Leading Networking Solutions for Industrial
... line interface), providing secure remote configuration through the network. Configuration data and device Operating System can be saved and stored on an external flash-based configuration storage device, simplifying and automating commissioning and device replacement. Assured Enterprise Interoperabi ...
... line interface), providing secure remote configuration through the network. Configuration data and device Operating System can be saved and stored on an external flash-based configuration storage device, simplifying and automating commissioning and device replacement. Assured Enterprise Interoperabi ...
Lenovo Network Application Guide for Lenovo Cloud Network
... Services Administration “GSA” contract, use, reproduction, or disclosure is subject to restrictions set forth in Contract No. GS-35F-05925. Lenovo and the Lenovo logo are trademarks of Lenovo in the United States, other countries, or both. ...
... Services Administration “GSA” contract, use, reproduction, or disclosure is subject to restrictions set forth in Contract No. GS-35F-05925. Lenovo and the Lenovo logo are trademarks of Lenovo in the United States, other countries, or both. ...
IBM N/OS 6.8 for RackSwitch G8124/G8124-E
... VLANs Overview. . . . . . . . . . . . VLANs and Port VLAN ID Numbers . . . . VLAN Numbers . . . . . . . . . . PVID Numbers . . . . . . . . . . . VLAN Tagging . . . . . . . . . . . . VLAN Topologies and Design Considerations Multiple VLANs with Tagging Adapters . VLAN Configuration Example . . . . . ...
... VLANs Overview. . . . . . . . . . . . VLANs and Port VLAN ID Numbers . . . . VLAN Numbers . . . . . . . . . . PVID Numbers . . . . . . . . . . . VLAN Tagging . . . . . . . . . . . . VLAN Topologies and Design Considerations Multiple VLANs with Tagging Adapters . VLAN Configuration Example . . . . . ...
Release Notes for Catalyst 3850 Series Switch, Cisco IOS XE
... Zone) controller via tunneling. The guest access solution is also used as a fallback method for guest clients that fail dot1x and MAB authentication methods. This document covers deployment of wired guest access feature on Catalyst 3850 switch as foreign anchor and Cisco 5760 Wireless LAN controller ...
... Zone) controller via tunneling. The guest access solution is also used as a fallback method for guest clients that fail dot1x and MAB authentication methods. This document covers deployment of wired guest access feature on Catalyst 3850 switch as foreign anchor and Cisco 5760 Wireless LAN controller ...
Cisco Catalyst 3750 Series Switches Data Sheet
... ● Autosensing on each non-SFP port detects the speed of the attached device and automatically configures the port for 10-, 100-, or 1000-Mbps operation, easing switch deployment in mixed 10, 100, and 1000BASE-T environments. ● Autonegotiating on all ports automatically selects half- or full-duplex t ...
... ● Autosensing on each non-SFP port detects the speed of the attached device and automatically configures the port for 10-, 100-, or 1000-Mbps operation, easing switch deployment in mixed 10, 100, and 1000BASE-T environments. ● Autonegotiating on all ports automatically selects half- or full-duplex t ...
BACnet in China
... • Configurable by web browser – Virtual local area network (VLAN) – Quality of Service (QoS) – Port security, rate limiting and port mirroring – RSTP or RapidRing® cable redundancy – Programmable fault relay ...
... • Configurable by web browser – Virtual local area network (VLAN) – Quality of Service (QoS) – Port security, rate limiting and port mirroring – RSTP or RapidRing® cable redundancy – Programmable fault relay ...
Demystifying Layer 2 and Layer 3 VPNs
... Figure 1. — Leased Line Private Network (Layer 1) ................................................................................................................................................................................... 8 Figure 2. — Examples of Private Networks ........................... ...
... Figure 1. — Leased Line Private Network (Layer 1) ................................................................................................................................................................................... 8 Figure 2. — Examples of Private Networks ........................... ...
PDF
... The Gigabit Ethernet EHWIC enables branch offices to cost-effectively use high-speed uplinks in numerous environments (Figure 1). The enhanced performance of Gigabit Ethernet in Cisco ISR G2 routers enables new applications and services and provides greater capacity for existing IVR and bridging cap ...
... The Gigabit Ethernet EHWIC enables branch offices to cost-effectively use high-speed uplinks in numerous environments (Figure 1). The enhanced performance of Gigabit Ethernet in Cisco ISR G2 routers enables new applications and services and provides greater capacity for existing IVR and bridging cap ...
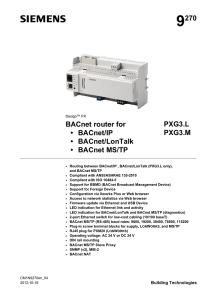
PXG3.L, PXG3.M BACnet Router
... access from a public network to BACnet devices in a private network is possible. Important: the public IP address must be static. For details see standard 135-2010. ...
... access from a public network to BACnet devices in a private network is possible. Important: the public IP address must be static. For details see standard 135-2010. ...
Brocade VDX 6940 Switch data sheet
... computing environments, compromising performance, increasing latency, and creating bottlenecks. With the increased prevalence of virtualization and distributed applications, data center network traffic is now predominantly east-west or serverserver. The VCS fabric was specifically designed and optim ...
... computing environments, compromising performance, increasing latency, and creating bottlenecks. With the increased prevalence of virtualization and distributed applications, data center network traffic is now predominantly east-west or serverserver. The VCS fabric was specifically designed and optim ...
Introducing the Specifications of the MEF
... – Service Frames containing the protocol will be transported across the MEN to the destination UNI(s) without change ...
... – Service Frames containing the protocol will be transported across the MEN to the destination UNI(s) without change ...
