Document
... Suppose you have proved the theorem when n is 4 or an odd prime then it must also be true for every other n for example for n = 200 because x200 + y200 = z200 can be rewritten (x50)4 + (y50)4 = (z50)4 so any solution for n = 200 would give a solution for n = 4 which is not possible. ...
... Suppose you have proved the theorem when n is 4 or an odd prime then it must also be true for every other n for example for n = 200 because x200 + y200 = z200 can be rewritten (x50)4 + (y50)4 = (z50)4 so any solution for n = 200 would give a solution for n = 4 which is not possible. ...
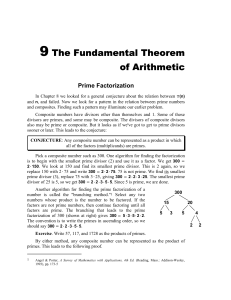
Programming with Prime Numbers
... because the only operations in the inner loop (Step 4) are a single comparison, addition and crossing-out, it is very fast in practice. There are other ways to make lists of prime numbers. If memory is constrained, or if you want only the primes on a limited range from m to n, you may be interested ...
... because the only operations in the inner loop (Step 4) are a single comparison, addition and crossing-out, it is very fast in practice. There are other ways to make lists of prime numbers. If memory is constrained, or if you want only the primes on a limited range from m to n, you may be interested ...
Extra handout: Reducing polynomials modulo p
... This gives another irreducibility test for polynomials. (Or as in the Problems Class, and in Tutorial 2, Question 3 the ideas can be used as a stepping-stone to deduce certain degree factors cannot occur.) Example. Show each polynomial fk,` (x) in the following family is irreducible, where fk,` (x) ...
... This gives another irreducibility test for polynomials. (Or as in the Problems Class, and in Tutorial 2, Question 3 the ideas can be used as a stepping-stone to deduce certain degree factors cannot occur.) Example. Show each polynomial fk,` (x) in the following family is irreducible, where fk,` (x) ...
Strong Pseudoprimes to Twelve Prime Bases
... we can simply append insertions to the end of the list, and so insertion time is dominated by the time to compute the hash value, O(m) time. Note that the signature and λp is stored with the prime for use by the fetch operation. The fetch operation computes the hash value, and then scans the linked ...
... we can simply append insertions to the end of the list, and so insertion time is dominated by the time to compute the hash value, O(m) time. Note that the signature and λp is stored with the prime for use by the fetch operation. The fetch operation computes the hash value, and then scans the linked ...
6B.E Prime or Composite
... way to find out is to find the square root of the number. Then divide the three-digit number by all the prime numbers lower than its square root. If none divide evenly; then, the number is prime. The square root of 359 is 18.9. Divide 359 by 2, 3, 5, 7, 11, 13, and 17. All composite numbers can be f ...
... way to find out is to find the square root of the number. Then divide the three-digit number by all the prime numbers lower than its square root. If none divide evenly; then, the number is prime. The square root of 359 is 18.9. Divide 359 by 2, 3, 5, 7, 11, 13, and 17. All composite numbers can be f ...
CMP3_G6_PT_AAG_3-2
... 3. To find the first number in a factor pair, first choose some of the prime numbers in the factorization. Multiply these primes together. To find the second factor in the pair, multiply the remaining prime factors. For example, a student might circle 2 × 3 × 3 and 2 to find the factor pair ...
... 3. To find the first number in a factor pair, first choose some of the prime numbers in the factorization. Multiply these primes together. To find the second factor in the pair, multiply the remaining prime factors. For example, a student might circle 2 × 3 × 3 and 2 to find the factor pair ...