Reasoning in Architecture
... specify tasks, design phases or step from beginning to end. Schön theory is presented in his book The Reflective Practitioner (1983) 2. Jeff Hawkins (1957) is a computer architect turned neurologist. He is interested in making truly intelligent machines, but believes one can only do so when we und ...
... specify tasks, design phases or step from beginning to end. Schön theory is presented in his book The Reflective Practitioner (1983) 2. Jeff Hawkins (1957) is a computer architect turned neurologist. He is interested in making truly intelligent machines, but believes one can only do so when we und ...
INFO372 - Department of Computer Science
... Rational behavior: doing the right thing; that which is expected to maximize goal achievement, given the available information; Doesn't necessarily involve thinking – e.g., blinking reflex – but thinking should be in the service of rational action; ...
... Rational behavior: doing the right thing; that which is expected to maximize goal achievement, given the available information; Doesn't necessarily involve thinking – e.g., blinking reflex – but thinking should be in the service of rational action; ...
Designing Web-Based Organizational Memory for Knowledge
... knowledge; d) Combining knowledge (combination). An organization can perform at its best if all available knowledge can be combined in its new products and services. OM may facilitate this combination by making it easier to access knowledge developed in different parts of the organization. To unders ...
... knowledge; d) Combining knowledge (combination). An organization can perform at its best if all available knowledge can be combined in its new products and services. OM may facilitate this combination by making it easier to access knowledge developed in different parts of the organization. To unders ...
over deliver
... years have had positive results. Many no doubt go unreported, but two high profile ones in recent time are Microsoft’s Tay AI Bot (a Machine Learning onl online ine chatbot that learns from its interactions). Tay developed a “character” with strong racist, sexist opinions, and had to be removed [16] ...
... years have had positive results. Many no doubt go unreported, but two high profile ones in recent time are Microsoft’s Tay AI Bot (a Machine Learning onl online ine chatbot that learns from its interactions). Tay developed a “character” with strong racist, sexist opinions, and had to be removed [16] ...
Joanna J. Bryson - Department of Computer Science
... of Emergent Group-Level Traits”. Jekaterina Novikova, Leonn Watts and Joanna J. Bryson, “The Role of Emotions in Inter-Action Selection”, commentary on Faragó et al. “Social behaviours in dog-owner interactions can serve as a model for designing social robots”, Interaction Studies, 15(2):216–223. K ...
... of Emergent Group-Level Traits”. Jekaterina Novikova, Leonn Watts and Joanna J. Bryson, “The Role of Emotions in Inter-Action Selection”, commentary on Faragó et al. “Social behaviours in dog-owner interactions can serve as a model for designing social robots”, Interaction Studies, 15(2):216–223. K ...
Rise of the humans
... transformation in the way that humans and machines connect and relate. In the view of Klaus Schwab, founder of the World Economic Forum, the first three industrial revolutions were underpinned by steam engines, mass production and electricity, and information technology. According to Schwab, the fou ...
... transformation in the way that humans and machines connect and relate. In the view of Klaus Schwab, founder of the World Economic Forum, the first three industrial revolutions were underpinned by steam engines, mass production and electricity, and information technology. According to Schwab, the fou ...
Software Agents - UMBC Agent Web
... by new ones in distributed artificial intelligence, robotics, artificial life, distributed object computing, human-computer interaction, intelligent and adaptive interfaces, intelligent search and filtering, information retrieval, knowledge acquisition, end-user programming, programming-by-demonstra ...
... by new ones in distributed artificial intelligence, robotics, artificial life, distributed object computing, human-computer interaction, intelligent and adaptive interfaces, intelligent search and filtering, information retrieval, knowledge acquisition, end-user programming, programming-by-demonstra ...
An Agent Model for Future Autonomic Communications
... that is made available within a network to access and exploit the network resources. IP datagram routing, DNS, socketbased point-to-point communication, cryptographic tools, web services and P2P data delivery services, can all be considered communication services. The definition applies independentl ...
... that is made available within a network to access and exploit the network resources. IP datagram routing, DNS, socketbased point-to-point communication, cryptographic tools, web services and P2P data delivery services, can all be considered communication services. The definition applies independentl ...
Turing*s Legacy - Cognitive Science Department
... is not clear that a machine couldn’t do anything new or creative when looked at from a higher level. • Indeed, look at Deep Blue: Deep Blue beats every human in chess, but that would be impossible if Deep Blue couldn’t do any better than any of its programmers. • Similarly, pending any mechanical gl ...
