ppt - Department of Mathematics and Statistics
... • By convention, we will try to use lower-case letters at the beginning of the alphabet to denote symbols, and lower-case letters near the end of the alphabet to represent strings. ...
... • By convention, we will try to use lower-case letters at the beginning of the alphabet to denote symbols, and lower-case letters near the end of the alphabet to represent strings. ...
Problem 3a: Hyperbolic PDE
... undamped oscillations. Since the hyperbolic PDE has 2 second order derivatives with respect to time and 2 second order derivatives with respect to position there needs to be an additional boundary condition. The 2 with respect to position are where u(0,t)=u(1,t)=0. The boundary conditions with respe ...
... undamped oscillations. Since the hyperbolic PDE has 2 second order derivatives with respect to time and 2 second order derivatives with respect to position there needs to be an additional boundary condition. The 2 with respect to position are where u(0,t)=u(1,t)=0. The boundary conditions with respe ...
CS3378 FINAL EXAM SPRING 2000 C. HAZLEWOOD 1. Sketch
... rewrite the string until it is in the language. The rewrite rules will not let us generate any strings except the ones in the language. We will distinguish between terminal symbols, which appear in strings in the language, and non-terminal symbols, which are ”helpers”. The start symbol is a non-term ...
... rewrite the string until it is in the language. The rewrite rules will not let us generate any strings except the ones in the language. We will distinguish between terminal symbols, which appear in strings in the language, and non-terminal symbols, which are ”helpers”. The start symbol is a non-term ...
mcnair 2003 poster template
... The saw tooth formations from bowing the instrument at the note regarded as the middle b will be established from both the D and A strings either from past mathematical data, if available, or will be estimated using a violin and a computer program that will estimate this saw tooth formation from the ...
... The saw tooth formations from bowing the instrument at the note regarded as the middle b will be established from both the D and A strings either from past mathematical data, if available, or will be estimated using a violin and a computer program that will estimate this saw tooth formation from the ...
(5 points) Problem 2c Solution (5 points)
... Now consider Lk+1 . By the inductive hypothesis there is a DFA with Ω(2k ) states for Lk . We can modify this DFA to decide Lk+1 : For each accepting state of this DFA, change it to an unaccepting state, remove its outgoing transitions, and create two new accepting states for it to transition to (on ...
... Now consider Lk+1 . By the inductive hypothesis there is a DFA with Ω(2k ) states for Lk . We can modify this DFA to decide Lk+1 : For each accepting state of this DFA, change it to an unaccepting state, remove its outgoing transitions, and create two new accepting states for it to transition to (on ...
Bethe Ansatz in AdS/CFT: from local operators to classical
... Noether charges are determined by asymptotic behaviour of quasimomentum: ...
... Noether charges are determined by asymptotic behaviour of quasimomentum: ...
Bethe Ansatz and AdS/CFT
... • BMN limit Berenstein, Maldacena, Nastase’02; Metsaev’02;… • Near-BMN limit Callan, Lee,McLoughlin,Schwarz,Swanson,Wu’03;… • Quantum corrections to classical string solutions Frolov, Tseytlin’03 Frolov, Park, Tsetlin’04 Park, Tirziu, Tseytlin’05 ...
... • BMN limit Berenstein, Maldacena, Nastase’02; Metsaev’02;… • Near-BMN limit Callan, Lee,McLoughlin,Schwarz,Swanson,Wu’03;… • Quantum corrections to classical string solutions Frolov, Tseytlin’03 Frolov, Park, Tsetlin’04 Park, Tirziu, Tseytlin’05 ...
Java Programming 2 – Lecture #14 –
... The default clone operation simply instantiates a new object of the appropriate type, and copies the values in the fields across to this new object. This is similar to the copy constructor outlined ab ...
... The default clone operation simply instantiates a new object of the appropriate type, and copies the values in the fields across to this new object. This is similar to the copy constructor outlined ab ...
Lecture 2 Slides
... This is a word we make up to identify part of the program (in this case, the program itself) Identifiers must be a single word ...
... This is a word we make up to identify part of the program (in this case, the program itself) Identifiers must be a single word ...
String Combiners in SolarEdge Systems, North America
... The intent is to provide overcurrent protection for circuits connected to more than one electrical source. All sources of current need to be considered: multiple series strings of PV modules connected in parallel to the inverter as well as the string inverter itself. SolarEdge inverters have been ve ...
