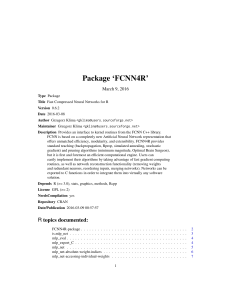
Package `FCNN4R`
... grad(input, output). This function is useful for implementing on-line teaching algorithms. mlp_gradij computes gradients of network outputs, i.e the derivatives of outputs w.r.t. active weights, at given data row. The derivatives of outputs are placed in subsequent columns of the returned matrix. Sc ...
... grad(input, output). This function is useful for implementing on-line teaching algorithms. mlp_gradij computes gradients of network outputs, i.e the derivatives of outputs w.r.t. active weights, at given data row. The derivatives of outputs are placed in subsequent columns of the returned matrix. Sc ...
Planning with Markov Decision Processes
... when designing an intelligent agent that needs to act for long periods of time in an environment where its actions could have uncertain outcomes. MDPs are actively researched in two related subareas of AI, probabilistic planning and reinforcement learning. Probabilistic planning assumes known models ...
... when designing an intelligent agent that needs to act for long periods of time in an environment where its actions could have uncertain outcomes. MDPs are actively researched in two related subareas of AI, probabilistic planning and reinforcement learning. Probabilistic planning assumes known models ...
10. Fuzzy Reasoning - Computing Science
... P(A) = 0.5 means that A may be true or may be false A logical value of 0.5 means both true and false at the same time. The difference is still ambiguous to many scholars. ...
... P(A) = 0.5 means that A may be true or may be false A logical value of 0.5 means both true and false at the same time. The difference is still ambiguous to many scholars. ...
Induction on Number Series - Angewandte Informatik / Kognitive
... MagicHaskeller is an inductive functional programming system based on systematic exhaustive search (Katayama, 2011). The system synthesizes given input-output specifications to find functions that represent the input-output specifications, e.g. f [1..5] == 6 ⇒ f = (\f → 1 + length a). f [1..5] == 6 ...
... MagicHaskeller is an inductive functional programming system based on systematic exhaustive search (Katayama, 2011). The system synthesizes given input-output specifications to find functions that represent the input-output specifications, e.g. f [1..5] == 6 ⇒ f = (\f → 1 + length a). f [1..5] == 6 ...
click here
... • The built-in search procedure is based on the generate and test paradigm, which becomes very inefficient for complex problems. Solutions are generated by non-deterministic choice, and then tested in a deterministic way. • The basic data structures in Prolog are un-interpreted (Herbrand) terms. The ...
... • The built-in search procedure is based on the generate and test paradigm, which becomes very inefficient for complex problems. Solutions are generated by non-deterministic choice, and then tested in a deterministic way. • The basic data structures in Prolog are un-interpreted (Herbrand) terms. The ...
On reasoning in networks with qualitative
... one formalism is the best in every situation. Instead, it is intended as some indication of which formalism is best for a particular situation. If a permissive formal ism is required, then evidence theory may be the best choice, while probability might be better when a more restrictive formalism is ...
... one formalism is the best in every situation. Instead, it is intended as some indication of which formalism is best for a particular situation. If a permissive formal ism is required, then evidence theory may be the best choice, while probability might be better when a more restrictive formalism is ...
Simple Stochastic Temporal Constraint Networks
... stochastically imprecise time points and intervals, as well as for reasoning with such events using imprecise metric time relations. But it does not support (among other things), the use topological time relations. Neither does it take advantage of the general framework of constraint-based approach ...
... stochastically imprecise time points and intervals, as well as for reasoning with such events using imprecise metric time relations. But it does not support (among other things), the use topological time relations. Neither does it take advantage of the general framework of constraint-based approach ...
Using human-machine dialogue to refine generalisation evaluation
... Among other works that deal with automatic generalisation evaluation, [3] proposes a generalisation evaluation method based on the definition of functions translating the expected evolution of geographic objects during generalisation. These functions are then aggregated in order to get a global qual ...
... Among other works that deal with automatic generalisation evaluation, [3] proposes a generalisation evaluation method based on the definition of functions translating the expected evolution of geographic objects during generalisation. These functions are then aggregated in order to get a global qual ...