... is not clear that a machine couldn’t do anything new or creative when looked at from a higher level. • Indeed, look at Deep Blue: Deep Blue beats every human in chess, but that would be impossible if Deep Blue couldn’t do any better than any of its programmers. • Similarly, pending any mechanical gl ...
TOSHIBA PORTÉGÉ Z930/Satellite Z930 Series
... FCC information FCC notice "Declaration of Conformity Information" This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference in a resid ...
... FCC information FCC notice "Declaration of Conformity Information" This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference in a resid ...
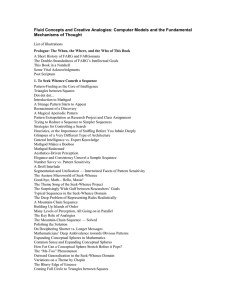
Word - Egodeath.com
... Prologue: The When, the Where, and the Who of This Book A Short History of FARG and FARGonauts The Double-Strandedness of FARG’s Intellectual Goals This Book in a Nutshell Some Vital Acknowledgments Post Scriptum 1. To Seek Whence Cometh a Sequence Pattern-Finding as the Core of Intelligence Triangl ...
... Prologue: The When, the Where, and the Who of This Book A Short History of FARG and FARGonauts The Double-Strandedness of FARG’s Intellectual Goals This Book in a Nutshell Some Vital Acknowledgments Post Scriptum 1. To Seek Whence Cometh a Sequence Pattern-Finding as the Core of Intelligence Triangl ...
Slide 1
... DSS Characteristics and Capabilities • The key characteristics and capabilities of DSS – Support for decision makers, mainly in semistructured and unstructured situations, by bringing together human judgment and computerized information – Support for all managerial levels, ranging ...
... DSS Characteristics and Capabilities • The key characteristics and capabilities of DSS – Support for decision makers, mainly in semistructured and unstructured situations, by bringing together human judgment and computerized information – Support for all managerial levels, ranging ...
PPT - 서울대 Biointelligence lab
... “Success of AI depends on creating programs that do as well as the best humans at various tasks” So to achieve human-level intelligence, we might have to build a person. ...
... “Success of AI depends on creating programs that do as well as the best humans at various tasks” So to achieve human-level intelligence, we might have to build a person. ...
умк федорович - Электронная библиотека Полоцкого
... doesn't think that Jane___4. be happy with___5. She wants her daughter to marry a younger man. One evening when Jane came home, her mother___6. for her. She came out into the hall and ___7. tears in her eyes. She said she ___8. her daughter to marry that gentleman. Jane couldn't understand. "Why?" s ...
... doesn't think that Jane___4. be happy with___5. She wants her daughter to marry a younger man. One evening when Jane came home, her mother___6. for her. She came out into the hall and ___7. tears in her eyes. She said she ___8. her daughter to marry that gentleman. Jane couldn't understand. "Why?" s ...
AI Magazine - Spring 2016
... Say?) takes a step back and focuses instead on synergy between human and machine, and the development of conjoint superhuman intelligence. While the articles included in this issue propose and discuss several kinds of tests, and we hope to see many of them being deployed very soon, they should be co ...
... Say?) takes a step back and focuses instead on synergy between human and machine, and the development of conjoint superhuman intelligence. While the articles included in this issue propose and discuss several kinds of tests, and we hope to see many of them being deployed very soon, they should be co ...
Juan_Mancilla Caceres
... these data collection methods, respondent fatigue [Porter et al., 2004] associated with survey methods and the lack of fine grained observations of the interactions (available only through other more expensive means such as observational studies) has limited the power of such studies. Therefore, it ...
... these data collection methods, respondent fatigue [Porter et al., 2004] associated with survey methods and the lack of fine grained observations of the interactions (available only through other more expensive means such as observational studies) has limited the power of such studies. Therefore, it ...
Rule Based Expert System for Medical Diagnosis-A Review
... with the desired goal, and then attempts to find evidence for proving the goal. Returning to the same example, the task to prove that D is true would be initiated by first finding a rule that proves D. Rule 4 does so, which also provides a subgoal to prove that Z is true. Now Rule 2 comes into play, ...
