Document
... Unlike wireless LAN, directional antenna is used, users are divided into sections that do not interfere with each other. Since signal falls off sharply in the millimeter bands, different modulation schemes are used at different distances. At typical 25 MHz spectrum, closer users get 150 Mbps, distan ...
... Unlike wireless LAN, directional antenna is used, users are divided into sections that do not interfere with each other. Since signal falls off sharply in the millimeter bands, different modulation schemes are used at different distances. At typical 25 MHz spectrum, closer users get 150 Mbps, distan ...
MAC, Scheduling, IP …
... CSMA/CD In CSMA, when there is a collision of two transmissions, it is detected only after the entire frames have been transmitted … irrespective of when the collision occurs CSMA/CD includes a collision detection mechanism that can detect collisions even as stations are transmitting Transmitting s ...
... CSMA/CD In CSMA, when there is a collision of two transmissions, it is detected only after the entire frames have been transmitted … irrespective of when the collision occurs CSMA/CD includes a collision detection mechanism that can detect collisions even as stations are transmitting Transmitting s ...
ppt - The Fengs
... • each station assigned fixed frequency band • unused transmission time in frequency bands go idle • example: 6-station LAN, 1,3,4 have pkt, frequency ...
... • each station assigned fixed frequency band • unused transmission time in frequency bands go idle • example: 6-station LAN, 1,3,4 have pkt, frequency ...
1 - Portal UniMAP
... b. Star topology: The other devices will still be able to send data through the hub; there will be no access to the device which has the failed connection to the hub. c. Bus Topology: All transmission stops if the failure is in the bus. If the drop-line fails, only the corresponding device cannot op ...
... b. Star topology: The other devices will still be able to send data through the hub; there will be no access to the device which has the failed connection to the hub. c. Bus Topology: All transmission stops if the failure is in the bus. If the drop-line fails, only the corresponding device cannot op ...
IP_review
... Determines which part of an IP address is the network field and which part is the host field. Follow these steps to determine the subnet mask: 1. Express the subnetwork IP address in binary form. 2. Replace the network and subnet portion of the address with all 1s. 3. Replace the host portion ...
... Determines which part of an IP address is the network field and which part is the host field. Follow these steps to determine the subnet mask: 1. Express the subnetwork IP address in binary form. 2. Replace the network and subnet portion of the address with all 1s. 3. Replace the host portion ...
Week10_2
... – A class B net allocated enough for 65K hosts • Even if only 2K hosts in that network ...
... – A class B net allocated enough for 65K hosts • Even if only 2K hosts in that network ...
Introduction
... Determines which part of an IP address is the network field and which part is the host field. Follow these steps to determine the subnet mask: 1. Express the subnetwork IP address in binary form. 2. Replace the network and subnet portion of the address with all 1s. 3. Replace the host portion ...
... Determines which part of an IP address is the network field and which part is the host field. Follow these steps to determine the subnet mask: 1. Express the subnetwork IP address in binary form. 2. Replace the network and subnet portion of the address with all 1s. 3. Replace the host portion ...
What is an IP address?
... Use of different physical media Preservation of address space Security ...
... Use of different physical media Preservation of address space Security ...
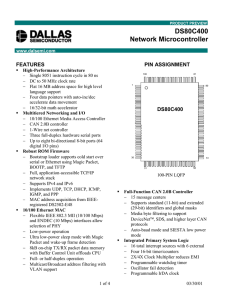
DS80C400-FCS - Maxim Integrated Products, Inc.
... 15 total message centers, 14 of which can be configured as either transmit or receive buffers and 1 which can serve as a receive double buffer. The device supports standard 11-bit or 29-extended message identifiers, and offers two separate 8-bit media masks and media arbitration fields to support th ...
... 15 total message centers, 14 of which can be configured as either transmit or receive buffers and 1 which can serve as a receive double buffer. The device supports standard 11-bit or 29-extended message identifiers, and offers two separate 8-bit media masks and media arbitration fields to support th ...
TCP/IP
... TCP is a connection-oriented transport protocol that sends data as an unstructured stream of bytes. By using sequence numbers and acknowledgment messages, TCP can provide a sending node with delivery information about packets transmitted to a destination node. ...
... TCP is a connection-oriented transport protocol that sends data as an unstructured stream of bytes. By using sequence numbers and acknowledgment messages, TCP can provide a sending node with delivery information about packets transmitted to a destination node. ...
University of Ottawa - School of Electrical Engineering and
... This communication pattern requires us to send 3 (64 – 8) or 168 total packets— that is, 56 packets in each of the three communication phases: northward, eastward, westwards. The number of hops suffered by packets depends on the topology. Here are the various cases: _ Bus—The mapping of the 8 ...
... This communication pattern requires us to send 3 (64 – 8) or 168 total packets— that is, 56 packets in each of the three communication phases: northward, eastward, westwards. The number of hops suffered by packets depends on the topology. Here are the various cases: _ Bus—The mapping of the 8 ...
