DA-10562 - Worldwide
... Diverse data sources and formats Data access middleware needs to present a consistent data model to standard application programming interfaces (APIs), regardless of the multiplicity of back-end data sources. This allows applications to access all desired data regardless of storage format—from simpl ...
... Diverse data sources and formats Data access middleware needs to present a consistent data model to standard application programming interfaces (APIs), regardless of the multiplicity of back-end data sources. This allows applications to access all desired data regardless of storage format—from simpl ...
Connecting an ArcIMS Site to an External Database
... While JavaScript with HTML tags can be used to make Web pages interactive on the client side, creating Web pages by accessing a serverside database is not allowed for security reasons. However, a serverside crossplatform technology called JavaServer Pages (JSP) with Java Database Connectivity (JDBC) ...
... While JavaScript with HTML tags can be used to make Web pages interactive on the client side, creating Web pages by accessing a serverside database is not allowed for security reasons. However, a serverside crossplatform technology called JavaServer Pages (JSP) with Java Database Connectivity (JDBC) ...
Microsoft SQL Server - Microsoft Center
... Web interactions, brick-and-mortar transactions, mobile apps on cellular phones, and intelligent devices on the factory floor: Today there is an explosion of data sources that is driving an exponential boom in the volume of data. It may seem overwhelming, but the good news is organizations of all ty ...
... Web interactions, brick-and-mortar transactions, mobile apps on cellular phones, and intelligent devices on the factory floor: Today there is an explosion of data sources that is driving an exponential boom in the volume of data. It may seem overwhelming, but the good news is organizations of all ty ...
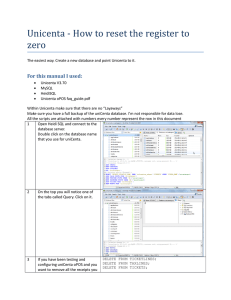
Unicenta - How to reset the register to zero
... Unicenta - How to reset the register to zero - sql03.txt Unicenta - How to reset the register to zero - sql07.txt Unicenta - How to reset the register to zero - sql09.txt Unicenta - How to reset the register to zero - sql10.txt Unicenta - How to reset the register to zero - sql11.txt ...
... Unicenta - How to reset the register to zero - sql03.txt Unicenta - How to reset the register to zero - sql07.txt Unicenta - How to reset the register to zero - sql09.txt Unicenta - How to reset the register to zero - sql10.txt Unicenta - How to reset the register to zero - sql11.txt ...
O'Brien - Intro. to Information Systems
... Logical Data Models e.g., relational, network, hierarchical, multidimensional, Or object-oriented models ...
... Logical Data Models e.g., relational, network, hierarchical, multidimensional, Or object-oriented models ...
Downaload - atlanta academy
... Unit II - Ms DOS Operating System - 15 Hrs (25 Marks) Function of Operating System, Job scheduling, Real-time OS, Multiprogramming, Timesharing, Introduction to Dos, System File, Dos Architecture, Booting, Internal and External Commands, Batch File. Unit III - Ms Windows Operating System - 15 Hrs (2 ...
... Unit II - Ms DOS Operating System - 15 Hrs (25 Marks) Function of Operating System, Job scheduling, Real-time OS, Multiprogramming, Timesharing, Introduction to Dos, System File, Dos Architecture, Booting, Internal and External Commands, Batch File. Unit III - Ms Windows Operating System - 15 Hrs (2 ...
Guided Test Generation for Database Applications via Synthesized
... solved with a constraint solver for test generation, but a constraint solver could not directly handle environment constraints. Considering the preceding four parts of constraints, applying DSE on testing database applications faces great challenges for generating both effective program inputs and s ...
... solved with a constraint solver for test generation, but a constraint solver could not directly handle environment constraints. Considering the preceding four parts of constraints, applying DSE on testing database applications faces great challenges for generating both effective program inputs and s ...
Third Year Computer Science and Engineering, 6 th
... Answer:a 31. Data integrity constraints are used to: a) Control who is allowed access to the data b) Ensure that duplicate records are not entered into the table c) Improve the quality of data entered for a specific property (i.e., table column) d) Prevent users from changing the values stored in th ...