On Maxsum Fair Cake Divisions
... Ri (x). The first part entails no loss in welfare. The second part may entail some loss, but allocating these intervals in a decreasing order of Ri (x) ensures that this is the lowest possible loss. In addition, if agent 1 receives value greater than v, it must come from additional intervals that ar ...
... Ri (x). The first part entails no loss in welfare. The second part may entail some loss, but allocating these intervals in a decreasing order of Ri (x) ensures that this is the lowest possible loss. In addition, if agent 1 receives value greater than v, it must come from additional intervals that ar ...
ppt
... • Pick a desired accuracy, , to limit the accepted range (VMAX-VMIN) of likely values of the root node; The smaller , the bigger the tree will get. • Pick a conspiracy threshold, NT, to determine what size of conspiracies are deemed sufficiently likely; The greater NT, the bigger the tree will get ...
... • Pick a desired accuracy, , to limit the accepted range (VMAX-VMIN) of likely values of the root node; The smaller , the bigger the tree will get. • Pick a conspiracy threshold, NT, to determine what size of conspiracies are deemed sufficiently likely; The greater NT, the bigger the tree will get ...
Calc/Cream - Related Web Pages
... Abstract. Calc/Cream is a constraint programming system with a spreadsheet front-end implemented on OpenOffice.org Calc and Java language. Constraint problems are described by users as cell expressions on a spreadsheet, and solutions are searched by the constraint solver and shown as cell values by ...
... Abstract. Calc/Cream is a constraint programming system with a spreadsheet front-end implemented on OpenOffice.org Calc and Java language. Constraint problems are described by users as cell expressions on a spreadsheet, and solutions are searched by the constraint solver and shown as cell values by ...
A Bayes Optimal Approach for Partitioning the Values of Categorical
... I: number of categorical values ni: number of instances for value i nij: number of instances for value i and class j K: number of groups k(i): index of the group containing value i nk: number of instances for group k nkj: number of instances for group k and class j The purpose of a grouping model is ...
... I: number of categorical values ni: number of instances for value i nij: number of instances for value i and class j K: number of groups k(i): index of the group containing value i nk: number of instances for group k nkj: number of instances for group k and class j The purpose of a grouping model is ...
LNCS 3258 - Full Dynamic Substitutability by SAT Encoding
... Full Dynamic Substitutability by SAT Encoding ...
... Full Dynamic Substitutability by SAT Encoding ...
ÚÙد ÙÙ
ÙÙ
٠تÙ
رÛÙ - Hassan Saneifar Professional Page
... In the second phase of the game, the man is replaced by a computer programmed to deceive the interrogator as the man did. It would e v e n b e p ro g r a m m e d t o m a k e mistakes and provide fuzzy answers in the way a human would. If the computer can fool the interrogator as often as the man did ...
... In the second phase of the game, the man is replaced by a computer programmed to deceive the interrogator as the man did. It would e v e n b e p ro g r a m m e d t o m a k e mistakes and provide fuzzy answers in the way a human would. If the computer can fool the interrogator as often as the man did ...
Condition interference in rats performing a choice task with switched
... all four reward-probability settings in each of the four blocks and (ii) not to repeat any of the settings. Each rat performed at least four blocks per day (i.e., per session) and any sessions consisting of fewer than five blocks were excluded from the analysis. In the fixed-reward condition, the re ...
... all four reward-probability settings in each of the four blocks and (ii) not to repeat any of the settings. Each rat performed at least four blocks per day (i.e., per session) and any sessions consisting of fewer than five blocks were excluded from the analysis. In the fixed-reward condition, the re ...
Document
... Information is the life blood of modern society. Decisions are based on information. More often than not, decision-relevant information is imperfect in the sense that it is in part imprecise and/or uncertain and/or incomplete and/or conflicting and/or partially true. There is a long list of methods ...
... Information is the life blood of modern society. Decisions are based on information. More often than not, decision-relevant information is imperfect in the sense that it is in part imprecise and/or uncertain and/or incomplete and/or conflicting and/or partially true. There is a long list of methods ...
