bigdatainhealthcare
... fairly rapid pace with tools like SparkSQL and other query tools that leverage conventional SQL for querying. In short, big data is cheap but more difficult to use. Relational databases are expensive but very usable. ...
... fairly rapid pace with tools like SparkSQL and other query tools that leverage conventional SQL for querying. In short, big data is cheap but more difficult to use. Relational databases are expensive but very usable. ...
Kernel-Based Manifold Learning for Statistical Analysis of Diffusion
... kFDA to obtain a voxel-wise p-value map. We note that the projections found by kPCA and kFDA lie along directions in the linear RKHS and hence linear tests for statistical inference can be reliably applied to these projections in order to identify separation between groups. Regions with low p-values ...
... kFDA to obtain a voxel-wise p-value map. We note that the projections found by kPCA and kFDA lie along directions in the linear RKHS and hence linear tests for statistical inference can be reliably applied to these projections in order to identify separation between groups. Regions with low p-values ...
Compile-time meta
... •The resulting index & data: 1TB. •One simple entity search: 16s. •The complete process of property-based data access may take up to hours as multiple queries, entity and property retrievals are being performed. •Computing the quality, principal components, latent types and information gain for all ...
... •The resulting index & data: 1TB. •One simple entity search: 16s. •The complete process of property-based data access may take up to hours as multiple queries, entity and property retrievals are being performed. •Computing the quality, principal components, latent types and information gain for all ...
Moving to a fourth generation: SPC that lets you
... 4th Generation SPC You won’t find a definition for fourth-generation SPC on the NIST website. If you Google long enough, it will show up somewhere. There is nothing official about this; the name is just a way to think about and discuss how SPC might make the next leap forward. Let’s start by descri ...
... 4th Generation SPC You won’t find a definition for fourth-generation SPC on the NIST website. If you Google long enough, it will show up somewhere. There is nothing official about this; the name is just a way to think about and discuss how SPC might make the next leap forward. Let’s start by descri ...
Chapter 5 Business Intelligence: Data Warehousing, Data
... © 2005 Prentice Hall, Decision Support Systems and Intelligent Systems, 7th Edition, Turban, Aronson, and Liang ...
... © 2005 Prentice Hall, Decision Support Systems and Intelligent Systems, 7th Edition, Turban, Aronson, and Liang ...
CASME: A CASE Tool for Spatial Data Marts Design and Generation
... implicit knowledge, spatial relationships, which are not explicitly stored into geographical databases [7]. In fact, the collected data can exceed human's capacity to analyze and extract interesting knowledge from large spatial databases. Many methods of knowledge discovery in geographic database ha ...
... implicit knowledge, spatial relationships, which are not explicitly stored into geographical databases [7]. In fact, the collected data can exceed human's capacity to analyze and extract interesting knowledge from large spatial databases. Many methods of knowledge discovery in geographic database ha ...
Symptoms Autonomic Framework for Market Prediction, Analysis
... want to think about how this impacts standards around XaaS in general, e.g. is there a need for a generalized standard that would make SIS's job easier? At present is needs five different interfaces to composed his service. More details about each role and their interactions in the following sectio ...
... want to think about how this impacts standards around XaaS in general, e.g. is there a need for a generalized standard that would make SIS's job easier? At present is needs five different interfaces to composed his service. More details about each role and their interactions in the following sectio ...
Theory Matters for Financial Advice! (PDF, 763 KB) (PDF, 745 KB)
... characteristics (e.g. means and variances of returns) and it suggests a way to model the risk tolerance of a client (e.g. by variance aversion). Without a decision theory the financial advisor would have to explain to the client all characteristics of the markets for all possible portfolios he can r ...
... characteristics (e.g. means and variances of returns) and it suggests a way to model the risk tolerance of a client (e.g. by variance aversion). Without a decision theory the financial advisor would have to explain to the client all characteristics of the markets for all possible portfolios he can r ...
A Robust Seedless Algorithm for Correlation Clustering
... In subspace clustering, the clusters are formed in the subspaces rather than the fulldimensional space [4,6]. Finding arbitrary-oriented subspace cluster (Fig. 1(c)) involves exponential search space. To efficiently address the problem, most correlation based approaches use PCA to avoid searching un ...
... In subspace clustering, the clusters are formed in the subspaces rather than the fulldimensional space [4,6]. Finding arbitrary-oriented subspace cluster (Fig. 1(c)) involves exponential search space. To efficiently address the problem, most correlation based approaches use PCA to avoid searching un ...
