Availability Confidentiality Integrity
... denies service to those who are not • One of the problems is that additional security is overhead that reduces amount of work that can be done – Although not as extreme as the availability issues of attacks Copyright © 2013-2016 – Curt Hill ...
... denies service to those who are not • One of the problems is that additional security is overhead that reduces amount of work that can be done – Although not as extreme as the availability issues of attacks Copyright © 2013-2016 – Curt Hill ...
eHealthcare and Electronic Health Records
... used again (e.g. once the patient has passed away) such a patient identifier can be used as the primary key in an IT system. Note that most regulations somehow limit or even prohibit the use of personal identifiers with global (not restricted to a single contract) applications and/or longterm storag ...
... used again (e.g. once the patient has passed away) such a patient identifier can be used as the primary key in an IT system. Note that most regulations somehow limit or even prohibit the use of personal identifiers with global (not restricted to a single contract) applications and/or longterm storag ...
CyberShield Command Core
... • Cyber Intelligence - acquisition and extraction of cyberdefense intelligence, combining collection systems, data management and alert generation mechanisms for closing the intelligence-C2 operational loop. This module also includes receipt of intelligence from various sources (including open sour ...
... • Cyber Intelligence - acquisition and extraction of cyberdefense intelligence, combining collection systems, data management and alert generation mechanisms for closing the intelligence-C2 operational loop. This module also includes receipt of intelligence from various sources (including open sour ...
VLSI Implementation of Flexible Architecture for Decision Tree
... developed by Quinlan Ross(Quinlan, 1986 and 1987)[1]. Hunt’s algorithm is the base for this algorithm. It chooses the splitting attribute using the concept of information gain measure. It can only accept categorical attributes in the process of making a tree structure. IDE3 cannot be used in an atmo ...
... developed by Quinlan Ross(Quinlan, 1986 and 1987)[1]. Hunt’s algorithm is the base for this algorithm. It chooses the splitting attribute using the concept of information gain measure. It can only accept categorical attributes in the process of making a tree structure. IDE3 cannot be used in an atmo ...
Learning Relational Probability Trees
... and everything one link away, but the RPT algorithm can reason with subgraphs of arbitrary complexity. The RPT algorithm constructs a probability estimation tree to predict the target class label given (1) the attributes of the target objects, (2) the attributes of other objects and links in the rel ...
... and everything one link away, but the RPT algorithm can reason with subgraphs of arbitrary complexity. The RPT algorithm constructs a probability estimation tree to predict the target class label given (1) the attributes of the target objects, (2) the attributes of other objects and links in the rel ...
Analysis Services
... No processing dependencies (one table can be processed without processing related ...
... No processing dependencies (one table can be processed without processing related ...
Semantic Web Applications in Bioinformatics
... • shared definitions of knowledge domains, i.e. ontologies, • association of concepts to existing data, • metadata information describing information sources and contents, • search tools able to make the best use of this additional information. ...
... • shared definitions of knowledge domains, i.e. ontologies, • association of concepts to existing data, • metadata information describing information sources and contents, • search tools able to make the best use of this additional information. ...
Introducing Enterprise NoSQL
... Live in JavaScript. Run JavaScript near the data for unparalleled power and efficiency with a high performance JavaScript runtime inside MarkLogic using Google’s V8. ...
... Live in JavaScript. Run JavaScript near the data for unparalleled power and efficiency with a high performance JavaScript runtime inside MarkLogic using Google’s V8. ...
XML and Mobile Agent Technology Enabling the Virtual Enterprise
... The IDOAgent is the agent that searches the database to get the XML elements of one or more document according to document name(s). The IDOAgent is dispatch by the IDOMAgent described below. It dispatches itself back to the application server with the found data and disposes itself after its back to ...
... The IDOAgent is the agent that searches the database to get the XML elements of one or more document according to document name(s). The IDOAgent is dispatch by the IDOMAgent described below. It dispatches itself back to the application server with the found data and disposes itself after its back to ...
Web Data Mining Techniques and Implementation for Handling Big
... concerns related to data security. There is loads of personal information available on the internet and web data mining had helped to keep the idea of the need to secure that information at the forefront. As data is a collection of facts from the grids of web servers along the web usually of unorgan ...
... concerns related to data security. There is loads of personal information available on the internet and web data mining had helped to keep the idea of the need to secure that information at the forefront. As data is a collection of facts from the grids of web servers along the web usually of unorgan ...
bigdatainhealthcare
... Big Data and the Internet of Things For healthcare, any device that generates data about a person’s health and sends that data into the cloud will be part of this IoT. Wearables are perhaps the most familiar example of such a device. Many people now can wear a fitness device that tracks their heartr ...
... Big Data and the Internet of Things For healthcare, any device that generates data about a person’s health and sends that data into the cloud will be part of this IoT. Wearables are perhaps the most familiar example of such a device. Many people now can wear a fitness device that tracks their heartr ...
[handout
... Present attacks damage machines and disrupt network access Attacks continue to grow in numbers Information sharing can mitigate attack risk It is a constant challenge for research to keep pace with attack vectors ...
... Present attacks damage machines and disrupt network access Attacks continue to grow in numbers Information sharing can mitigate attack risk It is a constant challenge for research to keep pace with attack vectors ...
Read the report - The Beckman Report on Database Research
... The new era of Big Data has drawn many communities into the “data management game.” There has been a groundswell of efforts in these communities to develop custom data management solutions, such as Hadoop and NoSQL. Many of these early solutions were not based on database management system (DBMS) pr ...
... The new era of Big Data has drawn many communities into the “data management game.” There has been a groundswell of efforts in these communities to develop custom data management solutions, such as Hadoop and NoSQL. Many of these early solutions were not based on database management system (DBMS) pr ...
