ppt - FCN
... Outer Join An extension of the join operation that avoids loss of information. Computes the join and then adds tuples form one relation that does not ...
... Outer Join An extension of the join operation that avoids loss of information. Computes the join and then adds tuples form one relation that does not ...
User`s Guide and Reference
... "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agencyspecific supplemental regulations. As such, use, duplication, disclosure, modification, and adaptation of the programs, including any operating system, integrated software, any programs installed on th ...
... "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agencyspecific supplemental regulations. As such, use, duplication, disclosure, modification, and adaptation of the programs, including any operating system, integrated software, any programs installed on th ...
Microsoft Dynamics NAV
... Indicates the percentage of requests made by this instance that were serviced by the calculated fields cache. ...
... Indicates the percentage of requests made by this instance that were serviced by the calculated fields cache. ...
Chapter 5: Other Relational Languages
... bank, but do not have a loan from the bank. range of t is depositor range of u is borrower retrieve unique (t.customer-name) where any (u.loan-number by t.customer-name where u.customer-name = t.customer-name) = 0 The use of a comparison with any is analogous to the “there ...
... bank, but do not have a loan from the bank. range of t is depositor range of u is borrower retrieve unique (t.customer-name) where any (u.loan-number by t.customer-name where u.customer-name = t.customer-name) = 0 The use of a comparison with any is analogous to the “there ...
R - Department of Computer Science
... Let r and s be relations on schemas R and S respectively.The result is a relation on schema R S which is obtained by considering each pair of tuples tr from r and ts from s. If tr and ts have the same value on each of the attributes in R S, a tuple t is added to the result, where t has the ...
... Let r and s be relations on schemas R and S respectively.The result is a relation on schema R S which is obtained by considering each pair of tuples tr from r and ts from s. If tr and ts have the same value on each of the attributes in R S, a tuple t is added to the result, where t has the ...
SQL*Plus User`s Guide and Reference
... any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and ada ...
... any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and ada ...
Database Lifecycle Management
... the database needs frequent or periodic changes to features, functionality, or data, then this book is for you. It describes how to apply the business and technical approaches of Database Lifecycle Management (DLM) to make all database processes more visible, predictable, and measurable, with the ob ...
... the database needs frequent or periodic changes to features, functionality, or data, then this book is for you. It describes how to apply the business and technical approaches of Database Lifecycle Management (DLM) to make all database processes more visible, predictable, and measurable, with the ob ...
Partition Maintenance Effects
... The cost-based optimizer works off of statistics. Statistics on standard tables are easier to generate and comprehend than statistics on partition tables. Statistics are the number one problem with partitioning implementations. With partitions, there are LOCAL and GLOBAL statistics. GLOBAL statistic ...
... The cost-based optimizer works off of statistics. Statistics on standard tables are easier to generate and comprehend than statistics on partition tables. Statistics are the number one problem with partitioning implementations. With partitions, there are LOCAL and GLOBAL statistics. GLOBAL statistic ...
Query Planning for Searching Inter-dependent Deep
... and error-prone process. Recently, there has been a lot of work on developing deep web mining systems [6, 7, 14, 15, 19, 31, 38]. Most of these systems focus on query interface integration and schema matching. A challenge associated with deep web systems, which has not received attention so far, ari ...
... and error-prone process. Recently, there has been a lot of work on developing deep web mining systems [6, 7, 14, 15, 19, 31, 38]. Most of these systems focus on query interface integration and schema matching. A challenge associated with deep web systems, which has not received attention so far, ari ...
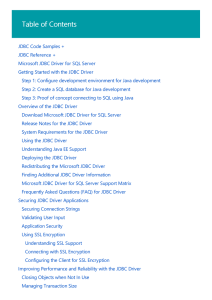
Microsoft JDBC Driver for SQL Server | Microsoft Docs
... Table-Valued Parameters Table-valued parameters provide an easy way to marshal multiple rows of data from a client application to SQL Server without requiring multiple round trips or special server-side logic for processing the data. You can use table-valued parameters to encapsulate rows of data in ...
