File
... Then, along with hundreds or thousands of others, it does whatever it's told. Bots are often used to send spam, so the spammer's own systems aren't implicated. Some malicious programs exist specifically to aid in distribution of other malware. These dropper programs tend to be tiny and unobtrusive t ...
... Then, along with hundreds or thousands of others, it does whatever it's told. Bots are often used to send spam, so the spammer's own systems aren't implicated. Some malicious programs exist specifically to aid in distribution of other malware. These dropper programs tend to be tiny and unobtrusive t ...
Liam Michael Rafferty
... IP Access is a leading provider of small cell, cellular communication solutions to the mobile phone industry, it has a world-wide client base consisting of both tier-1 and tier-2 service providers. Contracted as a IT Support Analyst to provide IT support to over 250 staff members across their office ...
... IP Access is a leading provider of small cell, cellular communication solutions to the mobile phone industry, it has a world-wide client base consisting of both tier-1 and tier-2 service providers. Contracted as a IT Support Analyst to provide IT support to over 250 staff members across their office ...
Professional Profile
... accounts on Domain Controller and Mail Server. Daily system administration task for Windows 2000 Domain and Windows 2000 Active Directory servers, performance monitoring and tuning for in-house servers and at various client sites. Implementing and monitoring of Norton Anti Virus Corporate Version to ...
... accounts on Domain Controller and Mail Server. Daily system administration task for Windows 2000 Domain and Windows 2000 Active Directory servers, performance monitoring and tuning for in-house servers and at various client sites. Implementing and monitoring of Norton Anti Virus Corporate Version to ...
Chapter 01 Test
... In the past, Microsoft maintained a ____ to keep track of which products would work with each operating system. a. Hardware Compatibility List (HCL) b. Windows Driver Foundation (WDF) c. Windows Imaging Foundation (WIF) d. Windows Hardware Quality Labs (WHQL) A single ____ in Windows represents a co ...
... In the past, Microsoft maintained a ____ to keep track of which products would work with each operating system. a. Hardware Compatibility List (HCL) b. Windows Driver Foundation (WDF) c. Windows Imaging Foundation (WIF) d. Windows Hardware Quality Labs (WHQL) A single ____ in Windows represents a co ...
Factsheet - KFSensor
... New threats are constantly emerging to the security of organisations' information systems infrastructure. Firewalls and VPNs cannot prevent all intrusions and do little to prevent attacks from within the organisation itself. Intrusion detection plays a vital role in ensuring the integrity of a netwo ...
... New threats are constantly emerging to the security of organisations' information systems infrastructure. Firewalls and VPNs cannot prevent all intrusions and do little to prevent attacks from within the organisation itself. Intrusion detection plays a vital role in ensuring the integrity of a netwo ...
Resume - Training Directory Mena
... Install and configure Active Directory on windows Server 2003, 2008 and 2012 Install and configure DNS, DHCP. WSUS, WDS, GPOs, VPN, Terminal Services, Print Server and File Server. Managing and configuring Hyper-V. Install and configure Exchange 2013. Install and configure an SCCM 2012 Sever. Managi ...
... Install and configure Active Directory on windows Server 2003, 2008 and 2012 Install and configure DNS, DHCP. WSUS, WDS, GPOs, VPN, Terminal Services, Print Server and File Server. Managing and configuring Hyper-V. Install and configure Exchange 2013. Install and configure an SCCM 2012 Sever. Managi ...
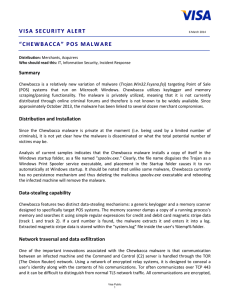
“CHEWBACCA” POS Malware
... Chewbacca binary is a PE32 executable compiled with Free Pascal 2.7.1 (the version dated 22.10.2013). The 5 MB file contains Tor 0.2.3.25 as well. Chewbacca binary is a PE32 executable compiled with Free Pascal 2.7.1 (the version dated 22.10.2013). The 5 MB file contains Tor 0.2.3.25 as well. Chewba ...
... Chewbacca binary is a PE32 executable compiled with Free Pascal 2.7.1 (the version dated 22.10.2013). The 5 MB file contains Tor 0.2.3.25 as well. Chewbacca binary is a PE32 executable compiled with Free Pascal 2.7.1 (the version dated 22.10.2013). The 5 MB file contains Tor 0.2.3.25 as well. Chewba ...
networkworld - Sift Security
... There's a powerful new generation of security tools coming to market designed to help security operations (SecOps) teams find and react to threats much quicker than before. The best of these tools also enable security analysts to proactively hunt for threats that might be present in their enterprise ...
... There's a powerful new generation of security tools coming to market designed to help security operations (SecOps) teams find and react to threats much quicker than before. The best of these tools also enable security analysts to proactively hunt for threats that might be present in their enterprise ...
Emerging Threats to Business Security
... while the Zlob Trojan family is also being constantly improved and may become one of the major threats next year. Other such trojans, which create networks of infected computers and use them to spread viruses, spam or to perform denial of service attacks, may also surface. For businesses, firewalls ...
... while the Zlob Trojan family is also being constantly improved and may become one of the major threats next year. Other such trojans, which create networks of infected computers and use them to spread viruses, spam or to perform denial of service attacks, may also surface. For businesses, firewalls ...