... with the desired goal, and then attempts to find evidence for proving the goal. Returning to the same example, the task to prove that D is true would be initiated by first finding a rule that proves D. Rule 4 does so, which also provides a subgoal to prove that Z is true. Now Rule 2 comes into play, ...
here. - Computer Science and Engineering
... Manager, Knowledge Technologies Group, Andersen Consulting, Chicago, IL, 1992 – 1995 Senior Consultant, Artificial Intelligence, Andersen Consulting, Chicago, IL, 1990 – 1992 Consultant, Artificial Intelligence Group, Andersen Consulting, Chicago, IL, 1988 – 1990 ...
... Manager, Knowledge Technologies Group, Andersen Consulting, Chicago, IL, 1992 – 1995 Senior Consultant, Artificial Intelligence, Andersen Consulting, Chicago, IL, 1990 – 1992 Consultant, Artificial Intelligence Group, Andersen Consulting, Chicago, IL, 1988 – 1990 ...
Chapter 12 - Missouri State University
... • Identification of underlying patterns, categories, and behaviors in large data sets, using techniques such as neural networks and data mining Artificial Intelligence (AI) technology: • Computer-based systems based on human behavior, with the ability to learn languages, accomplish physical tasks, u ...
... • Identification of underlying patterns, categories, and behaviors in large data sets, using techniques such as neural networks and data mining Artificial Intelligence (AI) technology: • Computer-based systems based on human behavior, with the ability to learn languages, accomplish physical tasks, u ...
Keonwook Kim - Mercer University
... Miami University, Oxford, OH Worked to establish Dept. of ECE (formally established in summer of 2004). As a founding member of a new department, I was primarily responsible for creating and revamping courses in Computer Engineering. I was also actively involved in curriculum development, policy dev ...
... Miami University, Oxford, OH Worked to establish Dept. of ECE (formally established in summer of 2004). As a founding member of a new department, I was primarily responsible for creating and revamping courses in Computer Engineering. I was also actively involved in curriculum development, policy dev ...
Chapter 11 - Barbara Hecker
... behaviors in large data sets, using techniques such as neural networks and data mining Artificial Intelligence (AI) technology: • Computer-based systems based on human behavior, with the ability to learn languages, accomplish physical tasks, use a perceptual apparatus, and emulate human expertise an ...
... behaviors in large data sets, using techniques such as neural networks and data mining Artificial Intelligence (AI) technology: • Computer-based systems based on human behavior, with the ability to learn languages, accomplish physical tasks, use a perceptual apparatus, and emulate human expertise an ...
The Next Knowledge Medium
... This article examines how AI technology could change civilization dramatically. The article is in three parts: stories, models, and predictions. The stories describe processes of cultural change that have been studied by historians and anthropologists. They provide a historical context for consideri ...
... This article examines how AI technology could change civilization dramatically. The article is in three parts: stories, models, and predictions. The stories describe processes of cultural change that have been studied by historians and anthropologists. They provide a historical context for consideri ...
How Can Expertise be Defined?
... of the main processes that are needed to accomplish the goal of the program (Adelson 1981; Jeffries et al. 1981; McKeithen et al. 1981). Experienced programmers are better able to identify bugs, especially those that can be found only after a detailed conceptual understanding of program function. Ex ...
... of the main processes that are needed to accomplish the goal of the program (Adelson 1981; Jeffries et al. 1981; McKeithen et al. 1981). Experienced programmers are better able to identify bugs, especially those that can be found only after a detailed conceptual understanding of program function. Ex ...
Intelligent Techniques for Decision Support System in Human
... decision makers to extend their capabilities but not to replace their judgment(Turban et al., 2007). In the enhancement to DSS traditional approach, advance intelligent techniques are available in designing an intelligent system application. DSS applications which are embedded with intelligent compo ...
... decision makers to extend their capabilities but not to replace their judgment(Turban et al., 2007). In the enhancement to DSS traditional approach, advance intelligent techniques are available in designing an intelligent system application. DSS applications which are embedded with intelligent compo ...
INTELLIGENT AGENT full document
... Messaging software (such a software for e-mail) has existed for some time, and is also an area where intelligent agent function is currently being used. Users today want the ability to automatically prioritise and organise their e-mail, and in the future, they would like to do even more automaticall ...
... Messaging software (such a software for e-mail) has existed for some time, and is also an area where intelligent agent function is currently being used. Users today want the ability to automatically prioritise and organise their e-mail, and in the future, they would like to do even more automaticall ...