(Superpersistent Bootkit)
... The kernel is compressed with an algorithm that I’ve tried to replicate but failed miserably, so it can’t be modified. ...
... The kernel is compressed with an algorithm that I’ve tried to replicate but failed miserably, so it can’t be modified. ...
A Virtual Machine Introspection Based Architecture for Intrusion
... of the host. This offers visibility comparable to that offered by an HIDS. Directly observing hardware state offers a more robust view of the system than that obtained by an HIDS, which traditionally relies on the integrity of the operating system. This view from below provided by a VMI-based IDS al ...
... of the host. This offers visibility comparable to that offered by an HIDS. Directly observing hardware state offers a more robust view of the system than that obtained by an HIDS, which traditionally relies on the integrity of the operating system. This view from below provided by a VMI-based IDS al ...
Chapter 2
... DOS when you need a small OS DOS is more compact than Windows and hence useful for embedded systems or for portability DOS is popular as an operating system due to its ability to pack all startup files on a single floppy disk The floppy disk is also known as the startup disk Startup disk accommodate ...
... DOS when you need a small OS DOS is more compact than Windows and hence useful for embedded systems or for portability DOS is popular as an operating system due to its ability to pack all startup files on a single floppy disk The floppy disk is also known as the startup disk Startup disk accommodate ...
SecureSwitch: BIOS-Assisted Isolation and Switch between Trusted
... more space, cooling, and energy. It is inflexible and cannot support the current need for a range of trusted environments. Moreover, it is inconvenient for users to switch between two computers to finish their tasks. Multi-boot supports the installation of multiple OSes on the same machine and uses ...
... more space, cooling, and energy. It is inflexible and cannot support the current need for a range of trusted environments. Moreover, it is inconvenient for users to switch between two computers to finish their tasks. Multi-boot supports the installation of multiple OSes on the same machine and uses ...
Application of Software Components in Operating System Design
... and also my individual contributions to the implementation of HelenOS. That being written, it is completely necessary to acknowledge that no human is an island and (almost) all ideas are always extensions and recombination of previous ideas. The current source code of HelenOS in its mainline branch ...
... and also my individual contributions to the implementation of HelenOS. That being written, it is completely necessary to acknowledge that no human is an island and (almost) all ideas are always extensions and recombination of previous ideas. The current source code of HelenOS in its mainline branch ...
Linux Kernel - Teacher Pages
... Normal kernel code is non-preemptible – when a time interrupt is received while a process is executing a kernel system service routine, the kernel’s need_resched flag is set so that the scheduler will run once the system call has completed and control is about to be returned to user mode ...
... Normal kernel code is non-preemptible – when a time interrupt is received while a process is executing a kernel system service routine, the kernel’s need_resched flag is set so that the scheduler will run once the system call has completed and control is about to be returned to user mode ...
chapter 1 - University of Virginia
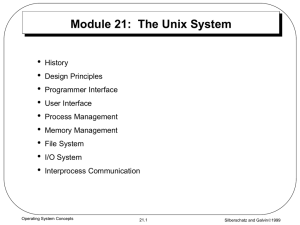
... by using threads and inter-process communication (IPC). This allows programmers to abstract their programs better and it provides better performance in multi-processor and network computers. (Silberschatz) Many programs can be broken down into multiple tasks, each of which can be executed by a separ ...
... by using threads and inter-process communication (IPC). This allows programmers to abstract their programs better and it provides better performance in multi-processor and network computers. (Silberschatz) Many programs can be broken down into multiple tasks, each of which can be executed by a separ ...
Homework Assignment 1 Practice the following questions based on
... One way is to allow the command interpreter to contain the code needed to execute the command. The other way is to implement the commands through system programs. Compare and contrast the two approaches. Ans: In the first approach, upon the user issuing a command, the interpreter jumps to the approp ...
... One way is to allow the command interpreter to contain the code needed to execute the command. The other way is to implement the commands through system programs. Compare and contrast the two approaches. Ans: In the first approach, upon the user issuing a command, the interpreter jumps to the approp ...