What`s New with Windows 7?
... Software to automatically query multiple computers on the network to verify compatibility with Windows 7 before deployment Used for lite-touch or zero-touch deployments Recommended by Microsoft for deployments of more than 200 computers ...
... Software to automatically query multiple computers on the network to verify compatibility with Windows 7 before deployment Used for lite-touch or zero-touch deployments Recommended by Microsoft for deployments of more than 200 computers ...
How does it get written up?
... sorts of things I’d be willing to get paged at 3am about • i.e.. only send an alert when something is an immediate threat, or requires immediate action • implies that alerts ought to include recommendations for action! ...
... sorts of things I’d be willing to get paged at 3am about • i.e.. only send an alert when something is an immediate threat, or requires immediate action • implies that alerts ought to include recommendations for action! ...
Orange Book Summary - UMBC Center for Information Security and
... This document is a summary of the US Department of Defense Trusted Computer System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the O ...
... This document is a summary of the US Department of Defense Trusted Computer System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the O ...
Orange
... This document is a summary of the US Department of Defense Trusted Computer System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the O ...
... This document is a summary of the US Department of Defense Trusted Computer System Evaluation Criteria, known as the Orange Book. Although originally written for military systems, the security classifications are now broadly used within the computer industry, You can get further information on the O ...
MENNOM_1_1
... segments into an internetwork. The router, once connected, can make intelligent decisions about how best to get network data to its destination based on network performance data that it gathers from the network itself. Routers are very complex devices. Often, routers are computers unto themselves wi ...
... segments into an internetwork. The router, once connected, can make intelligent decisions about how best to get network data to its destination based on network performance data that it gathers from the network itself. Routers are very complex devices. Often, routers are computers unto themselves wi ...
1993 - abuad lms
... segments into an internetwork. The router, once connected, can make intelligent decisions about how best to get network data to its destination based on network performance data that it gathers from the network itself. Routers are very complex devices. Often, routers are computers unto themselves wi ...
... segments into an internetwork. The router, once connected, can make intelligent decisions about how best to get network data to its destination based on network performance data that it gathers from the network itself. Routers are very complex devices. Often, routers are computers unto themselves wi ...
Windows 7 and A+ - Cengage Learning
... • Software to automatically query multiple computers on the network to verify compatibility with Windows 7 before deployment • Used for lite-touch or zero-touch deployments • Recommended by Microsoft for deployments of more than 200 computers ...
... • Software to automatically query multiple computers on the network to verify compatibility with Windows 7 before deployment • Used for lite-touch or zero-touch deployments • Recommended by Microsoft for deployments of more than 200 computers ...
Network Related Registry Keys
... • The date and times the user has been connected to their AP and the Internet • Whether the user was using a different adapter ...
... • The date and times the user has been connected to their AP and the Internet • Whether the user was using a different adapter ...
Document
... share a wide range of files such as Flash, Video, Microsoft Power Point, PDF, website etc. With Document Conference, every user will get the actual copy of files. ...
... share a wide range of files such as Flash, Video, Microsoft Power Point, PDF, website etc. With Document Conference, every user will get the actual copy of files. ...
9_13_35_JanResume
... Network Security configuring, designing ACLs In-depth knowledge of domain model and group policy In-depth knowledge of TCP/IP , subnetting very strong problem solving skills Good understanding of Networking, being able to troubleshoot Possess good organizational and management skills Ability to hand ...
... Network Security configuring, designing ACLs In-depth knowledge of domain model and group policy In-depth knowledge of TCP/IP , subnetting very strong problem solving skills Good understanding of Networking, being able to troubleshoot Possess good organizational and management skills Ability to hand ...
Information Security and its Implications on Everyday
... Antivirus software Essential no matter which platform you are using Update once a week (at least) and whenever you receive an auc advisory ...
... Antivirus software Essential no matter which platform you are using Update once a week (at least) and whenever you receive an auc advisory ...
PowerPoint Presentation - Security Risk Management
... Time between publication and exploit code ...
... Time between publication and exploit code ...
System Administrator
... Self-motivated, reliable, and highly adaptable with an exceptional aptitude for quickly mastering new hardware/software solutions. Professional Experience Consultant All American Small Business Computer Services: (July 2009 to Present) Gardner, KS. IT managed services using Kaseya software to manage ...
... Self-motivated, reliable, and highly adaptable with an exceptional aptitude for quickly mastering new hardware/software solutions. Professional Experience Consultant All American Small Business Computer Services: (July 2009 to Present) Gardner, KS. IT managed services using Kaseya software to manage ...
Slides.
... Limited number of login tries A database of all logins Simple login name/password as a trap – security personnel notified when attacker bites ...
... Limited number of login tries A database of all logins Simple login name/password as a trap – security personnel notified when attacker bites ...
Information Assurance Presentation
... major disruption of service from tier one carrier Level 3 Communications on October 21. The disruption caused increases in Internet response times and drops in availability. In addition, Websites were unreachable and service was shut off for some users. According to George Roettger, Internet securit ...
... major disruption of service from tier one carrier Level 3 Communications on October 21. The disruption caused increases in Internet response times and drops in availability. In addition, Websites were unreachable and service was shut off for some users. According to George Roettger, Internet securit ...