Risk Mgmt - WCU Computer Science
... information system and the POTENTIAL IMPACT the loss of information or capabilities of a system would have. The resulting analysis is used as a basis for identifying appropriate and cost-effective counter-measures. (Definition from National Information Systems Security (INFOSEC) Glossary, NSTISSI No ...
... information system and the POTENTIAL IMPACT the loss of information or capabilities of a system would have. The resulting analysis is used as a basis for identifying appropriate and cost-effective counter-measures. (Definition from National Information Systems Security (INFOSEC) Glossary, NSTISSI No ...
Asset Related Risk
... – Their vulnerabilities and likelihood of exploitation • Risk Management involves the identification, selection and adoption of security measures justified by – The identified risks to assets – The reduction of these risks to acceptable levels ...
... – Their vulnerabilities and likelihood of exploitation • Risk Management involves the identification, selection and adoption of security measures justified by – The identified risks to assets – The reduction of these risks to acceptable levels ...
Chapter 1: Security Problems in Computing
... The answer is that yes there is a problem and always has been since the early days when we discovered the operating system and allowed more than one programmer at a time access to the same computer. Easier access to computers has facilitated much of modern commerce, including e-mail and just-in-time ...
... The answer is that yes there is a problem and always has been since the early days when we discovered the operating system and allowed more than one programmer at a time access to the same computer. Easier access to computers has facilitated much of modern commerce, including e-mail and just-in-time ...
Financial Reporting: The Institutional Setting
... disclosure of information, and denial of service. Then, it is important to “Implement measures which will protect your assets in a cost-effective manner [and] review the process continuously and make improvements each time a weakness is found.” Every enterprise should have a security policy comprise ...
... disclosure of information, and denial of service. Then, it is important to “Implement measures which will protect your assets in a cost-effective manner [and] review the process continuously and make improvements each time a weakness is found.” Every enterprise should have a security policy comprise ...
Federal Bio
... Earl Crane, CISSP, CISM Department of Homeland Security Mr. Crane is located in Washington, DC where works for the Department of Homeland Security. Previously Mr. Crane was a Senior Information Security Consultant with Foundstone, a wholly owned subsidiary of McAfee, Inc. There he created and led th ...
... Earl Crane, CISSP, CISM Department of Homeland Security Mr. Crane is located in Washington, DC where works for the Department of Homeland Security. Previously Mr. Crane was a Senior Information Security Consultant with Foundstone, a wholly owned subsidiary of McAfee, Inc. There he created and led th ...
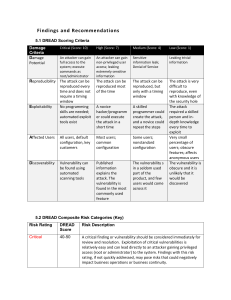
Findings and Recommendations
... person and indepth knowledge every time to exploit Very small percentage of users; obscure features; affects anonymous users The vulnerability is obscure and it is unlikely that it would be discovered ...
... person and indepth knowledge every time to exploit Very small percentage of users; obscure features; affects anonymous users The vulnerability is obscure and it is unlikely that it would be discovered ...
Addressing security threats and vulnerabilities
... 3. Estimate of the value of revenue that could be generated from the asset 4. Compare to a similar asset’s value Assign a likelihood that an event will occur that could cause loss or damage: – Use a scale such as high, moderate, low Assign values to a risk based on both the possible damage and the l ...
... 3. Estimate of the value of revenue that could be generated from the asset 4. Compare to a similar asset’s value Assign a likelihood that an event will occur that could cause loss or damage: – Use a scale such as high, moderate, low Assign values to a risk based on both the possible damage and the l ...
Department of Information Resources, State
... What can you do? • Have a security policy • Take a realistic look at your risks • Prepare a response team ...
... What can you do? • Have a security policy • Take a realistic look at your risks • Prepare a response team ...
Cyber Risks of Manufacturers Limiting the Risk Factors of
... as well as new requirements for personal protective equipment in order to limit fallrelated injuries in the workplace. ...
... as well as new requirements for personal protective equipment in order to limit fallrelated injuries in the workplace. ...