Post Graduate Diploma in Computer Application
... and many other formulae for calculations. Simpler calculations take less time. But complex calculations take much longer time. Another factor is accuracy in calculations. So man explored with the idea to develop a machine, which can perform this type of arithmetic calculation faster, and with full a ...
... and many other formulae for calculations. Simpler calculations take less time. But complex calculations take much longer time. Another factor is accuracy in calculations. So man explored with the idea to develop a machine, which can perform this type of arithmetic calculation faster, and with full a ...
File System - dhdurso.org index to available resources
... setuid bit sets the effective user identifier of the process to the user identifier of the owner of the file, and leaves the real user identifier as it was. setuid scheme allows certain processes to have more than ordinary privileges while still being executable by ordinary users. ...
... setuid bit sets the effective user identifier of the process to the user identifier of the owner of the file, and leaves the real user identifier as it was. setuid scheme allows certain processes to have more than ordinary privileges while still being executable by ordinary users. ...
Quick UNIX Tutorial
... Getting help while on the system The shell Working with files & directories Wild card characters ...
... Getting help while on the system The shell Working with files & directories Wild card characters ...
xv6 - PDOS-MIT
... word processor need not concern itself with which type of disk hardware is being used. It also multiplexes the hardware, allowing many programs to share the computer and run (or appear to run) at the same time. Finally, operating systems provide controlled ways for programs to interact, so that they ...
... word processor need not concern itself with which type of disk hardware is being used. It also multiplexes the hardware, allowing many programs to share the computer and run (or appear to run) at the same time. Finally, operating systems provide controlled ways for programs to interact, so that they ...
introduction
... software that runs in kernel mode—and even that is not always true. Part of the problem is that operating systems perform two basically unrelated functions: providing application programmers (and application programs) a clean abstract set of resources instead of the messy hardware ones and managing ...
... software that runs in kernel mode—and even that is not always true. Part of the problem is that operating systems perform two basically unrelated functions: providing application programmers (and application programs) a clean abstract set of resources instead of the messy hardware ones and managing ...
Introduction to Unix
... number of PC hardware devices (graphics cards, network cards, hard disks etc.), advanced processor and memory management features, and support for many different types of filesystems (including DOS floppies and the ISO9660 standard for CDROMs). In terms of the services that it provides to applicatio ...
... number of PC hardware devices (graphics cards, network cards, hard disks etc.), advanced processor and memory management features, and support for many different types of filesystems (including DOS floppies and the ISO9660 standard for CDROMs). In terms of the services that it provides to applicatio ...
LINUX
... devices (graphics cards, network cards, hard disks etc.), advanced processor and memory management features, and support for many different types of filesystems (including DOS floppies and the ISO9660 standard for CDROMs). In terms of the services that it provides to application programs and system ...
... devices (graphics cards, network cards, hard disks etc.), advanced processor and memory management features, and support for many different types of filesystems (including DOS floppies and the ISO9660 standard for CDROMs). In terms of the services that it provides to application programs and system ...
Solution Operating System Concepts By Galvin,Silberschatz Solved
... This sequence occurs because when the main thread fork () s two children they don't begin executing until main relinquishes the CPU which happens when main calls join (). Fork () has put t1 at the head of the run queue and t2 behind it, so when main calls join (), Nachos context switches to t1, caus ...
... This sequence occurs because when the main thread fork () s two children they don't begin executing until main relinquishes the CPU which happens when main calls join (). Fork () has put t1 at the head of the run queue and t2 behind it, so when main calls join (), Nachos context switches to t1, caus ...
Adopting and Commenting the Old Kernel Source Code for Education
... first read into the cache area from the block device. When a task needs to output the data to a block device, the data is put into the cache area first and then is written into the block device by the hardware driver in due time. The last part of the physical memory is the main area used dynamically ...
... first read into the cache area from the block device. When a task needs to output the data to a block device, the data is put into the cache area first and then is written into the block device by the hardware driver in due time. The last part of the physical memory is the main area used dynamically ...
Linux Tutorial
... directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the directory. This implies that you may read files in the directory if you have read permission on the individual files. example: ...
... directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the directory. This implies that you may read files in the directory if you have read permission on the individual files. example: ...
