Chapter 1: Introduction
... select ID, name, salary/12 as monthly_salary from instructor; Note: “as” 是在最後做,所以新定義的屬性名稱不能用在query其他地方 Tuple variables: “as”放在from clause ...
... select ID, name, salary/12 as monthly_salary from instructor; Note: “as” 是在最後做,所以新定義的屬性名稱不能用在query其他地方 Tuple variables: “as”放在from clause ...
Understanding and Interpreting SQL Server Performance Counters
... View contains one row per query plan • Lifetime of a row is tied to the plan itself ...
... View contains one row per query plan • Lifetime of a row is tied to the plan itself ...
The SQL++ Unifying Semi-structured Query Language, and an
... to MongoDB’s API, thereby augmenting MongoDB’s query capabilities (e.g. even though MongoDB cannot execute joins, the middleware can simulate some joins) but also altering query semantics (e.g. the middleware may transform the query result so that it conforms to a relational schema as required by JD ...
... to MongoDB’s API, thereby augmenting MongoDB’s query capabilities (e.g. even though MongoDB cannot execute joins, the middleware can simulate some joins) but also altering query semantics (e.g. the middleware may transform the query result so that it conforms to a relational schema as required by JD ...
Advanced Programming in Java
... ‘execute()’ method is used to execute a SQL statement which does not return a value, such as ‘CREATE TABLE’. ‘executeUpdate()’ method is used for SQL that updates a database, as in ‘INSERT’, ‘UPDATE’ and ‘DELETE’ SQL statements. It returns the number of rows affected. ‘executeQuery() ...
... ‘execute()’ method is used to execute a SQL statement which does not return a value, such as ‘CREATE TABLE’. ‘executeUpdate()’ method is used for SQL that updates a database, as in ‘INSERT’, ‘UPDATE’ and ‘DELETE’ SQL statements. It returns the number of rows affected. ‘executeQuery() ...
Slide 1
... • Describe the layout of each table in the database • Use CREATE TABLE command • TABLE is followed by the table name • Follow this with the names and data types of the columns in the table • Data types define type and size of data A Guide to MySQL ...
... • Describe the layout of each table in the database • Use CREATE TABLE command • TABLE is followed by the table name • Follow this with the names and data types of the columns in the table • Data types define type and size of data A Guide to MySQL ...
Containment of Conjunctive Queries over Databases With Null Values
... returns each answer item only once. Chaudhuri and Vardi considered containment under bag semantics, which allows tuples to occur more than once in an answer and is the semantics implemented in SQL database systems [4]. Another line of research considers the effect of integrity constraints such as f ...
... returns each answer item only once. Chaudhuri and Vardi considered containment under bag semantics, which allows tuples to occur more than once in an answer and is the semantics implemented in SQL database systems [4]. Another line of research considers the effect of integrity constraints such as f ...
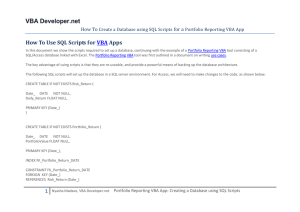
r VBA How To
... How to build a Black Scholes VBA Option Pricer for FX Options How to build a Black Scholes VBA Option Pricer for Equity Options How to build a Black Scholes VBA Option Pricer using Monte Carlo Simulation How to build a Black Scholes VBA Option Pricer for Binary Options How to build a Black Scholes V ...
... How to build a Black Scholes VBA Option Pricer for FX Options How to build a Black Scholes VBA Option Pricer for Equity Options How to build a Black Scholes VBA Option Pricer using Monte Carlo Simulation How to build a Black Scholes VBA Option Pricer for Binary Options How to build a Black Scholes V ...
Preference SQL - Institut für Informatik
... filling out query forms to match one’s personal preferences closely. Most probably, one has encountered answers before sounding like “no hotels, vehicles, flights, etc. could be found that matched your criteria; please try again with different choices”. The case of repeatedly receiving empty query r ...
... filling out query forms to match one’s personal preferences closely. Most probably, one has encountered answers before sounding like “no hotels, vehicles, flights, etc. could be found that matched your criteria; please try again with different choices”. The case of repeatedly receiving empty query r ...