Network Security Chapter 14
... ____ 22. the care that a reasonable person would exercise under the circumstances ____ 23. any investigation into suspicious employee conduct will examine all material facts ____ 24. a set of management statements that defines an organization’s philosophy of how to safeguard its information ____ 25. ...
... ____ 22. the care that a reasonable person would exercise under the circumstances ____ 23. any investigation into suspicious employee conduct will examine all material facts ____ 24. a set of management statements that defines an organization’s philosophy of how to safeguard its information ____ 25. ...
NIST 800-30 Risk Assessment Steps
... General Risk Assessment Overview Risk assessments can be completed by using many different methodologies. There is no single methodology that will work for all organizations and all situations. The following steps represent key steps to complete a comprehensive risk assessment program as outlined in ...
... General Risk Assessment Overview Risk assessments can be completed by using many different methodologies. There is no single methodology that will work for all organizations and all situations. The following steps represent key steps to complete a comprehensive risk assessment program as outlined in ...
D1S1_TSV404_Course_Intro_2011_v1
... Moderate Risk Level ■ Exploitation of the technical or procedural vulnerability will significantly impact the confidentiality, integrity, and/or availability of the system, application, or data ■ Exploitation of the vulnerability may cause moderate financial loss or public embarrassment ■ The threa ...
... Moderate Risk Level ■ Exploitation of the technical or procedural vulnerability will significantly impact the confidentiality, integrity, and/or availability of the system, application, or data ■ Exploitation of the vulnerability may cause moderate financial loss or public embarrassment ■ The threa ...
file - ScholarSphere
... implemented primarily to defend against external threats. However, not only are insiders aware of the policies, procedures, and technology used in their organizations, but they are often also aware of their vulnerabilities, such as loosely enforced policies and procedures or exploitable technical fl ...
... implemented primarily to defend against external threats. However, not only are insiders aware of the policies, procedures, and technology used in their organizations, but they are often also aware of their vulnerabilities, such as loosely enforced policies and procedures or exploitable technical fl ...
Review Questions
... D. is any person or thing with the power to carry out a threat against an asset 6. _____ constructs scenarios of the types of threats that assets can face in order to learn who the attackers are, why they attack, and what types of attacks may occur A. Risk assessment B. Attack stems C. Vulnerability ...
... D. is any person or thing with the power to carry out a threat against an asset 6. _____ constructs scenarios of the types of threats that assets can face in order to learn who the attackers are, why they attack, and what types of attacks may occur A. Risk assessment B. Attack stems C. Vulnerability ...
41 Annual Conference of the IEEE Industrial Electronics Society
... applications and industrial environments; Privacy-preserving enabled industrial informatics software systems; Risk assessment in service-oriented industrial systems; and designing for information security in industrial informatics. The work allows the notion of trust, privacy, risk and information s ...
... applications and industrial environments; Privacy-preserving enabled industrial informatics software systems; Risk assessment in service-oriented industrial systems; and designing for information security in industrial informatics. The work allows the notion of trust, privacy, risk and information s ...
IT risk management

IT risk management is the application of risk management methods to Information technology in order to manage IT risk, i.e.:The business risk associated with the use, ownership, operation, involvement, influence and adoption of IT within an enterprise or organizationIT risk management can be considered a component of a wider enterprise risk management system.The establishment, maintenance and continuous update of an ISMS provide a strong indication that a company is using a systematic approach for the identification, assessment and management of information security risks.Different methodologies have been proposed to manage IT risks, each of them divided in processes and steps.According to Risk IT, it encompasses not just only the negative impact of operations and service delivery which can bring destruction or reduction of the value of the organization, but also the benefit\value enabling risk associated to missing opportunities to use technology to enable or enhance business or the IT project management for aspects like overspending or late delivery with adverse business impact.Because risk is strictly tied to uncertainty, Decision theory should be applied to manage risk as a science, i.e. rationally making choices under uncertainty.Generally speaking, risk is the product of likelihood times impact (Risk = Likelihood * Impact).The measure of an IT risk can be determined as a product of threat, vulnerability and asset values:Risk = Threat * Vulnerability * AssetA more current Risk management framework for IT Risk would be the TIK framework:Risk = ((Vulnerability * Threat) / Counter Measure) * Asset Value at Risk IT Risk