Efficient Mining High Utility Itemsets From Transactional
... essential information in UP-Tree. By these approaches, overestimated utilities of candidates can be well reduced by discarding utilities of the items that cannot be high utility or are not included in the search space. Not only proposed strategies can decrease the overestimated utilities of PHUIs bu ...
... essential information in UP-Tree. By these approaches, overestimated utilities of candidates can be well reduced by discarding utilities of the items that cannot be high utility or are not included in the search space. Not only proposed strategies can decrease the overestimated utilities of PHUIs bu ...
Machine Learning Based Data Pre-processing for
... containing missing values and imbalanced with regards to the outcome class label. Many real-life data sets are incomplete, with missing values. In medical data mining the problem with missing values has become a challenging issue. In many clinical trials, the medical report proforma allow some attri ...
... containing missing values and imbalanced with regards to the outcome class label. Many real-life data sets are incomplete, with missing values. In medical data mining the problem with missing values has become a challenging issue. In many clinical trials, the medical report proforma allow some attri ...
Mining Temporal Sequential Patterns Based on Multi
... recurrent illnesses, system performance analysis and telecommunication network analysis etc. The problem of mining sequential patterns was first proposed by Agrawal and Strikant [3]: Given a data set of sequences, each sequence is a list of transactions, where each transaction is a set of items. The ...
... recurrent illnesses, system performance analysis and telecommunication network analysis etc. The problem of mining sequential patterns was first proposed by Agrawal and Strikant [3]: Given a data set of sequences, each sequence is a list of transactions, where each transaction is a set of items. The ...
NEW DENSITY-BASED CLUSTERING TECHNIQUE Rwand D. Ahmed
... Density Based Spatial Clustering of Applications of Noise (DBSCAN) is one of the most popular algorithms for cluster analysis. It can discover clusters with arbitrary shape and separate noises. But this algorithm cannot choose its parameter according to distribution of dataset. It simply uses the gl ...
... Density Based Spatial Clustering of Applications of Noise (DBSCAN) is one of the most popular algorithms for cluster analysis. It can discover clusters with arbitrary shape and separate noises. But this algorithm cannot choose its parameter according to distribution of dataset. It simply uses the gl ...
TopCat: Data Mining for Topic Identification in a Text
... multiple names may be used for a single entity. This gives us a high correlation between different variants of a name (e.g., Rios and Marcelo Rios) that add no useful information. We want to capture that these all refer to the same entity, mapping multiple instances to the same variant of the name, ...
... multiple names may be used for a single entity. This gives us a high correlation between different variants of a name (e.g., Rios and Marcelo Rios) that add no useful information. We want to capture that these all refer to the same entity, mapping multiple instances to the same variant of the name, ...
PPT
... Data Mining Classification: Basic Concepts, Decision Trees, and Model Evaluation Lecture Notes for Chapter 4 Introduction to Data Mining by Minqi Zhou ...
... Data Mining Classification: Basic Concepts, Decision Trees, and Model Evaluation Lecture Notes for Chapter 4 Introduction to Data Mining by Minqi Zhou ...
Data Preprocessing - School of Computing
... given concept may have different names in different databases, causing inconsistencies and redundancies. For example, the attribute for customer identification may be referred to as customer id in one data store and cust id in another. Naming inconsistencies may also occur for attribute values. For ...
... given concept may have different names in different databases, causing inconsistencies and redundancies. For example, the attribute for customer identification may be referred to as customer id in one data store and cust id in another. Naming inconsistencies may also occur for attribute values. For ...
Mining Sequential Patterns - VTT Virtual project pages
... events the switch-alarm pair of the telecommunications network. ...
... events the switch-alarm pair of the telecommunications network. ...
PPT
... Data Mining Classification: Basic Concepts, Decision Trees, and Model Evaluation Lecture Notes for Chapter 4 Introduction to Data Mining by Minqi Zhou ...
... Data Mining Classification: Basic Concepts, Decision Trees, and Model Evaluation Lecture Notes for Chapter 4 Introduction to Data Mining by Minqi Zhou ...
Cost Sensitive Credit Card Fraud Detection Using
... when applying the under-sampling methodology the estimated probabilities of fraud are overestimated. This may lead to methods that rely on true probabilities to have inconsistencies, which is the case of the Bayes minimum risk classifier [12]. The reason this happens, is because the prior probability ...
... when applying the under-sampling methodology the estimated probabilities of fraud are overestimated. This may lead to methods that rely on true probabilities to have inconsistencies, which is the case of the Bayes minimum risk classifier [12]. The reason this happens, is because the prior probability ...
lecture 1.pptx
... Data Mining, Security & Fraud Detection (cont) • Data mining and security was in the headlines with US Government efforts on using data mining for terrorism detection, as part of now closed Total Information Awareness Program. However, the problem of terrorism is unlikely to go away soon, and US go ...
