DBMS File Structure
... Heap File Organization: When a file is created using Heap File Organization mechanism, the Operating Systems allocates memory area to that file without any further accounting details. File records can be placed anywhere in that memory area. It is the responsibility of software to manage the records. ...
... Heap File Organization: When a file is created using Heap File Organization mechanism, the Operating Systems allocates memory area to that file without any further accounting details. File records can be placed anywhere in that memory area. It is the responsibility of software to manage the records. ...
Acronis Disk Director Suite
... partitions — on the disk drive, you now can keep your operating system separate from your applications and data. In fact, each partition can contain its own operating system. How many partitions can I have on my hard disk? Physical hard disks can contain up to four primary partitions or up to three ...
... partitions — on the disk drive, you now can keep your operating system separate from your applications and data. In fact, each partition can contain its own operating system. How many partitions can I have on my hard disk? Physical hard disks can contain up to four primary partitions or up to three ...
Week_12 - Computing Sciences
... uses to keep track of files on a disk or partition; that is the way the files are organized on the disk. 3. Think of a file system as a protocol. File systems give meaning to the data on a particular storage device. What is a block device? It is a device in which the data that moves to and from occu ...
... uses to keep track of files on a disk or partition; that is the way the files are organized on the disk. 3. Think of a file system as a protocol. File systems give meaning to the data on a particular storage device. What is a block device? It is a device in which the data that moves to and from occu ...
Lost or Stolen Laptop Policy
... Don’t advertise that you’re carrying a valuable computer. Always keep your laptop with you and hidden. Your laptop should be set with a strong login password. As much as possible, you should access sensitive company data on the company network storage drives rather than storing a copy of the data on ...
... Don’t advertise that you’re carrying a valuable computer. Always keep your laptop with you and hidden. Your laptop should be set with a strong login password. As much as possible, you should access sensitive company data on the company network storage drives rather than storing a copy of the data on ...
3D Optical Data Storage Technology
... Is any drive that uses a lens to read and write data. Some common type of optical drives include CDROM, (read-only memory) CD-RW (rewritable), DVD-ROM (random access memory), DVD-RW (rewritable), and Blue-ray drives. How does it work? These discs are made up of millions of bumps and dips. Optical dr ...
... Is any drive that uses a lens to read and write data. Some common type of optical drives include CDROM, (read-only memory) CD-RW (rewritable), DVD-ROM (random access memory), DVD-RW (rewritable), and Blue-ray drives. How does it work? These discs are made up of millions of bumps and dips. Optical dr ...
System software - Barbados SDA Secondary
... the data is stored and the directory or folder in which the file is located. For example, a prompt which shows • C:\> means that all commands will be performed with data on drive C: • A command prompt with A:\> refers to a diskette in the disk drive. A sub-directory or folder is similar to a drawer ...
... the data is stored and the directory or folder in which the file is located. For example, a prompt which shows • C:\> means that all commands will be performed with data on drive C: • A command prompt with A:\> refers to a diskette in the disk drive. A sub-directory or folder is similar to a drawer ...
solid state drive
... Solid State Drives in the literal sense have been around since the 1950s, although it wasn’t until 1983 that the first “modern” solid state drive was readily available: Sharp’s PC-5000 laptop’s internal storage held 128 kilobytes of data and used magnetism in a similar way to today’s magnetic hard d ...
... Solid State Drives in the literal sense have been around since the 1950s, although it wasn’t until 1983 that the first “modern” solid state drive was readily available: Sharp’s PC-5000 laptop’s internal storage held 128 kilobytes of data and used magnetism in a similar way to today’s magnetic hard d ...
Components of a Storage System Environment The three main
... individuals to store photos or as a backup medium on personal/laptop computers. It is also used as a istribution medium for single applications, such as games, or as a means of transferring small amounts of data from one self-contained system to another. Optical disks have limited capacity and speed ...
... individuals to store photos or as a backup medium on personal/laptop computers. It is also used as a istribution medium for single applications, such as games, or as a means of transferring small amounts of data from one self-contained system to another. Optical disks have limited capacity and speed ...
SAFE: Fast, Verifiable Sanitization for SSDs
... This report makes the detailed case for SAFE as an alternative to purely cryptographic erasure techniques. We show that SAFE can provide fast sanitization without sacrificing reliability. Given the demonstrated history of buggy sanitize operations and the long history of vulnerabilities in the appli ...
... This report makes the detailed case for SAFE as an alternative to purely cryptographic erasure techniques. We show that SAFE can provide fast sanitization without sacrificing reliability. Given the demonstrated history of buggy sanitize operations and the long history of vulnerabilities in the appli ...
The broken file shredder
... may ignore all but the last overwrite operation. Non-magnetic disks (flash, NVRAM) try to avoid overwriting the same bits repeatedly and instead create multiple copies of data. Not shredded: temporary copies from text editors, printer spoolers, mail clients; swap files. But wait, there is more ...
... may ignore all but the last overwrite operation. Non-magnetic disks (flash, NVRAM) try to avoid overwriting the same bits repeatedly and instead create multiple copies of data. Not shredded: temporary copies from text editors, printer spoolers, mail clients; swap files. But wait, there is more ...
MULTIMEDIA Technology
... It refers to the technology for creating an artificial (virtual) reality by combining computer graphics with sound effects. People can experience virtual realities like farremoved worlds, past and future locations, etc., as if they were actually there, while not setting foot outside their current lo ...
