A Practical Introduction to Data Structures and Algorithm Analysis
... Inheritance, a key feature of object-oriented programming, is used only sparingly in the code examples. Inheritance is an important tool that helps programmers avoid duplication, and thus minimize bugs. From a pedagogical standpoint, however, inheritance often makes code examples harder to understan ...
... Inheritance, a key feature of object-oriented programming, is used only sparingly in the code examples. Inheritance is an important tool that helps programmers avoid duplication, and thus minimize bugs. From a pedagogical standpoint, however, inheritance often makes code examples harder to understan ...
Internet of Things (IoT) in 5 days
... welcome! Please engage visiting IoT in five days GitHub repository The book has been developed in asciidoc, and it can be compiled from its sources to produce HTML, PDF, eBook and others formats. The following are the authors who contributed to this book: Antonio Liñán defines himself as "an enginee ...
... welcome! Please engage visiting IoT in five days GitHub repository The book has been developed in asciidoc, and it can be compiled from its sources to produce HTML, PDF, eBook and others formats. The following are the authors who contributed to this book: Antonio Liñán defines himself as "an enginee ...
Survey of Cyber Moving Targets Lincoln Laboratory Technical Report 1166
... defend a system and increase the complexity of cyber attacks by making the system less homogeneous, less static, and less deterministic [1]. In this survey, we describe the technical details of each technique, identify the proper threat model associated with the technique, and identify its implement ...
... defend a system and increase the complexity of cyber attacks by making the system less homogeneous, less static, and less deterministic [1]. In this survey, we describe the technical details of each technique, identify the proper threat model associated with the technique, and identify its implement ...
Clustered Objects - Computer Science
... sharing on OS resources, thus limiting scalability. We contend that in order to ensure the remaining sharing does not limit our performance, we must use distribution, partitioning and replication to remove sharing in the common paths. Using distributed implementations for key virtual memory objects, ...
... sharing on OS resources, thus limiting scalability. We contend that in order to ensure the remaining sharing does not limit our performance, we must use distribution, partitioning and replication to remove sharing in the common paths. Using distributed implementations for key virtual memory objects, ...
Full book - NATO Cooperative Cyber Defence Centre of Excellence
... or even years, sometimes even with the help of insiders. The traditional cyber security methods, mostly passive, perimeter-bound and reactive are not conceptually and technologically wellequipped to challenge APT. The commonly used term for ACD is the one given in the 2011 US Department of Defense, ...
... or even years, sometimes even with the help of insiders. The traditional cyber security methods, mostly passive, perimeter-bound and reactive are not conceptually and technologically wellequipped to challenge APT. The commonly used term for ACD is the one given in the 2011 US Department of Defense, ...
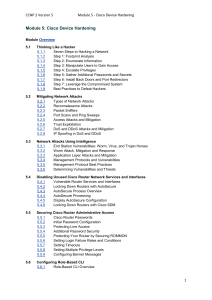
CCNP 2 Version 5 Module 5 - Cisco Device Hardening Module 5
... By following some simple advice, network administrators can make footprinting more difficult. Figure outlines the process detailed below. Hackers can build a complete profile or “footprint” of the company security posture. Using a range of tools and techniques, an attacker can discover the company d ...
... By following some simple advice, network administrators can make footprinting more difficult. Figure outlines the process detailed below. Hackers can build a complete profile or “footprint” of the company security posture. Using a range of tools and techniques, an attacker can discover the company d ...
PDF hosted at the Radboud Repository of the Radboud University
... Traditionally, voting in such elections, e.g. for president or parliamentary representatives, has been done by paper ballots. Even longer ago, oral voting by stating the name of the preferred candidate was practised. In the second half of the twentieth century, the era in which the computer was tran ...
... Traditionally, voting in such elections, e.g. for president or parliamentary representatives, has been done by paper ballots. Even longer ago, oral voting by stating the name of the preferred candidate was practised. In the second half of the twentieth century, the era in which the computer was tran ...
Information Security Manual Approval Date: 7/23/14
... Guidance for Colleges While this Manual is based on the foundation of the State of North Carolina Information Security Manual simply adopting these standards will not provide a comprehensive security program. College management should emphasize the importance of information security throughout their ...
... Guidance for Colleges While this Manual is based on the foundation of the State of North Carolina Information Security Manual simply adopting these standards will not provide a comprehensive security program. College management should emphasize the importance of information security throughout their ...
5th International Conference on Cyber Conflict Proceedings
... or even years, sometimes even with the help of insiders. The traditional cyber security methods, mostly passive, perimeter-bound and reactive are not conceptually and technologically wellequipped to challenge APT. The commonly used term for ACD is the one given in the 2011 US Department of Defense, ...
