NetDefend Family Overview & Strategy
... NetDefendOS Introduction The hardware of D-Link Firewalls DFL-210/260/800/860/1600/2500 is driven and controlled by NetDefendOS. Designed as a dedicated firewall operating system, NetDefendOS features high throughput performance with high reliability while at the same time implementing the key eleme ...
... NetDefendOS Introduction The hardware of D-Link Firewalls DFL-210/260/800/860/1600/2500 is driven and controlled by NetDefendOS. Designed as a dedicated firewall operating system, NetDefendOS features high throughput performance with high reliability while at the same time implementing the key eleme ...
Thwarting E-mail Spam Laundering - Computer Science
... sources is critical to dampen the dramatically-grown spam volume. At present, proxies such as off-the-shelf SOCKS [Leech et al. 1996] and HTTP proxies play an important role in the spam epidemic. Spammers launder e-mail spam through spam proxies to conceal their real identities and reduce spamming c ...
... sources is critical to dampen the dramatically-grown spam volume. At present, proxies such as off-the-shelf SOCKS [Leech et al. 1996] and HTTP proxies play an important role in the spam epidemic. Spammers launder e-mail spam through spam proxies to conceal their real identities and reduce spamming c ...
About the VM-Series Firewall
... License the VM-Series Firewall When you purchase a VM-Series firewall, you receive a set of authorization codes over email. Typically the email includes authorization code(s) to license the VM-Series model you purchased (VM-100, VM-200, VM300, VM-1000-HV), support entitlement that provides access to ...
... License the VM-Series Firewall When you purchase a VM-Series firewall, you receive a set of authorization codes over email. Typically the email includes authorization code(s) to license the VM-Series model you purchased (VM-100, VM-200, VM300, VM-1000-HV), support entitlement that provides access to ...
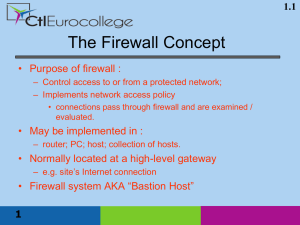
Network Security (Firewall)
... The primary advantage of using a packet-filtering firewall is that it provides some measure of protection for relatively low cost and causes little to no delay in network performance. It primarily operates only at the network layer of the Open Systems Interconnection (OSI) model. ...
... The primary advantage of using a packet-filtering firewall is that it provides some measure of protection for relatively low cost and causes little to no delay in network performance. It primarily operates only at the network layer of the Open Systems Interconnection (OSI) model. ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... As the sub product of electronic mail services, spam became a serious issue in penetrating into any mail system and this types of penetration is mainly used by hackers for stealing confidential data without the knowledge of the user. Generally few hackers use worm which is standalone malware compute ...
... As the sub product of electronic mail services, spam became a serious issue in penetrating into any mail system and this types of penetration is mainly used by hackers for stealing confidential data without the knowledge of the user. Generally few hackers use worm which is standalone malware compute ...
What is a Firewall
... Protocol (CVP), which defines how a firewall forwards packets and data to specialized servers •An administrator can configure and monitor Firewall-1 on the firewall itself or from anywhere on the network •Any unauthorized use can trigger a visible or audible alert to the System Status screen or one ...
... Protocol (CVP), which defines how a firewall forwards packets and data to specialized servers •An administrator can configure and monitor Firewall-1 on the firewall itself or from anywhere on the network •Any unauthorized use can trigger a visible or audible alert to the System Status screen or one ...
Hardware firewall vs Software firewall
... be a separate device. But now these are included, offering us greater protection. When an IPDS detects a malicious activity it sends and signal and reset the connection and block the IP address. It uses signature-based, statistical anomaly-based and stateful protocol analysis. The main drawback I fi ...
... be a separate device. But now these are included, offering us greater protection. When an IPDS detects a malicious activity it sends and signal and reset the connection and block the IP address. It uses signature-based, statistical anomaly-based and stateful protocol analysis. The main drawback I fi ...
Hardware Firewall
... be a separate device. But now these are included, offering us greater protection. When an IPDS detects a malicious activity it sends and signal and reset the connection and block the IP address. It uses signature-based, statistical anomaly-based and stateful protocol analysis. The main drawback I fi ...
... be a separate device. But now these are included, offering us greater protection. When an IPDS detects a malicious activity it sends and signal and reset the connection and block the IP address. It uses signature-based, statistical anomaly-based and stateful protocol analysis. The main drawback I fi ...
in Word DOC
... be a separate device. But now these are included, offering us greater protection. When an IPDS detects a malicious activity it sends and signal and reset the connection and block the IP address. It uses signature-based, statistical anomaly-based and stateful protocol analysis. The main drawback I fi ...
... be a separate device. But now these are included, offering us greater protection. When an IPDS detects a malicious activity it sends and signal and reset the connection and block the IP address. It uses signature-based, statistical anomaly-based and stateful protocol analysis. The main drawback I fi ...
William Stallings, Cryptography and Network Security 5/e
... Only the services that the network administrator considers essential are installed May require additional authentication before a user is allowed access to the proxy services Each proxy is configured to support only a subset of the standard application’s command set Each proxy is configured to allow ...
... Only the services that the network administrator considers essential are installed May require additional authentication before a user is allowed access to the proxy services Each proxy is configured to support only a subset of the standard application’s command set Each proxy is configured to allow ...
CIS484-FIREWALL
... Packet filtering - a simple method, packet filtering entails analyzing small packets or chunks of data through a series of filters. ...
... Packet filtering - a simple method, packet filtering entails analyzing small packets or chunks of data through a series of filters. ...
Firewall - theodoros christophides site
... – Located between Ethernet adapter driver of machine on which they are installed and the TCP/IP stack, where they inspect traffic between the driver and the ...
... – Located between Ethernet adapter driver of machine on which they are installed and the TCP/IP stack, where they inspect traffic between the driver and the ...
Buyer`s Guide - Windows IT Pro
... firewall; identifies unauthorized code (including ActiveX controls and Java applets) that makes it through the firewall, then prevents suspicious content from accessing system resources; prevents execution of malicious Microsoft Word macros; supports console-based centralized management ...
... firewall; identifies unauthorized code (including ActiveX controls and Java applets) that makes it through the firewall, then prevents suspicious content from accessing system resources; prevents execution of malicious Microsoft Word macros; supports console-based centralized management ...
DumpsReview
... NO.15 Which Symantec Enterprise Firewall task must you perform to ensure proper functioning of DNSd for a security gateway facing the Internet? A. Disable public zone files on the security gateway. B. Configure a DNS forwarder to point to a root name server. C. Configure the public recursion record ...
... NO.15 Which Symantec Enterprise Firewall task must you perform to ensure proper functioning of DNSd for a security gateway facing the Internet? A. Disable public zone files on the security gateway. B. Configure a DNS forwarder to point to a root name server. C. Configure the public recursion record ...