* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Download ppt - Computer Science & Engineering
Survey
Document related concepts
Piggybacking (Internet access) wikipedia , lookup
Wireless security wikipedia , lookup
Computer network wikipedia , lookup
Point-to-Point Protocol over Ethernet wikipedia , lookup
IEEE 802.11 wikipedia , lookup
Internet protocol suite wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
Zero-configuration networking wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Transcript
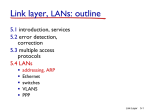
University of Nevada – Reno Computer Science & Engineering Department Fall 2015 CPE 400 / 600 Computer Communication Networks Lecture 22 Prof. Shamik Sengupta Office SEM 204 [email protected] http://www.cse.unr.edu/~shamik/ Chapter 5 Link Layer A note on the use of these ppt slides: We’re making these slides freely available to all (faculty, students, readers). They’re in PowerPoint form so you see the animations; and can add, modify, and delete slides (including this one) and slide content to suit your needs. They obviously represent a lot of work on our part. In return for use, we only ask the following: If you use these slides (e.g., in a class) that you mention their source (after all, we’d like people to use our book!) If you post any slides on a www site, that you note that they are adapted from (or perhaps identical to) our slides, and note our copyright of this material. Computer Networking: A Top Down Approach 6th edition Jim Kurose, Keith Ross Addison-Wesley March 2012 Thanks and enjoy! JFK/KWR All material copyright 1996-2012 J.F Kurose and K.W. Ross, All Rights Reserved Link Layer 5-2 The Data Link Layer Our goals: understand principles behind data link layer services: link layer addressing sharing a broadcast channel: multiple access reliable data transfer error detection, correction Understanding various link layer technologies Ethernet (wired domain) Hubs, Switches, Bridges Differences with Routers Wi-Fi (wireless domain) Link Layer: Introduction Some terminology: hosts and routers are nodes communication channels that connect adjacent nodes along communication path are links wired links wireless links layer-2 packet is a frame, encapsulates datagram data-link layer has responsibility of transferring datagram from one node to adjacent node over a link Link Layer Services framing, link access: encapsulate datagram into frame, adding header, trailer channel access if shared medium “MAC” addresses used in frame headers to identify source, dest different from IP address! reliable delivery between adjacent nodes Q: why both link-level and end-end reliability? Link Layer Services (more) flow control: pacing between adjacent sending and receiving nodes error detection: errors caused by signal attenuation, noise. receiver detects presence of errors: signals sender for retransmission or drops frame error correction: receiver identifies and corrects bit error(s) without resorting to retransmission Where is the link layer implemented? in each and every host link layer implemented in “adaptor” (aka network interface card NIC) Ethernet card, 802.11 card implements link, physical layer attaches into host’s system buses combination of hardware, software, firmware host schematic application transport network link cpu memory controller link physical host bus (e.g., PCI) physical transmission network adapter card MAC Addresses There are two types of addresses: 32-bit IP address: network-layer address used to get datagram to destination IP subnet MAC (or LAN or physical or Ethernet) address: function: get frame from one interface to another physically-connected interface (same network) 48 bit MAC address (for most LANs) burned in NIC ROM, also sometimes software settable MAC Addresses MAC (or LAN or physical or Ethernet) address: 48 bit MAC address MAC Addresses Each adapter on LAN has unique MAC address Locally administered Broadcast address = FF-FF-FF-FF-FF-FF 1A-2F-BB-76-09-AD 71-65-F7-2B-08-53 LAN (wired or wireless) = adapter 58-23-D7-FA-20-B0 0C-C4-11-6F-E3-98 Which ones are globally unique and which ones are locally administered? ARP Link Layer 5-11 ARP: Address Resolution Protocol Question: how to determine MAC address of B knowing B’s IP address? 137.196.7.78 1A-2F-BB-76-09-AD 137.196.7.23 137.196.7.14 LAN 71-65-F7-2B-08-53 137.196.7.88 58-23-D7-FA-20-B0 0C-C4-11-6F-E3-98 Each IP node (host, router) on LAN has ARP table ARP table: IP/MAC address mappings for some LAN nodes < IP address; MAC address> Timeout: time after which address mapping will be forgotten (Varies from vendor to vendor, device to device) ARP: Address Resolution Protocol Question: how to determine MAC address of B knowing B’s IP address? 