TCP/IP
... The cost of providing a reliable service is more overhead in connection setup and closedown, processing power for correcting errors and data transmission, but some applications need reliability irrespective of cost. – UDP just extends IP’s connectionless datagram service to applications that do not ...
... The cost of providing a reliable service is more overhead in connection setup and closedown, processing power for correcting errors and data transmission, but some applications need reliability irrespective of cost. – UDP just extends IP’s connectionless datagram service to applications that do not ...
(1.8 MB)
... • When the LAN control is enabled, serial RS-232C commands may not be transmitted. • You can’t control the LAN/serial RS-232C commands for about 10 seconds after turning on the main power of the projector. • When commands for LAN control and for RS-232C control are issued at the same time, the LA ...
... • When the LAN control is enabled, serial RS-232C commands may not be transmitted. • You can’t control the LAN/serial RS-232C commands for about 10 seconds after turning on the main power of the projector. • When commands for LAN control and for RS-232C control are issued at the same time, the LA ...
Arch Rock
... • IP has always done “multi-hop” – Routers connect sub-networks to one another – The sub-networks may be the same or different physical links ...
... • IP has always done “multi-hop” – Routers connect sub-networks to one another – The sub-networks may be the same or different physical links ...
Data Sheet
... support Modbus over EIA-232, EIA-485(optionally) and over TCP/IP. The gateway polls the modbus objects at a configurable rate. Values can be read or written by BACnet clients and by the Web Interface using the browser. BACnet clients can requests COV. ...
... support Modbus over EIA-232, EIA-485(optionally) and over TCP/IP. The gateway polls the modbus objects at a configurable rate. Values can be read or written by BACnet clients and by the Web Interface using the browser. BACnet clients can requests COV. ...
BOOTP and DHCP
... Bootstrap Protocol (BOOTP): • BOOTP (Bootstrap Protocol): – Is a protocol that allows a diskless workstation to determine it’s IP address (and other information) without using RARP. • BOOTP is a client / server program where a BOOTP agent requests bootstrap information from designated BOOTP servers ...
... Bootstrap Protocol (BOOTP): • BOOTP (Bootstrap Protocol): – Is a protocol that allows a diskless workstation to determine it’s IP address (and other information) without using RARP. • BOOTP is a client / server program where a BOOTP agent requests bootstrap information from designated BOOTP servers ...
Connecting UniOP to Modbus/TCP
... UniOP identifies Modbus/TCP devices using their IP addresses. You should take note of these addresses as you assign them because you will need them later in the set-up phase of the user interface application. Different physical media, gateways, routers and hubs can be used in the communication netwo ...
... UniOP identifies Modbus/TCP devices using their IP addresses. You should take note of these addresses as you assign them because you will need them later in the set-up phase of the user interface application. Different physical media, gateways, routers and hubs can be used in the communication netwo ...
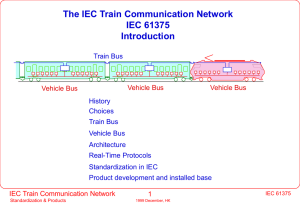
TCN Introduction
... autonumbering of nodes (inauguration) and self-configuration failure recovery over two independent lines fritting to overcome oxidation of contacts long transmission distance without repeater (860 m ) over bad quality cables (jumpers, connectors, discontinuities) operation without previous commissio ...
... autonumbering of nodes (inauguration) and self-configuration failure recovery over two independent lines fritting to overcome oxidation of contacts long transmission distance without repeater (860 m ) over bad quality cables (jumpers, connectors, discontinuities) operation without previous commissio ...
A Model for Naming, Addressing, and Routing
... Hop-by-hop routing: Only the next portion of the route is determined at each step. That is, the mapping of the destination name into a list of names is not performed once by a single entity; each entity along the route determines only the next element. To be complete, one should add the definition o ...
... Hop-by-hop routing: Only the next portion of the route is determined at each step. That is, the mapping of the destination name into a list of names is not performed once by a single entity; each entity along the route determines only the next element. To be complete, one should add the definition o ...
