DutyCon: A dynamic duty-cycle control approach to end
... GUOLIANG XING, Michigan State University ...
... GUOLIANG XING, Michigan State University ...
MRP: Wireless mesh networks routing protocol Jangeun Jun, Mihail L. Sichitiu
... In a class of their own, the geographical routing algorithms (e.g., LAR [32], DREAM [33], and ZRP [47]) take advantage of node location information (that can be relatively inexpensive to distribute [34]) to reduce routing overhead and improve the performance of the protocol. Geocasting [48,49] takes ...
... In a class of their own, the geographical routing algorithms (e.g., LAR [32], DREAM [33], and ZRP [47]) take advantage of node location information (that can be relatively inexpensive to distribute [34]) to reduce routing overhead and improve the performance of the protocol. Geocasting [48,49] takes ...
pdf
... devices located in a single large room. Results show that 100 concurrent web sessions degrade the performance by only 5%. Golmie et al. [19] use a detailed MAC and PHY simulation framework to evaluate the impact of interference for a pair of 802.11b nodes and a pair of Bluetooth nodes. Similar resul ...
... devices located in a single large room. Results show that 100 concurrent web sessions degrade the performance by only 5%. Golmie et al. [19] use a detailed MAC and PHY simulation framework to evaluate the impact of interference for a pair of 802.11b nodes and a pair of Bluetooth nodes. Similar resul ...
IP: Addresses and Forwarding - RPI ECSE
... When the connection between two neighbors comes up, the routers must wait for their LS DBs to be synchronized. Else routing loops and black holes due to inconsistency OSPF technique: Source sends only LSA headers, then Neighbor requests LSAs that are more recent. Those LSAs are sent over A ...
... When the connection between two neighbors comes up, the routers must wait for their LS DBs to be synchronized. Else routing loops and black holes due to inconsistency OSPF technique: Source sends only LSA headers, then Neighbor requests LSAs that are more recent. Those LSAs are sent over A ...
Emulation of RDRN on an ATM-Testbed and a Comparative
... IP over ATM specification says that the MTU cannot be larger than 9180 bytes; hence the CLIP can pass a packet of the above size to the “glue_layer”. Hence, when the DLC layer would attach its own header and trailer, it would cause an overflow on the ENI card. In the above case the segmentation ...
... IP over ATM specification says that the MTU cannot be larger than 9180 bytes; hence the CLIP can pass a packet of the above size to the “glue_layer”. Hence, when the DLC layer would attach its own header and trailer, it would cause an overflow on the ENI card. In the above case the segmentation ...
3214W17Ch4
... Priority: identify priority among datagrams in flow Flow Label: identify datagrams in same “flow.” (concept of“flow” not well defined). Next header: identify upper layer protocol for data ...
... Priority: identify priority among datagrams in flow Flow Label: identify datagrams in same “flow.” (concept of“flow” not well defined). Next header: identify upper layer protocol for data ...
Institutionen f r systemteknik ö
... A Tactical Data Link (TDL) system has been deployed in many military missions as a winning strategy. The performance of a TDL system is governed by the MAC protocol. The MAC protocol that is able to provide more flexibility and high quality of services is more desirable. However, most MAC protocols ...
... A Tactical Data Link (TDL) system has been deployed in many military missions as a winning strategy. The performance of a TDL system is governed by the MAC protocol. The MAC protocol that is able to provide more flexibility and high quality of services is more desirable. However, most MAC protocols ...
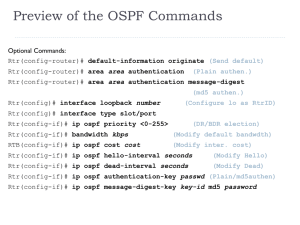
OSPF
... Cisco’s OSPF metric is based on bandwidth RIP is based on hop count IGRP/EIGRP bandwidth, delay, reliability, load OSPF only sends out changes when they occur. RIP sends entire routing table every 30 seconds, IGRP every 90 seconds Extra: With OSPF, a router does flood its own LSAs when it ag ...
... Cisco’s OSPF metric is based on bandwidth RIP is based on hop count IGRP/EIGRP bandwidth, delay, reliability, load OSPF only sends out changes when they occur. RIP sends entire routing table every 30 seconds, IGRP every 90 seconds Extra: With OSPF, a router does flood its own LSAs when it ag ...
Gossip-based Signaling Dissemination Extension for Next Steps In
... during its whole operating time to find and update information and metrics about all other GIST nodes present in the network. The discovery algorithm is gossip-based: all nodes periodically communicate with a randomly-selected neighbor and exchange (bounded) peering information in order to improve t ...
... during its whole operating time to find and update information and metrics about all other GIST nodes present in the network. The discovery algorithm is gossip-based: all nodes periodically communicate with a randomly-selected neighbor and exchange (bounded) peering information in order to improve t ...
route
... construct its routing table Routing table in OSPF includes the cost of reaching each network in the area To find the cost of reaching network outside of the area, the routers use the ...
