Ecommerce: Security and Control
... commonly used when transferring sensitive data electronically across (e.g.) the Internet Authentication: Providing secure mechanisms for accessing specific elements of the ecommerce system. Most common method is registration with the ecommerce system, and using usernames and passwords. Digital signa ...
... commonly used when transferring sensitive data electronically across (e.g.) the Internet Authentication: Providing secure mechanisms for accessing specific elements of the ecommerce system. Most common method is registration with the ecommerce system, and using usernames and passwords. Digital signa ...
Introduction to quantum cryptography
... • and telescopes with 8-inch mirrors to send and receive photons over the air. • Using the quantum transmitted key messages were encrypted at the rate 1 million bits per second. The speed was impressive but the distance between two NIST buildings was only 730 ...
... • and telescopes with 8-inch mirrors to send and receive photons over the air. • Using the quantum transmitted key messages were encrypted at the rate 1 million bits per second. The speed was impressive but the distance between two NIST buildings was only 730 ...
Java Security
... Implementation independence means that different providers can implement the same engine class in different ways. A user may request an implementation from a specific provider or specify a preference order of the providers in which providers are searched for requested services when no specific provi ...
... Implementation independence means that different providers can implement the same engine class in different ways. A user may request an implementation from a specific provider or specify a preference order of the providers in which providers are searched for requested services when no specific provi ...
compatible-development-of
... often used for signing, encrypting and decrypting e-mails to increase the security of email communications. RSA Security Inc. released their RSA algorithm into the public domain, a few days in advance of their U.S. Patent 4,405,829 expiring. Following the relaxation of the U.S. government export res ...
... often used for signing, encrypting and decrypting e-mails to increase the security of email communications. RSA Security Inc. released their RSA algorithm into the public domain, a few days in advance of their U.S. Patent 4,405,829 expiring. Following the relaxation of the U.S. government export res ...
Packaging Information: Data Compression and
... The secret key must be transferred securely in order for secret key methods to be secure Data Encryption Standard (DES) is a US government sponsored secret key cipher. DES uses a 56-bit key. International Data Encryption Algorithm (IDEA) has been proposed to replace DES. It uses a 128-bit key. Longe ...
... The secret key must be transferred securely in order for secret key methods to be secure Data Encryption Standard (DES) is a US government sponsored secret key cipher. DES uses a 56-bit key. International Data Encryption Algorithm (IDEA) has been proposed to replace DES. It uses a 128-bit key. Longe ...
Slides on Security
... key along with some information about the user, such as their email address. • The digital certificate is digitally signed by a Certificate Authority. • Certificate Authorities are venders of ...
... key along with some information about the user, such as their email address. • The digital certificate is digitally signed by a Certificate Authority. • Certificate Authorities are venders of ...
notes
... might be replaced to new router which can support IP Multicast function. May incur cost to replace router 2. While a few recent works have considered issues with key dissemination using overlays, these works rely on analysis or simulations with synthetic workloads and don’t consider issues such as ...
... might be replaced to new router which can support IP Multicast function. May incur cost to replace router 2. While a few recent works have considered issues with key dissemination using overlays, these works rely on analysis or simulations with synthetic workloads and don’t consider issues such as ...
Guide to Firewalls and Network Security with Intrusion Detection and
... PGP Hybrid system that combines advantages of asymmetric (scalability) and symmetric (speed) encryption systems ...
... PGP Hybrid system that combines advantages of asymmetric (scalability) and symmetric (speed) encryption systems ...
Presentation4 - University Of Worcester
... e.g. Windows SIGVER (file signing) » method of checking incoming files to ensure that they are from a Microsoft approved source ...
... e.g. Windows SIGVER (file signing) » method of checking incoming files to ensure that they are from a Microsoft approved source ...
Protecting Valuable Physical Assets in a High Traffic Setting
... used a combination of electronic card reader door locks and standard padlocks to guard sensitive areas of the airport. Although the use of two locks might seem redundant in other settings, in an airport environment it is necessary in case the electronic readers fail. Card readers play an important r ...
... used a combination of electronic card reader door locks and standard padlocks to guard sensitive areas of the airport. Although the use of two locks might seem redundant in other settings, in an airport environment it is necessary in case the electronic readers fail. Card readers play an important r ...
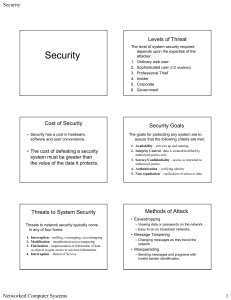
Security
... receiver with a key can decipher the content A single (symmetric) secret key is used to encrypt and decrypt Requires the communication of the key between sender and receiver! Basis of nuclear war-head command and control security ...
