2-7 The Mathematics Models and an Actual Proof Experiment
... • Measure Synflood attacks in real time in order to distinguish between normal data and attack flows. • When an attack is detected by the above procedure, use a traceback system to generate a suspect list. • Generate a suspect list periodically (e.g., every second at the time of attacks) and judge f ...
... • Measure Synflood attacks in real time in order to distinguish between normal data and attack flows. • When an attack is detected by the above procedure, use a traceback system to generate a suspect list. • Generate a suspect list periodically (e.g., every second at the time of attacks) and judge f ...
E - Read
... – 2n+o(n) by Bent and John (STOC 1985) – (2+2-80)n by Dor and Zwick (FOCS 1996, SIAM Journal on Discrete Math 2001). ...
... – 2n+o(n) by Bent and John (STOC 1985) – (2+2-80)n by Dor and Zwick (FOCS 1996, SIAM Journal on Discrete Math 2001). ...
A Mathematical Model for Optimal Tuning Systems
... or even a single composer. Such a system may also serve as an abstraction, or model, for the derivation of any number of related systems and sub-systems. Smaller, functional subsets of pitches, such as scales, are extracted from a larger tuning system for specific musical purposes. Examples include ...
... or even a single composer. Such a system may also serve as an abstraction, or model, for the derivation of any number of related systems and sub-systems. Smaller, functional subsets of pitches, such as scales, are extracted from a larger tuning system for specific musical purposes. Examples include ...
Chapter16-PresentationDistilled
... mistakes and high-level thinking. After a set time interval the roles are switched and work continues. Like a continuous code review. ...
... mistakes and high-level thinking. After a set time interval the roles are switched and work continues. Like a continuous code review. ...
LifeCare PCA Infusion System With Hospira MedNet Software
... information can be downloaded in reports and used for continuous quality improvement. The primary feature of the LifeCare PCA® Infusion System is the integral barcode reader. The barcode reader identifies the drug and concentration of the vial inserted in the device, and links it to the correct dosi ...
... information can be downloaded in reports and used for continuous quality improvement. The primary feature of the LifeCare PCA® Infusion System is the integral barcode reader. The barcode reader identifies the drug and concentration of the vial inserted in the device, and links it to the correct dosi ...
Research Article Classification of Textual E-Mail Spam
... before using genetic algorithm, at first it is necessary to design solutions of a problem in the form of a chromosome. Proceeding from character of a solved problem (8)–(11), a chromosome in populations is represented in such kind: X = (x11 , . . . , x1k , x21 , . . . , x2k , . . . , xn1 , . . . , x ...
... before using genetic algorithm, at first it is necessary to design solutions of a problem in the form of a chromosome. Proceeding from character of a solved problem (8)–(11), a chromosome in populations is represented in such kind: X = (x11 , . . . , x1k , x21 , . . . , x2k , . . . , xn1 , . . . , x ...
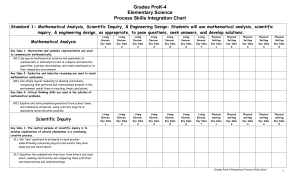
154 kb - Mahopac Central School District
... descriptions of objects and events and to from their own tentative explanations of what they have observed. Key Idea 2: Beyond the use of reasoning & consensus, scientific inquiry involves the testing of proposed explanations involving the use of conventional techniques & procedures & usually requir ...
... descriptions of objects and events and to from their own tentative explanations of what they have observed. Key Idea 2: Beyond the use of reasoning & consensus, scientific inquiry involves the testing of proposed explanations involving the use of conventional techniques & procedures & usually requir ...
EE579T-Class 4
... The computer can factor any N, using the trial division method, in approximately N0.5/1010 seconds. If N has 100 digits, this process will require approximately ...
... The computer can factor any N, using the trial division method, in approximately N0.5/1010 seconds. If N has 100 digits, this process will require approximately ...
ipSecMicrosof
... IPSec is based on an end-to-end security model that establishes trust and security from a source IP to a destination IP address. Any computers that only route data from source to destination are not required to support IPSec, unless firewall-type packet filtering or network address translation (NAT ...
... IPSec is based on an end-to-end security model that establishes trust and security from a source IP to a destination IP address. Any computers that only route data from source to destination are not required to support IPSec, unless firewall-type packet filtering or network address translation (NAT ...