... It refers to the technology for creating an artificial (virtual) reality by combining computer graphics with sound effects. People can experience virtual realities like farremoved worlds, past and future locations, etc., as if they were actually there, while not setting foot outside their current lo ...
File I/O
... PrintWriter outFile = new PrintWriter( new BufferedWriter ( new FileWriter (file_name) ) ); ...
... PrintWriter outFile = new PrintWriter( new BufferedWriter ( new FileWriter (file_name) ) ); ...
BCS HIGHER EDUCATION QUALIFICATIONS Level 4 Certificate in IT March 2015
... Hard disk drives store data on rotating flat platters of aluminium or glass coated with a magnetic material. The rotating platter passes under a read/write head that can magnetize the surface (writing) and determine the state of the magnetization (reading). Because the magnetization is permanent unt ...
... Hard disk drives store data on rotating flat platters of aluminium or glass coated with a magnetic material. The rotating platter passes under a read/write head that can magnetize the surface (writing) and determine the state of the magnetization (reading). Because the magnetization is permanent unt ...
Computer Forensics
... – RAM slack is the space from the end of the file to the end of the containing sector. Before a sector is written to disk, it is stored in a buffer somewhere in RAM. If the buffer is only partially filled with information before being committed to disk, remnants from the end of the buffer will be wr ...
... – RAM slack is the space from the end of the file to the end of the containing sector. Before a sector is written to disk, it is stored in a buffer somewhere in RAM. If the buffer is only partially filled with information before being committed to disk, remnants from the end of the buffer will be wr ...
p1 p2 p3 pn
... • Prototypical workload • High throughput, sequential IO, write once • Cluster machines working in parallel • Configurable number of replicas per dataset ...
... • Prototypical workload • High throughput, sequential IO, write once • Cluster machines working in parallel • Configurable number of replicas per dataset ...
Paper - NDSU Computer Science
... memory area. For example, a symmetric multiprocessor computer would fall into this category, if it were running by itself. This architecture is the easiest to maintain with only one central system, but is difficult to scale up to large sizes. For example, there are very few computers built with more ...
... memory area. For example, a symmetric multiprocessor computer would fall into this category, if it were running by itself. This architecture is the easiest to maintain with only one central system, but is difficult to scale up to large sizes. For example, there are very few computers built with more ...
Chapter 1b
... users to resources defined by the OS Security – defense of the system against internal and external attacks ...
... users to resources defined by the OS Security – defense of the system against internal and external attacks ...
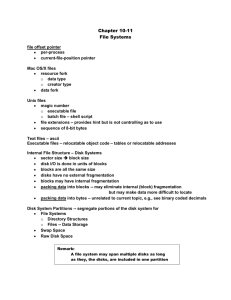
Chapter 10-11 File Systems
... o search System-Wide Open-File Table to see if file is currently in use if it is, create a Per-Process Open-File table entry pointing to the existing System-Wide Open-File Table if it is not, search the directory for the file name; once found, place the FCB in the System-Wide Open-File Table o m ...
... o search System-Wide Open-File Table to see if file is currently in use if it is, create a Per-Process Open-File table entry pointing to the existing System-Wide Open-File Table if it is not, search the directory for the file name; once found, place the FCB in the System-Wide Open-File Table o m ...
CUSTOMER_CODE SMUDE DIVISION_CODE SMUDE
... To locate a particular item, the search information provided is passed through the hash function again, so the search is quickly narrowed down to roughly 1/N of the total pieces of data that might otherwise be searched. The defect in static hashing is the fact that the number of buckets remain stati ...
... To locate a particular item, the search information provided is passed through the hash function again, so the search is quickly narrowed down to roughly 1/N of the total pieces of data that might otherwise be searched. The defect in static hashing is the fact that the number of buckets remain stati ...
Multi-Drive Libraries, Virtual Tape Libraries (VTL
... A number of storage vendors ship devices that appear to a backup application as a tape library. In actuality, these devices are disk-based storage mechanisms that have an operating system and filesystem that allow the disk volume(s) to emulate tape drives and libraries right down to the SCSI command ...
... A number of storage vendors ship devices that appear to a backup application as a tape library. In actuality, these devices are disk-based storage mechanisms that have an operating system and filesystem that allow the disk volume(s) to emulate tape drives and libraries right down to the SCSI command ...
Comparing and Contrasting Windows and Linux Forensics Zlatko
... physical structure of hard drive are listed in /dev directory (p. 254). Linux hard drive structure consists of: Inodes, Superblock, Data block, and Dentry (Nelson, p. 134) File management system for two OS’s is different. Windows could have FAT (with its variations) or NTFS file system, while Linux ...
... physical structure of hard drive are listed in /dev directory (p. 254). Linux hard drive structure consists of: Inodes, Superblock, Data block, and Dentry (Nelson, p. 134) File management system for two OS’s is different. Windows could have FAT (with its variations) or NTFS file system, while Linux ...
TrusTed plaTform module (Tpm) Toshiba securiTy
... The Emergency Recovery Archive File stores all user security keys. This file should be backed up periodically to an external storage device in case the HDD ever becomes inaccessible. The Emergency Recovery Token is a key that is required to access the Emergency Recovery Archive file. This token file ...
... The Emergency Recovery Archive File stores all user security keys. This file should be backed up periodically to an external storage device in case the HDD ever becomes inaccessible. The Emergency Recovery Token is a key that is required to access the Emergency Recovery Archive file. This token file ...