second-hand brokerage - The University of Chicago Booth School of
... emotions to be understood. In contrast, the social capital of brokerage concerns information arbitrage. Knowing how information varies between friends of friends could be valuable. For example, building on Brass’s (1984) early report of promotion correlated with information control measured by Freem ...
... emotions to be understood. In contrast, the social capital of brokerage concerns information arbitrage. Knowing how information varies between friends of friends could be valuable. For example, building on Brass’s (1984) early report of promotion correlated with information control measured by Freem ...
RNX-N600PCE_v2.0 N600 Wireless Dual Band PCI
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses and can radiate ...
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses and can radiate ...
OSPF Single Area
... Link-State Routing Protocols - History An IETF working group designed a routing protocol specifically for IP routing, OSPF (Open Shortest Path First). For most network administrators they had two open-standard routing protocols to choose from: RIP, simple but very limited, or OSPF, robust but m ...
... Link-State Routing Protocols - History An IETF working group designed a routing protocol specifically for IP routing, OSPF (Open Shortest Path First). For most network administrators they had two open-standard routing protocols to choose from: RIP, simple but very limited, or OSPF, robust but m ...
... Copyright 2014 by PLANET Technology Corp. All rights reserved. No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language or computer language, in any form or by any means, electronic, mechanical, magnetic, optical, chemic ...
File - George P. Lumayag
... to start an Ad Hoc network if no matching network name is found after scanning all available modes. This mode also allows the selection of the channel the wireless adapter uses. The channels available depend on the regulatory domain. If the adapter finds no other ad hoc adapters, the channel that th ...
... to start an Ad Hoc network if no matching network name is found after scanning all available modes. This mode also allows the selection of the channel the wireless adapter uses. The channels available depend on the regulatory domain. If the adapter finds no other ad hoc adapters, the channel that th ...
CoBox-FL-IAP User Guide - SemiconductorStore.com
... The Lantronix Industrial Automation Platform (IAP) family of Device Servers allows a single network and protocol to connect multiple serial devices from many vendors. IAP provides the automation industry with a network-enabling solution using TCP/IP and standard Ethernet networks that is vendor-inde ...
... The Lantronix Industrial Automation Platform (IAP) family of Device Servers allows a single network and protocol to connect multiple serial devices from many vendors. IAP provides the automation industry with a network-enabling solution using TCP/IP and standard Ethernet networks that is vendor-inde ...
New Courier Enhancement
... A server stub will be placed in a RCVMSG state when the IS server sends data back to the client over the network. It will remain in this state until the connection is closed by the client or if the OS tells courier that the network connection no longer exists. This means that any reason why the clos ...
... A server stub will be placed in a RCVMSG state when the IS server sends data back to the client over the network. It will remain in this state until the connection is closed by the client or if the OS tells courier that the network connection no longer exists. This means that any reason why the clos ...
PDF Using the HASP dongle with Windows XP
... How can I reduce the time it takes to communicate with the NetHASP key? If it takes 20-30 seconds for the protected program to load, you can speed it up by specifying the exact location (network address) of the LM in the nethasp.ini configuration file. You can do that with the TCPIP, IPX or NetBIOS ...
... How can I reduce the time it takes to communicate with the NetHASP key? If it takes 20-30 seconds for the protected program to load, you can speed it up by specifying the exact location (network address) of the LM in the nethasp.ini configuration file. You can do that with the TCPIP, IPX or NetBIOS ...
The Front Line Battle Against P2P
... technologies, and open-source products referred to in this paper. It is beyond the scope of this paper to discuss installation instructions for each product referenced in this paper, and readers will be referred to installation instructions where appropriate. Interested users should refer to Snort [ ...
... technologies, and open-source products referred to in this paper. It is beyond the scope of this paper to discuss installation instructions for each product referenced in this paper, and readers will be referred to installation instructions where appropriate. Interested users should refer to Snort [ ...
PDF only - at www.arxiv.org.
... inject vector (ap1,2) on area 3, since the underlying route crosses this area (it is via R3). Thus, R6 keeps believing that the shortest path from itself to ap1 is via R3 with a cost of 5, which not optimal. The OSPF LSDB is divided in records, named Link State Advertisements (LSAs), each describing ...