Davies, Erin Lane: A Critical Review of Computational Methods Used to Manage Microarray Data Sets
... vectors in n-dimensional expression space (5). Alternatively, correlation coefficients can be used as similarity measures (4,5). The dot product is calculated for each pair of gene expression vectors in the data set; thus correlation coefficients range in value from –1 to 1. For example, Eisen et. a ...
... vectors in n-dimensional expression space (5). Alternatively, correlation coefficients can be used as similarity measures (4,5). The dot product is calculated for each pair of gene expression vectors in the data set; thus correlation coefficients range in value from –1 to 1. For example, Eisen et. a ...
Operational Scenarios Using the Microsoft Data
... diagram: These technologies aren’t layered in the sense that each one depends on the others shown below it. It’s more accurate to think of each column as a group of technologies for working with data in a particular way. Also, realize that the lines between the columns are permeable—these technologi ...
... diagram: These technologies aren’t layered in the sense that each one depends on the others shown below it. It’s more accurate to think of each column as a group of technologies for working with data in a particular way. Also, realize that the lines between the columns are permeable—these technologi ...
Data Warehouse of Spatial Information
... taken by satellites or plane, and processed by GIS software, such as ARC/INFO, ERDAS etc. The application-specific data is obtained through the application department or data center of respectively department. The data acquiring tools are become more and more intelligence, the framework data set acq ...
... taken by satellites or plane, and processed by GIS software, such as ARC/INFO, ERDAS etc. The application-specific data is obtained through the application department or data center of respectively department. The data acquiring tools are become more and more intelligence, the framework data set acq ...
Database Systems: Design, Implementation, and
... • Links tables based on equality condition that compares specified columns of tables • Does not eliminate duplicate columns • Join criteria must be explicitly defined • Theta JOIN • EquiJOIN that compares specified columns of each table using operator other than equality one • Outer JOIN ...
... • Links tables based on equality condition that compares specified columns of tables • Does not eliminate duplicate columns • Join criteria must be explicitly defined • Theta JOIN • EquiJOIN that compares specified columns of each table using operator other than equality one • Outer JOIN ...
Mathematical Programming for Data Mining: Formulations and
... placed by the KDD system on the discovered patterns or models. The term knowledge in KDD is user-oriented, domain-specific, and determined by the interestingness measure; it is not a general definition of knowledge and should not be taken as an attempt at a general (e.g., philosophical) definition. ...
... placed by the KDD system on the discovered patterns or models. The term knowledge in KDD is user-oriented, domain-specific, and determined by the interestingness measure; it is not a general definition of knowledge and should not be taken as an attempt at a general (e.g., philosophical) definition. ...
Online transaction processing, or OLTP, refers to a class of systems
... IMPLEMENTATION OF OLTP:On-Line Transaction Processing is a processing that supports the daily business operations. Also know as operational processing and OLTP. An OLTP is a database which must typically allow the realtime processing of SQL transactions to support traditional retail processes, e-co ...
... IMPLEMENTATION OF OLTP:On-Line Transaction Processing is a processing that supports the daily business operations. Also know as operational processing and OLTP. An OLTP is a database which must typically allow the realtime processing of SQL transactions to support traditional retail processes, e-co ...
Chapter_5
... Principles and Learning Objectives • Data management and modeling are key aspects of organizing data and information – Define general data management concepts and terms, highlighting the advantages of the database approach to data management – Describe logical and physical database design considera ...
... Principles and Learning Objectives • Data management and modeling are key aspects of organizing data and information – Define general data management concepts and terms, highlighting the advantages of the database approach to data management – Describe logical and physical database design considera ...
Construction of SARIMAX
... interval of a 4 weeks period. The outdoor temperature is possibly used as an external variable (X term) in the model, if the data correlate with each other. The consumption and the temperature are plotted with SAS software [15] in Figure 1. As you can see, there is evident linear trend and seasonal ...
... interval of a 4 weeks period. The outdoor temperature is possibly used as an external variable (X term) in the model, if the data correlate with each other. The consumption and the temperature are plotted with SAS software [15] in Figure 1. As you can see, there is evident linear trend and seasonal ...
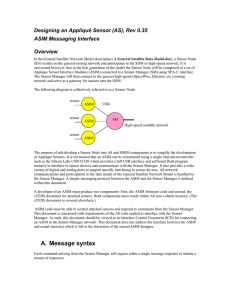
A. Message syntax
... of Appliqué Sensors. It is envisioned that an ASIM can be constructed using a single chip microcontroller such as the Silicon Labs C8051F320 which provides a full USB interface and sufficient flash program memory to interface to sensor devices and communicate with the Sensor Manager. It also provide ...
