routing concepts and theory
... too many packets, they drop them things get worse at the “freeway exchanges” does routing protocol add congestion burden? how do we prevent/detect congestion? obviously circuit-switches don’t have this problem once circuit is set, but they waste ...
... too many packets, they drop them things get worse at the “freeway exchanges” does routing protocol add congestion burden? how do we prevent/detect congestion? obviously circuit-switches don’t have this problem once circuit is set, but they waste ...
Quality of Service Networking
... Quality of Service (QoS) refers to the capability of a network to provide better service to selected network traffic over various technologies, including Frame Relay, Asynchronous Transfer Mode (ATM), Ethernet and 802.1 networks, SONET, and IP-routed networks that may use any or all of these underly ...
... Quality of Service (QoS) refers to the capability of a network to provide better service to selected network traffic over various technologies, including Frame Relay, Asynchronous Transfer Mode (ATM), Ethernet and 802.1 networks, SONET, and IP-routed networks that may use any or all of these underly ...
Scalable Routing Strategies for Ad hoc Wireless Networks
... The major advantage of hierarchical routing is drastic reduction of routing table storage and processing overhead. A hierarchical clustering and routing approach speci cally designed for large wireless networks was recently proposed in [1] [10]. The proposal addresses the link and network layers onl ...
... The major advantage of hierarchical routing is drastic reduction of routing table storage and processing overhead. A hierarchical clustering and routing approach speci cally designed for large wireless networks was recently proposed in [1] [10]. The proposal addresses the link and network layers onl ...
Protection And Restoration In MPLS Networks
... of hardware and software. When a primary copy fails, processing is switched to the backup. This process, called failover, should result in minimal disruption to the data plane. Network providers can supply the required levels of service to their customers by building their network from equipment tha ...
... of hardware and software. When a primary copy fails, processing is switched to the backup. This process, called failover, should result in minimal disruption to the data plane. Network providers can supply the required levels of service to their customers by building their network from equipment tha ...
IP Multicast
... Truncated Broadcasting • Extension of Reverse Path Forwarding. • No members of a group on a subnet leaf router will not forward packets of this group to the subnet (pruning). • But does not reduce traffic in the core network. • More efficient multicast routing is needed!!! ...
... Truncated Broadcasting • Extension of Reverse Path Forwarding. • No members of a group on a subnet leaf router will not forward packets of this group to the subnet (pruning). • But does not reduce traffic in the core network. • More efficient multicast routing is needed!!! ...
Application of Mininet
... it knows that this PC is connected to this port and the traffic to this PC needs to only ben sent to that port and not to any of the others. The broadcasting happens at the beginning. Most of the traffic only goes where it needs to go rather than to every port. So a switch is faster. When there's hi ...
... it knows that this PC is connected to this port and the traffic to this PC needs to only ben sent to that port and not to any of the others. The broadcasting happens at the beginning. Most of the traffic only goes where it needs to go rather than to every port. So a switch is faster. When there's hi ...
Routing protocols for wireless networks
... Two special types of ad-hoc network • WSNs (Wireless Sensor Networks) • VANETs (Vehicular Ad-hoc Networks) ...
... Two special types of ad-hoc network • WSNs (Wireless Sensor Networks) • VANETs (Vehicular Ad-hoc Networks) ...
Chapter 7
... Describe the structure of an IPv4 address. Describe the purpose of the subnet mask. Compare the characteristics and uses of the unicast, broadcast and multicast IPv4 addresses. Explain the need for IPv6 addressing. Describe the representation of an IPv6 address. Describe types of IPv6 network addres ...
... Describe the structure of an IPv4 address. Describe the purpose of the subnet mask. Compare the characteristics and uses of the unicast, broadcast and multicast IPv4 addresses. Explain the need for IPv6 addressing. Describe the representation of an IPv6 address. Describe types of IPv6 network addres ...
6781_MPLS_Lecture2 - Computer Science and Engineering
... • MPLS can use the source routing capability to steer traffic on desired path • Operator may manually configure these in each LSR along the desired path - analogous to setting up PVCs in ATM switches • Ingress LSR may be configured with the path, RSVP used to set up LSP - some vendors have extended ...
... • MPLS can use the source routing capability to steer traffic on desired path • Operator may manually configure these in each LSR along the desired path - analogous to setting up PVCs in ATM switches • Ingress LSR may be configured with the path, RSVP used to set up LSP - some vendors have extended ...
Chapter 7: Label Distribution Protocols
... – This field is known as the request send targeted hellos. A value of 1 indicates that the receiver is requested to send periodic targeted hellos to the source of this hello. A value of 0 makes no such ...
... – This field is known as the request send targeted hellos. A value of 1 indicates that the receiver is requested to send periodic targeted hellos to the source of this hello. A value of 0 makes no such ...
Chapter6 (Delivery, Forwarding, and Routing of IP Packets)
... packet. In a connectionless service, the network layer protocol treats each packet independently, with each packet having no relationship to any other packet. The packets in a message may or may not travel the same path to their destination. The IP protocol is a connectionless protocol. The deli ...
... packet. In a connectionless service, the network layer protocol treats each packet independently, with each packet having no relationship to any other packet. The packets in a message may or may not travel the same path to their destination. The IP protocol is a connectionless protocol. The deli ...