Introducing the iRMX® Operating Systems
... Most of the references to system calls in the text and graphics use C syntax instead of PL/M (for example, the system call send_message instead of send$message). If you are working in C, you must use the C header files, rmx_c.h, udi_c.h, and rmx_err.h. If you are working in PL/M, you must use dollar ...
... Most of the references to system calls in the text and graphics use C syntax instead of PL/M (for example, the system call send_message instead of send$message). If you are working in C, you must use the C header files, rmx_c.h, udi_c.h, and rmx_err.h. If you are working in PL/M, you must use dollar ...
OPERATING SYSTEM : AN OVERVIEW – [UNIT
... Computer software can be divided into two main categories: application software and system software. Application software consists of the programs for performing tasks particular to the machine’s utilisation. This software is designed to solve a particular problem for users. Examples of application ...
... Computer software can be divided into two main categories: application software and system software. Application software consists of the programs for performing tasks particular to the machine’s utilisation. This software is designed to solve a particular problem for users. Examples of application ...
A Taxonomy of Computer Program Security Flaws, with Examples
... Knowing how systems have failed can help us build systems that resist failure. Petroski [1] makes this point eloquently in the context of engineering design, and although software failures may be less visible than those of the bridges he describes, they can be equally damaging. But the history of so ...
... Knowing how systems have failed can help us build systems that resist failure. Petroski [1] makes this point eloquently in the context of engineering design, and although software failures may be less visible than those of the bridges he describes, they can be equally damaging. But the history of so ...
Quick UNIX Tutorial
... directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the directory. This implies that you may read files in the directory if you have read permission on the individual files. example: CS4 ...
... directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the directory. This implies that you may read files in the directory if you have read permission on the individual files. example: CS4 ...
LinuxOS-SGOSbookCh20
... Anyone using Linux, or creating their own derivative of Linux, may not make the derived product proprietary; software released under the GPL may not be redistributed as a binary-only product ...
... Anyone using Linux, or creating their own derivative of Linux, may not make the derived product proprietary; software released under the GPL may not be redistributed as a binary-only product ...
Forensics Book 2: Investigating Hard Disk and File and Operating
... partition loader, or boot loader, examines the partition table for a partition marked as active The partition loader then searches the very first sector of that partition for a boot record. The active partition’s boot record is checked for a valid boot signature and, if found, the boot sector co ...
... partition loader, or boot loader, examines the partition table for a partition marked as active The partition loader then searches the very first sector of that partition for a boot record. The active partition’s boot record is checked for a valid boot signature and, if found, the boot sector co ...
unit-1-The-UNIX-Operating-System
... For example, an OS ensures safe access to a printer by allowing only one application program to send data directly to the printer at any one time. An OS encourages efficient use of the CPU by suspending programs that are waiting for I/O operations to complete to make way for programs that can use th ...
... For example, an OS ensures safe access to a printer by allowing only one application program to send data directly to the printer at any one time. An OS encourages efficient use of the CPU by suspending programs that are waiting for I/O operations to complete to make way for programs that can use th ...
Acorn MOS

Acorn's Machine Operating System (MOS) or OS was a computer operating system used in the Acorn BBC computer range. It included support for four-channel sound and graphics, file system abstraction, and digital and analogue I/O including a daisy-chained fast expansion bus. The implementation was single-tasking, monolithic and non-reentrant.Versions 0.10 to 1.20 were used on the BBC Micro, version 1.00 on the Electron, version 2 was used on the B+, and versions 3 to 5 were used in the BBC Master Series range.The final BBC computer, the BBC A3000, was 32-bit and ran RISC OS. Its operating system used portions of the Acorn MOS architecture and shared a number of characteristics (commands, VDU system) with the earlier 8-bit MOS.Versions 0 and 1 of the MOS were 16KiB in size, written in 6502 machine code, and held in ROM on the motherboard. The upper quarter of the 16-bit address space (0xC000 to 0xFFFF) is reserved for its ROM code and I/O space.Versions 2 to 5 were still restricted to a 16KiB address space but managed to hold more code and hence more complex routines, partly because of the alternative 65C102 CPU with its denser instruction set plus the careful use of paging.