Automatically Synthesizing SQL Queries from Input
... applied to the example input, then it produces the example and the de facto standard query language (SQL) are perfectly output; and if the synthesized SQL query is applied to other adequate for most end-users’ needs, the costs associated similar input (potentially much larger database tables), then ...
... applied to the example input, then it produces the example and the de facto standard query language (SQL) are perfectly output; and if the synthesized SQL query is applied to other adequate for most end-users’ needs, the costs associated similar input (potentially much larger database tables), then ...
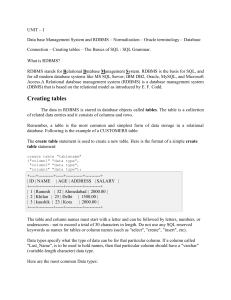
DataBase Management Systems Lecture Notes
... This is the average number of transactions that can be processed per minute. 5. Security Design: In this step, we must identify different user groups and different roles played by various users. For each role, and user group, we must identify the parts of the database that they must be able to acces ...
... This is the average number of transactions that can be processed per minute. 5. Security Design: In this step, we must identify different user groups and different roles played by various users. For each role, and user group, we must identify the parts of the database that they must be able to acces ...
jayavel - Berkeley Database Research
... • XML has emerged as the Internet data format • But relational database systems will continue to be used for data management tasks • Internet application developers currently have to explicitly bridge this “data model gap” • Can we design a system that automatically bridges this gap for application ...
... • XML has emerged as the Internet data format • But relational database systems will continue to be used for data management tasks • Internet application developers currently have to explicitly bridge this “data model gap” • Can we design a system that automatically bridges this gap for application ...
Monitor an Enterprise of SQL Servers - Automating Management by
... The first layer deals with critical SQL Server production errors that must be addressed promptly. We leverage the existing enterprise monitoring infrastructure to notify the DBAs, and rely on the SQL Server alert mechanism and other enterprise monitoring agents for error detection at this layer. SNM ...
... The first layer deals with critical SQL Server production errors that must be addressed promptly. We leverage the existing enterprise monitoring infrastructure to notify the DBAs, and rely on the SQL Server alert mechanism and other enterprise monitoring agents for error detection at this layer. SNM ...
Day 3 - Kuali Wiki
... if(broker != null) broker.abortTransaction(); // do more exception handling } finally { if (broker != null) broker.close(); ...
... if(broker != null) broker.abortTransaction(); // do more exception handling } finally { if (broker != null) broker.close(); ...
RDBMS - E
... data that can go into a table. This ensures the accuracy and reliability of the data in the database. Contraints could be column level or table level. Column level constraints are applied only to one column where as table level constraints are applied to the whole table. Following are commonly used ...
... data that can go into a table. This ensures the accuracy and reliability of the data in the database. Contraints could be column level or table level. Column level constraints are applied only to one column where as table level constraints are applied to the whole table. Following are commonly used ...
SELECT count(*) FROM customer
... Authorization – What can I do? SQL follows GRANT security model By default, a connected userid is not allowed to do anything. Exceptions: - the DBA account (full operations) - the TABLE owner DBA controls operation privileges with GRANT / REVOKE syntax ...
... Authorization – What can I do? SQL follows GRANT security model By default, a connected userid is not allowed to do anything. Exceptions: - the DBA account (full operations) - the TABLE owner DBA controls operation privileges with GRANT / REVOKE syntax ...
here.
... null values. • E.g. Find all loan number which appear in the loan relation with null values for amount. ...
... null values. • E.g. Find all loan number which appear in the loan relation with null values for amount. ...
Semantically Correct Query Answers in the Presence of Null Values
... More precisely, a repair of a database instance D, as introduced in [2], is a new instance of the same schema as D that satisfies the given ICs, and makes minimal under set inclusion the symmetric set difference with the original instance, taken both instances as sets of ground database atoms. In [2, ...
... More precisely, a repair of a database instance D, as introduced in [2], is a new instance of the same schema as D that satisfies the given ICs, and makes minimal under set inclusion the symmetric set difference with the original instance, taken both instances as sets of ground database atoms. In [2, ...
