraints for a leading vendor using RS-485 at 19.2K and found reliable communication could be guaranteed only if the network length was less than 4 feet. ...
... Companies using RS-485 claim an advantage of higher bit rates (19.2K or faster) compared to INCOM (9.6K). One consultant tested the distance constraints for a leading vendor using RS-485 at 19.2K and found reliable communication could be guaranteed only if the network length was less than 4 feet. ...