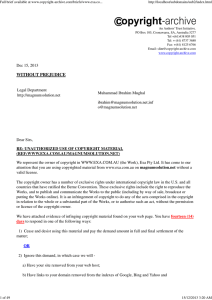
Copyright-Archive Report - Copyright
... You are now on notice as to copyright in respect of the Work. If we do not receive an adequate response by Dec 29, 2013, we will immediately and without further warning take such action as necessary in order to protect our client's rights including, without limitation, legal action for injunctive re ...
... You are now on notice as to copyright in respect of the Work. If we do not receive an adequate response by Dec 29, 2013, we will immediately and without further warning take such action as necessary in order to protect our client's rights including, without limitation, legal action for injunctive re ...
Selenium WebDriver Recipes in Ruby
... After observing many failed test automation attempts by using expensive commercial test automation tools, I am delighted to see that the value of open-source testing frameworks has finally been recognized. I still remember the day (a rainy day at a Gold Coast hotel in 2011) when I found out that the ...
... After observing many failed test automation attempts by using expensive commercial test automation tools, I am delighted to see that the value of open-source testing frameworks has finally been recognized. I still remember the day (a rainy day at a Gold Coast hotel in 2011) when I found out that the ...
ASP
... – ASP.NET (originally called ASP+) is the next generation ASP. – ASP.NET is different than its predecessor in two major ways: • It supports code written in compiled languages such as Visual Basic, C++, C# and Perl, • It features server controls that can separate the code from the content, allowing W ...
... – ASP.NET (originally called ASP+) is the next generation ASP. – ASP.NET is different than its predecessor in two major ways: • It supports code written in compiled languages such as Visual Basic, C++, C# and Perl, • It features server controls that can separate the code from the content, allowing W ...
PDF factsheet (Word, 1.8MB)
... and incomplete. Some features convey semantic meaning that is not supported by all assistive technologies (such as screen readers). For example, a tagged heading allows a user to navigate the sections of a document quickly, and a tagged paragraph identifies paragraph blocks. These features are not y ...
... and incomplete. Some features convey semantic meaning that is not supported by all assistive technologies (such as screen readers). For example, a tagged heading allows a user to navigate the sections of a document quickly, and a tagged paragraph identifies paragraph blocks. These features are not y ...
Point and Click Web Pages with Design-Time Controls and SAS/IntrNet Software
... reads the Windows registry and loads your default SAS server connection information. This information is set when the DesignTIme Controls are installed on your machine. The control does not connect to the SAS server at this time. When you invoke the properties dialog for the control and make selecti ...
... reads the Windows registry and loads your default SAS server connection information. This information is set when the DesignTIme Controls are installed on your machine. The control does not connect to the SAS server at this time. When you invoke the properties dialog for the control and make selecti ...
MS Word format
... audio. The problem was even more acute when it came to access to data using software such as Macromedia Flash or Adobe PDF. Macromedia Flash’s SWF format provides many features attractive to projects. Projects, quite rightly, considered that the ability to create stylish graphics and animations woul ...
... audio. The problem was even more acute when it came to access to data using software such as Macromedia Flash or Adobe PDF. Macromedia Flash’s SWF format provides many features attractive to projects. Projects, quite rightly, considered that the ability to create stylish graphics and animations woul ...
Week 11 - cda college
... • A web page is often an interested page including pictures, background and a lot of information. Each page includes different or similar information and every web page has its own source code. For each web page there exist different web addresses which you have to type it in your web browser to go ...
... • A web page is often an interested page including pictures, background and a lot of information. Each page includes different or similar information and every web page has its own source code. For each web page there exist different web addresses which you have to type it in your web browser to go ...
The following paper was originally published in the
... Why use Tcl? Scripting languages such as Tcl represent a very different style of programming than system programming languages such as C or JavaTM. Scripting languages are designed to achieve a higher level of programming and more rapid application development than system programming languages. Scri ...
... Why use Tcl? Scripting languages such as Tcl represent a very different style of programming than system programming languages such as C or JavaTM. Scripting languages are designed to achieve a higher level of programming and more rapid application development than system programming languages. Scri ...
Web CMS 1 Basic Editing
... out as most people read from left to right, making sure your important messages do not get missed. ...
... out as most people read from left to right, making sure your important messages do not get missed. ...
What is HTML?
... HTML 3.2 Was Very Wrong ! The original HTML was never intended to contain tags for formatting a document. HTML tags were intended to define the content of the document like:
... HTML 3.2 Was Very Wrong ! The original HTML was never intended to contain tags for formatting a document. HTML tags were intended to define the content of the document like:
This is a paragraph
This is a heading
When tags like and color attributes were added to the HTML 3.2 sp ...
