querying description logic knowledge bases
... are instances of these concepts, and roles (also known as properties) that are interpreted as pairs of individuals that are related by the role. Operators, such as negation (¬) or conjunction (u), can be used in order to build more complicated composite concepts. As an example, consider the followin ...
... are instances of these concepts, and roles (also known as properties) that are interpreted as pairs of individuals that are related by the role. Operators, such as negation (¬) or conjunction (u), can be used in order to build more complicated composite concepts. As an example, consider the followin ...
Dowe2010_MML_Handboo.. - Clayton School
... hypothesis H, this is equivalent to choosing H to maximise P r(H) . P r(D|H). By the monotonicity of the logarithm function, this is in turn equivalent to choosing H so as to minimise − log P r(H) − log P r(D|H). From Shannon’s information theory (see sec. 2.1), this is the amount of information req ...
... hypothesis H, this is equivalent to choosing H to maximise P r(H) . P r(D|H). By the monotonicity of the logarithm function, this is in turn equivalent to choosing H so as to minimise − log P r(H) − log P r(D|H). From Shannon’s information theory (see sec. 2.1), this is the amount of information req ...
A. Breadth-First Search - NIA :: ECSU
... Artificial Intelligence was founded after World War II, after several individuals began to work on intelligent machines. It is cited that the English mathematician, Alan Turing, was the first to work with Artificial Intelligence. In 1950, he wrote an article titled “Computing Machinery and Intellige ...
... Artificial Intelligence was founded after World War II, after several individuals began to work on intelligent machines. It is cited that the English mathematician, Alan Turing, was the first to work with Artificial Intelligence. In 1950, he wrote an article titled “Computing Machinery and Intellige ...
Osmand Christian - XY Home
... different platforms. As a result, they provide different interfaces which lead to heterogeneity. As per [79], software is very diverse. Even though programs provide users with significant value, interoperability is a major problem along with heterogeneity causing problems in interoperation. Agents s ...
... different platforms. As a result, they provide different interfaces which lead to heterogeneity. As per [79], software is very diverse. Even though programs provide users with significant value, interoperability is a major problem along with heterogeneity causing problems in interoperation. Agents s ...
Toward a truly personal computer
... The files on this disk or server have been provided by ACM. Copyright and all rights therein are maintained by ACM. It is understood that all persons copying this information will adhere to the terms and constraints invoked by ACM’s copyright. These works may not be reposted without the explicit per ...
... The files on this disk or server have been provided by ACM. Copyright and all rights therein are maintained by ACM. It is understood that all persons copying this information will adhere to the terms and constraints invoked by ACM’s copyright. These works may not be reposted without the explicit per ...
CURRICULUM VITAE - University of Memphis
... http://www.memphis.edu/psychology/people/faculty/graesser.php, ...
... http://www.memphis.edu/psychology/people/faculty/graesser.php, ...
rtf - MIT Media Lab
... {\pard \ql \f0 \sa180 \li360 \fi-360 \bullet \tx360\tab {\b Constraining inference} . Inference is a combination of the reader\u8217's background knowledge and the knowledge that is explicitly in the text. To keep both reader and author \u8220"on the same page\u8221", inferences should be relevant ...
... {\pard \ql \f0 \sa180 \li360 \fi-360 \bullet \tx360\tab {\b Constraining inference} . Inference is a combination of the reader\u8217's background knowledge and the knowledge that is explicitly in the text. To keep both reader and author \u8220"on the same page\u8221", inferences should be relevant ...
Argumentation and Dialogue in Artificial Intelligence
... every y ∈ X if y defeats x then there is some z ∈ S such that z defeats y. A conflict-free set, S, is admissible if every x ∈ S is acceptable to S. Finally, S, is a preferred extension if it is a maximal (with respect to set containment) admissible set. Any preference relation P ref induces a standa ...