... Answer:a 31. Data integrity constraints are used to: a) Control who is allowed access to the data b) Ensure that duplicate records are not entered into the table c) Improve the quality of data entered for a specific property (i.e., table column) d) Prevent users from changing the values stored in th ...
Manuscript for chapter 20
... [H2]Setting up the layout ***PD: please insert figure jafe2026.pcx source of DbDemo main and constructor through (not including) try [H3][a]Create an instance of the application This is standard procedure for standalone applications [H3][b]Set up the layout [H3][c]Add the listeners You might be surp ...
... [H2]Setting up the layout ***PD: please insert figure jafe2026.pcx source of DbDemo main and constructor through (not including) try [H3][a]Create an instance of the application This is standard procedure for standalone applications [H3][b]Set up the layout [H3][c]Add the listeners You might be surp ...
The Relational Theory
... • Treat data in a disciplined way –Apply rigor of mathematics –Uses Set Theory – sets of related data • Improve programmer productivity ...
... • Treat data in a disciplined way –Apply rigor of mathematics –Uses Set Theory – sets of related data • Improve programmer productivity ...
Statistical Database Query Languages
... embed a specific statistical procedures library into an SDBMS and develop syntactically simpler and easy-to-use capabilities in the query language to execute statistical analysis procedures (alternative one). This may be viewed as a master-slave approach in which the SDBMS dictates the execution of ...
... embed a specific statistical procedures library into an SDBMS and develop syntactically simpler and easy-to-use capabilities in the query language to execute statistical analysis procedures (alternative one). This may be viewed as a master-slave approach in which the SDBMS dictates the execution of ...
Structured Query Language SQL
... SQL supports different comparison operators. They can be used to compare attributes with constants or with other attributes. DIf an operator is used to compare an attribute with a constant, we talk about restriction. If the operator is used to compare two attributes, then we talk about a join. With ...
... SQL supports different comparison operators. They can be used to compare attributes with constants or with other attributes. DIf an operator is used to compare an attribute with a constant, we talk about restriction. If the operator is used to compare two attributes, then we talk about a join. With ...
iRequestManager for X3
... • Requester can be informed of status of his/her work requests through email, e.g., request accepted, completed, etc. • When a Work Request is approved, it can be emailed to the assigned technician and/or sent to his/her text pager or cell phone • You can customize the email/pager messages sent out ...
... • Requester can be informed of status of his/her work requests through email, e.g., request accepted, completed, etc. • When a Work Request is approved, it can be emailed to the assigned technician and/or sent to his/her text pager or cell phone • You can customize the email/pager messages sent out ...
Working with Data and ADO.Net
... Running a Command Command object provides three methods that are used to execute commands on the database: ExecuteNonQuery() – Execute commands that have no return value such as DELETE, INSERT, UPDATE. ...
... Running a Command Command object provides three methods that are used to execute commands on the database: ExecuteNonQuery() – Execute commands that have no return value such as DELETE, INSERT, UPDATE. ...
Oracle Apps DBA - Software Contractors` Guild
... AIX System Admin. Configured and installed AIX on pSeries equipment. Configured equipment using HACMP for Oracle 9i RAC environment. Extensive Performance Tuning at kernel, application and database levels Configured OEM for monitoring of all environments. Load balanced the application tier to two no ...
... AIX System Admin. Configured and installed AIX on pSeries equipment. Configured equipment using HACMP for Oracle 9i RAC environment. Extensive Performance Tuning at kernel, application and database levels Configured OEM for monitoring of all environments. Load balanced the application tier to two no ...
Distributed Database - delab-auth
... System? A distributed database (DDB) is a collection of multiple, logically interrelated databases distributed over a computer network. A distributed database management system (D–DBMS) is the software that manages the DDB and provides an access mechanism that makes this distribution transparent to ...