137.196.7.78 1A-2F-BB-76-09-AD 137.196.7.23 137.196.7.14 LAN 71-65-F7-2B-08-53 137.196.7.88 58-23-D7-FA-20-B0 0C-C4-11-6F-E3-98 arp -a arp -s arp -d ARP protocol: Same LAN (network) A wants to send datagram to B, and B’s MAC address not in A’s ARP table. A broadcasts ARP query packet, containing B's IP address dest MAC address = FF-FFFF-FF-FF-FF all machines on LAN receive ARP query B receives ARP packet, replies to A with its (B's) MAC address frame sent to A’s MAC address (unicast) A caches (saves) IP-to-MAC address pair in its ARP table until information becomes old (times out) soft state: information that times out (goes away) unless refreshed ARP is “plug-and-play”: nodes create their ARP tables without intervention from net administrator Addressing: routing to another LAN Proxy-ARP: walkthrough: send datagram from A to B via R assume A knows B’s IP address 88-B2-2F-54-1A-0F 74-29-9C-E8-FF-55 A 111.111.111.111 E6-E9-00-17-BB-4B 1A-23-F9-CD-06-9B 222.222.222.220 111.111.111.110 111.111.111.112 R 222.222.222.221 222.222.222.222 B 49-BD-D2-C7-56-2A CC-49-DE-D0-AB-7D two ARP tables in router R, one for each IP network (LAN) Addressing: routing to another LAN A creates IP datagram with IP source A, destination B A creates link-layer frame with R's MAC address as dest, frame contains A-to-B IP datagram MAC src: 74-29-9C-E8-FF-55 MAC dest: E6-E9-00-17-BB-4B IP src: 111.111.111.111 IP dest: 222.222.222.222 IP Eth Phy A R 111.111.111.111 74-29-9C-E8-FF-55 B 222.222.222.222 49-BD-D2-C7-56-2A 222.222.222.220 1A-23-F9-CD-06-9B 111.111.111.112 CC-49-DE-D0-AB-7D 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.221 88-B2-2F-54-1A-0F Link Layer 5-16 Addressing: routing to another LAN frame sent from A to R frame received at R, datagram removed, passed up to IP MAC src: 74-29-9C-E8-FF-55 MAC dest: E6-E9-00-17-BB-4B IP src: 111.111.111.111 IP dest: 222.222.222.222 IP src: 111.111.111.111 IP dest: 222.222.222.222 IP Eth Phy A IP Eth Phy R 111.111.111.111 74-29-9C-E8-FF-55 B 222.222.222.222 49-BD-D2-C7-56-2A 222.222.222.220 1A-23-F9-CD-06-9B 111.111.111.112 CC-49-DE-D0-AB-7D 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.221 88-B2-2F-54-1A-0F Link Layer 5-17 Addressing: routing to another LAN R forwards datagram with IP source A, destination B R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram MAC src: 1A-23-F9-CD-06-9B MAC dest: 49-BD-D2-C7-56-2A IP src: 111.111.111.111 IP dest: 222.222.222.222 IP Eth Phy A R 111.111.111.111 74-29-9C-E8-FF-55 IP Eth Phy B 222.222.222.222 49-BD-D2-C7-56-2A 222.222.222.220 1A-23-F9-CD-06-9B 111.111.111.112 CC-49-DE-D0-AB-7D 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.221 88-B2-2F-54-1A-0F Link Layer 5-18 Addressing: routing to another LAN R forwards datagram with IP source A, destination B R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram MAC src: 1A-23-F9-CD-06-9B MAC dest: 49-BD-D2-C7-56-2A IP src: 111.111.111.111 IP dest: 222.222.222.222 IP Eth Phy A R 111.111.111.111 74-29-9C-E8-FF-55 IP Eth Phy B 222.222.222.222 49-BD-D2-C7-56-2A 222.222.222.220 1A-23-F9-CD-06-9B 111.111.111.112 CC-49-DE-D0-AB-7D 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.221 88-B2-2F-54-1A-0F Link Layer 5-19 Addressing: routing to another LAN R forwards datagram with IP source A, destination B R creates link-layer frame with B's MAC address as dest, frame contains A-to-B IP datagram MAC src: 1A-23-F9-CD-06-9B MAC dest: 49-BD-D2-C7-56-2A IP src: 111.111.111.111 IP dest: 222.222.222.222 IP Eth Phy A R 111.111.111.111 74-29-9C-E8-FF-55 B 222.222.222.222 49-BD-D2-C7-56-2A 222.222.222.220 1A-23-F9-CD-06-9B 111.111.111.112 CC-49-DE-D0-AB-7D 111.111.111.110 E6-E9-00-17-BB-4B 222.222.222.221 88-B2-2F-54-1A-0F Link Layer 5-20 Understanding the competition for medium (channel) access Protocols for Medium Access Control (MAC) Multiple Access Links and Protocols Two types of “links”: broadcast (shared wire or medium) Ethernet 802.11 wireless LAN humans at a cocktail party (shared air, acoustical) point-to-point point-to-point link between switches/Bridges and hosts shared wire (e.g., cabled Ethernet) shared RF (e.g., 802.11 WiFi) shared RF (satellite) Multiple Access protocols single shared broadcast channel two or more simultaneous transmissions by nodes: interference collision if node receives two or more signals at the same time multiple access protocol distributed algorithm that determines how nodes share channel, i.e., determine when node can transmit communication about channel sharing must use channel itself! no