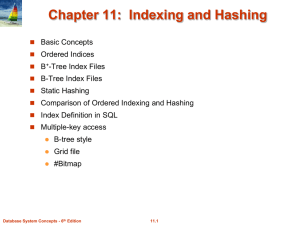
Physical Data Organization and Indexing
... – Occupancy of each bucket roughly same for an average instance of indexed table ...
... – Occupancy of each bucket roughly same for an average instance of indexed table ...
Data Modeling - Temple Fox MIS
... So why do you think we defined “Zip” as a VARCHAR() instead of an INT? ...
... So why do you think we defined “Zip” as a VARCHAR() instead of an INT? ...
A FAST METHOD FOR IMPLEMENTATION OF THE PROPERTY
... Sequential Search and Bucketing [1] may be used. In most systems, a hash-table imposes too much overhead when objects are expected to have only a handful of properties, up to perhaps two or three dozen [6]. A common solution is to use a hybrid model, in which the property list begins life as a simpl ...
... Sequential Search and Bucketing [1] may be used. In most systems, a hash-table imposes too much overhead when objects are expected to have only a handful of properties, up to perhaps two or three dozen [6]. A common solution is to use a hybrid model, in which the property list begins life as a simpl ...
D amortized analysis binomial heaps Fibonacci heaps
... Figure 17.2 An 8-bit binary counter as its value goes from 0 to 16 by a sequence of 16 I NCREMENT operations. Bits that flip to achieve the next value are shaded. The running cost for flipping bits is shown at the right. Notice that the total cost is always less than twice the total number of I NCRE ...
... Figure 17.2 An 8-bit binary counter as its value goes from 0 to 16 by a sequence of 16 I NCREMENT operations. Bits that flip to achieve the next value are shaded. The running cost for flipping bits is shown at the right. Notice that the total cost is always less than twice the total number of I NCRE ...
TUKE-08-SRBD-02-Fyzicke-organizacie
... If the records of R and S are physically sorted (ordered) by value of the join attributes A and B, respectively, we can implement the join in the most efficient way possible. Both files are scanned concurrently in order of the join attributes, matching the records that have the same values for A and ...
... If the records of R and S are physically sorted (ordered) by value of the join attributes A and B, respectively, we can implement the join in the most efficient way possible. Both files are scanned concurrently in order of the join attributes, matching the records that have the same values for A and ...
De-amortized Cuckoo Hashing: Provable Worst
... research has been devoted over the years for studying dynamic dictionaries both on the theoretical side by exploring upper and lower bounds on the performance guarantees, and on the practical side by designing efficient dynamic dictionaries that are suitable for real-world applications. The most eff ...
... research has been devoted over the years for studying dynamic dictionaries both on the theoretical side by exploring upper and lower bounds on the performance guarantees, and on the practical side by designing efficient dynamic dictionaries that are suitable for real-world applications. The most eff ...
An Efficient Dynamic and Distributed Cryptographic Accumulator
... directories. This approach is secure, but it is inefficient, for it requires the transmission of the entire set of revoked certificates for both source-to-directory and directory-to-user communication. Thus, this solution is clearly not size-oblivious, and even more recent modifications of this solution ...
... directories. This approach is secure, but it is inefficient, for it requires the transmission of the entire set of revoked certificates for both source-to-directory and directory-to-user communication. Thus, this solution is clearly not size-oblivious, and even more recent modifications of this solution ...
PDF
... research has been devoted over the years for studying dynamic dictionaries both on the theoretical side by exploring upper and lower bounds on the performance guarantees, and on the practical side by designing efficient dynamic dictionaries that are suitable for real-world applications. The most eff ...
... research has been devoted over the years for studying dynamic dictionaries both on the theoretical side by exploring upper and lower bounds on the performance guarantees, and on the practical side by designing efficient dynamic dictionaries that are suitable for real-world applications. The most eff ...
Data Structures and Analysis - Department of Computer Science
... analysis: what inputs we’re looking at, and how we’re measuring runtime. The final step is what we had initially talked about: compute the average running time over inputs of length n. This often requires some calculation, so let’s get to it. To simplify our calculations even further, we’ll assume t ...
... analysis: what inputs we’re looking at, and how we’re measuring runtime. The final step is what we had initially talked about: compute the average running time over inputs of length n. This often requires some calculation, so let’s get to it. To simplify our calculations even further, we’ll assume t ...
ppt
... • Analyze BubbleSort to determine if it is correct, and fix it if incorrect. • Hint: you need to define “correct” • Hint2: you need to define a loop invariant to ...
