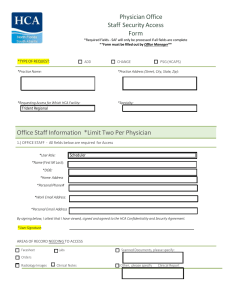
Computer and System Logging Policy
... 3. Scope This policy applies to all [LEP] staff that create, deploy, or support application and system software. ...
... 3. Scope This policy applies to all [LEP] staff that create, deploy, or support application and system software. ...
Chapter 05
... Mandatory (MAC): decisions made beyond the end user. Discretionary (DAC): end user decides access. Non-Discretionary: Role based access control. Roles define access. Content/Context dependent: check an additional context before allowing access such as time, or if accessing their records. Cen ...
... Mandatory (MAC): decisions made beyond the end user. Discretionary (DAC): end user decides access. Non-Discretionary: Role based access control. Roles define access. Content/Context dependent: check an additional context before allowing access such as time, or if accessing their records. Cen ...
answer-sheet-7540-040-7630-345-b_
... having just a password you will also have scanners on the pc or laptop that will scan your finger print only letting you access into your account on your PC. This is good because you are the only person with your fingerprint or retina, therefore no one else will be able to get access into your compu ...
... having just a password you will also have scanners on the pc or laptop that will scan your finger print only letting you access into your account on your PC. This is good because you are the only person with your fingerprint or retina, therefore no one else will be able to get access into your compu ...
Operating System Security Fundamentals
... Digital Authentication Mechanism • Digital certificates: digital passport that identifies and verifies holder of certificate • Digital token (security token): – Small electronic device – Displays a number unique to the token holder; used with the holder’s PIN as a password – Uses a different passwo ...
... Digital Authentication Mechanism • Digital certificates: digital passport that identifies and verifies holder of certificate • Digital token (security token): – Small electronic device – Displays a number unique to the token holder; used with the holder’s PIN as a password – Uses a different passwo ...
ACCESS CONTROL OPTIONS FOR WIRED NETWORKS
... device visibility have become valuable components during the authentication and authorization phase. This data is then used to enforce policies on wireless and wired networks. But, the growth of IoT devices, that are not associated with a specific user or group, is now causing security concerns on t ...
... device visibility have become valuable components during the authentication and authorization phase. This data is then used to enforce policies on wireless and wired networks. But, the growth of IoT devices, that are not associated with a specific user or group, is now causing security concerns on t ...
Security Considerations for RemotelyAnywhere
... has been authenticated RemotelyAnywhere impersonates them towards the operating system when servicing requests. This ensures that the user is only able to perform actions that their Windows credentials allow. There is always the chance that someone will gain access to the password by a brute-force m ...
... has been authenticated RemotelyAnywhere impersonates them towards the operating system when servicing requests. This ensures that the user is only able to perform actions that their Windows credentials allow. There is always the chance that someone will gain access to the password by a brute-force m ...
abstract - Chennaisunday.com
... the Internet. To accommodate the scale of transactions across the Internet, some of ...
... the Internet. To accommodate the scale of transactions across the Internet, some of ...
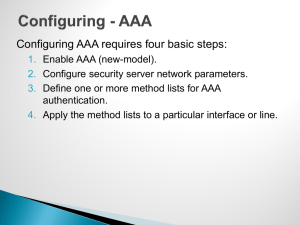
Router/Switch Security
... • The NTP source interface has been configured • One or more NTP servers have been configured. • ACL has been established to permit NTP to device. ...
... • The NTP source interface has been configured • One or more NTP servers have been configured. • ACL has been established to permit NTP to device. ...
file - ScholarSphere
... servers and do they utilize offsite storage Do they require users to utilize complex passwords; how frequently are users required to change passwords; how often can a previous password be reused Do they have anti-virus software installed on all users’ computers; on all file servers; how frequently d ...
... servers and do they utilize offsite storage Do they require users to utilize complex passwords; how frequently are users required to change passwords; how often can a previous password be reused Do they have anti-virus software installed on all users’ computers; on all file servers; how frequently d ...
creamery upgrades with movicon scada
... critical principle for maintaining the highest environmental standards. Again, all data is recorded. Redundancy The main control room also accommodates two additional PC stations, which run Windows 7 with Movicon 11 setup in a redundant configuration. Both PCs are constantly updated and each backs u ...
... critical principle for maintaining the highest environmental standards. Again, all data is recorded. Redundancy The main control room also accommodates two additional PC stations, which run Windows 7 with Movicon 11 setup in a redundant configuration. Both PCs are constantly updated and each backs u ...
