MIS 431
... QuantityOnHand + (SELECT QuantitySold FROM DELETED) WHERE ProductCode = (SELECT ProductCode FROM DELETED) ...
... QuantityOnHand + (SELECT QuantitySold FROM DELETED) WHERE ProductCode = (SELECT ProductCode FROM DELETED) ...
Chapter 5
... • Relation - collection of data representing multiple occurrences of an object, event, or agent. • Tuples (rows) - set of data that describe an instance of the entity represented by a relation; like a record in traditional file structure. • Attributes (columns) - items of data that characterize an o ...
... • Relation - collection of data representing multiple occurrences of an object, event, or agent. • Tuples (rows) - set of data that describe an instance of the entity represented by a relation; like a record in traditional file structure. • Attributes (columns) - items of data that characterize an o ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... All organizations public, governmental or private, small or large| depend on computerized information systems for carrying out their daily activity. At the heart of each such information system, there is a database. At a very general level, we can de ne a database as a persistent collection of relat ...
... All organizations public, governmental or private, small or large| depend on computerized information systems for carrying out their daily activity. At the heart of each such information system, there is a database. At a very general level, we can de ne a database as a persistent collection of relat ...
Database
... FIGURE 1-18: Sample data that relates books to authors and books to branches for Henry Books (continued) ...
... FIGURE 1-18: Sample data that relates books to authors and books to branches for Henry Books (continued) ...
Chapter 9 Physical Database Design Methodology
... • Select software based on user’s requirement • Select hardware based on software requirement ...
... • Select software based on user’s requirement • Select hardware based on software requirement ...
Querying Database - San Francisco State University
... Open Database Connectivity (ODBC) • Provide a standard to retrieve data from a database. • It manages one or more "database drivers“ that enables the communication between database and applications. • To access a database, we use ODBC facilities to define a ODBC data source name for the database. ...
... Open Database Connectivity (ODBC) • Provide a standard to retrieve data from a database. • It manages one or more "database drivers“ that enables the communication between database and applications. • To access a database, we use ODBC facilities to define a ODBC data source name for the database. ...
Document
... • Automate tasks that you perform on a regular basis in a database. • Modules. • Automate a group of related procedures. ...
... • Automate tasks that you perform on a regular basis in a database. • Modules. • Automate a group of related procedures. ...
Database System Concepts and Architecture
... called a database state or snapshot or current set of occurrences or instances in the database • When we define a new database we have database state is empty state (schema specified only in DBMS) • The initial state when the database is first populated • Then At any point in time, the database has ...
... called a database state or snapshot or current set of occurrences or instances in the database • When we define a new database we have database state is empty state (schema specified only in DBMS) • The initial state when the database is first populated • Then At any point in time, the database has ...
Physical data organization Disks, blocks, tuples, schemas
... This is the subject of chapters 13 and 14 in the book ...
... This is the subject of chapters 13 and 14 in the book ...
notes
... many machines, so shrink sizes further. Data Cracking to avoid too much sorting for insertions. [24, 21, 22] 8. Query Processing: perform directly on the column data instead of decompose ”eagerly”, trade CPU for I/O throughput. [19, 4] Further experiments have shown that it might be possible to simu ...
... many machines, so shrink sizes further. Data Cracking to avoid too much sorting for insertions. [24, 21, 22] 8. Query Processing: perform directly on the column data instead of decompose ”eagerly”, trade CPU for I/O throughput. [19, 4] Further experiments have shown that it might be possible to simu ...
Java Queries
... You can run multiple queries on the same statement. By default Connection objects are set to auto-commit – all changes are solidified after single statements are run. conn.setAutoCommit(booleanAutoCommit); If set to false (off) the changes will only be solidified when commit called: conn.commit(); U ...
... You can run multiple queries on the same statement. By default Connection objects are set to auto-commit – all changes are solidified after single statements are run. conn.setAutoCommit(booleanAutoCommit); If set to false (off) the changes will only be solidified when commit called: conn.commit(); U ...
DBAdminFund_PPT_2.1
... In programming, a definition of a set of data that specifies the possible range of values of the set, the operations that can be performed on the values, and the way in which the values are stored in memory. Defining the data type allows a computer to manipulate the data appropriately. Data types ar ...
... In programming, a definition of a set of data that specifies the possible range of values of the set, the operations that can be performed on the values, and the way in which the values are stored in memory. Defining the data type allows a computer to manipulate the data appropriately. Data types ar ...
Hands on Demonstration for Testing Security in Web Applications
... form to the attacker 2. Attacker sends an attack in the form data 3. Application forwards attack to the database in a SQL query 4. Database runs query containing attack and sends encrypted results back to application 5. Application decrypts data as normal and sends results to the user ...