No Slide Title - IEEE-SA
... LOCKED since 2.5 hours. Last user: Pertti. See use history. Brought to you by www.securihome.com at 10:23 27-Feb 2000. ...
... LOCKED since 2.5 hours. Last user: Pertti. See use history. Brought to you by www.securihome.com at 10:23 27-Feb 2000. ...
More on IP and Packet Forwarding
... Error Reporting (ICMP) and traceroute Internet Control Message Protocol: – Used by a router/end-host to report some types of error: – E.g. Destination Unreachable: packet can’t be forwarded to/towards its destination. – E.g. Time Exceeded: TTL reached zero, or fragment didn’t arrive in time. Tracero ...
... Error Reporting (ICMP) and traceroute Internet Control Message Protocol: – Used by a router/end-host to report some types of error: – E.g. Destination Unreachable: packet can’t be forwarded to/towards its destination. – E.g. Time Exceeded: TTL reached zero, or fragment didn’t arrive in time. Tracero ...
PowerPoint - DePaul University
... What is the least number of CIDR announcements that can be made for this ISP? ...
... What is the least number of CIDR announcements that can be made for this ISP? ...
3.5 Reverse Address Resolution Protocol (RARP) 3.5.1 RARP concept
... It is incremented by a router that relays the request to another server and is used to identify loops. RFC 951 suggests that a value of 3 indicates a loop. • Transaction ID: A random number used to match this boot request with the response it generates. • Seconds: Set by the client. It is the elaps ...
... It is incremented by a router that relays the request to another server and is used to identify loops. RFC 951 suggests that a value of 3 indicates a loop. • Transaction ID: A random number used to match this boot request with the response it generates. • Seconds: Set by the client. It is the elaps ...
CISCO IOS NETWORK ADDRESS TRANSLATION
... Copyright 2004 Cisco Systems, Inc. All rights reserved. Cisco, Cisco Systems, and the Cisco Systems logo are registered trademarks of Cisco Systems, Inc. and/or its affiliates in the United States and certain other countries. All other trademarks mentioned in this document or Web site are the proper ...
... Copyright 2004 Cisco Systems, Inc. All rights reserved. Cisco, Cisco Systems, and the Cisco Systems logo are registered trademarks of Cisco Systems, Inc. and/or its affiliates in the United States and certain other countries. All other trademarks mentioned in this document or Web site are the proper ...
01_NF_Ch09
... All network devices that have messages to send must listen before transmitting. If a device detects a signal from another device, it will wait for a specified amount of time before attempting to transmit. While this transmission is occurring, the device continues to listen for traffic or collisions ...
... All network devices that have messages to send must listen before transmitting. If a device detects a signal from another device, it will wait for a specified amount of time before attempting to transmit. While this transmission is occurring, the device continues to listen for traffic or collisions ...
Dynamic addressing
... to store in every host • One solution is to store the entire host file in a single computer and allow access to this centralized info to every PC that needs a mapping – but this would create a huge amount of traffic • Another solution is to divide this huge amount of info into smaller parts and stor ...
... to store in every host • One solution is to store the entire host file in a single computer and allow access to this centralized info to every PC that needs a mapping – but this would create a huge amount of traffic • Another solution is to divide this huge amount of info into smaller parts and stor ...
ECE544 - WINLAB
... – The Transport Layer is the lowest Layer in the network stack that is an end-to-end protocol ...
... – The Transport Layer is the lowest Layer in the network stack that is an end-to-end protocol ...
Internet 2
... MS registers with an SGSN (authentication...) Location updates are now possible PDP context is created MS is assigned PDP (IP) address Packet transmission can take place GPRS detach PDP context is terminated Allocated IP address is released ...
... MS registers with an SGSN (authentication...) Location updates are now possible PDP context is created MS is assigned PDP (IP) address Packet transmission can take place GPRS detach PDP context is terminated Allocated IP address is released ...
LAN Control Utility User Manual - Mitsubishi Electric Corporation
... • When the LAN control is enabled, serial RS-232C commands may not be transmitted. • You can’t control the LAN/serial RS-232C commands for about 10 seconds after turning on the main power of the projector. • When commands for LAN control and for RS-232C control are issued at the same time, the LAN c ...