... System? A distributed database (DDB) is a collection of multiple, logically interrelated databases distributed over a computer network. A distributed database management system (D–DBMS) is the software that manages the DDB and provides an access mechanism that makes this distribution transparent to ...
Buffer Management in Distributed Database Systems: A Data Mining
... by other users afterwards should not enter the public bu er. { public bu er replacement problem: When a public bu er frame is needed to bring in a page from disk, and all current bu er frames are in use, which page from the public bu er should be replaced? { private bu er replacement problem: When a ...
... by other users afterwards should not enter the public bu er. { public bu er replacement problem: When a public bu er frame is needed to bring in a page from disk, and all current bu er frames are in use, which page from the public bu er should be replaced? { private bu er replacement problem: When a ...
this PDF file
... A logical program is finite set of rules together with database. A goal is a formula written as +-Bl, ... , Bm.A query is formula built from finite set of rules together with a goal. We distinguish between intensional database (IDP) and extensional database (EBP) predicate symbols, which are built f ...
... A logical program is finite set of rules together with database. A goal is a formula written as +-Bl, ... , Bm.A query is formula built from finite set of rules together with a goal. We distinguish between intensional database (IDP) and extensional database (EBP) predicate symbols, which are built f ...
Effective Usage of SQL Server 2005 Database Mirroring
... Webmaster(SQLMaster) of www.sqlserver-qa.net & www.sqloogle.co.uk ...
... Webmaster(SQLMaster) of www.sqlserver-qa.net & www.sqloogle.co.uk ...
Access to Databases Using SAS/ACCESS
... the parenthesized expression "select "' from EMP" is the pass-through SQL. This code is sent to the Oracle database server to return the data :from table "emp". The outer "select • from connection to oracle" returns the result to SAS. Finally, the "create table" clause cause the results to be saved ...
... the parenthesized expression "select "' from EMP" is the pass-through SQL. This code is sent to the Oracle database server to return the data :from table "emp". The outer "select • from connection to oracle" returns the result to SAS. Finally, the "create table" clause cause the results to be saved ...
Locks and Concurrency
... o READ COMMITTED - Specifies that shared locks are held while the data is being read to avoid dirty reads, but the data can be changed before the end of the transaction, resulting in nonrepeatable reads or phantom data. This option is the SQL Server default. o READ UNCOMMITTED - Implements dirty rea ...
... o READ COMMITTED - Specifies that shared locks are held while the data is being read to avoid dirty reads, but the data can be changed before the end of the transaction, resulting in nonrepeatable reads or phantom data. This option is the SQL Server default. o READ UNCOMMITTED - Implements dirty rea ...
Effective Use of SQL in SAS Programming
... identify each row in a table uniquely and foreign keys are used to maintain the integrity of the database. Many of the SQL primary keys and foreign keys are similar to variables used in the SAS by-merge data step. A database schema is used to describe the structure and relationship among tables. Usi ...
... identify each row in a table uniquely and foreign keys are used to maintain the integrity of the database. Many of the SQL primary keys and foreign keys are similar to variables used in the SAS by-merge data step. A database schema is used to describe the structure and relationship among tables. Usi ...
PowerPoint document describing the Trends data store - GCE-LTER
... • An ecological metadata standard • Very extensible; it can be used to describe many different types of data • Comprehensive and supports a rich set of constructs to fully describe data including – how to access distributed data – its logical and physical structure ...
... • An ecological metadata standard • Very extensible; it can be used to describe many different types of data • Comprehensive and supports a rich set of constructs to fully describe data including – how to access distributed data – its logical and physical structure ...
Oracle 10g Backup and Recovery New Features
... • In Oracle 10g, you no longer have to back up your database following an incomplete recovery and OPEN RESETLOGS operations. • This new feature is also applicable to the following two scenarios: – When you perform a recovery using a backup control file and open the database with the RESETLOGS operat ...
... • In Oracle 10g, you no longer have to back up your database following an incomplete recovery and OPEN RESETLOGS operations. • This new feature is also applicable to the following two scenarios: – When you perform a recovery using a backup control file and open the database with the RESETLOGS operat ...