... of Appliqué Sensors. It is envisioned that an ASIM can be constructed using a single chip microcontroller such as the Silicon Labs C8051F320 which provides a full USB interface and sufficient flash program memory to interface to sensor devices and communicate with the Sensor Manager. It also provide ...
Streaming String Transducers - the Department of Computer and
... Checking Equivalence of SSTs S and S’ (4) Propagate classification of variables consistently. Add a counter to check assumption about lengths When S adds symbols to L vars & to left in M vars, increment; When S’ adds symbols to L vars & to left of M vars, decrement ...
... Checking Equivalence of SSTs S and S’ (4) Propagate classification of variables consistently. Add a counter to check assumption about lengths When S adds symbols to L vars & to left in M vars, increment; When S’ adds symbols to L vars & to left of M vars, decrement ...
các vấn đề bảo mật nổi bật trong các hệ thống quản trị dữ liệu và
... emerging DMSs and applications. Interestingly, this problem does not happen to mandatory security models. 2.2 Mandatory security Mandatory security deals with granting access to the data on the basis of users’ clearance level and the sensitivity level of the data. Users and data are considered as su ...
... emerging DMSs and applications. Interestingly, this problem does not happen to mandatory security models. 2.2 Mandatory security Mandatory security deals with granting access to the data on the basis of users’ clearance level and the sensitivity level of the data. Users and data are considered as su ...
Informatica Data Quality - 10.1.1 - Using Random Sampling Option
... random rows in the Customers table for profiling, a sample query is Select * from Customers SAMPLE (X) statement, where X is the approximate percentage of random rows. The query returns an approximate X percentage of rows on which the profile runs. For example, assume that the estimated source row c ...
... random rows in the Customers table for profiling, a sample query is Select * from Customers SAMPLE (X) statement, where X is the approximate percentage of random rows. The query returns an approximate X percentage of rows on which the profile runs. For example, assume that the estimated source row c ...
Quick Recovery For MS Backup
... another folder, this deleted file may get overwritten! A folder may be somewhere and files under it may be somewhere else, they are linked by the FAT/MFT. Viruses may infect a computer today, but they affect harm on the system many days later or even years later. They require this time for spreading ...
... another folder, this deleted file may get overwritten! A folder may be somewhere and files under it may be somewhere else, they are linked by the FAT/MFT. Viruses may infect a computer today, but they affect harm on the system many days later or even years later. They require this time for spreading ...
Best Practices ® Data Protection in the Cloud
... that are not authorized to access such data. This is by far the largest category of threats and is usually the first that comes to mind. These threats can be aimed directly at the tables in the database or can be made more indirectly, such as by looking at the log files or at the table space files o ...
... that are not authorized to access such data. This is by far the largest category of threats and is usually the first that comes to mind. These threats can be aimed directly at the tables in the database or can be made more indirectly, such as by looking at the log files or at the table space files o ...
Detecting sterile neutrinos with KATRIN
... • Could there be more than three neutrino species? • The suggestion is: sterile neutrinos. They mix with the active species via a larger mixing matrix, but otherwise do not interact in the Standard Model. • The LSND experiment observed an excess appearance of electron antineutrinos in muon antineutr ...
... • Could there be more than three neutrino species? • The suggestion is: sterile neutrinos. They mix with the active species via a larger mixing matrix, but otherwise do not interact in the Standard Model. • The LSND experiment observed an excess appearance of electron antineutrinos in muon antineutr ...
Data analysis

Analysis of data is a process of inspecting, cleaning, transforming, and modeling data with the goal of discovering useful information, suggesting conclusions, and supporting decision-making. Data analysis has multiple facets and approaches, encompassing diverse techniques under a variety of names, in different business, science, and social science domains.Data mining is a particular data analysis technique that focuses on modeling and knowledge discovery for predictive rather than purely descriptive purposes. Business intelligence covers data analysis that relies heavily on aggregation, focusing on business information. In statistical applications, some people divide data analysis into descriptive statistics, exploratory data analysis (EDA), and confirmatory data analysis (CDA). EDA focuses on discovering new features in the data and CDA on confirming or falsifying existing hypotheses. Predictive analytics focuses on application of statistical models for predictive forecasting or classification, while text analytics applies statistical, linguistic, and structural techniques to extract and classify information from textual sources, a species of unstructured data. All are varieties of data analysis.Data integration is a precursor to data analysis, and data analysis is closely linked to data visualization and data dissemination. The term data analysis is sometimes used as a synonym for data modeling.