CS206 --- Electronic Commerce - The Stanford University InfoLab
... We thought Datalog was going to take over for SQL; it didn’t. But it is natural and clean, and the study turned out to be worth the effort ...
... We thought Datalog was going to take over for SQL; it didn’t. But it is natural and clean, and the study turned out to be worth the effort ...
Physical data organization Disks, blocks, tuples, schemas
... In order to select a physical plan we need to know: • The physical algorithms available to implement the relational algebra operators e.g., scan a relation to implement a selection ...
... In order to select a physical plan we need to know: • The physical algorithms available to implement the relational algebra operators e.g., scan a relation to implement a selection ...
Goal of data integration
... customers can call about any service or product they obtain from the company.When a representative is on the phone with a customer, it´s important to see the entire set of services the customer is getting from FullServe (internet service, credit card or products purchased). Furthermore, it is useful ...
... customers can call about any service or product they obtain from the company.When a representative is on the phone with a customer, it´s important to see the entire set of services the customer is getting from FullServe (internet service, credit card or products purchased). Furthermore, it is useful ...
Original Motivation for the Project New
... • Many of the same ones need to track the lineage (provenance) of their data ...
... • Many of the same ones need to track the lineage (provenance) of their data ...
Satellite for Crops - Netherlands and you
... To strengthen the agricultural sector and fortify food security in Bangladesh, BRAC (Bangladesh Rural Advancement Committee) and the Center for Environmental and Geographical Information Services (CEGIS) use remote sensing technology. Satellites provide unbiased and consistently collected data of la ...
... To strengthen the agricultural sector and fortify food security in Bangladesh, BRAC (Bangladesh Rural Advancement Committee) and the Center for Environmental and Geographical Information Services (CEGIS) use remote sensing technology. Satellites provide unbiased and consistently collected data of la ...
How Business Intelligence Software Works and a Brief Review of
... A strategy to ensure the right information is available to the right decision makers at the right time Working definition- products that are designed to extract and present data from a data warehouse (ideally) ...
... A strategy to ensure the right information is available to the right decision makers at the right time Working definition- products that are designed to extract and present data from a data warehouse (ideally) ...
CHAPTER 25 - Distributed Databases and Client*Server Architectures
... Ability to keep track of the data distribution, fragmentation, and replication by expanding the DDBMS catalog. Ability to access remote sites and transmit queries and data among the various sites via a communication network. Executed with the proper management of the security of the data and the aut ...
... Ability to keep track of the data distribution, fragmentation, and replication by expanding the DDBMS catalog. Ability to access remote sites and transmit queries and data among the various sites via a communication network. Executed with the proper management of the security of the data and the aut ...
chapter07
... • Identify sources for and actual questions that might be used • Identify sources for and actual sample frames that might be used ...
... • Identify sources for and actual questions that might be used • Identify sources for and actual sample frames that might be used ...
MSKCC Web Core - Memorial Sloan Kettering Cancer Center
... The Web Core of Memorial Sloan-Kettering Cancer Center is an institutional resource which assists investigators to create secure electronic surveys for use in research. The Core includes programmers to create study-specific surveys, and maintains servers for secure administration and storage of data ...
... The Web Core of Memorial Sloan-Kettering Cancer Center is an institutional resource which assists investigators to create secure electronic surveys for use in research. The Core includes programmers to create study-specific surveys, and maintains servers for secure administration and storage of data ...
Slides
... analysing, and organizing any information that serves to identify, manage, locate, and interpret the holdings of archival institutions and explain the contexts and records systems from which those holdings were selected’ Working Group on Standards for Archival Description (WGSAD) (1989) ...
... analysing, and organizing any information that serves to identify, manage, locate, and interpret the holdings of archival institutions and explain the contexts and records systems from which those holdings were selected’ Working Group on Standards for Archival Description (WGSAD) (1989) ...
Data Protection Policy - Bohunt School Wokingham
... accordance with the Data Protection Act 1998, and other related legislation. It will apply to information regardless of the way it is collected, used, recorded, stored and destroyed, and irrespective of whether it is held in paperfiles or electronically. ...
... accordance with the Data Protection Act 1998, and other related legislation. It will apply to information regardless of the way it is collected, used, recorded, stored and destroyed, and irrespective of whether it is held in paperfiles or electronically. ...
IIDPS: An Internal Intrusion Detection and
... attacks. To deal with these new problems of networks, data mining based IIDS are opening new research avenues. Data mining provides a wide range of techniques to classify these attacks. The paper provides a study on the various data mining based intrusion detection techniques. In this paper, we prop ...