Full Dynamic Substitutability by SAT Encoding
... only if every solution in which v = a remains a solution when b is substituted for a (but not necessarily vice-versa) [15]. Substitutability is weaker than interchangeability. Note that the term weaker is used in the interchangeability literature to mean achieves more problem reduction; the weakness ...
... only if every solution in which v = a remains a solution when b is substituted for a (but not necessarily vice-versa) [15]. Substitutability is weaker than interchangeability. Note that the term weaker is used in the interchangeability literature to mean achieves more problem reduction; the weakness ...
Full Text - Harvard University
... general, not specific, and motivational, not directing,' thus energizing behavior in a nonspecific way (Bolles 1975). Various needs such as food or water deprivation constitute different ways of activating drive, but drive itself is singular. Moreover, he postulated that the internal buildup of driv ...
... general, not specific, and motivational, not directing,' thus energizing behavior in a nonspecific way (Bolles 1975). Various needs such as food or water deprivation constitute different ways of activating drive, but drive itself is singular. Moreover, he postulated that the internal buildup of driv ...
Reinforcement Learning in the Presence of Rare Events
... agents that operate in complex stochastic environments. In reinforcement learning, environments are commonly represented as Markov decision processes, which are characterized by a set of states that an agent can find itself in and sets of actions that an agent can take at each state. An agent intera ...
... agents that operate in complex stochastic environments. In reinforcement learning, environments are commonly represented as Markov decision processes, which are characterized by a set of states that an agent can find itself in and sets of actions that an agent can take at each state. An agent intera ...
Solving Large Markov Decision Processes (depth paper)
... or function) schemata and action schemata defined over object classes instead of using explicit states and actions. This representation not only makes it possible to describe large state-space problems, but is also capable of specifying similar decision-making problems (related MDPs) by using one si ...
... or function) schemata and action schemata defined over object classes instead of using explicit states and actions. This representation not only makes it possible to describe large state-space problems, but is also capable of specifying similar decision-making problems (related MDPs) by using one si ...
X is A - Wiki Index
... • X is an n-ary variable, X= (X1, …, Xn) • X is a proposition, e.g., Leslie is tall • X is a function of another variable: X=f(Y) • X is conditioned on another variable, X/Y • X has a structure, e.g., X= Location ...
... • X is an n-ary variable, X= (X1, …, Xn) • X is a proposition, e.g., Leslie is tall • X is a function of another variable: X=f(Y) • X is conditioned on another variable, X/Y • X has a structure, e.g., X= Location ...
A Planning Heuristic Based on Causal Graph Analysis
... cations, and solid arcs correspond to roads. Note that location D has four incoming but no outgoing roads, and hence can be entered but not left. The objective is to move a cargo item located at E to location B, as indicated by the dashed arrow. Two trucks initially located at C and F may be used to ...
... cations, and solid arcs correspond to roads. Note that location D has four incoming but no outgoing roads, and hence can be entered but not left. The objective is to move a cargo item located at E to location B, as indicated by the dashed arrow. Two trucks initially located at C and F may be used to ...
Generalized Weighted Fuzzy Expected Values in
... the “weighting process” by weights w(|χi − M T V |). Both postulates are combined into a normalized sum χi w(|χi − s|)g ` ({xi }) presented in Eq. (4). This means that M T V ≡ W F EVg` (the solution of (5) is invariant with respect to the “weight” function constructed by the FSK principle which is c ...
... the “weighting process” by weights w(|χi − M T V |). Both postulates are combined into a normalized sum χi w(|χi − s|)g ` ({xi }) presented in Eq. (4). This means that M T V ≡ W F EVg` (the solution of (5) is invariant with respect to the “weight” function constructed by the FSK principle which is c ...
A Methodology for Medical Diagnosis based on Fuzzy Logic
... has been extended to handle the concept of partial truth – truth values between "completely true" and "completely false". It was introduced by Zadeh in 1965 [7] as a means to model the uncertainty of natural language. In this paper we develop a fuzzy expert system that uses a collection of fuzzy mem ...
... has been extended to handle the concept of partial truth – truth values between "completely true" and "completely false". It was introduced by Zadeh in 1965 [7] as a means to model the uncertainty of natural language. In this paper we develop a fuzzy expert system that uses a collection of fuzzy mem ...