... form to the attacker 2. Attacker sends an attack in the form data 3. Application forwards attack to the database in a SQL query 4. Database runs query containing attack and sends encrypted results back to application 5. Application decrypts data as normal and sends results to the user ...
Chapter 1
... Repository–centralized storehouse of metadata Database Management System (DBMS) –software for managing the database Database–storehouse of the data Application Programs–software using the data User Interface–text and graphical displays to users Data/Database Administrators–personnel responsible for ...
... Repository–centralized storehouse of metadata Database Management System (DBMS) –software for managing the database Database–storehouse of the data Application Programs–software using the data User Interface–text and graphical displays to users Data/Database Administrators–personnel responsible for ...
Three Main Components
... ArcIMS, Webmap, and Map Guide •GIS Programing: AML, Avenue, Visual Basic ...
... ArcIMS, Webmap, and Map Guide •GIS Programing: AML, Avenue, Visual Basic ...
View File - UET Taxila
... A data model is a collection of concepts for describing data. A schema is a description of a particular collection of data, using the a given data model. The relational model of data is the most widely used model today. - Main concept: relation, basically a table with rows and columns. - Every relat ...
... A data model is a collection of concepts for describing data. A schema is a description of a particular collection of data, using the a given data model. The relational model of data is the most widely used model today. - Main concept: relation, basically a table with rows and columns. - Every relat ...
The essence of data normalization is to spit the data into several
... 1. The same as a field. 2. The allowable values a column (or attribute) can have. 3. A link to another table. 4. A derived class. 5. A always a 1 - 1 relationship. The difference between composition and aggregation (collection): 1. Composition can exit only for one – one relation. 2. Composition can ...
... 1. The same as a field. 2. The allowable values a column (or attribute) can have. 3. A link to another table. 4. A derived class. 5. A always a 1 - 1 relationship. The difference between composition and aggregation (collection): 1. Composition can exit only for one – one relation. 2. Composition can ...
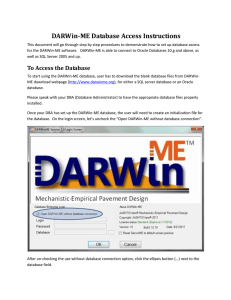
To Access the Database
... The “and” and “or” buttons provide the flexibility for users to select as many values from the third column as they want. In order to use these buttons, the user must first choose one of the six other buttons (Not Buttons “and” and “or”) to lock the object from the first column. Then user can click ...
... The “and” and “or” buttons provide the flexibility for users to select as many values from the third column as they want. In order to use these buttons, the user must first choose one of the six other buttons (Not Buttons “and” and “or”) to lock the object from the first column. Then user can click ...
Database Security - Department of Computer Science and
... fine grained authorizations, such as to individual tuples, can be implemented by the application. authorizations based on business logic easier to code at application level Authorization must be done in application code, and may be dispersed all over an application Hard to check or modify authorizat ...
... fine grained authorizations, such as to individual tuples, can be implemented by the application. authorizations based on business logic easier to code at application level Authorization must be done in application code, and may be dispersed all over an application Hard to check or modify authorizat ...
Attacking Data Stores
... Returns a dataset containing both the authors,titles,year and username,password,uid in one table This example only works if users table has three columns ...
... Returns a dataset containing both the authors,titles,year and username,password,uid in one table This example only works if users table has three columns ...
acdt2
... • ASP and SQL • Backend relational Access database • HTML web pages incorporating more complex HTML parameters for multimedia objects. • Delivered via a Windows 2000 server. ...
... • ASP and SQL • Backend relational Access database • HTML web pages incorporating more complex HTML parameters for multimedia objects. • Delivered via a Windows 2000 server. ...
Abstract
... Querying uncertain data has become a prominent application due to the proliferation of usergenerated content from social media and of data streams from sensors. When data ambiguity cannot be reduced algorithmically, crowdsourcing proves a viable approach, which consists of posting tasks to humans an ...
... Querying uncertain data has become a prominent application due to the proliferation of usergenerated content from social media and of data streams from sensors. When data ambiguity cannot be reduced algorithmically, crowdsourcing proves a viable approach, which consists of posting tasks to humans an ...
Section 10 - ODBC and Access Reports
... ODBC stands for Open Database Connectivity ODBC is Microsoft's strategic interface for accessing data in a heterogeneous environment of relational and non- relational database management systems. ...
... ODBC stands for Open Database Connectivity ODBC is Microsoft's strategic interface for accessing data in a heterogeneous environment of relational and non- relational database management systems. ...