... The intent is to provide overcurrent protection for circuits connected to more than one electrical source. All sources of current need to be considered: multiple series strings of PV modules connected in parallel to the inverter as well as the string inverter itself. SolarEdge inverters have been ve ...
Final-F10
... 1. (25) Write a complete, working, one-class application that reads in exactly 5 Strings from the keyboard, each on a separate line, and then prints the Strings out in a column in reverse order. You must use an array in an essential way here. An example: if the entered strings are now is surely the ...
... 1. (25) Write a complete, working, one-class application that reads in exactly 5 Strings from the keyboard, each on a separate line, and then prints the Strings out in a column in reverse order. You must use an array in an essential way here. An example: if the entered strings are now is surely the ...
Introduction to Java 2 Programming
... • Must use a combination of modifiers to make a constant – static – indicates a class variable. It’s not owned by an individual object – final – to make a variable with a single value. Can be assigned to once – E.g. public final static int MY_CONSTANT = 0; ...
... • Must use a combination of modifiers to make a constant – static – indicates a class variable. It’s not owned by an individual object – final – to make a variable with a single value. Can be assigned to once – E.g. public final static int MY_CONSTANT = 0; ...
SIMPLE SYSTEM PLANNING WITH REFUsol
... of 555 Wp per kilogram. This goal can only be achieved by focusing consistently on necessary functionalities. Not least, this is demonstrated by the technological development of the precise, highly efficient MPP tracker installed in every REFUsol device. This article explains how your solar system c ...
... of 555 Wp per kilogram. This goal can only be achieved by focusing consistently on necessary functionalities. Not least, this is demonstrated by the technological development of the precise, highly efficient MPP tracker installed in every REFUsol device. This article explains how your solar system c ...
JavaScriptLesson04
... How to use built in JavaScript functions to format input data for arithmetic (parseInt, parseFloat, and eval) ...
... How to use built in JavaScript functions to format input data for arithmetic (parseInt, parseFloat, and eval) ...
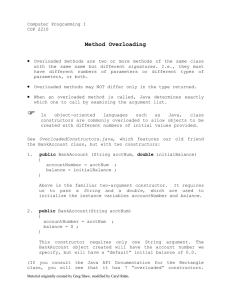
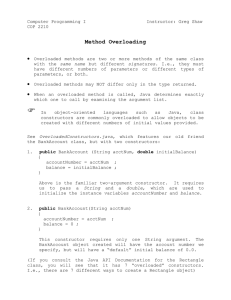
Method Overloading
... Overloaded methods are two or more methods of the same class with the same name but different signatures. I.e., they must have different numbers of parameters or different types of parameters, or both. ...
... Overloaded methods are two or more methods of the same class with the same name but different signatures. I.e., they must have different numbers of parameters or different types of parameters, or both. ...
Method Overloading
... Overloaded methods are two or more methods of the same class with the same name but different signatures. I.e., they must have different numbers of parameters or different types of parameters, or both. ...
... Overloaded methods are two or more methods of the same class with the same name but different signatures. I.e., they must have different numbers of parameters or different types of parameters, or both. ...
ceng 562 machine learning
... select individuals to reproduce mate pairs at random apply crossover operator apply mutation operator evaluate each individual's fitness ...
... select individuals to reproduce mate pairs at random apply crossover operator apply mutation operator evaluate each individual's fitness ...
1. Automata - CIS @ Temple University
... chosen from some alphabet, such as 01001, cis, or ϵ (epsilon, empty string) The length of a string is the number of symbols in it, so |01001| = 5, |ϵ| = 0 ...
... chosen from some alphabet, such as 01001, cis, or ϵ (epsilon, empty string) The length of a string is the number of symbols in it, so |01001| = 5, |ϵ| = 0 ...
String (computer science)

In computer programming, a string is traditionally a sequence of characters, either as a literal constant or as some kind of variable. The latter may allow its elements to be mutated and the length changed, or it may be fixed (after creation). A string is generally understood as a data type and is often implemented as an array of bytes (or words) that stores a sequence of elements, typically characters, using some character encoding. A string may also denote more general arrays or other sequence (or list) data types and structures.Depending on programming language and precise data type used, a variable declared to be a string may either cause storage in memory to be statically allocated for a predetermined maximum length or employ dynamic allocation to allow it to hold variable number of elements.When a string appears literally in source code, it is known as a string literal or an anonymous string.In formal languages, which are used in mathematical logic and theoretical computer science, a string is a finite sequence of symbols that are chosen from a set called an alphabet.