19:29, 30 May 2006
... by database, but by the application itself. Users connect to the database through a shared (may be even pooled) connection with the same web application specific database username and password (the database role), and the application username and password (the application role) are stored in the d ...
... by database, but by the application itself. Users connect to the database through a shared (may be even pooled) connection with the same web application specific database username and password (the database role), and the application username and password (the application role) are stored in the d ...
Advanced Topics on SQL Injection Protection
... by database, but by the application itself. Users connect to the database through a shared (may be even pooled) connection with the same web application specific database username and password (the database role), and the application username and password (the application role) are stored in the d ...
... by database, but by the application itself. Users connect to the database through a shared (may be even pooled) connection with the same web application specific database username and password (the database role), and the application username and password (the application role) are stored in the d ...
PL/SQL
... SELECT query to PL/SQL program variables when we are sure that the query will return one and only one record. If the query returns more than one record, or does not return any record, an error occurs. ...
... SELECT query to PL/SQL program variables when we are sure that the query will return one and only one record. If the query returns more than one record, or does not return any record, an error occurs. ...
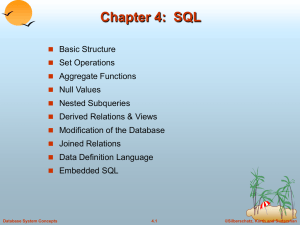
SQL: Queries, Programming, Triggers
... Rather than modify compiler, add library with database calls (API) and call their methods from program. Special standardized interface: procedures/objects. Pass SQL strings from programming language, present result sets in a languagefriendly way. Examples: ODBC, JDBC. ...
... Rather than modify compiler, add library with database calls (API) and call their methods from program. Special standardized interface: procedures/objects. Pass SQL strings from programming language, present result sets in a languagefriendly way. Examples: ODBC, JDBC. ...
kifer_268334_ppt08
... table); // table – host var; even the table is known only at run time! EXEC SQL PREPARE st FROM :my_sql_stmt; EXEC SQL ALLOCATE DESCRIPTOR ‘st_output’; EXEC SQL DESCRIBE OUTPUT st USING SQL DESCRIPTOR ‘st_output’ – The SQL statement to execute is known only at run time – At this point DBMS knows wha ...
... table); // table – host var; even the table is known only at run time! EXEC SQL PREPARE st FROM :my_sql_stmt; EXEC SQL ALLOCATE DESCRIPTOR ‘st_output’; EXEC SQL DESCRIBE OUTPUT st USING SQL DESCRIPTOR ‘st_output’ – The SQL statement to execute is known only at run time – At this point DBMS knows wha ...
SQL - STATUS
... Allows any of the ILE languages to access SQL functions directly through procedure calls to a service program provided by the system. Using this interface, one can perform all the SQL functions without the need for a precompile. It is ideally suited for a client-server environment, in which the ta ...
... Allows any of the ILE languages to access SQL functions directly through procedure calls to a service program provided by the system. Using this interface, one can perform all the SQL functions without the need for a precompile. It is ideally suited for a client-server environment, in which the ta ...
Null (SQL)

Null is a special marker used in Structured Query Language (SQL) to indicate that a data value does not exist in the database. Introduced by the creator of the relational database model, E. F. Codd, SQL Null serves to fulfill the requirement that all true relational database management systems (RDBMS) support a representation of ""missing information and inapplicable information"". Codd also introduced the use of the lowercase Greek omega (ω) symbol to represent Null in database theory. NULL is also an SQL reserved keyword used to identify the Null special marker.For people new to the subject, a good way to remember what null means is to remember that in terms of information, ""lack of a value"" is not the same thing as ""a value of zero""; similarly, ""lack of an answer"" is not the same thing as ""an answer of no"". For example, consider the question ""How many books does Juan own?"" The answer may be ""zero"" (we know that he owns none) or ""null"" (we do not know how many he owns, or doesn't own). In a database table, the column reporting this answer would start out with a value of null, and it would not be updated with ""zero"" until we have ascertained that Juan owns no books.SQL null is a state (unknown) and not a value. This usage is quite different from most programming languages, where null means not assigned to a particular instance.