Application Security within Java 2, Standard Edition (J2SE)
... In order to perform JAAS authorization, you need to know three things. You need to know 1) who or what is authorizing, 2) the resource they are trying to use and 3) what they are actually trying to do with the resource (read, write, execute, ...
... In order to perform JAAS authorization, you need to know three things. You need to know 1) who or what is authorizing, 2) the resource they are trying to use and 3) what they are actually trying to do with the resource (read, write, execute, ...
離散對數密碼系統 - 國立交通大學資訊工程學系NCTU Department of
... Algorithms for Discrete Logarithm • Shanks’ algorithm (1972) – Compute L1 = {(i, gmi), i = 0, 1, …, m-1} L2 = {(i, ag-i), i = 0, 1, …, m-1} – where m = ceiling((p-1) ½) Sort L1 and L2 with respect to the 2nd coordinate. – Find the same 2nd coordinate from L1 and L2, say, (q, gmq), (r, ag-r), to get ...
... Algorithms for Discrete Logarithm • Shanks’ algorithm (1972) – Compute L1 = {(i, gmi), i = 0, 1, …, m-1} L2 = {(i, ag-i), i = 0, 1, …, m-1} – where m = ceiling((p-1) ½) Sort L1 and L2 with respect to the 2nd coordinate. – Find the same 2nd coordinate from L1 and L2, say, (q, gmq), (r, ag-r), to get ...
W. Dean. Algorithms and the mathematical foundations of computer
... demonstrated in the course of answering Hilbert’s Entscheidungsproblem in the negative (which is what is reported by (1)). And it has a similar effect for other formal undecidability results for problems such as the word problem for semigroups or Hilbert’s tenth problem. Taken on its own, however, C ...
... demonstrated in the course of answering Hilbert’s Entscheidungsproblem in the negative (which is what is reported by (1)). And it has a similar effect for other formal undecidability results for problems such as the word problem for semigroups or Hilbert’s tenth problem. Taken on its own, however, C ...
Computer Supported Formal Work: Towards a Digital Mathematical
... The Ωmega project6 represents one of the major attempts to build an all encompassing assistant tool for the working mathematician. It is a representative of systems in the new paradigm of proof planning and combines interactive tactical and automated proof construction for domains with rich and well ...
... The Ωmega project6 represents one of the major attempts to build an all encompassing assistant tool for the working mathematician. It is a representative of systems in the new paradigm of proof planning and combines interactive tactical and automated proof construction for domains with rich and well ...
Absolute Provability and Safe Knowledge of
... strictly somewhat more powerful than ours. They use A to settle various previously open questions. Since both A and all of their other first principles are true, no inconsistency ever results. Indeed, A will have various consequences that the creatures can independently test on the basis of the A-f ...
... strictly somewhat more powerful than ours. They use A to settle various previously open questions. Since both A and all of their other first principles are true, no inconsistency ever results. Indeed, A will have various consequences that the creatures can independently test on the basis of the A-f ...
Attestation
... Embedding PCR values in blob ensures that only certain apps can decrypt data. e.g.: Messing with MBR or OS kernel will change PCR values. Why can’t attacker disable TPM until after boot, then extend PCRs with whatever he wants? Root of trust: BIOS boot block. Gaping hole: role-back attack on enc ...
... Embedding PCR values in blob ensures that only certain apps can decrypt data. e.g.: Messing with MBR or OS kernel will change PCR values. Why can’t attacker disable TPM until after boot, then extend PCRs with whatever he wants? Root of trust: BIOS boot block. Gaping hole: role-back attack on enc ...
Spear Phishing Attacks—Why They are Successful and How to Stop
... The assault began with spear phishing attacks that sent targeted users an email with a Microsoft Excel file attachment that leveraged a zero-day flaw in Adobe Flash. It is clear that not only was RSA the focus of the attack, but only four individuals within RSA were the recipients of the malicious e ...
... The assault began with spear phishing attacks that sent targeted users an email with a Microsoft Excel file attachment that leveraged a zero-day flaw in Adobe Flash. It is clear that not only was RSA the focus of the attack, but only four individuals within RSA were the recipients of the malicious e ...