... Table-Valued Parameters Table-valued parameters provide an easy way to marshal multiple rows of data from a client application to SQL Server without requiring multiple round trips or special server-side logic for processing the data. You can use table-valued parameters to encapsulate rows of data in ...
TimesTen SQL Reference
... any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and ada ...
... any programs installed on the hardware, and/or documentation, delivered to U.S. Government end users are "commercial computer software" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, use, duplication, disclosure, modification, and ada ...
Database Replication – an Overview of Replication Techniques in Patrik Rantanen
... However, networks and processors are getting faster and more capable, thus shifting the bottleneck towards the database management software and the operating systems. Databases and their performance, availability, response times and throughput are consequently facing new and challenging requirements ...
... However, networks and processors are getting faster and more capable, thus shifting the bottleneck towards the database management software and the operating systems. Databases and their performance, availability, response times and throughput are consequently facing new and challenging requirements ...
HP Vertica Analytics Platform 7.0.x Concepts Guide
... HP Vertica's unique approach to failure recovery is based on the distributed nature of a database. An HP Vertica database is said to be K-safe if any node can fail at any given time without causing the database to shut down. When the lost node comes back online and rejoins the database, it recovers ...
... HP Vertica's unique approach to failure recovery is based on the distributed nature of a database. An HP Vertica database is said to be K-safe if any node can fail at any given time without causing the database to shut down. When the lost node comes back online and rejoins the database, it recovers ...
Ingres 2006 SQL Reference Guide
... This documentation and related computer software program (hereinafter referred to as the "Documentation") is for the end user's informational purposes only and is subject to change or withdrawal by Ingres Corporation ("Ingres") at any time. This Documentation may not be copied, transferred, reprodu ...
... This documentation and related computer software program (hereinafter referred to as the "Documentation") is for the end user's informational purposes only and is subject to change or withdrawal by Ingres Corporation ("Ingres") at any time. This Documentation may not be copied, transferred, reprodu ...
Introduction to MS Query - Hutchins Central
... Figure 2: Synergetic MS Query Application Programing Interface (API) ................................... 4 Figure 3: Extract of StudentYears table..................................................................................... 5 Figure 4: Extract of StudentContacts table ....................... ...
... Figure 2: Synergetic MS Query Application Programing Interface (API) ................................... 4 Figure 3: Extract of StudentYears table..................................................................................... 5 Figure 4: Extract of StudentContacts table ....................... ...
Chapter 1
... an overarching multitenant container database. A multitenant container database (CDB) is defined as a database capable of housing one or more pluggable databases. A container is defined as a collection of data files and metadata that exist within a CDB. A pluggable database is a special type of cont ...
... an overarching multitenant container database. A multitenant container database (CDB) is defined as a database capable of housing one or more pluggable databases. A container is defined as a collection of data files and metadata that exist within a CDB. A pluggable database is a special type of cont ...
phpMyAdmin Arbitrary Command Execution Vulnerabilities
... The PHP Exploit that forms the basis for this practical is representative of a specific application vulnerability (in this instance, a vulnerability in a scripting language) that could be manipulated to effect a variety of application-based attacks, using HTTP as a transport mechanism. Of the protoc ...
... The PHP Exploit that forms the basis for this practical is representative of a specific application vulnerability (in this instance, a vulnerability in a scripting language) that could be manipulated to effect a variety of application-based attacks, using HTTP as a transport mechanism. Of the protoc ...
Getting started with IBM Data Studio for DB2
... The licensed program described in this document and all licensed material available for it are provided by IBM under terms of the IBM Customer Agreement, IBM International Program License Agreement or any equivalent agreement between us. Any performance data contained herein was determined in a con ...
... The licensed program described in this document and all licensed material available for it are provided by IBM under terms of the IBM Customer Agreement, IBM International Program License Agreement or any equivalent agreement between us. Any performance data contained herein was determined in a con ...
Accessing External Databases from RPG
... ErrMsg = 'Unable to CREATE table'; // show error message to user endif; ...
... ErrMsg = 'Unable to CREATE table'; // show error message to user endif; ...