... receiver with a key can decipher the content A single (symmetric) secret key is used to encrypt and decrypt Requires the communication of the key between sender and receiver! Basis of nuclear war-head command and control security ...
Lecture on Security
... If I have a certificate from my bank, I can log on to the Bank’s website without a password. Moreover, If I have a certificate from the government, do I need to show my Social Security Number at every step? ...
... If I have a certificate from my bank, I can log on to the Bank’s website without a password. Moreover, If I have a certificate from the government, do I need to show my Social Security Number at every step? ...
Cryptography and Coding Theory
... IT662 Cryptography and Coding Theory L – T – P: 3 – 0 – 0 Credit: 3 Objectives: The objective of the course is to provide detail knowledge of cryptography and Coding Theory Pre-requisite: Cryptography knowledge of under grad level. Outcome: Should have earned knowledge of several cryptographic algor ...
... IT662 Cryptography and Coding Theory L – T – P: 3 – 0 – 0 Credit: 3 Objectives: The objective of the course is to provide detail knowledge of cryptography and Coding Theory Pre-requisite: Cryptography knowledge of under grad level. Outcome: Should have earned knowledge of several cryptographic algor ...
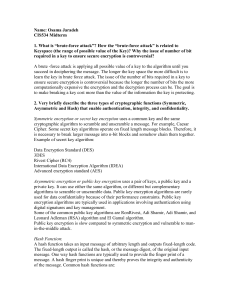
Three challenges with secret key encryption
... required in a key to ensure secure encryption is controversial? A brute -force attack is applying all possible value of a key to the algorithm until you succeed in deciphering the message. The longer the key space the more difficult is to learn the key in brute force attack. The issue of the number ...
... required in a key to ensure secure encryption is controversial? A brute -force attack is applying all possible value of a key to the algorithm until you succeed in deciphering the message. The longer the key space the more difficult is to learn the key in brute force attack. The issue of the number ...
Chapter 8: Network Security
... confidentiality since anyone with the public key could decrypt such a message. This property is, however, useful for authentication since it tells the receiver of such a message that it could only have been created by the owner of the keys. ...
... confidentiality since anyone with the public key could decrypt such a message. This property is, however, useful for authentication since it tells the receiver of such a message that it could only have been created by the owner of the keys. ...
security
... • Dictionary attack is trying to determine a decryption key or pass-phrase by searching a large number of possibilities • Remote access to a user’s account allows files to be copied or corrupted. • Hacking used to be a game – now it is done by criminals for theft. ...
... • Dictionary attack is trying to determine a decryption key or pass-phrase by searching a large number of possibilities • Remote access to a user’s account allows files to be copied or corrupted. • Hacking used to be a game – now it is done by criminals for theft. ...
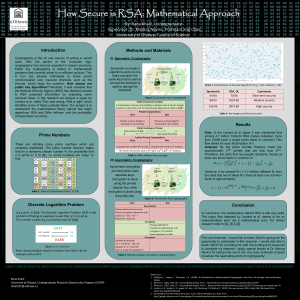
Genigraphics Research Poster Template 44x44
... Cryptography is the art and science of writing in secret code. With the advent of the Computer Age, cryptography has become essential in today's economy. Public key cryptography is based on mathematical problems that currently admit to no efficient solution. This in turn has allowed individuals to s ...
... Cryptography is the art and science of writing in secret code. With the advent of the Computer Age, cryptography has become essential in today's economy. Public key cryptography is based on mathematical problems that currently admit to no efficient solution. This in turn has allowed individuals to s ...
Chapter 08
... Public-key encryption does not require that you openly exchange a secret key with the recipient of an encrypted message RSA is the most familiar public-key algorithm Signatures on a document show that the sender is the only one who could have sent the document Certificates are issued and signed by c ...
... Public-key encryption does not require that you openly exchange a secret key with the recipient of an encrypted message RSA is the most familiar public-key algorithm Signatures on a document show that the sender is the only one who could have sent the document Certificates are issued and signed by c ...
Powerpoint Slides
... intermediate router and impersonate an authorized client. An imposter can also impersonate a server. ...
... intermediate router and impersonate an authorized client. An imposter can also impersonate a server. ...
Public Key Encryption and Digital Signatures
... problems with allowable exports, and are not always allowed to talk about their work. • Is it desirable to have government able to crack all codes? • What is the tradeoff between privacy of law abiding citizens vs. the ability of terrorists and drug traffickers to communicate in secret? ...
