Maximum query latency Network traffic per query
... SG Project Challenges Real-time requirement • an query must be answered within a certain bounded time • e.g. a stolen car Scalable • up to millions of users and hundreds of thousands of vehicles • huge number of simultaneous queries ...
... SG Project Challenges Real-time requirement • an query must be answered within a certain bounded time • e.g. a stolen car Scalable • up to millions of users and hundreds of thousands of vehicles • huge number of simultaneous queries ...
Topologies for Power Efficient Wireless Sensor Networks
... It is a new communication protocol that tries to evenly distribute the energy load among the network nodes. This assumes that we have a finite amount of power and aims at conserving as much energy as possible despite a dynamic network. It uses data compression to reduce the amount of data that must ...
... It is a new communication protocol that tries to evenly distribute the energy load among the network nodes. This assumes that we have a finite amount of power and aims at conserving as much energy as possible despite a dynamic network. It uses data compression to reduce the amount of data that must ...
Visualisation and Analysis of Real Time Application Behaviour in a
... schemes • Evaluation of the behaviour of real time applications would benefit from an ability to assess the “quality of reproduction” when subjected to a particular network scheme ...
... schemes • Evaluation of the behaviour of real time applications would benefit from an ability to assess the “quality of reproduction” when subjected to a particular network scheme ...
Browsing around a digital library seminar
... probability of class given other attributes Not probability of the instances But: no closed-form solution for probabilities in nodes’ tables that maximize this However: can easily compute conditional probability of data based on given network Seems to work well when used for network scoring ...
... probability of class given other attributes Not probability of the instances But: no closed-form solution for probabilities in nodes’ tables that maximize this However: can easily compute conditional probability of data based on given network Seems to work well when used for network scoring ...
Defending Against Collaborative Attacks by Malicious
... (RREQ) packet through the network. If an intermediate node has routing information to the destination in its route cache, it will reply with a RREP to the source node. When the RREQ is forwarded to a node, the node adds its address information into the route record in the RREQ packet. When destinati ...
... (RREQ) packet through the network. If an intermediate node has routing information to the destination in its route cache, it will reply with a RREP to the source node. When the RREQ is forwarded to a node, the node adds its address information into the route record in the RREQ packet. When destinati ...
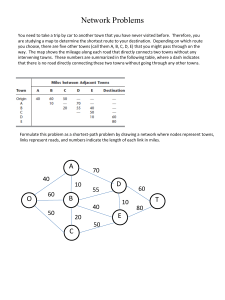
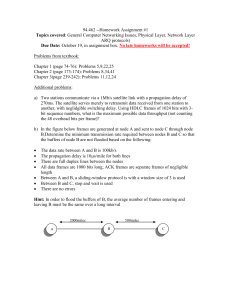
Document
... Additional problems: a) Two stations communicate via a 1Mb/s satellite link with a propagation delay of 270ms. The satellite serves merely to retransmit data received from one station to another, with neglidgible switching delay. Using HDLC frames of 1024 bits with 3bit sequence numbers, what is the ...
... Additional problems: a) Two stations communicate via a 1Mb/s satellite link with a propagation delay of 270ms. The satellite serves merely to retransmit data received from one station to another, with neglidgible switching delay. Using HDLC frames of 1024 bits with 3bit sequence numbers, what is the ...
Homework 6
... with a sample S 0 of size c, then with probability at least .99, the number returned will be a (.05)-approximate median of S. (You may consider either the version of the algorithm that constructs S 0 by sampling with replacement, so that an element of S can be selected multiple times, or without rep ...
... with a sample S 0 of size c, then with probability at least .99, the number returned will be a (.05)-approximate median of S. (You may consider either the version of the algorithm that constructs S 0 by sampling with replacement, so that an element of S can be selected multiple times, or without rep ...
SEARCH ALGORITHMS IN PEER TO PEER NETWORKS
... Properties of DHT • Keys mapped evenly to all nodes in the network • Each node maintains information about only a few other nodes • Efficient routing of messages to nodes • Node insertion/deletion only affects a few nodes ...
... Properties of DHT • Keys mapped evenly to all nodes in the network • Each node maintains information about only a few other nodes • Efficient routing of messages to nodes • Node insertion/deletion only affects a few nodes ...
Producer-Consumer Problem
... • This does not apply to the critical and noncritical sections in a solution of the critical section problem, only to the pre- and postprotocols. ...
... • This does not apply to the critical and noncritical sections in a solution of the critical section problem, only to the pre- and postprotocols. ...