... • Analyze BubbleSort to determine if it is correct, and fix it if incorrect. • Hint: you need to define “correct” • Hint2: you need to define a loop invariant to ...
Lecture 9 — 16 Feb, 2012 1 Overview 2 The problem
... Notice that if S was a static set then we could store the predecessor and successor of each x ∈ S explicitly, so that look-up time for these operations would be O(1). However, if |S| = m, this would require extra storage space of O(m log m) bits. ...
... Notice that if S was a static set then we could store the predecessor and successor of each x ∈ S explicitly, so that look-up time for these operations would be O(1). However, if |S| = m, this would require extra storage space of O(m log m) bits. ...
MIS2502: Data Analytics SQL – Putting Information Into a Database
... FirstName VARCHAR(45) NULL , LastName VARCHAR(45) NULL , City VARCHAR(45) NULL , State VARCHAR(2) NULL , Zip VARCHAR(10) NULL , ...
... FirstName VARCHAR(45) NULL , LastName VARCHAR(45) NULL , City VARCHAR(45) NULL , State VARCHAR(2) NULL , Zip VARCHAR(10) NULL , ...
Example of Sparse Index Files
... " Dense indices – if the search-key value does not appear in the ...
... " Dense indices – if the search-key value does not appear in the ...
Coda Server Internals
... each link points to a DiskVnode lists link vnodes with identical vnodenumbers but different uniquefiers new vnodes grabbed from FreeLists (index.cc, recov{a,b,c}.cc) volumes have arrays of rec_smolists which grow when they are full ...
... each link points to a DiskVnode lists link vnodes with identical vnodenumbers but different uniquefiers new vnodes grabbed from FreeLists (index.cc, recov{a,b,c}.cc) volumes have arrays of rec_smolists which grow when they are full ...
Document
... AGENT table’s primary key is AGENT_CODE, and this primary key column is also free of null entries. • Referential integrity. The CUSTOMER table contains a foreign key, AGENT_CODE, which links entries in the CUSTOMER table to the AGENT table. The CUS_CODE row that is identified by the (primary key) nu ...
... AGENT table’s primary key is AGENT_CODE, and this primary key column is also free of null entries. • Referential integrity. The CUSTOMER table contains a foreign key, AGENT_CODE, which links entries in the CUSTOMER table to the AGENT table. The CUS_CODE row that is identified by the (primary key) nu ...
B + -Tree Index Files
... number of records assigned to it irrespective of the actual distribution of search-key values in the file. Typical hash functions perform computation on the internal binary ...
... number of records assigned to it irrespective of the actual distribution of search-key values in the file. Typical hash functions perform computation on the internal binary ...
Efficient Consistency Proofs for Generalized Queries on a
... A very similar data structure (again, a Merkle tree) also allows one to also answer one-dimensional range queries, e.g. “What keys lie between x and y?” [4, 11, 16]. Merkle trees were subsequently modified to allow efficient updates by changing the structure to resemble a skip list [12]. Our work ge ...
... A very similar data structure (again, a Merkle tree) also allows one to also answer one-dimensional range queries, e.g. “What keys lie between x and y?” [4, 11, 16]. Merkle trees were subsequently modified to allow efficient updates by changing the structure to resemble a skip list [12]. Our work ge ...
Accountable systems or how to catch a liar?
... • Each file is writable by one user or group • Each user/group manages its own pool of inodes – A pool of inodes is represented as a hash tree ...
... • Each file is writable by one user or group • Each user/group manages its own pool of inodes – A pool of inodes is represented as a hash tree ...
Accountable systems or how to catch a liar?
... • Each file is writable by one user or group • Each user/group manages its own pool of inodes – A pool of inodes is represented as a hash tree ...
... • Each file is writable by one user or group • Each user/group manages its own pool of inodes – A pool of inodes is represented as a hash tree ...
Rainbow table
A rainbow table is a precomputed table for reversing cryptographic hash functions, usually for cracking password hashes. Tables are usually used in recovering a plaintext password up to a certain length consisting of a limited set of characters. It is a practical example of a space/time trade-off, using less computer processing time and more storage than a brute-force attack which calculates a hash on every attempt, but more processing time and less storage than a simple lookup table with one entry per hash. Use of a key derivation function that employs a salt makes this attack infeasible.Rainbow tables are an application of an earlier, simpler algorithm by Martin Hellman.