... problems with allowable exports, and are not always allowed to talk about their work. • Is it desirable to have government able to crack all codes? • What is the tradeoff between privacy of law abiding citizens vs. the ability of terrorists and drug traffickers to communicate in secret? ...
E-Commerce Security
... Public Key Encryption • Uses two different keys: a public and a private key. • Receiver’s public key must be delivered in advance. • Sender uses receiver’s public key to encrypt the message and receiver uses private key to decrypt the message (Sender can be sure the receiver is the true receiver) • ...
... Public Key Encryption • Uses two different keys: a public and a private key. • Receiver’s public key must be delivered in advance. • Sender uses receiver’s public key to encrypt the message and receiver uses private key to decrypt the message (Sender can be sure the receiver is the true receiver) • ...
Implementing Security for Electronic Commerce
... and is used to decrypt an encrypted message. If Jack wants to send a message to Jill, then Jack obtains Jill’s public key, encrypts the message with it, and sends it. Only Jill can decrypt this message with her private key. ...
... and is used to decrypt an encrypted message. If Jack wants to send a message to Jill, then Jack obtains Jill’s public key, encrypts the message with it, and sends it. Only Jill can decrypt this message with her private key. ...
Network Security
... PGP (short for Pretty Good Privacy), created by Philip Zimmermann, is the de facto standard program for secure e-mail and file encryption on the Internet. Its public-key cryptography system enables people who have never met to secure transmitted messages against unauthorized reading and to add digit ...
... PGP (short for Pretty Good Privacy), created by Philip Zimmermann, is the de facto standard program for secure e-mail and file encryption on the Internet. Its public-key cryptography system enables people who have never met to secure transmitted messages against unauthorized reading and to add digit ...
Public-key cryptography
Public-key cryptography, also known as asymmetric cryptography, is a class of cryptographic protocols based on algorithms that require two separate keys, one of which is secret (or private) and one of which is public. Although different, the two parts of this key pair are mathematically linked. The public key is used, for example, to encrypt plaintext or to verify a digital signature; whereas the private key is used for the opposite operation, in these examples to decrypt ciphertext or to create a digital signature. The term ""asymmetric"" stems from the use of different keys to perform these opposite functions, each the inverse of the other – as contrasted with conventional (""symmetric"") cryptography which relies on the same key to perform both.Public-key algorithms are based on mathematical problems that currently admit no efficient solution and are inherent in certain integer factorization, discrete logarithm, and elliptic curve relationships. It is computationally easy for a user to generate a public and private key-pair and to use it for encryption and decryption. The strength lies in the ""impossibility"" (computational impracticality) for a properly generated private key to be determined from its corresponding public key. Thus the public key may be published without compromising security. Security depends only on keeping the private key private. Public key algorithms, unlike symmetric key algorithms, do not require a secure channel for the initial exchange of one (or more) secret keys between the parties.Because of the computational complexity of asymmetrical encryption, it is typically used only to transfer a symmetrical encryption key by which the message (and usually the entire conversation) is encrypted. The symmetrical encryption/decryption is based on simpler algorithms and is much faster.Message authentication involves hashing the message to produce a ""digest,"" and encrypting the digest with the private key to produce a digital signature. Thereafter anyone can verify this signature by (1) computing the hash of the message, (2) decrypting the signature with the signer's public key, and (3) comparing the computed digest with the decrypted digest. Equality between the digests confirms the message is unmodified since it was signed, and that the signer, and no one else, intentionally performed the signature operation — presuming the signer's private key has remained secret to the signer. The security of such procedure depends on a hash algorithm of such quality that it is computationally impossible to alter or find a substitute message that produces the same digest - but studies have shown that even with the MD5 and SHA-1 algorithms, producing an altered or substitute message is not impossible. The current hashing standard for encryption is SHA-2. The message itself can also be used in place of the digest.Public-key algorithms are fundamental security ingredients in cryptosystems, applications and protocols. They underpin various Internet standards, such as Transport Layer Security (TLS), S/MIME, PGP, and GPG. Some public key algorithms provide key distribution and secrecy (e.g., Diffie–Hellman key exchange), some provide digital signatures (e.g., Digital Signature Algorithm), and some provide both (e.g., RSA).Public-key cryptography finds application in, amongst others, the IT security discipline information security. Information security (IS) is concerned with all aspects of protecting electronic information assets against security threats. Public-key cryptography is used as a method of assuring the confidentiality, authenticity and non-repudiability of electronic communications and data storage.