Campus Area Networking
... from lower-priority traffic. Tags may be added to the packets to identify such classes, but they do not guarantee delivery as do quality of service (QoS) functions, which are implemented in the network devices. TechEncyclopedia, 2003(class of service) ...
... from lower-priority traffic. Tags may be added to the packets to identify such classes, but they do not guarantee delivery as do quality of service (QoS) functions, which are implemented in the network devices. TechEncyclopedia, 2003(class of service) ...
Logical addressing
... IP stands for Internet Protocol which is used for communicating data across a packet-switched internetwork using the Internet Protocol Suite, also referred to as TCP/IP. Logical addressing is an addressing scheme above the physical addressing. This is used for universal communication between differe ...
... IP stands for Internet Protocol which is used for communicating data across a packet-switched internetwork using the Internet Protocol Suite, also referred to as TCP/IP. Logical addressing is an addressing scheme above the physical addressing. This is used for universal communication between differe ...
Chapter 5: ARP
... back and forth, which means ARP messages must also pass back and forth to find these data link layer addresses. However, routers establish their own broadcast domains and generally do not pass ARP messages from interface to interface (although ARPs are used on each individual interface). 3. Why does ...
... back and forth, which means ARP messages must also pass back and forth to find these data link layer addresses. However, routers establish their own broadcast domains and generally do not pass ARP messages from interface to interface (although ARPs are used on each individual interface). 3. Why does ...
Internet Protocol, IP Addressing and Datagrams
... – suffix: a host attached to a given physical network, also known as host number ...
... – suffix: a host attached to a given physical network, also known as host number ...
Cisco Discovery 1 Module 05 Quiz Picture Descriptions
... if a bit is a zero (0), its column value is not counted. The value of each bit in an octet is twice that of the bit to its right. The rightmost bit in an octet has a value of 0 when it is turned on. A host looks at every bit of an IP address as it is received by the host NIC. If all of the bits in a ...
... if a bit is a zero (0), its column value is not counted. The value of each bit in an octet is twice that of the bit to its right. The rightmost bit in an octet has a value of 0 when it is turned on. A host looks at every bit of an IP address as it is received by the host NIC. If all of the bits in a ...
cut-through
... What will a bridge do if it receives a frame with a MAC address that is not within the table? • send frame to all ports except source port ...
... What will a bridge do if it receives a frame with a MAC address that is not within the table? • send frame to all ports except source port ...
Ethernet (CSMA/CD) - Universitas Hasanuddin
... – Growth of networks and the Internet – Extended use of TCP/IP – Single address per host ...
... – Growth of networks and the Internet – Extended use of TCP/IP – Single address per host ...
PPT Version
... • What problems do these discovery mechanisms solve? • Why should they be specified in the IETF? ...
... • What problems do these discovery mechanisms solve? • Why should they be specified in the IETF? ...
Embedded System Communication
... Single data wire, possibly also control and power wires Words transmitted one bit at a time Higher data throughput with long distances Less average capacitance, so more bits per unit of time ...
... Single data wire, possibly also control and power wires Words transmitted one bit at a time Higher data throughput with long distances Less average capacitance, so more bits per unit of time ...
Embedded System Communication
... Single data wire, possibly also control and power wires Words transmitted one bit at a time Higher data throughput with long distances Less average capacitance, so more bits per unit of time ...
... Single data wire, possibly also control and power wires Words transmitted one bit at a time Higher data throughput with long distances Less average capacitance, so more bits per unit of time ...
Network Architecture
... An Ethernet LAN that uses switches to connect individual hosts or segments. In the case of individual hosts, the switch replaces the repeater and effectively gives the device full 10 Mbps bandwidth (or 100 Mbps for Fast Ethernet) to the rest of the network. ...
... An Ethernet LAN that uses switches to connect individual hosts or segments. In the case of individual hosts, the switch replaces the repeater and effectively gives the device full 10 Mbps bandwidth (or 100 Mbps for Fast Ethernet) to the rest of the network. ...
I²C
I²C (Inter-Integrated Circuit), pronounced I-squared-C, is a multi-master, multi-slave, single-ended, serial computer bus invented by Philips Semiconductor (now NXP Semiconductors). It is typically used for attaching lower-speed peripheral ICs to processors and microcontrollers. Alternatively I²C is spelled I2C (pronounced I-two-C) or IIC (pronounced I-I-C). Since October 10, 2006, no licensing fees are required to implement the I²C protocol. However, fees are still required to obtain I²C slave addresses allocated by NXP.Several competitors, such as Siemens AG (later Infineon Technologies AG, now Intel mobile communications), NEC, Texas Instruments, STMicroelectronics (formerly SGS-Thomson), Motorola (later Freescale), and Intersil, have introduced compatible I²C products to the market since the mid-1990s.SMBus, defined by Intel in 1995, is a subset of I²C that defines the protocols more strictly. One purpose of SMBus is to promote robustness and interoperability. Accordingly, modern I²C systems incorporate policies and rules from SMBus, sometimes supporting both I²C and SMBus, requiring only minimal reconfiguration.