... every y ∈ X if y defeats x then there is some z ∈ S such that z defeats y. A conflict-free set, S, is admissible if every x ∈ S is acceptable to S. Finally, S, is a preferred extension if it is a maximal (with respect to set containment) admissible set. Any preference relation P ref induces a standa ...
Bibliography on Knowledge Management
... Huang, K-T. (1997); Capitalizing collective knowledge for winning execution and teamwork, Journal of Knowledge Management, Vol. 1, No. 2, 1997, p149-156. Huang, K-T. (1998); Capitalizing on intellectual assets, IBM Systems Journal, Vol. 37, No. 4, 1998, p570-83. Husema, R.C. and Goodman, J.P. (1998) ...
... Huang, K-T. (1997); Capitalizing collective knowledge for winning execution and teamwork, Journal of Knowledge Management, Vol. 1, No. 2, 1997, p149-156. Huang, K-T. (1998); Capitalizing on intellectual assets, IBM Systems Journal, Vol. 37, No. 4, 1998, p570-83. Husema, R.C. and Goodman, J.P. (1998) ...
PhD Thesis
... Embodied pedagogical agents – visually represented, computer generated characters in pedagogical roles, such as virtual instructors, mentors and learning companions – populate the digital society in increasing numbers. They are found in educational programmes from preschool to university, as well as ...
... Embodied pedagogical agents – visually represented, computer generated characters in pedagogical roles, such as virtual instructors, mentors and learning companions – populate the digital society in increasing numbers. They are found in educational programmes from preschool to university, as well as ...
The Promise of Artificial Intelligence - IEEE
... Deep-learning techniques allow a computer system to connect the dots from many different areas of knowledge, similar to how the human brain works, to make the best decision possible. Facebook, Google, Microsoft, ...
... Deep-learning techniques allow a computer system to connect the dots from many different areas of knowledge, similar to how the human brain works, to make the best decision possible. Facebook, Google, Microsoft, ...
SETI Aff UM 7wk - Open Evidence Archive
... 670,000. Drake himself estimates a more conservative 10,000. But even if that lower value turns out to be correct, at the rate they're going, it wouldn't take scientists too long to discover an alien signal, Shostak said. "This range, from Sagan's million down to 10,000 that's the range of estimates ...
... 670,000. Drake himself estimates a more conservative 10,000. But even if that lower value turns out to be correct, at the rate they're going, it wouldn't take scientists too long to discover an alien signal, Shostak said. "This range, from Sagan's million down to 10,000 that's the range of estimates ...
Intelligence by Design - Department of Computer Science
... the extent to which this dissertation is just an expansion on it, despite the conspicuous differences. I’ve never met him, but Toby Tyrrell did an amazing piece of work for his PhD, and I’m deeply indebted to him not only for his research, but for making his code publicly available through internet ...
... the extent to which this dissertation is just an expansion on it, despite the conspicuous differences. I’ve never met him, but Toby Tyrrell did an amazing piece of work for his PhD, and I’m deeply indebted to him not only for his research, but for making his code publicly available through internet ...
Intelligence by Design: Principles of Modularity and Coordination for
... project that I started thinking about specialized learning. I reread that paper a month ago, and I’m amazed the extent to which this dissertation is just an expansion of it, despite the conspicuous differences. I’ve never met him, but Toby Tyrrell did an amazing piece of work for his PhD. I have a d ...
... project that I started thinking about specialized learning. I reread that paper a month ago, and I’m amazed the extent to which this dissertation is just an expansion of it, despite the conspicuous differences. I’ve never met him, but Toby Tyrrell did an amazing piece of work for his PhD. I have a d ...
Biologically Inspired Modular Neural Networks
... Introduction Artificial intelligence is the study of intelligent behavior and how computer programs can be made to exhibit such behavior. There are two categories of artificial intelligence from the computational point of view. One is based on symbolism, and the other is based on connectionism. In t ...
