![Introduction - start [kondor.etf.rs]](http://s1.studyres.com/store/data/000507900_1-4612cc6372b2ee158f9c52bcf8aea7c5-300x300.png)
Introduction - start [kondor.etf.rs]
... In 1974, TCP/IP model has been established by Cerf and Kahn, and incorporated into Berkeley UNIX. Because of the large number of hosts, domain name system (DNS) was created in 1980s. ...
... In 1974, TCP/IP model has been established by Cerf and Kahn, and incorporated into Berkeley UNIX. Because of the large number of hosts, domain name system (DNS) was created in 1980s. ...
15-744: Computer Networking
... • You learn a lot by working together • Several class meetings dedicated to projects ...
... • You learn a lot by working together • Several class meetings dedicated to projects ...
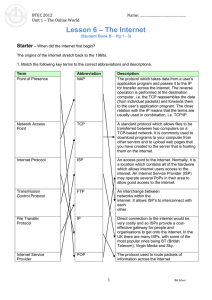
U1L6_The_Internet
... Internet Service Provider An Internet Service Provider (ISP) is a company which provides access to the internet for individuals or other companies (e.g. BT). An ISP will have many servers to do different things depending on the size of the company and amount of customers, e.g. one for outgoing email ...
... Internet Service Provider An Internet Service Provider (ISP) is a company which provides access to the internet for individuals or other companies (e.g. BT). An ISP will have many servers to do different things depending on the size of the company and amount of customers, e.g. one for outgoing email ...
L-IP - CentraLine
... A rather complex example for an L–IP deployment is shown below. In this scenario, the EIA-709 networks of two geographically separated facilites have to be connected. At both locations, the EIA-709 networks are connected to the company's IP network with an L–IP router. The L–IP (labeled CS) acts as ...
... A rather complex example for an L–IP deployment is shown below. In this scenario, the EIA-709 networks of two geographically separated facilites have to be connected. At both locations, the EIA-709 networks are connected to the company's IP network with an L–IP router. The L–IP (labeled CS) acts as ...
Internet - Introduction
... A wiki is a publishing platform on which many people can contribute new content and revise existing content. The content benefits from the collective knowledge of the contributors, so wikis can be very beneficial for group projects. Some businesses and organizations use wikis to maintain documents. ...
... A wiki is a publishing platform on which many people can contribute new content and revise existing content. The content benefits from the collective knowledge of the contributors, so wikis can be very beneficial for group projects. Some businesses and organizations use wikis to maintain documents. ...
25th IEEE International Conference on Network Protocols
... http://iqua.ece.toronto.edu/icnp17/ ICNP, the IEEE International Conference on Network Protocols, is the premier conference covering all aspects of network protocol research, including design, analysis, specification, verification, implementation, and performance. ICNP 2017, celebrating the silver a ...
... http://iqua.ece.toronto.edu/icnp17/ ICNP, the IEEE International Conference on Network Protocols, is the premier conference covering all aspects of network protocol research, including design, analysis, specification, verification, implementation, and performance. ICNP 2017, celebrating the silver a ...
Analytical work on 7DS
... 802.11 currently hard to deploy across city or large area 2.5G/3G wireless networks not suitable for large data volumes – cost and network design ...
... 802.11 currently hard to deploy across city or large area 2.5G/3G wireless networks not suitable for large data volumes – cost and network design ...
Lect01
... • Because it spans many countries Internet is called the global network. • Other networks were: BITNET, FIDONET, JANET, EARN. ...
... • Because it spans many countries Internet is called the global network. • Other networks were: BITNET, FIDONET, JANET, EARN. ...
MegaNet Dedicated Internet Access Features
... Multi-location companies can benefit from a fully secure and private Wide Area Network deployed over MegaNet T1 lines. Internal traffic stays off of the public Internet, and locations can each be connected to each other via private links, in addition to connectivity to the company’s main location. A ...
... Multi-location companies can benefit from a fully secure and private Wide Area Network deployed over MegaNet T1 lines. Internal traffic stays off of the public Internet, and locations can each be connected to each other via private links, in addition to connectivity to the company’s main location. A ...
Network Layer 2 - Faruk Hadziomerovic
... packet size of 8 payload bytes plus header. (c) Fragments after passing through a size 5 gateway. ...
... packet size of 8 payload bytes plus header. (c) Fragments after passing through a size 5 gateway. ...
The main goal of this thesis is to articulate and to prove security
... The main goal of this thesis is to articulate and to prove security properties of the key exchange protocol IKE, through which the IPSec protocol establishes agreement on keys used for securing internet traffic. It also covers the description of differences between asymptotic and concrete security t ...