Words - Picnic Website Code Tutorials
... understand and encourage you as the “Client” to voice your opinion and request to make any and all changes that you feel is in the best interest of your website. However, “you” as the Client, must also understand that in doing so, this may mean a considerable amount of work for me to make any major ...
... understand and encourage you as the “Client” to voice your opinion and request to make any and all changes that you feel is in the best interest of your website. However, “you” as the Client, must also understand that in doing so, this may mean a considerable amount of work for me to make any major ...
Computer Science E-259
... the host web server, in a different process on the same host, or on a different host from the web server for which it processes requests. 3. The servlet container determines which servlet to invoke based on the configuration of its servlets, and calls it with objects representing the request and res ...
... the host web server, in a different process on the same host, or on a different host from the web server for which it processes requests. 3. The servlet container determines which servlet to invoke based on the configuration of its servlets, and calls it with objects representing the request and res ...
Metasearch engines perform keyword searches on multiple search
... 3. Try the same searches on at least one other search engine. Do you get the same results? 4. Phrase searching is used to locate an exact phrase, like the title of an article. It’s also good for forcing the search engine to include key words it might otherwise ignore (like “Star Wars I”). Return to ...
... 3. Try the same searches on at least one other search engine. Do you get the same results? 4. Phrase searching is used to locate an exact phrase, like the title of an article. It’s also good for forcing the search engine to include key words it might otherwise ignore (like “Star Wars I”). Return to ...
Test Bank for The Web Wizard`s Guide to HTML
... Answer: The web browser will know what size the images are going to be, reserve space for them and place the text on the reserved space. Thus users can read the text while the images are loading. ...
... Answer: The web browser will know what size the images are going to be, reserve space for them and place the text on the reserved space. Thus users can read the text while the images are loading. ...
Mobi-sites and Apps for Mobile Devices
... • https://pittsburghkids.org/ • http://www.bostonglobe.com/ ...
... • https://pittsburghkids.org/ • http://www.bostonglobe.com/ ...
Introduction to Dreamweaver
... the WYSIWYG mode stomps all over the underlying HTML code, Dreamweaver respects hand-typed code and doesn’t try to rewrite it (unless you ask it to). In addition, Dreamweaver can open many other types of files commonly used in Web sites, such as external JavaScript files (.js files), so you don’t ha ...
... the WYSIWYG mode stomps all over the underlying HTML code, Dreamweaver respects hand-typed code and doesn’t try to rewrite it (unless you ask it to). In addition, Dreamweaver can open many other types of files commonly used in Web sites, such as external JavaScript files (.js files), so you don’t ha ...
What Is Web Design? - McGraw-Hill
... structured using a markup technology such as HTML. ■ Visuals This refers to the screen layout used in a site. The layout is usually created using HTML, CSS, or even Flash and may include graphic elements either as decoration or for navigation. The visual aspect of the site is the most obvious aspect ...
... structured using a markup technology such as HTML. ■ Visuals This refers to the screen layout used in a site. The layout is usually created using HTML, CSS, or even Flash and may include graphic elements either as decoration or for navigation. The visual aspect of the site is the most obvious aspect ...
Why Workflows?
... • take actions that push possible workflow instances further without knowing which instances currently exist. • make complex decisions about which actions to take to maximize the expected utility. ...
... • take actions that push possible workflow instances further without knowing which instances currently exist. • make complex decisions about which actions to take to maximize the expected utility. ...
The Security Architecture of the Chromium Browser
... 1. The attacker owns a domain name, say attacker.com, that has not yet been added to the browser’s malware blacklist [19]. The attacker has a valid HTTPS certificate for the domain, and controls at least one host on the network. These abilities can be purchased for about $5. 2. The attacker is able ...
... 1. The attacker owns a domain name, say attacker.com, that has not yet been added to the browser’s malware blacklist [19]. The attacker has a valid HTTPS certificate for the domain, and controls at least one host on the network. These abilities can be purchased for about $5. 2. The attacker is able ...
The Security Architecture of the Chromium Browser
... 1. The attacker owns a domain name, say attacker.com, that has not yet been added to the browser’s malware blacklist [19]. The attacker has a valid HTTPS certificate for the domain, and controls at least one host on the network. These abilities can be purchased for about $5. 2. The attacker is able ...
... 1. The attacker owns a domain name, say attacker.com, that has not yet been added to the browser’s malware blacklist [19]. The attacker has a valid HTTPS certificate for the domain, and controls at least one host on the network. These abilities can be purchased for about $5. 2. The attacker is able ...