March 31, 2006 - Cisco Communications for the Small or Branch Office
... • Network privacy (Proxy/NAT equivalent) Provides the ability to “Peer” with other networks and only provide a single address/port hiding internal topology of a SP Network ...
... • Network privacy (Proxy/NAT equivalent) Provides the ability to “Peer” with other networks and only provide a single address/port hiding internal topology of a SP Network ...
BayStack LAN Switching
... across multiple devices. Device Manager is the configuration tool for those functions that require communicating with a single device. However, Device Manager uses a common user interface and workflow that supports many Nortel Networks Ethernet Switches. This commonality allows the network manager t ...
... across multiple devices. Device Manager is the configuration tool for those functions that require communicating with a single device. However, Device Manager uses a common user interface and workflow that supports many Nortel Networks Ethernet Switches. This commonality allows the network manager t ...
RAD Katalog 2016
... operation, with software-based functions running on an x86 D-NFV module integrated within RAD’s Megaplex-4 • Integrates higher-level applications (routing, firewall, encryption, SCADA, and more) with communications platform in a single device ...
... operation, with software-based functions running on an x86 D-NFV module integrated within RAD’s Megaplex-4 • Integrates higher-level applications (routing, firewall, encryption, SCADA, and more) with communications platform in a single device ...
Nortel Secure Network Access 2.0 802.1X
... and the Network Access Protection (NAP) concurrently. These components interoperate, allowing customers to enforce security policies for network access using both NSNA and NAP. This architecture allows deployment of NAP clients with or without a Windows 2008 Server based Network Policy Server (NPS) ...
... and the Network Access Protection (NAP) concurrently. These components interoperate, allowing customers to enforce security policies for network access using both NSNA and NAP. This architecture allows deployment of NAP clients with or without a Windows 2008 Server based Network Policy Server (NPS) ...
IBM Networking OS Application Guide for the IBM Flex System
... Chapter 8 Ports and Trunking . . . . . Configuring Port Modes . . . . . . . . Trunking Overview . . . . . . . . . . Static Trunks . . . . . . . . . . . . Before Configuring Static Trunks . . . Static Trunk Group Configuration Rules Configuring a Static Port Trunk . . . Configurable Trunk Hash Algori ...
... Chapter 8 Ports and Trunking . . . . . Configuring Port Modes . . . . . . . . Trunking Overview . . . . . . . . . . Static Trunks . . . . . . . . . . . . Before Configuring Static Trunks . . . Static Trunk Group Configuration Rules Configuring a Static Port Trunk . . . Configurable Trunk Hash Algori ...
Dimension ES-4024 Ethernet Switch: User`s Guide
... herein. Neither does it convey any license under its patent rights nor the patents rights of others. ZyXEL further reserves the right to make changes in any products described herein without notice. This publication is subject to change without notice. ...
... herein. Neither does it convey any license under its patent rights nor the patents rights of others. ZyXEL further reserves the right to make changes in any products described herein without notice. This publication is subject to change without notice. ...
Motorola Outdoor System Planner
... This outdoor Wi-Fi planning guide has been written in a step-by-step process that should assist the end user in designing and deploying a basic outdoor Motorola Solutions MCX (MeshConnex™) outdoor wireless network. The guide also includes details of the 802.11n features and its impacts on outdoor de ...
... This outdoor Wi-Fi planning guide has been written in a step-by-step process that should assist the end user in designing and deploying a basic outdoor Motorola Solutions MCX (MeshConnex™) outdoor wireless network. The guide also includes details of the 802.11n features and its impacts on outdoor de ...
PDF
... security to protect your business. The switches provide embedded encryption capabilities to help ensure that all management traffic to and from the device is protected with Secure Sockets Layer (SSL) encryption. The Cisco Catalyst 520 Series also provides built-in support for advanced security servi ...
... security to protect your business. The switches provide embedded encryption capabilities to help ensure that all management traffic to and from the device is protected with Secure Sockets Layer (SSL) encryption. The Cisco Catalyst 520 Series also provides built-in support for advanced security servi ...
2930F TAA Switch Series Data Sheet
... • IEEE 802.1v protocol VLANs isolate select non-IPv4 protocols automatically into their own VLANs • Rapid Per-VLAN Spanning Tree (RPVST+) allows each VLAN to build a separate spanning tree to improve link bandwidth usage; is compatible with PVST+ • GVRP and MVRP allows automatic learning and dynamic ...
... • IEEE 802.1v protocol VLANs isolate select non-IPv4 protocols automatically into their own VLANs • Rapid Per-VLAN Spanning Tree (RPVST+) allows each VLAN to build a separate spanning tree to improve link bandwidth usage; is compatible with PVST+ • GVRP and MVRP allows automatic learning and dynamic ...
Performance Enhancement of TFRC in Wireless Networks
... Four pairs of Category 5 UTP. IEEE 802.3ab ratified in June 1999. Category 5, 6 and 7 copper up to 100 meters. This requires extensive signal processing. ...
... Four pairs of Category 5 UTP. IEEE 802.3ab ratified in June 1999. Category 5, 6 and 7 copper up to 100 meters. This requires extensive signal processing. ...
IP Networking Guide - Plantec Distribuidora
... When using the IP telephones and V-IPGW16 card, you must ensure that the IP network in use has enough bandwidth to support VoIP communications. If the amount of bandwidth required for VoIP communications is more than the network can accommodate, speech quality will be compromised. In addition, there ...
... When using the IP telephones and V-IPGW16 card, you must ensure that the IP network in use has enough bandwidth to support VoIP communications. If the amount of bandwidth required for VoIP communications is more than the network can accommodate, speech quality will be compromised. In addition, there ...