... Data Mining, Security & Fraud Detection (cont) • Data mining and security was in the headlines with US Government efforts on using data mining for terrorism detection, as part of now closed Total Information Awareness Program. However, the problem of terrorism is unlikely to go away soon, and US go ...
Data Mining with Weka - Department of Computer Science
... Lesson 1.2: Exploring the Experimenter Use the Experimenter for … determining mean and standard deviation performance of a classification algorithm on a dataset … or several algorithms on several datasets Is one classifier better than another on a particular dataset? … and is the difference sta ...
... Lesson 1.2: Exploring the Experimenter Use the Experimenter for … determining mean and standard deviation performance of a classification algorithm on a dataset … or several algorithms on several datasets Is one classifier better than another on a particular dataset? … and is the difference sta ...
Yuchen_Zhao_Mim2016
... relationships can be discovered by big data mining techniques. Despite all those uncertainties, the concept of big data analysis and data mining approaches still attracts public awareness, and there have been tons of attempts of utilizing these methods for value creation in different fields and indu ...
... relationships can be discovered by big data mining techniques. Despite all those uncertainties, the concept of big data analysis and data mining approaches still attracts public awareness, and there have been tons of attempts of utilizing these methods for value creation in different fields and indu ...
ATLaS: A Native Extension of SQL for Data Mining
... used in Datalog [2], and a stream-oriented computation will 4 Table Functions and Recursive UDAs be discussed in the next section. Example 5 illustrates the typical structure of an ATLaS Recursive queries can be supported in ATLaS without program. The declaration of the table dgraph(start, end) is a ...
... used in Datalog [2], and a stream-oriented computation will 4 Table Functions and Recursive UDAs be discussed in the next section. Example 5 illustrates the typical structure of an ATLaS Recursive queries can be supported in ATLaS without program. The declaration of the table dgraph(start, end) is a ...
Pre-Triage Decision Support Improvement in Maternity Care by
... in CMIN. The IDSS will be able to be executed in real time and will include business intelligence components (eg. indicators of Voluntary interruption of pregnancy, triage indicators) and Data Mining. This system is implemented since 2010 and along four years of existence, the number of GO patients ...
... in CMIN. The IDSS will be able to be executed in real time and will include business intelligence components (eg. indicators of Voluntary interruption of pregnancy, triage indicators) and Data Mining. This system is implemented since 2010 and along four years of existence, the number of GO patients ...
The CRISP-DM Process Model
... represents an idealised sequence of events. In practice, many of the tasks can be performed in a different order and it will often be necessary to repeatedly backtrack to previous tasks and repeat certain actions. Our process model does not attempt to capture all of these possible routes through the ...
... represents an idealised sequence of events. In practice, many of the tasks can be performed in a different order and it will often be necessary to repeatedly backtrack to previous tasks and repeat certain actions. Our process model does not attempt to capture all of these possible routes through the ...
application of big data in education data mining
... Researchers have also used the big data techniques in predicting the risk of attrition associated with students. In educational institutions where the students are likely to drop out of courses, the student's activities are monitored and the student's engagement score is predicted. The predicted sco ...
... Researchers have also used the big data techniques in predicting the risk of attrition associated with students. In educational institutions where the students are likely to drop out of courses, the student's activities are monitored and the student's engagement score is predicted. The predicted sco ...
CG33504508
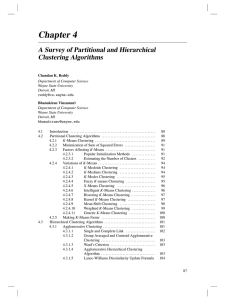
... The goal of clustering is to group the data points or objects that are close or similar to each other and identify such grouping in an unsupervised manner, unsupervised is in the sense that no information is provided to the algorithm about which data point belongs to which cluster. In other words da ...
... The goal of clustering is to group the data points or objects that are close or similar to each other and identify such grouping in an unsupervised manner, unsupervised is in the sense that no information is provided to the algorithm about which data point belongs to which cluster. In other words da ...
Nonlinear dimensionality reduction

High-dimensional data, meaning data that requires more than two or three dimensions to represent, can be difficult to interpret. One approach to simplification is to assume that the data of interest lie on an embedded non-linear manifold within the higher-dimensional space. If the manifold is of low enough dimension, the data can be visualised in the low-dimensional space.Below is a summary of some of the important algorithms from the history of manifold learning and nonlinear dimensionality reduction (NLDR). Many of these non-linear dimensionality reduction methods are related to the linear methods listed below. Non-linear methods can be broadly classified into two groups: those that provide a mapping (either from the high-dimensional space to the low-dimensional embedding or vice versa), and those that just give a visualisation. In the context of machine learning, mapping methods may be viewed as a preliminary feature extraction step, after which pattern recognition algorithms are applied. Typically those that just give a visualisation are based on proximity data – that is, distance measurements.