Chapter 5 Business Intelligence: Data Warehousing, Data
... data that employees use to unlock valuable secrets to enable the organization to compete successfully. Some organizations do this extremely well, but others are quite ineffective. To use analytic tools to improve organization decision making, a foundation data architecture & enterprise architecture ...
... data that employees use to unlock valuable secrets to enable the organization to compete successfully. Some organizations do this extremely well, but others are quite ineffective. To use analytic tools to improve organization decision making, a foundation data architecture & enterprise architecture ...
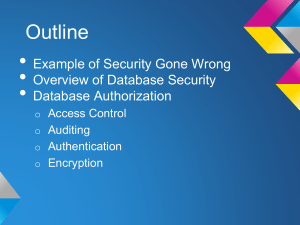
MIS409_DB_Security_Auth_Encrypt
... • Access policy determined by the system. not the owner. • Used in commercial applications and also ...
... • Access policy determined by the system. not the owner. • Used in commercial applications and also ...
FMIS - WordPress.com
... (3) Improve interpersonal communication. DSS can improve communication and collaboration among decision makers. In appropriate circumstances, communications- driven and group DSS have had this impact. Model-driven DSS provides a means for sharing facts and assumptions. Data-driven DSS make "one ver ...
... (3) Improve interpersonal communication. DSS can improve communication and collaboration among decision makers. In appropriate circumstances, communications- driven and group DSS have had this impact. Model-driven DSS provides a means for sharing facts and assumptions. Data-driven DSS make "one ver ...
History and Development of CRM
... With customer data coming from all business areas, a 360 degree view of the customer is possible. Today, CRM efforts include gathering information from all customer touch points, including call centers and Internet systems. ...
... With customer data coming from all business areas, a 360 degree view of the customer is possible. Today, CRM efforts include gathering information from all customer touch points, including call centers and Internet systems. ...
H7385-ITRON Customer Profile
... Lukes. “I found it much easier to work with my LUNs, my RAID groups, and my pools. The dashboards provided an informative view into the system as well. Unisphere is a great improvement, yet keeps the Navisphere fundamentals that storage administrators are used to seeing. Unisphere also enables us to ...
... Lukes. “I found it much easier to work with my LUNs, my RAID groups, and my pools. The dashboards provided an informative view into the system as well. Unisphere is a great improvement, yet keeps the Navisphere fundamentals that storage administrators are used to seeing. Unisphere also enables us to ...
Digital PRI Voice Service - TouchTone Communications
... DIDs and Number Portability Transfer your phone numbers from another carrier to TouchTone, or choose local/enhanced DID numbers in over 26 countries. CUSTOMER PROVIDED ROUTER/SWITCH ...
... DIDs and Number Portability Transfer your phone numbers from another carrier to TouchTone, or choose local/enhanced DID numbers in over 26 countries. CUSTOMER PROVIDED ROUTER/SWITCH ...
PDF 181 KB - Ingenico Group
... magstripe cards – by adding the tip after the initial card authorization. This is becoming increasingly important for merchants who have not yet switched to Pay-at-the-Table solutions to accept EMV chip cards, where the customer would enter the tip directly into the terminal. Additionally, by provid ...
... magstripe cards – by adding the tip after the initial card authorization. This is becoming increasingly important for merchants who have not yet switched to Pay-at-the-Table solutions to accept EMV chip cards, where the customer would enter the tip directly into the terminal. Additionally, by provid ...
Data Exfiltration and DNS
... Automating Threat Response through Integration While detection and blocking of data exfiltration attempts is critical, it is also important to ensure fast remediation of infected devices. This can be achieved by tighter integration between detection technologies and endpoint remediation solutions. I ...
... Automating Threat Response through Integration While detection and blocking of data exfiltration attempts is critical, it is also important to ensure fast remediation of infected devices. This can be achieved by tighter integration between detection technologies and endpoint remediation solutions. I ...
Using Markov Chain Monte Carlo to Play Trivia
... probabilistic and recursive rules can be used for implementation of the required features of Trivia Masster. We use a rules set as depicted above, implementing a PageRank-style cleaning process, and change the query event according to our goal. Specifically, for query answering, the query event is s ...
... probabilistic and recursive rules can be used for implementation of the required features of Trivia Masster. We use a rules set as depicted above, implementing a PageRank-style cleaning process, and change the query event according to our goal. Specifically, for query answering, the query event is s ...
ToR-MRM4Syria-RO-MRM-Database-manager-TA
... The Annex to the 2011 Secretary General’s Report on Children and Armed Conflict listed the Free Syria Army (FSA) and a number of Government forces in Syria as persistent violators of grave violations against children in the context of the ongoing conflict in Syria. With the activation of the MRM for ...
... The Annex to the 2011 Secretary General’s Report on Children and Armed Conflict listed the Free Syria Army (FSA) and a number of Government forces in Syria as persistent violators of grave violations against children in the context of the ongoing conflict in Syria. With the activation of the MRM for ...
Android UI Develop and Design - Seneca ICT
... • Two diagrams (Figures 4-4, 4-5 in Learning Android) • http://libcat.senecacollege.ca/vwebv/holdingsInfo?searchId=38206 &recCount=50&recPointer=1&bibId=315195 • Demo (the Contacts Provider) • a built-in Android content provider ...
... • Two diagrams (Figures 4-4, 4-5 in Learning Android) • http://libcat.senecacollege.ca/vwebv/holdingsInfo?searchId=38206 &recCount=50&recPointer=1&bibId=315195 • Demo (the Contacts Provider) • a built-in Android content provider ...