... The main goal of this thesis is to articulate and to prove security properties of the key exchange protocol IKE, through which the IPSec protocol establishes agreement on keys used for securing internet traffic. It also covers the description of differences between asymptotic and concrete security t ...
9. telecommunications
... The TCP/IP Internet Protocol • Set of protocols developed by Vincent Cerf and Robert Kahn – Transmission Control Protocol (TCP) • Controls the assembly of a message into smaller packets before transmission, and reassembles them ...
... The TCP/IP Internet Protocol • Set of protocols developed by Vincent Cerf and Robert Kahn – Transmission Control Protocol (TCP) • Controls the assembly of a message into smaller packets before transmission, and reassembles them ...
Recitation1-Subnets
... Each network must be advertised. Inflexible Lack of a network classes for mid-sized organization (between class B and C). Address space will be eventually exhausted Internet Networking ...
... Each network must be advertised. Inflexible Lack of a network classes for mid-sized organization (between class B and C). Address space will be eventually exhausted Internet Networking ...
Recitation1
... Each network must be advertised. Inflexible Lack of a network classes for mid-sized organization (between class B and C). Address space will be eventually exhausted Internet Networking ...
... Each network must be advertised. Inflexible Lack of a network classes for mid-sized organization (between class B and C). Address space will be eventually exhausted Internet Networking ...
Week-10.3-2
... • Wide-area network (WAN) A network that connects two or more local-area networks over a potentially large geographic distance Often one particular node on a LAN is set up to serve as a gateway to handle all communication going between that LAN and other networks ...
... • Wide-area network (WAN) A network that connects two or more local-area networks over a potentially large geographic distance Often one particular node on a LAN is set up to serve as a gateway to handle all communication going between that LAN and other networks ...
ppt - Carnegie Mellon University
... • What is an Autonomous System (AS)? • A set of routers under a single technical administration, using an interior gateway protocol (IGP) and common metrics to route packets within the AS and using an exterior gateway protocol (EGP) to route packets to other AS’s ...
... • What is an Autonomous System (AS)? • A set of routers under a single technical administration, using an interior gateway protocol (IGP) and common metrics to route packets within the AS and using an exterior gateway protocol (EGP) to route packets to other AS’s ...
Internetworking - University of Maine System
... The clouds in each picture can represent a different network topology (FDDI, Ethernet), address scheme (IP, IPX), or both! ...
... The clouds in each picture can represent a different network topology (FDDI, Ethernet), address scheme (IP, IPX), or both! ...
01-intro
... • Traffic pattern (bursty or constant bit rate) • Traffic target (multipoint or single destination, mobile or fixed) • Delay sensitivity • Loss sensitivity ...
... • Traffic pattern (bursty or constant bit rate) • Traffic target (multipoint or single destination, mobile or fixed) • Delay sensitivity • Loss sensitivity ...
Internet and World Wide Web: Amazing Developments
... split into ARPANET (would continue its advanced research activities) and MILNET (would be reserved for military uses). As PCs became more powerful and affordable, firms increasingly used them to construct LANs. Today we use the term intranet to describe LANs or WANs that use the TCP/IP ...
... split into ARPANET (would continue its advanced research activities) and MILNET (would be reserved for military uses). As PCs became more powerful and affordable, firms increasingly used them to construct LANs. Today we use the term intranet to describe LANs or WANs that use the TCP/IP ...
Optical Packet/Burst Switching
... evolution towards smaller cell sizes in order to be able to satisfy the demand for high bandwidth. This however, results in a high handover frequency (a handover typically every few seconds) when the users move at vehicular speeds. ...
... evolution towards smaller cell sizes in order to be able to satisfy the demand for high bandwidth. This however, results in a high handover frequency (a handover typically every few seconds) when the users move at vehicular speeds. ...
2: Internet History How did the Internet come to be?
... 1990-1993: Ready for Public Consumption ...
... 1990-1993: Ready for Public Consumption ...
Technologies that make the Internet Robust
... • Compare with the old-style telephone networks – designed top-down by companies like AT&T, who built the network of telephone lines, and wanted (and had) complete control over their use – good aspect of design: • old handsets did not need electrical power • energy for dial-tone and speakers came f ...
... • Compare with the old-style telephone networks – designed top-down by companies like AT&T, who built the network of telephone lines, and wanted (and had) complete control over their use – good aspect of design: • old handsets did not need electrical power • energy for dial-tone and speakers came f ...