Technical Reference Model for the Government Procurement
... Procurement Related to Information Systems,” effective from July 2007 (agreed at the Liaison Conference of Chief Information Officers (CIO) of Ministries and Agencies, hereinafter referred to as the Procurement Guidelines), could, in some cases, create problems due to the lack of interoperability of ...
... Procurement Related to Information Systems,” effective from July 2007 (agreed at the Liaison Conference of Chief Information Officers (CIO) of Ministries and Agencies, hereinafter referred to as the Procurement Guidelines), could, in some cases, create problems due to the lack of interoperability of ...
IBM Security Access Manager for Web Version 7.0: Auditing Guide
... Chapter 4. Globalization . . . . . . . 17 Language support overview . . . . . . . . . Installing language support packages . . . . . . Uninstalling language support packages . . . . . Locale environment variables . . . . . . . . LANG variable on AIX, Linux, or Solaris systems LANG variable on Window ...
... Chapter 4. Globalization . . . . . . . 17 Language support overview . . . . . . . . . Installing language support packages . . . . . . Uninstalling language support packages . . . . . Locale environment variables . . . . . . . . LANG variable on AIX, Linux, or Solaris systems LANG variable on Window ...
JDK 1.4 Tutorial (Manning).
... code. Java, on the other hand, almost never gave me a headache. On the contrary—it was eerily fun. We heard that the designers (James Gosling and his team) had used a simple design rule: if you don’t know how to do something really nicely, leave it out. What an excellent rule! Play to your strengths ...
... code. Java, on the other hand, almost never gave me a headache. On the contrary—it was eerily fun. We heard that the designers (James Gosling and his team) had used a simple design rule: if you don’t know how to do something really nicely, leave it out. What an excellent rule! Play to your strengths ...
Using a Graphical User Interface
... services such as DHCP and DNS. It can take a more active part in object management, such as when used as an Active Directory domain controller. It can also serve as a personal operating system since it is so closely tied to its brother, Windows XP. In this role it might provide security of local dat ...
... services such as DHCP and DNS. It can take a more active part in object management, such as when used as an Active Directory domain controller. It can also serve as a personal operating system since it is so closely tied to its brother, Windows XP. In this role it might provide security of local dat ...
Cisco SAFE Reference Guide
... He is a network security expert with over 17 years of experience in the networking industry. He obtained his CCIE certification in 1996 and CISSP in 2004. Martin joined Cisco in 1998 and has held a variety of technical positions. Started as a Customer Support Engineer in Cisco’s Technical Assistance ...
... He is a network security expert with over 17 years of experience in the networking industry. He obtained his CCIE certification in 1996 and CISSP in 2004. Martin joined Cisco in 1998 and has held a variety of technical positions. Started as a Customer Support Engineer in Cisco’s Technical Assistance ...
Document
... Chapter 6. Quality of Service . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6.1 QoS definition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6.1.1 Differentiated Services . . . . . . . . . . . ...
... Chapter 6. Quality of Service . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6.1 QoS definition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6.1.1 Differentiated Services . . . . . . . . . . . ...
Scene of the Cybercrime - Computer Forensics Handbook (Syngress).
... enjoyed even more—and it was easier on the body and paid better, to boot. I’d been a computer hobbyist for a long time (my old VIC-20 and Commodore 64 are still here on a high shelf in the closet) and after meeting my husband online, together we set up our home network and studied together to become ...
... enjoyed even more—and it was easier on the body and paid better, to boot. I’d been a computer hobbyist for a long time (my old VIC-20 and Commodore 64 are still here on a high shelf in the closet) and after meeting my husband online, together we set up our home network and studied together to become ...
SUSE Linux Enterprise Desktop www.suse.com
... This manual introduces the basic concepts of system security on SUSE Linux Enterprise Desktop. It covers extensive documentation about the authentication mechanisms available on Linux, such as NIS or LDAP. It also deals with aspects of local security like access control lists, encryption and intrusi ...
... This manual introduces the basic concepts of system security on SUSE Linux Enterprise Desktop. It covers extensive documentation about the authentication mechanisms available on Linux, such as NIS or LDAP. It also deals with aspects of local security like access control lists, encryption and intrusi ...
Amazon Web Services: Overview of Security Processes
... security responsibilities become shared between you and your cloud service provider. In this case, AWS is responsible for securing the underlying infrastructure that supports the cloud, and you’re responsible for anything you put on the cloud or connect to the cloud. This shared security responsibil ...
... security responsibilities become shared between you and your cloud service provider. In this case, AWS is responsible for securing the underlying infrastructure that supports the cloud, and you’re responsible for anything you put on the cloud or connect to the cloud. This shared security responsibil ...
AWS Overview of Security Processes
... relating to that content as part of the AWS “shared responsibility” model. This shared responsibility model is fundamental to understanding the respective roles of the customer and AWS in the context of the Cloud Security Principles. Under the shared responsibility model, AWS operates, manages, and ...
... relating to that content as part of the AWS “shared responsibility” model. This shared responsibility model is fundamental to understanding the respective roles of the customer and AWS in the context of the Cloud Security Principles. Under the shared responsibility model, AWS operates, manages, and ...
