NP10_Chapter03
... 3 Security Software Basics Security software is designed to protect computers from various forms of destructive software and unauthorized intrusions The terms malicious software and malware refer to any computer program designed to surreptitiously enter a computer, gain unauthorized access to dat ...
... 3 Security Software Basics Security software is designed to protect computers from various forms of destructive software and unauthorized intrusions The terms malicious software and malware refer to any computer program designed to surreptitiously enter a computer, gain unauthorized access to dat ...
EMC Syncplicity - KEMP Technologies
... 1. The origin of this software must not be misrepresented; you must not claim that you wrote the original software. If you use this software in a product, an acknowledgment in the product documentation would be appreciated but is not required. 2. Altered source versions must be plainly marked as suc ...
... 1. The origin of this software must not be misrepresented; you must not claim that you wrote the original software. If you use this software in a product, an acknowledgment in the product documentation would be appreciated but is not required. 2. Altered source versions must be plainly marked as suc ...
Discovering Computers 2008
... Allows you to plan, schedule, track, and analyze the events, resources, and costs of a project ...
... Allows you to plan, schedule, track, and analyze the events, resources, and costs of a project ...
Numerical Methods 2
... • The Jacobian matrix does not become ill-conditioned with small h because all differential equations are multiplied by h (no terms of the form 1/h in the Jacobian) • The integrators can monitor error on both position and velocity (unlike I3, velocities are guaranteed to satisfy ERROR with SI2 ...
... • The Jacobian matrix does not become ill-conditioned with small h because all differential equations are multiplied by h (no terms of the form 1/h in the Jacobian) • The integrators can monitor error on both position and velocity (unlike I3, velocities are guaranteed to satisfy ERROR with SI2 ...
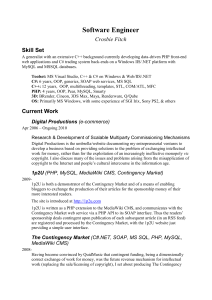
CV_G - Crosbie Fitch
... effecting the exchange of the work for the money of those offering its price – thus making file-sharing free distribution and a promotional benefit, rather than a price competitor. In this indefinitely long auction, designed for unreleased works that are trivially reproducible at zero cost (recordin ...
... effecting the exchange of the work for the money of those offering its price – thus making file-sharing free distribution and a promotional benefit, rather than a price competitor. In this indefinitely long auction, designed for unreleased works that are trivially reproducible at zero cost (recordin ...
Session 34
... • The company may have to show clients the source code to customize the software for the client's needs. ...
... • The company may have to show clients the source code to customize the software for the client's needs. ...