... Introduction Artificial intelligence is the study of intelligent behavior and how computer programs can be made to exhibit such behavior. There are two categories of artificial intelligence from the computational point of view. One is based on symbolism, and the other is based on connectionism. In t ...
Wikibook (pages 1-223)
... In artificial intelligence, an evolutionary algorithm (EA) is a subset of evolutionary computation, a generic population-based metaheuristic optimization algorithm. An EA uses some mechanisms inspired by biological evolution: reproduction, mutation, recombination, and selection. Candidate solutions ...
... In artificial intelligence, an evolutionary algorithm (EA) is a subset of evolutionary computation, a generic population-based metaheuristic optimization algorithm. An EA uses some mechanisms inspired by biological evolution: reproduction, mutation, recombination, and selection. Candidate solutions ...
On a razor`s edge: evaluating arguments from expert opinion
... knowledge that the person who is claimed to be an expert has in that subject. But a dubious aspect of it from an argumentation point of view is that it differentiates between experts and nonexperts on the basis of the number of propositions known by the person who is claimed to be an expert, resting ...
... knowledge that the person who is claimed to be an expert has in that subject. But a dubious aspect of it from an argumentation point of view is that it differentiates between experts and nonexperts on the basis of the number of propositions known by the person who is claimed to be an expert, resting ...
Computer Science (MS)
... server and client side technologies. The course is targeted at students who are interested in the development of application programs using a database system such as Oracle, or Microsoft SQL. Prerequisite: CSCI 6302 or equivalent. CSCI 6316: Design for Information Technology Systems ...
... server and client side technologies. The course is targeted at students who are interested in the development of application programs using a database system such as Oracle, or Microsoft SQL. Prerequisite: CSCI 6302 or equivalent. CSCI 6316: Design for Information Technology Systems ...
You can this announcement in pdf format.
... a result, AI technologies are often in the news and a number of organizations (including the U.S. government) are trying to ensure that AI technologies are being used for the maximum benefit of society. As with all potentially transformative technologies (such as the automobile and the transistor ...
... a result, AI technologies are often in the news and a number of organizations (including the U.S. government) are trying to ensure that AI technologies are being used for the maximum benefit of society. As with all potentially transformative technologies (such as the automobile and the transistor ...
Man, machine, and strategy
... challenges such as predicting credit or insurance risk, for instance – is valuable drudgery, not revolution. Products that are marketed as being able to cope with ‘raw data’ turn out to have their own definitions of ‘raw’. We have tried several of the more visibly marketed analytic tools currently o ...
... challenges such as predicting credit or insurance risk, for instance – is valuable drudgery, not revolution. Products that are marketed as being able to cope with ‘raw data’ turn out to have their own definitions of ‘raw’. We have tried several of the more visibly marketed analytic tools currently o ...
The Hanson-Yudkowsky AI-Foom Debate
... push a set of tools through a mutual-improvement process; their team would improve those tools, and then use those improved versions to improve them further, and so on through a rapid burst until they were in a position to basically “take over the world.” I asked what it would take to convince you t ...
... push a set of tools through a mutual-improvement process; their team would improve those tools, and then use those improved versions to improve them further, and so on through a rapid burst until they were in a position to basically “take over the world.” I asked what it would take to convince you t ...
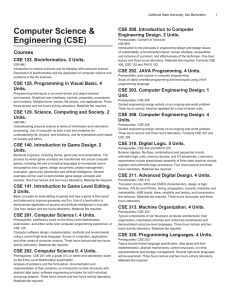
PDF of this page
... process by which game concepts are transformed into actual computer games, including the use of scripting languages to incorporate sound and graphics into a game, design documents, project management, evaluation, game play parameters and artificial intelligence. Several examples will be used to demo ...
... process by which game concepts are transformed into actual computer games, including the use of scripting languages to incorporate sound and graphics into a game, design documents, project management, evaluation, game play parameters and artificial intelligence. Several examples will be used to demo ...