... or even years, sometimes even with the help of insiders. The traditional cyber security methods, mostly passive, perimeter-bound and reactive are not conceptually and technologically wellequipped to challenge APT. The commonly used term for ACD is the one given in the 2011 US Department of Defense, ...
High Availability Cluster User Guide 4.0.3
... The primary benefit of HA Cluster is to detect storage system failures and transfer ownership of the shared volumes to the alternate NexentaStor appliance. All configured volume services failover to the other server. HA Cluster ensures service continuity during exceptional events, including power ou ...
... The primary benefit of HA Cluster is to detect storage system failures and transfer ownership of the shared volumes to the alternate NexentaStor appliance. All configured volume services failover to the other server. HA Cluster ensures service continuity during exceptional events, including power ou ...
Security Enhanced (SE) Android: Bringing Flexible
... inability to confine any system daemons or setuid programs that run with the root or superuser identity. Security Enhanced Linux (SELinux) was originally developed as a Mandatory Access Control (MAC) mechanism for Linux to demonstrate how to overcome the shortcomings of DAC [28]. Although SELinux ha ...
... inability to confine any system daemons or setuid programs that run with the root or superuser identity. Security Enhanced Linux (SELinux) was originally developed as a Mandatory Access Control (MAC) mechanism for Linux to demonstrate how to overcome the shortcomings of DAC [28]. Although SELinux ha ...
Dr.Halil ADAHAN NEAR EAST UNIVERSITY Faculty of
... When the users log on to their computers, the application installs. You publish an application to users when you want the application to be available to the users who are managed by your Group Policy object. These users then determine when to install the application. ...
... When the users log on to their computers, the application installs. You publish an application to users when you want the application to be available to the users who are managed by your Group Policy object. These users then determine when to install the application. ...
Security Warrior
... These are some of the topics we cover. Although some parts will necessarily be review for more advanced users, we also cover unique topics that might gratify even seasoned veterans. To give one example, we cover reverse code engineering (RCE), including the esoteric subjects of Linux and embedded RC ...
... These are some of the topics we cover. Although some parts will necessarily be review for more advanced users, we also cover unique topics that might gratify even seasoned veterans. To give one example, we cover reverse code engineering (RCE), including the esoteric subjects of Linux and embedded RC ...
Web Application Architecture Guide
... When designing a Web application, the goals of a software architect are to minimize the complexity by separating tasks into different areas of concern while designing a secure and high performance application. When designing Web application, consider following guidelines: • Partition your applicatio ...
... When designing a Web application, the goals of a software architect are to minimize the complexity by separating tasks into different areas of concern while designing a secure and high performance application. When designing Web application, consider following guidelines: • Partition your applicatio ...
Chapter 3. Summary of Linux and Unix Security
... A wise man attacks the city of the mighty and pulls down the stronghold in which they trust. Proverbs 21:22 (NIV) This book describes a set of guidelines for writing secure programs on Linux and Unix systems. For purposes of this book, a ``secure program'' is a program that sits on a security bounda ...
... A wise man attacks the city of the mighty and pulls down the stronghold in which they trust. Proverbs 21:22 (NIV) This book describes a set of guidelines for writing secure programs on Linux and Unix systems. For purposes of this book, a ``secure program'' is a program that sits on a security bounda ...
Advanced Information Assurance Handbook
... External use. Requests for permission to reproduce this document or prepare derivative works of this document for external and commercial use should be addressed to the SEI Licensing Agent. This work was created in the performance of Federal Government Contract Number F19628-00-C-0003 with Carnegie ...
... External use. Requests for permission to reproduce this document or prepare derivative works of this document for external and commercial use should be addressed to the SEI Licensing Agent. This work was created in the performance of Federal Government Contract Number F19628-00-C-0003 with Carnegie ...
reducing communication cost in scalable shared memory systems
... instrumented application pipes a detailed trace to configuration independent (CIAT) and configuration dependent (CDAT) analysis tools. CIAT characterizes inherent application characteristics that do not change from one configuration to another, including working sets, concurrency, sharing behavior, ...
... instrumented application pipes a detailed trace to configuration independent (CIAT) and configuration dependent (CDAT) analysis tools. CIAT characterizes inherent application characteristics that do not change from one configuration to another, including working sets, concurrency, sharing behavior, ...
D5.1 Survey of Middleware for Networked Embedded
... network topology and the available network resources as they can change rapidly; temporary and unannounced loss of network connectivity happens frequently when mobile nodes move; hosts must be discovered in an ad-hoc manner; nodes are likely to have scarce resources, such as low battery power, slow ...
... network topology and the available network resources as they can change rapidly; temporary and unannounced loss of network connectivity happens frequently when mobile nodes move; hosts must be discovered in an ad-hoc manner; nodes are likely to have scarce resources, such as low battery power, slow ...