... inject vector (ap1,2) on area 3, since the underlying route crosses this area (it is via R3). Thus, R6 keeps believing that the shortest path from itself to ap1 is via R3 with a cost of 5, which not optimal. The OSPF LSDB is divided in records, named Link State Advertisements (LSAs), each describing ...
pmac2wn07-slide-v0
... Each MMA will be a member of multicast tree Each MH should have one MMA MMA of the MH will change as it roams in the network Each MH keeps a counter to record the number of subnets it has crossed within the service area of its MMA Regional service area of MMA = Number of subnets covered by the MMA ...
... Each MMA will be a member of multicast tree Each MH should have one MMA MMA of the MH will change as it roams in the network Each MH keeps a counter to record the number of subnets it has crossed within the service area of its MMA Regional service area of MMA = Number of subnets covered by the MMA ...
EtherFast® 10/100 LAN Card
... Built to run with the fastest network applications, the EtherFast® 10/100 LAN Card is a high performance network adapter for desktop computers with 32-bit PCI expansion slots. The EtherFast® 10/100 LAN Card is ready to run with both 10BaseT and 100BaseTX networks right out of the box – the card's 10 ...
... Built to run with the fastest network applications, the EtherFast® 10/100 LAN Card is a high performance network adapter for desktop computers with 32-bit PCI expansion slots. The EtherFast® 10/100 LAN Card is ready to run with both 10BaseT and 100BaseTX networks right out of the box – the card's 10 ...
Setup Guide (DA4-90270-60)
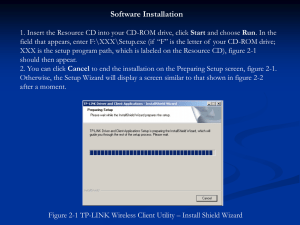
... Installing the OfficeBridge programs NOTE: • Install utility programs or drivers on each computer. • Before installing, scan for viruses and close any running applications. Failing to do so may interfere with proper installation. • Windows 2000, Windows XP, Windows NT 4.0, and Windows server 2003 re ...
... Installing the OfficeBridge programs NOTE: • Install utility programs or drivers on each computer. • Before installing, scan for viruses and close any running applications. Failing to do so may interfere with proper installation. • Windows 2000, Windows XP, Windows NT 4.0, and Windows server 2003 re ...
AW-GA200 User Manual V1.1 AzureWave Technologies Inc, 2006
... size, the RTS/CTS mechanism will not be enabled. The device sends request to send (RTS) frames to a particular receiving station and negotiates the sending of a data frame. Default setting is 2347. Beacon Period: A beacon is a packet broadcast by the device to synchronize the wireless network. The B ...
... size, the RTS/CTS mechanism will not be enabled. The device sends request to send (RTS) frames to a particular receiving station and negotiates the sending of a data frame. Default setting is 2347. Beacon Period: A beacon is a packet broadcast by the device to synchronize the wireless network. The B ...
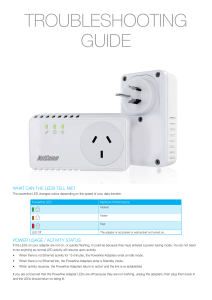
troubleshooting guide - NetComm Wireless Support
... Within 2 minutes, press the “SIMPLE CONNECT” button on the second adapter for less than 3 seconds. The network password has been reset and both adapters will be able to communicate with each other. To make this process easier it is recommended that both Adapters are connected to a powerpoint near ea ...
... Within 2 minutes, press the “SIMPLE CONNECT” button on the second adapter for less than 3 seconds. The network password has been reset and both adapters will be able to communicate with each other. To make this process easier it is recommended that both Adapters are connected to a powerpoint near ea ...
Document
... Does such a scheme converge to a fair allocation ? Here max-min and proportionally fair are the same (i.e. same rate to all) The scheme may not converge as sources may not be stationary But we would like that the scheme increases fairness ...
... Does such a scheme converge to a fair allocation ? Here max-min and proportionally fair are the same (i.e. same rate to all) The scheme may not converge as sources may not be stationary But we would like that the scheme increases fairness ...
Tenda Wireless Network Adapter User Guide
... belongs to Shenzhen Tenda Technology Co., Ltd. Without prior expressed written permission from Shenzhen Tenda Technology Co., Ltd, any individual or party is not allowed to copy, plagiarize, reproduce, or translate it into other languages. All photos and product specifications mentioned in this manu ...