... attacks. To deal with these new problems of networks, data mining based IIDS are opening new research avenues. Data mining provides a wide range of techniques to classify these attacks. The paper provides a study on the various data mining based intrusion detection techniques. In this paper, we prop ...
Chapter 8 1 DATA FARMING: CONCEPTS AND METHODS
... from routinely gathered data, to process improvement projects, and to data required for archival purposes. In some cases, the set of considered features might be large (a wide data set) and sufficient for extraction of knowledge. In other cases the data set might be narrow and insufficient to extrac ...
... from routinely gathered data, to process improvement projects, and to data required for archival purposes. In some cases, the set of considered features might be large (a wide data set) and sufficient for extraction of knowledge. In other cases the data set might be narrow and insufficient to extrac ...
Database Models: Flat Files and the Relational Database
... • Minimize redundancy • Minimize wasted storage • Facilitate updates, appending new data to existing systems • Facilitate queries, makes asking questions of the database easier • Keeps tables small for portability and improved data processing ...
... • Minimize redundancy • Minimize wasted storage • Facilitate updates, appending new data to existing systems • Facilitate queries, makes asking questions of the database easier • Keeps tables small for portability and improved data processing ...
講座貢三元教授美國普林斯頓大學電機工程學系時間2015/12/24
... space) or in the dual domain (in the induced kernel space). Even though the two formulations are mathematically equivalent, they require very different computational costs. This talk will address how to exploits the such a dual–cost strategy to gain computational saving by orders of magnitude, both ...
... space) or in the dual domain (in the induced kernel space). Even though the two formulations are mathematically equivalent, they require very different computational costs. This talk will address how to exploits the such a dual–cost strategy to gain computational saving by orders of magnitude, both ...
How to use R, Python, and machine learning with
... SQL Server Machine Learning Services SQL Server Developer Tutorials ...
... SQL Server Machine Learning Services SQL Server Developer Tutorials ...
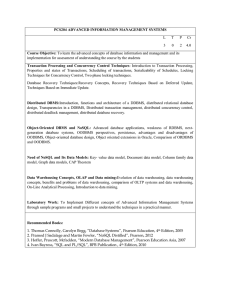
PCS204 ADVANCED INFORMATION MANAGEMENT SYSTEMS Course Objective: L
... Need of NoSQL and Its Data Models: Key- value data model, Document data model, Column family data model, Graph data models, CAP Theorem ...
... Need of NoSQL and Its Data Models: Key- value data model, Document data model, Column family data model, Graph data models, CAP Theorem ...
Position Title: Business Analyst
... Minimum three (3) years of experience in data analysis Minimum of five (5) years preferably in a wholesale/retail environment working in inventory planning, category management and/or supply chain Proficient in MS Office applications Excel, Access, Word & PowerPoint Advanced technical skills with da ...
... Minimum three (3) years of experience in data analysis Minimum of five (5) years preferably in a wholesale/retail environment working in inventory planning, category management and/or supply chain Proficient in MS Office applications Excel, Access, Word & PowerPoint Advanced technical skills with da ...
Case study
... For example road works may span several junctions and as such the relevant data from the NTCC needs to reflect that section of road. ...
... For example road works may span several junctions and as such the relevant data from the NTCC needs to reflect that section of road. ...
Disclaimer - euphore home page
... Databases on the EUPHORE Web site include such examples as FTIR cross-sections, UV cross-sections, DNPH-MSn carbonyl spectra, experimental protocols and data, chemicals, documents and analysis tools. They are designed to provide and encourage facile access within the scientific community and users o ...
... Databases on the EUPHORE Web site include such examples as FTIR cross-sections, UV cross-sections, DNPH-MSn carbonyl spectra, experimental protocols and data, chemicals, documents and analysis tools. They are designed to provide and encourage facile access within the scientific community and users o ...
World Wide Web Conference
... present original reports of substantive new work and can be up to 10 pages in length. Papers should properly place the work within the field, cite related work, and clearly indicate the innovative aspects of the work and its contribution to the field. In addition to regular papers, we also solicit s ...
... present original reports of substantive new work and can be up to 10 pages in length. Papers should properly place the work within the field, cite related work, and clearly indicate the innovative aspects of the work and its contribution to the field. In addition to regular papers, we also solicit s ...
mca5043 - SMU Assignments
... mining is concerned with finding hidden relationships present in business data to allow businesses to make predictions for future use. It is the process of data-driven extraction of not so obvious but useful information from large databases. Data mining has emerged as a key business intelligence tec ...
... mining is concerned with finding hidden relationships present in business data to allow businesses to make predictions for future use. It is the process of data-driven extraction of not so obvious but useful information from large databases. Data mining has emerged as a key business intelligence tec ...