Networks Oy - Roggeweck.net
... A firewall protects an IP network against external attack (for example, hackers from the mobile users or from the Internet). In the case of GPRS, the firewall might be configured to reject all packets that are not part of a GPRS subscriberinitiated connection. The firewall can also include NAT (Netw ...
... A firewall protects an IP network against external attack (for example, hackers from the mobile users or from the Internet). In the case of GPRS, the firewall might be configured to reject all packets that are not part of a GPRS subscriberinitiated connection. The firewall can also include NAT (Netw ...
host
... • Only solution: split up the people onto multiple wires • But how can they talk to each other? ...
... • Only solution: split up the people onto multiple wires • But how can they talk to each other? ...
Fingerprinting Encrypted Tunnel Endpoints Vafa Dario Izadinia U
... to devise a way to better protect the information, or investigators putting together clues in the aftermath of a break-in; the more is known of the system as a whole, the more detailed the image that can be constructed. One method for acquiring this information is termed Operating System Fingerprint ...
... to devise a way to better protect the information, or investigators putting together clues in the aftermath of a break-in; the more is known of the system as a whole, the more detailed the image that can be constructed. One method for acquiring this information is termed Operating System Fingerprint ...
Secure Efficient Distance Vector Routing for Mobile Wireless Ad Hoc
... multihop paths. Since the nodes in the network may move at any time, or may even move continuously, and since sources of wireless interference and wireless transmission propagation conditions may change frequently, the routing protocol must also be able to react to these changes and to learn new rou ...
... multihop paths. Since the nodes in the network may move at any time, or may even move continuously, and since sources of wireless interference and wireless transmission propagation conditions may change frequently, the routing protocol must also be able to react to these changes and to learn new rou ...
BlackDiamond 8800 series chassis-based switches simplify the
... serves well as a high-performance Enterprise core and Data Center switch. The ports interconnect thousands of servers for High Performance Cluster Computing (HPCC). The BlackDiamond 8800 series switches with 8900-xl series modules meet the needs of next generation service provider transport networks ...
... serves well as a high-performance Enterprise core and Data Center switch. The ports interconnect thousands of servers for High Performance Cluster Computing (HPCC). The BlackDiamond 8800 series switches with 8900-xl series modules meet the needs of next generation service provider transport networks ...
Peer-to-Peer Overlay Broker Networks in an Event
... network with full IP connectivity. However, for scalability reasons and in order to do content-based routing, an event broker only needs to know about a subset of all brokers in the system. Every event broker has such a set of neighbouring brokers and it chooses a next hop from this set when it is m ...
... network with full IP connectivity. However, for scalability reasons and in order to do content-based routing, an event broker only needs to know about a subset of all brokers in the system. Every event broker has such a set of neighbouring brokers and it chooses a next hop from this set when it is m ...
MRP: Wireless mesh networks routing protocol Jangeun Jun, Mihail L. Sichitiu
... and allowing them to forward each other’s packets to and from a common gateway (another AP connected to the distribution system). The main drawback of these deployments is the reduced bandwidth available to the users (this can become a major problem in scenarios with many active users [20]). Some co ...
... and allowing them to forward each other’s packets to and from a common gateway (another AP connected to the distribution system). The main drawback of these deployments is the reduced bandwidth available to the users (this can become a major problem in scenarios with many active users [20]). Some co ...
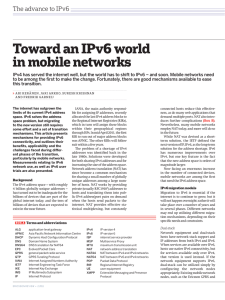
Toward an IPv6 world in mobile networks – mechanisms
... correct; and that any implementation bugs have been removed. The native dual-stack model is shown in Figure 1. Here the entire network – from the UE to the servers running the services – supports both IPv4 and IPv6. Services can be accessed using either protocol, depending on which one is supported ...
... correct; and that any implementation bugs have been removed. The native dual-stack model is shown in Figure 1. Here the entire network – from the UE to the servers running the services – supports both IPv4 and IPv6. Services can be accessed using either protocol, depending on which one is supported ...
document
... effectively divide an OSPF domain into sub-domains. •A router in an area knows nothing detailed of topology outside of its own area. •Expressed in an Area ID of 32 bits, most often as decimal, but can be in dotted decimal like an IP address. •Area 0 must exist in all OSPF implementations and should ...
... effectively divide an OSPF domain into sub-domains. •A router in an area knows nothing detailed of topology outside of its own area. •Expressed in an Area ID of 32 bits, most often as decimal, but can be in dotted decimal like an IP address. •Area 0 must exist in all OSPF implementations and should ...
- Lecturer
... Poisoning (files with contents different to its description) Polluting (inserting bad packets into the files) Defection (users use the service without sharing) Insertion of viruses (attached to other files) Malware (spy originally attached to the files) Denial of Service (slow down or stop the netwo ...
... Poisoning (files with contents different to its description) Polluting (inserting bad packets into the files) Defection (users use the service without sharing) Insertion of viruses (attached to other files) Malware (spy originally attached to the files) Denial of Service (slow down or stop the netwo ...