CH10
... Encryption Solutions (cont’d.) • Asymmetric encryption (public-key encryption) – Encodes messages using two mathematically related numeric keys – Public key: one key freely distributed to public • Encrypt messages using encryption algorithm ...
... Encryption Solutions (cont’d.) • Asymmetric encryption (public-key encryption) – Encodes messages using two mathematically related numeric keys – Public key: one key freely distributed to public • Encrypt messages using encryption algorithm ...
Chapter 10
... Security Policy and Integrated Security (cont’d.) • E-commerce site security policy points – Authentication: Who is trying to access site? – Access control: Who is allowed to log on to and ...
... Security Policy and Integrated Security (cont’d.) • E-commerce site security policy points – Authentication: Who is trying to access site? – Access control: Who is allowed to log on to and ...
4. Preliminary remarks on Algebraic Groups
... different in the published version. Please send an email to [email protected] if you find any mistakes. All feedback on the book is very welcome and will be acknowledged. For efficient public key cryptography based on discrete logarithms one would like to have groups for which computin ...
... different in the published version. Please send an email to [email protected] if you find any mistakes. All feedback on the book is very welcome and will be acknowledged. For efficient public key cryptography based on discrete logarithms one would like to have groups for which computin ...
21. immobilizer system (hiss)
... • The key has built-in electronic part (transponder). Do not drop and strike the key against a hard material object, and do not leave the key on the dashboard in the car, etc. where the temperature will rise. Do not leave the key in the water for a prolonged time such as by washing the clothes. • Th ...
... • The key has built-in electronic part (transponder). Do not drop and strike the key against a hard material object, and do not leave the key on the dashboard in the car, etc. where the temperature will rise. Do not leave the key in the water for a prolonged time such as by washing the clothes. • Th ...
Section2.1notesall
... Cryptanalysis of Shift Ciphers As the last two examples illustrate, one must know the key k used in a shift cipher when deciphering a message. This leads to an important question. How can we decipher a message in a shift cipher if we do not know the key k ? Cryptanalysis is the process of trying to ...
... Cryptanalysis of Shift Ciphers As the last two examples illustrate, one must know the key k used in a shift cipher when deciphering a message. This leads to an important question. How can we decipher a message in a shift cipher if we do not know the key k ? Cryptanalysis is the process of trying to ...
Application research and analysis based on Bitlocker
... then Windows 7 operating system uses of Bitlocker encryption system boot disk in the case of without installingtrusted platform module of TPM1.2 version. Encryption started, open the desktop icon, select the system disk (C:), click the right key and chooseBitlocker (B), requires the startup key when ...
... then Windows 7 operating system uses of Bitlocker encryption system boot disk in the case of without installingtrusted platform module of TPM1.2 version. Encryption started, open the desktop icon, select the system disk (C:), click the right key and chooseBitlocker (B), requires the startup key when ...
A+B
... Big-Omega and Big-Theta Nation • Definition 2: Let f and g be functions from the set of integers or the set of real numbers to the set of real numbers. • We say that f(x) is Ω(g(x)) if there are positive constants C and k such that |f(x)|≥ C|g(x)| Whenever x > k. ( this is read as “f(x) is big-Omeg ...
... Big-Omega and Big-Theta Nation • Definition 2: Let f and g be functions from the set of integers or the set of real numbers to the set of real numbers. • We say that f(x) is Ω(g(x)) if there are positive constants C and k such that |f(x)|≥ C|g(x)| Whenever x > k. ( this is read as “f(x) is big-Omeg ...
Cryptanalysis

Cryptanalysis (from the Greek kryptós, ""hidden"", and analýein, ""to loosen"" or ""to untie"") is the study of analyzing information systems in order to study the hidden aspects of the systems. Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown.In addition to mathematical analysis of cryptographic algorithms, cryptanalysis includes the study of side-channel attacks that do not target weaknesses in the cryptographic algorithms themselves, but instead exploit weaknesses in their implementation.Even though the goal has been the same, the methods and techniques of cryptanalysis have changed drastically through the history of cryptography, adapting to increasing cryptographic complexity, ranging from the pen-and-paper methods of the past, through machines like the British Bombes and Colossus computers at Bletchley Park in World War II, to the mathematically advanced computerized schemes of the present. Methods for breaking modern cryptosystems often involve solving carefully constructed problems in pure mathematics, the best-known being integer factorization.