Integrating a Real-Time Model in Configurable Middleware for Distributed Systems
... Common interaction models for distributed systems .................................. 3 Basic services provided by distribution middleware ................................. 10 Modelling applications according to the end-to-end flow model.............. 13 End-to-end flow model proposed by MARTE standa ...
... Common interaction models for distributed systems .................................. 3 Basic services provided by distribution middleware ................................. 10 Modelling applications according to the end-to-end flow model.............. 13 End-to-end flow model proposed by MARTE standa ...
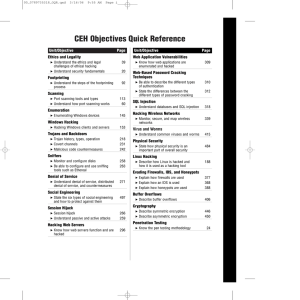
Review Questions
... network concepts and issues, computer hardware and operating systems, and applications will come in handy when you read this book. While every attempt has been made to present the concepts and exercises in an easy-to-understand format, you will need to have experience with IT and networking technolo ...
... network concepts and issues, computer hardware and operating systems, and applications will come in handy when you read this book. While every attempt has been made to present the concepts and exercises in an easy-to-understand format, you will need to have experience with IT and networking technolo ...
Bitdefender GravityZone Administrator`s Guide
... All rights reserved. No part of this book may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage and retrieval system, without written permission from an authorized representative of Bitdefender. The in ...
... All rights reserved. No part of this book may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage and retrieval system, without written permission from an authorized representative of Bitdefender. The in ...
Reference - Network Security Administrator/Specialist
... into underlying concepts such as packet fragmentation, overflow attacks, and operating system fingerprinting. You likewise want more on forensics, honeypots, and the psychological basis of social engineering. You also enjoy novel challenges such as implementing Bayesian intrusion detection and defen ...
... into underlying concepts such as packet fragmentation, overflow attacks, and operating system fingerprinting. You likewise want more on forensics, honeypots, and the psychological basis of social engineering. You also enjoy novel challenges such as implementing Bayesian intrusion detection and defen ...
UIA: A Global Connectivity Architecture for Mobile - PDOS-MIT
... The Internet’s architecture, designed in the days of large, stationary computers tended by technically savvy and accountable administrators, fails to meet the demands of the emerging ubiquitous computing era. Nontechnical users now routinely own multiple personal devices, many of them mobile, and ne ...
... The Internet’s architecture, designed in the days of large, stationary computers tended by technically savvy and accountable administrators, fails to meet the demands of the emerging ubiquitous computing era. Nontechnical users now routinely own multiple personal devices, many of them mobile, and ne ...
International Technical Support Organization June 1996 How to Secure
... This redbook describes how to create a secure implementation of the Internet Connection Server for MVS/ESA. It focuses on the Web server side of the World Wide Web. The implementation is based on the OS/390 Internet BonusPak. This document describes the basic server security, which is provided throu ...
... This redbook describes how to create a secure implementation of the Internet Connection Server for MVS/ESA. It focuses on the Web server side of the World Wide Web. The implementation is based on the OS/390 Internet BonusPak. This document describes the basic server security, which is provided throu ...
Firewall and SmartDefense
... All rights reserved. This product and related documentation are protected by copyright and distributed under licensing restricting their use, copying, distribution, and decompilation. No part of this product or related documentation may be reproduced in any form or by any means without prior written ...
... All rights reserved. This product and related documentation are protected by copyright and distributed under licensing restricting their use, copying, distribution, and decompilation. No part of this product or related documentation may be reproduced in any form or by any means without prior written ...
IIS Security and Programming Countermeasures
... fixes are not just new features that you might like to have and may choose to pay for, they are the first attempt Microsoft has ever made to create a product that is safe to use and free from severe defects. That Microsoft has failed yet again to achieve a reasonable level of safety for its products ...
... fixes are not just new features that you might like to have and may choose to pay for, they are the first attempt Microsoft has ever made to create a product that is safe to use and free from severe defects. That Microsoft has failed yet again to achieve a reasonable level of safety for its products ...
Root - Near East University
... Many research centers and University Campuses require using advanced level of Network functionality, management, design and structure. There are many factors that need to be considered in organization of Network Management. In my project I have mentioned about the Network management structures that ...
... Many research centers and University Campuses require using advanced level of Network functionality, management, design and structure. There are many factors that need to be considered in organization of Network Management. In my project I have mentioned about the Network management structures that ...
to the most recent version of this document
... Click here to download the most recent version of this document ...
... Click here to download the most recent version of this document ...
Internet-Based Workflow Management
... the network. Applications will demand permanent access to shared as well as private data. Storing private data on a laptop connected intermittently to the network limits access to that data; thus, a persistent storage service would be one of several societal services provided in this globally-shared ...
... the network. Applications will demand permanent access to shared as well as private data. Storing private data on a laptop connected intermittently to the network limits access to that data; thus, a persistent storage service would be one of several societal services provided in this globally-shared ...