... construct its routing table Routing table in OSPF includes the cost of reaching each network in the area To find the cost of reaching network outside of the area, the routers use the ...
Distance Vector Routing Protocols
... 1058. It has the following key characteristics: Hop count is used as the metric for path selection. If the hop count for a network is greater than 15, RIP cannot supply a route to that network. Routing updates are broadcast or multicast every 30 seconds, by ...
... 1058. It has the following key characteristics: Hop count is used as the metric for path selection. If the hop count for a network is greater than 15, RIP cannot supply a route to that network. Routing updates are broadcast or multicast every 30 seconds, by ...
GMPLS-based provisioning of Ethernet connections over WSON with Quality of Service Ph.D. Thesis
... bandwidth are intelligently reused when accommodating and serving new upper-layer LSPs. By doing so, the established lower-layer LSPs form a Virtual Network Topology (VNT) for the provisioning of CO-Ethernet services. This yields to improve the scalability and efficiency of the network resource uti ...
... bandwidth are intelligently reused when accommodating and serving new upper-layer LSPs. By doing so, the established lower-layer LSPs form a Virtual Network Topology (VNT) for the provisioning of CO-Ethernet services. This yields to improve the scalability and efficiency of the network resource uti ...
Secure routing for structured peer-to-peer overlay networks
... closed system of sufficiently large scale, it may be unrealistic to assume that none of the participating nodes have been compromised by attackers. Thus, structured overlays must be robust to a variety of security attacks, including the case where a fraction of the participating nodes act maliciousl ...
... closed system of sufficiently large scale, it may be unrealistic to assume that none of the participating nodes have been compromised by attackers. Thus, structured overlays must be robust to a variety of security attacks, including the case where a fraction of the participating nodes act maliciousl ...
wireless mesh networks
... Packet header size grows with route length Flood of route requests may potentially reach all nodes Care must be taken to avoid collisions between route requests propagated by neighboring nodes – insertion of random delays before forwarding RREQ ...
... Packet header size grows with route length Flood of route requests may potentially reach all nodes Care must be taken to avoid collisions between route requests propagated by neighboring nodes – insertion of random delays before forwarding RREQ ...
No Slide Title
... • Build virtual overlay is built as a graph with known properties – N-dimensional (incomplete) hypercube – Delaunay triangulation ...
... • Build virtual overlay is built as a graph with known properties – N-dimensional (incomplete) hypercube – Delaunay triangulation ...
hypercast-talk - University of Virginia, Department of Computer
... • Build virtual overlay is built as a graph with known properties – N-dimensional (incomplete) hypercube – Delaunay triangulation ...
... • Build virtual overlay is built as a graph with known properties – N-dimensional (incomplete) hypercube – Delaunay triangulation ...
ppt
... Overlay Routing • Basic idea: • Treat multiple hops through IP network as one hop in overlay network • Run routing protocol on overlay nodes ...
... Overlay Routing • Basic idea: • Treat multiple hops through IP network as one hop in overlay network • Run routing protocol on overlay nodes ...
Chord: A Scalable Peer-to-peer Lookup Service for Internet Applications Ion Stoica
... on real-world geographic location information to route its queries; Chord maps its nodes to an artificial one-dimensional space within which routing is carried out by an algorithm similar to Grid’s. Chord can be used as a lookup service to implement a variety of systems, as discussed in Section 3. I ...
... on real-world geographic location information to route its queries; Chord maps its nodes to an artificial one-dimensional space within which routing is carried out by an algorithm similar to Grid’s. Chord can be used as a lookup service to implement a variety of systems, as discussed in Section 3. I ...
Chord: A Scalable Peer-to-peer Lookup Service for Internet Applications Ion Stoica
... on real-world geographic location information to route its queries; Chord maps its nodes to an artificial one-dimensional space within which routing is carried out by an algorithm similar to Grid’s. Chord can be used as a lookup service to implement a variety of systems, as discussed in Section 3. I ...
... on real-world geographic location information to route its queries; Chord maps its nodes to an artificial one-dimensional space within which routing is carried out by an algorithm similar to Grid’s. Chord can be used as a lookup service to implement a variety of systems, as discussed in Section 3. I ...
Chord: A Scalable Peer-to-Peer Lookup Protocol for Internet Applications
... Chord in two main ways. First, the Chord library provides a function that yields the IP address of the node responsible for the key. Second, the Chord software on each node notifies the application of changes in the set of keys that the node is responsible for. This allows the application software t ...
... Chord in two main ways. First, the Chord library provides a function that yields the IP address of the node responsible for the key. Second, the Chord software on each node notifies the application of changes in the set of keys that the node is responsible for. This allows the application software t ...