... • When the LAN control is enabled, serial RS-232C commands may not be transmitted. • You can’t control the LAN/serial RS-232C commands for about 10 seconds after turning on the main power of the projector. • When commands for LAN control and for RS-232C control are issued at the same time, the LAN c ...
Ethernet frames - La Salle University
... Higher level • At a higher level (layer), a computer on a TCP/IP network is identified by an IP address, so there must be a correspondence between IP addresses (software) and MAC addresses (hardware) • The correspondence is not permanent allowing one to change one’s hardware (and thus hardware or M ...
... Higher level • At a higher level (layer), a computer on a TCP/IP network is identified by an IP address, so there must be a correspondence between IP addresses (software) and MAC addresses (hardware) • The correspondence is not permanent allowing one to change one’s hardware (and thus hardware or M ...
MANETconf: Configuration of Hosts in a Mobile Ad Hoc Network.
... 2. It uses the 169.254/16 IP address block. However, as stated in [10], this address block is registered with IANA for link-local unique addressing. Any router receiving a packet with an address from this block in the source or destination field(s) should discard the packet. So, even after nodes are ...
... 2. It uses the 169.254/16 IP address block. However, as stated in [10], this address block is registered with IANA for link-local unique addressing. Any router receiving a packet with an address from this block in the source or destination field(s) should discard the packet. So, even after nodes are ...
00197r3P802-15_TG3-LCW-HRWPAN-PHY-MAC
... • Initiating Slave sends Reassociation frame to desired recipient Slave • Recipient verifies the common Master, sends Reassociation response • Peer to Peer link is active until either party requests Disassociation Submission ...
... • Initiating Slave sends Reassociation frame to desired recipient Slave • Recipient verifies the common Master, sends Reassociation response • Peer to Peer link is active until either party requests Disassociation Submission ...
The Internet and Its Uses - Universitas Sebelas Maret
... Unicast packets use the host address of the destination device as the destination address and can be routed through an internetwork. –Broadcast and multicast, however, use special addresses as the destination address. –Broadcasts are generally restricted to the local network. –Multicast traffic ma ...
... Unicast packets use the host address of the destination device as the destination address and can be routed through an internetwork. –Broadcast and multicast, however, use special addresses as the destination address. –Broadcasts are generally restricted to the local network. –Multicast traffic ma ...
BootP and DHCP
... In the picture above you see the BOOTP message format. One line is 4 bytes long. Note the 64-octet vendor specific area at the bottom of the frame. This space can be used for various additional messages and will be extended by DHCP. In the middle part (red) the most important information is carried, ...
... In the picture above you see the BOOTP message format. One line is 4 bytes long. Note the 64-octet vendor specific area at the bottom of the frame. This space can be used for various additional messages and will be extended by DHCP. In the middle part (red) the most important information is carried, ...
I²C
I²C (Inter-Integrated Circuit), pronounced I-squared-C, is a multi-master, multi-slave, single-ended, serial computer bus invented by Philips Semiconductor (now NXP Semiconductors). It is typically used for attaching lower-speed peripheral ICs to processors and microcontrollers. Alternatively I²C is spelled I2C (pronounced I-two-C) or IIC (pronounced I-I-C). Since October 10, 2006, no licensing fees are required to implement the I²C protocol. However, fees are still required to obtain I²C slave addresses allocated by NXP.Several competitors, such as Siemens AG (later Infineon Technologies AG, now Intel mobile communications), NEC, Texas Instruments, STMicroelectronics (formerly SGS-Thomson), Motorola (later Freescale), and Intersil, have introduced compatible I²C products to the market since the mid-1990s.SMBus, defined by Intel in 1995, is a subset of I²C that defines the protocols more strictly. One purpose of SMBus is to promote robustness and interoperability. Accordingly, modern I²C systems incorporate policies and rules from SMBus, sometimes supporting both I²C and SMBus, requiring only minimal reconfiguration.