IT Security, SQL Server and You!
... Store critical data on systems located in secure rooms or datacenters. ...
... Store critical data on systems located in secure rooms or datacenters. ...
Distributed System Concepts and Architectures
... assigned a sensitivity label. The labels are used as the basis for mandatory access control decisions. ...
... assigned a sensitivity label. The labels are used as the basis for mandatory access control decisions. ...
Session 1 Framework
... • Create an archive of original media, configuration files, and security-related patches for all router and host operating systems and application software versions • Ensure that backup tools and procedures are working • Create a database of contact information • Select and install tools to use when ...
... • Create an archive of original media, configuration files, and security-related patches for all router and host operating systems and application software versions • Ensure that backup tools and procedures are working • Create a database of contact information • Select and install tools to use when ...
How Organizations Are Using Fortscale`s User Behavior Analytics
... A unique aspect of Fortscale is the ability to provide rich context for the analyst by automatically labeling users and machines based on many observed behaviors, helping analysts to quickly prioritize events for investigation. One account label applied is “service” which indicates an account whose ...
... A unique aspect of Fortscale is the ability to provide rich context for the analyst by automatically labeling users and machines based on many observed behaviors, helping analysts to quickly prioritize events for investigation. One account label applied is “service” which indicates an account whose ...
Chapter 05
... Some inference detection algorithm is needed for either of these approaches Progress has been made in devising specific inference detection techniques for multilevel secure databases and statistical databases ...
... Some inference detection algorithm is needed for either of these approaches Progress has been made in devising specific inference detection techniques for multilevel secure databases and statistical databases ...
Presentation
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
Chapter 19
... • Authentication: protocol used to define an exchange between a user and an AS • Access control: function that enforces the use of the authentication function, routes messages properly and facilitates key exchange. ...
... • Authentication: protocol used to define an exchange between a user and an AS • Access control: function that enforces the use of the authentication function, routes messages properly and facilitates key exchange. ...
Database Security
... • User authentication - verifying the identity of users • Operating system uses user profiles, user ids, passwords, authentication procedures, badges, keys, or physical characteristics of the user • Additional authentication can be required to access the database-additional user ID, PW ...
... • User authentication - verifying the identity of users • Operating system uses user profiles, user ids, passwords, authentication procedures, badges, keys, or physical characteristics of the user • Additional authentication can be required to access the database-additional user ID, PW ...
Lecture 10 - The University of Texas at Dallas
... A person can log into the system multiple times from different parts of the country and cast his/her vote Insufficient techniques for ensuring that a person can vote only once The systems may be attacked and compromised Solutions are being developed Johns Hopkins University is one of the l ...
... A person can log into the system multiple times from different parts of the country and cast his/her vote Insufficient techniques for ensuring that a person can vote only once The systems may be attacked and compromised Solutions are being developed Johns Hopkins University is one of the l ...
Section for introduction % \section{Introduction} Over the last several
... Over the last several years, innovations in the advancement of computing and communication hardware have allowed mobile phones to evolve into affordable general purpose computing platforms. In the fourth quarter of 2010 alone, 101.2 million smart phones were sold worldwide, a growth of 88.6\% from t ...
... Over the last several years, innovations in the advancement of computing and communication hardware have allowed mobile phones to evolve into affordable general purpose computing platforms. In the fourth quarter of 2010 alone, 101.2 million smart phones were sold worldwide, a growth of 88.6\% from t ...
Overview of Operating Systems Security Features
... Overview of Operating Systems Security Features - LINUX Introduction A key advantage of LINUX desktop operating system (OS) is its low cost and ease of customization to environment and/or solutions specific requirements, but this can also present security risks. A LINUX desktop that is part of the G ...
... Overview of Operating Systems Security Features - LINUX Introduction A key advantage of LINUX desktop operating system (OS) is its low cost and ease of customization to environment and/or solutions specific requirements, but this can also present security risks. A LINUX desktop that is part of the G ...
Frameworks, Standards and Regulations
... ICOFR Controls must be audited externally CEOs & CFOs are held accountable for (reports generated by systems and applications) ...
... ICOFR Controls must be audited externally CEOs & CFOs are held accountable for (reports generated by systems and applications) ...
Access control
_before_allowing_a_driver_to_enter_the_gate_at_U.S._Fleet_Activities_Sasebo,_Japan.jpg?width=300)
In the fields of physical security and information security, access control is the selective restriction of access to a place or other resource. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.Locks and login credentials are two analogous mechanisms of access control.