out-of-band channel for coordination Ideal Multiple Access Protocol What are the multiple access protocols? Channel Partitioning MAC protocols: TDMA TDMA: time division multiple access access to channel in "rounds" each station gets fixed length slot (length = pkt trans time) in each round unused slots go idle example: 6-station LAN, 1,3,4 have pkt, slots 2,5,6 idle 6-slot frame 1 3 4 1 3 4 Channel Partitioning MAC protocols: FDMA FDMA: frequency division multiple access channel spectrum divided into frequency bands each station assigned fixed frequency band unused transmission time in frequency bands go idle example: 6-station LAN, 1,3,4 have pkt, frequency bands 2,5,6 idle FDM cable frequency bands “Taking Turns” MAC protocols Polling: master node “invites” slave nodes to transmit in turn typically used with “dumb” slave devices concerns: 1. 2. 3. polling overhead latency single point of failure (master) data poll master data slaves “Taking Turns” MAC protocols Token ring: control token passed from one node to next sequentially. token message concerns: token overhead latency single point of failure (token) T (nothing to send) T data Concerns with Ideal protocols Conservative Too much overhead wasted Not flexible, dynamic If one user has nothing to send that “slot” is wasted Internet is all about dynamic…why not make MAC protocol dynamic in nature? MAC: Random Access Protocols When node has packet to send transmit at full channel data rate R. no a priori coordination among nodes two or more transmitting nodes ➜ “collision”, random access MAC protocol specifies: how to detect collisions how to recover from collisions (e.g., via delayed retransmissions) Examples of random access MAC protocols: Ethernet (IEEE 802.3) Wi-Fi (IEEE 802.11) Based on the principle of reducing collisions! CSMA (Carrier Sense Multiple Access) CSMA: listen before transmit: If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission human analogy: don’t interrupt others! CSMA/CD (Collision Detection) CSMA/CD: carrier sensing, collision detection collisions detected within short time colliding transmissions aborted, reducing channel wastage collision detection: easy in wired LANs: measure signal strengths, compare transmitted, received signals difficult in wireless LANs: received signal strength overwhelmed by local transmission strength human analogy: the polite conversationalist Ethernet Ethernet “dominant” wired LAN technology: cheap $20 for NIC first widely used LAN technology simpler, cheaper kept up with speed race: 10 Mbps – 10 Gbps Metcalfe’s Ethernet sketch Ethernet: physical topology bus: popular through mid 90s all nodes in same collision domain • can collide with each other star: prevails today active switch in center each “spoke” runs a (separate) Ethernet protocol • nodes do not collide with each other switch star bus: coaxial cable Link Layer 5-35 Ethernet frame structure sending adapter encapsulates IP datagram (or other network layer protocol packet) in Ethernet frame type dest. source preamble address address data (payload) CRC preamble: 7 bytes with pattern 10101010 followed by one byte with pattern 10101011 Link Layer 5-36 Ethernet frame structure (more) addresses: 6 byte source, destination MAC addresses if adapter receives frame with matching destination address, or with broadcast address (e.g. ARP packet), it passes data in frame to network layer protocol otherwise, adapter discards frame type: indicates higher layer protocol IPV4, IPV6, ARP etc. CRC: cyclic redundancy check at receiver error detected: frame is dropped type dest. source preamble address address data (payload) CRC Link Layer 5-37 Ethernet: Unreliable, connectionless connectionless: No handshaking between sending and receiving NICs unreliable: receiving NIC doesn’t send acks or nacks to sending NIC stream of datagrams passed to network layer can have gaps (missing datagrams) gaps will be filled if app is using TCP otherwise, app will see gaps Ethernet’s MAC protocol: unslotted CSMA/CD Ethernet CSMA/CD algorithm 1. NIC receives datagram from network 4. If NIC detects another transmission layer, creates frame while transmitting, aborts, send a jam signal and prepare for retransmission 2. If NIC senses channel idle, starts frame transmission. 5. After collision, NIC enters If NIC senses channel busy, waits exponential backoff: after mth until channel idle, then transmits collision, NIC chooses K at random from {0,1,2,…,2m-1}. NIC waits K 3. If NIC transmits entire frame without slot times, returns to Step 2 detecting another transmission, NIC (1 slot = 512 bit times) is done with frame !