... belongs to Shenzhen Tenda Technology Co., Ltd. Without prior expressed written permission from Shenzhen Tenda Technology Co., Ltd, any individual or party is not allowed to copy, plagiarize, reproduce, or translate it into other languages. All photos and product specifications mentioned in this manu ...
NodeUtil Node Utility User`s Guide
... tool. It allows you to view and modify the configuration of a single device, but does not manage a device’s configuration in the context of the network containing the device. Important: Using NodeUtil, it is possible to make a device inoperable, so that it no longer communicates with other devices i ...
... tool. It allows you to view and modify the configuration of a single device, but does not manage a device’s configuration in the context of the network containing the device. Important: Using NodeUtil, it is possible to make a device inoperable, so that it no longer communicates with other devices i ...
EFG80 user guide.qxd
... update its products, software, or documentation without obligation to notify any individual or entity. Please direct all inquiries to: Linksys P.O. Box 18558, Irvine, CA 92623. FCC STATEMENT This equipment has been tested and complies with the specification for a Class B digital device, pursuant to ...
... update its products, software, or documentation without obligation to notify any individual or entity. Please direct all inquiries to: Linksys P.O. Box 18558, Irvine, CA 92623. FCC STATEMENT This equipment has been tested and complies with the specification for a Class B digital device, pursuant to ...
Dismal Science Fictions: Network Effects, Microsoft
... regulation. It is interesting, particularly in the context of the antitrust debate over operating systems, that the industries that we have traditionally regarded as natural monopolies are now being widely deregulated. Network effects, sometimes called network externalities, may be understood as a s ...
... regulation. It is interesting, particularly in the context of the antitrust debate over operating systems, that the industries that we have traditionally regarded as natural monopolies are now being widely deregulated. Network effects, sometimes called network externalities, may be understood as a s ...
Network Interface Card Installation Guide
... PRQ_xxxxxx_BIN. This name is factory set and cannot be changed. ...
... PRQ_xxxxxx_BIN. This name is factory set and cannot be changed. ...
- Sonnet Technologies
... General Guidelines for OS-Specific Situations ...................................................................................................................................... 15 Chapter 3—Using the Wireless LAN Utility ........................................................................... ...
... General Guidelines for OS-Specific Situations ...................................................................................................................................... 15 Chapter 3—Using the Wireless LAN Utility ........................................................................... ...
XET1001 Wall-Plugged Ethernet Adapter User Guide
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
EFG80 user guide.qxd
... update its products, software, or documentation without obligation to notify any individual or entity. Please direct all inquiries to: Linksys P.O. Box 18558, Irvine, CA 92623. FCC STATEMENT This equipment has been tested and complies with the specification for a Class B digital device, pursuant to ...
... update its products, software, or documentation without obligation to notify any individual or entity. Please direct all inquiries to: Linksys P.O. Box 18558, Irvine, CA 92623. FCC STATEMENT This equipment has been tested and complies with the specification for a Class B digital device, pursuant to ...
Document
... Supported versions . . . . . . . . . . . . . . . . . . . . . Printing the configuration page . . . . . . . . . . . Network Card Setup utility for Mac OS 9 . . . . . . . Launching the Network Card Setup utility . . . . Setting the Printer Discovery settings. . . . . . . Changing the password . . . . ...
... Supported versions . . . . . . . . . . . . . . . . . . . . . Printing the configuration page . . . . . . . . . . . Network Card Setup utility for Mac OS 9 . . . . . . . Launching the Network Card Setup utility . . . . Setting the Printer Discovery settings. . . . . . . Changing the password . . . . ...
Network effect

In economics and business, a network effect (also called network externality or demand-side economies of scale) is the effect that one user of a good or service has on the value of that product to other people. When a network effect is present, the value of a product or service is dependent on the number of others using it.The classic example is the telephone. The more people who own telephones, the more valuable the telephone is to each owner. This creates a positive externality because a user may purchase a telephone without intending to create value for other users, but does so in any case. Online social networks work in the same way, with sites like Twitter and Facebook becoming more attractive as more users join.The expression ""network effect"" is applied most commonly to positive network externalities as in the case of the telephone. Negative network externalities can also occur, where more users make a product less valuable, but are more commonly referred to as ""congestion"" (as in traffic congestion or network congestion).Over time, positive network effects can create a bandwagon effect as the network becomes more valuable and more people join, in a positive feedback loop.